- Цена
- 50-150
- Контакты
- 6E9D910752250CED7D1A920ED1FDC61C87E2EA51E3204A9BD4531ADE4056CE530F197E3BAC05
EN:
Hello all,
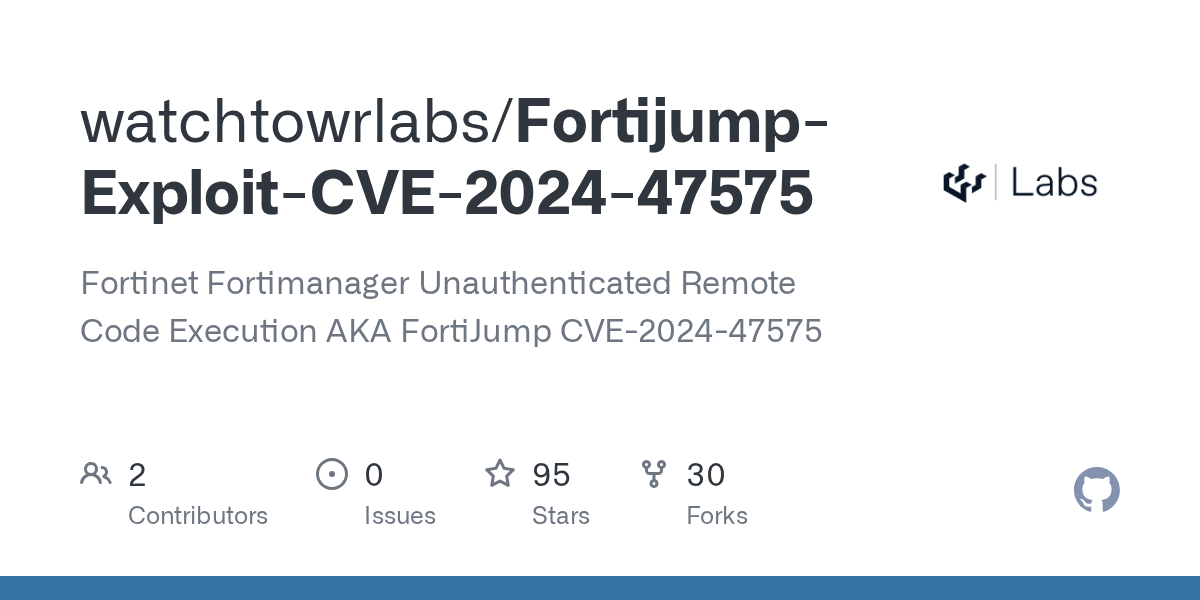
I am looking to buy an exploit code for the CVE in the title. Dm me on qTox. It is in my signature.
Thanks a lot,
Nickzfam
-------------------------------------------------------------------------------------------------------------------------------------
RU:
Всем здравствуйте,
Я хочу купить код эксплойта для CVE, указанный в заголовке. Напишите мне в qTox. Это у меня в подписи.
Большое спасибо,
Nickzfam
Hello all,
I am looking to buy an exploit code for the CVE in the title. Dm me on qTox. It is in my signature.
Thanks a lot,
Nickzfam
-------------------------------------------------------------------------------------------------------------------------------------
RU:
Всем здравствуйте,
Я хочу купить код эксплойта для CVE, указанный в заголовке. Напишите мне в qTox. Это у меня в подписи.
Большое спасибо,
Nickzfam