- Цена
- 500$ 1,200$ 2,000$
- Контакты
- @Kim_unbash
⁇ ⁇ Hello XSS Members, ⁇ ⁇
I am offering a comprehensive Advanced Office 365 Tutorial focusing on BEC (Business Email Compromise) prevention for educational purposes. This package includes detailed methods, BEC tools, and a step-by-step setup guide to enhance your understanding of how BEC attacks work and how to Bypass the secuirty reuls, Bot filtering, isp mailling trafic bot scan, vpn-bot killer etc.
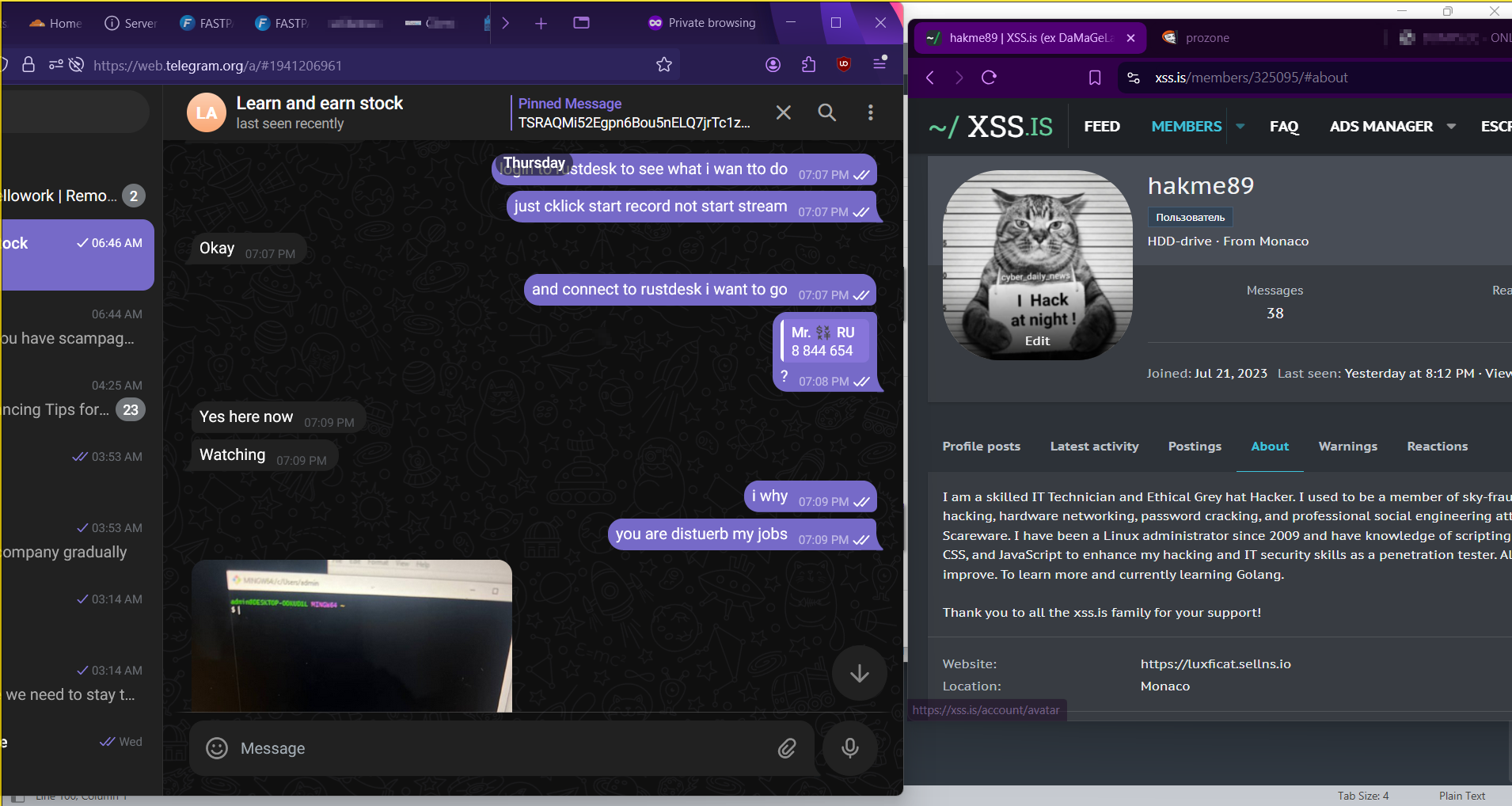
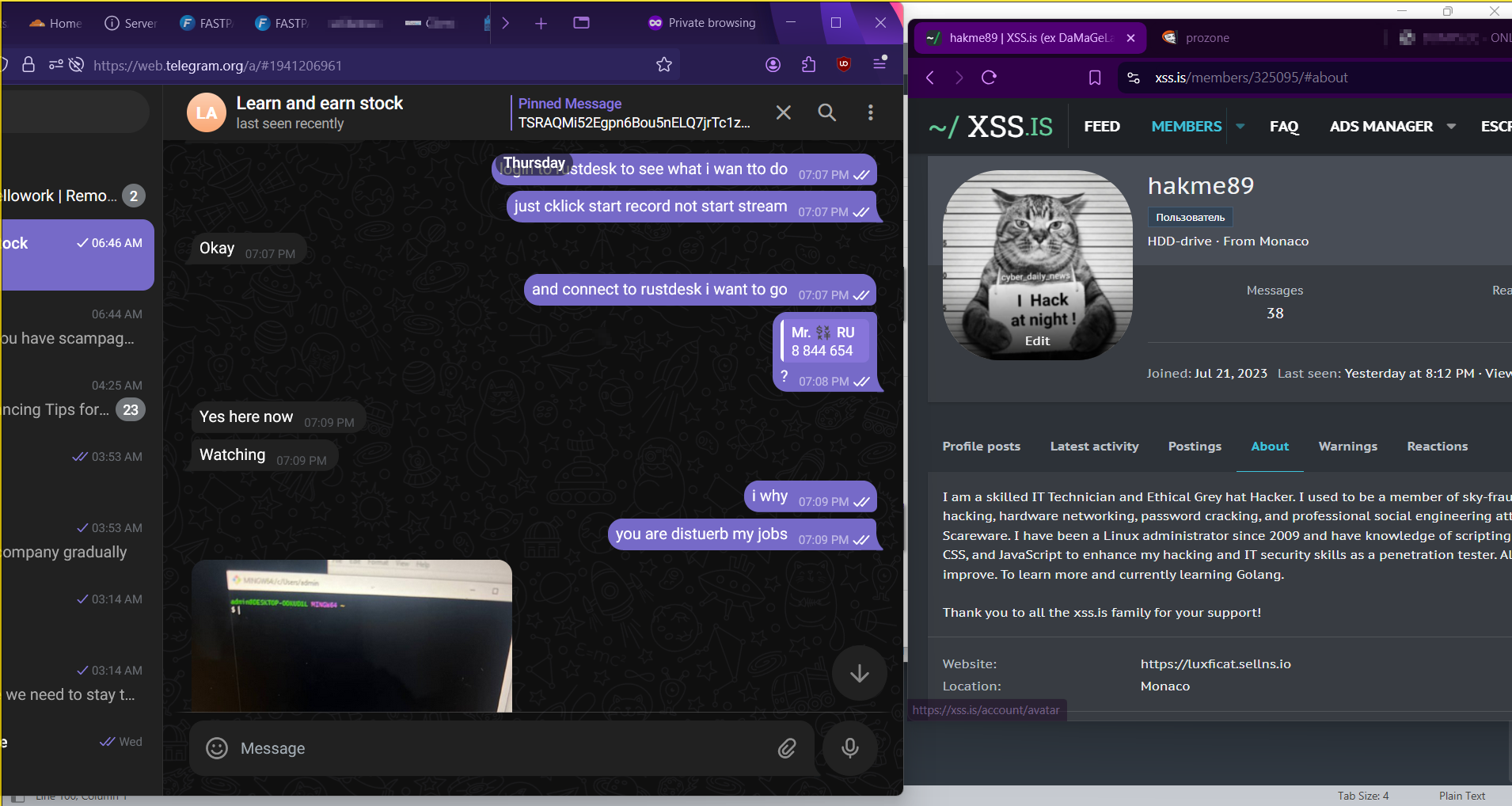
I provide support via RustDesk on RDP with lifetime assistance to ensure that you achieve practical results in improving Your BEC-0.365 Phishing Techniques.
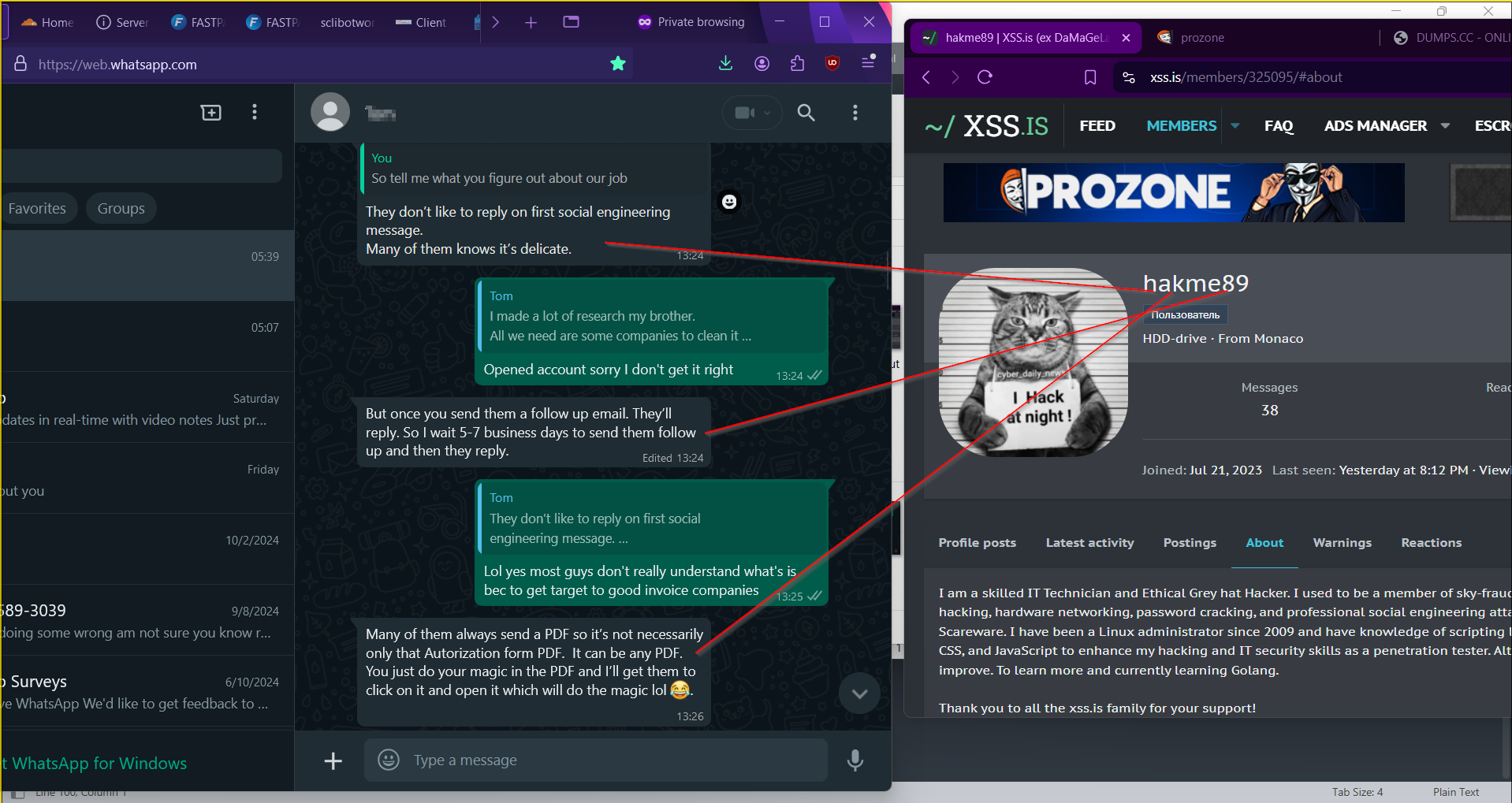
Included is a full list of tools and resources tailored to achieve your goals. This package is aimed at improving your BEC Phishing Techniques and How to get diffrence BEC orgnizations target sector Office 365 Email and their details for SI social engineering. This method is not massive spamming with randomly messages with mailer. it's total different and advance techniques of SI BEC Phishing Method..! you can search my threads about bec i have post full detail how bec works for beginners and intermediate Phishers.
<< ------- ---->>
What is SI and how can we use it to manipulate in bec office365 and gain access to mailbox to achieve wire invoioce as mafia BEC BUYERS..!This method reduce stress and headache of anti spam and no click link, inbox smtp issue, link issue, outlook anti filtering protection.
Social Influence: in BEC Office635 Manipulation Corp Employee for gainning access to their mailbox with Evil cookies this emthod perfect for only Box To Box Setup with their script cookies stealer and Link depend on aspect to use thie link.
Definition:
Social Influence refers to the ways individuals change their thoughts, feelings, or behaviors in response to social interactions or cues. In email manipulation, this involves crafting messages that exploit social norms, emotions, and psychological triggers.
Common Techniques:
Authority: Emails that come from perceived authoritative figures (like a manager or a recognized institution) can compel individuals to comply with requests or share information.
Scarcity: Creating a sense of urgency or scarcity (e.g., "limited-time offer" or "only a few spots left") can push recipients to act quickly without thinking critically.
Reciprocity: Offering something of value (like a free resource or helpful information) can create a sense of obligation for the recipient to respond favorably.
Social Proof: Including testimonials, reviews, or examples of others taking action can persuade individuals to follow suit.
Examples of Manipulative Emails:
Phishing Scams: Emails that appear to come from trusted sources, asking for sensitive information by playing on fears (e.g., account suspensions) or urgency (e.g., “immediate action required”).
Impersonation: Emails that imitate a colleague or supervisor to extract confidential information, often citing a need for help or quick response.
Fake Surveys: Emails asking recipients to participate in surveys, with the intention of gathering personal data under the guise of research.
Prevention and Awareness:
Critical Thinking: Encourage individuals to critically assess emails, especially those that invoke strong emotions or urgent actions.
Verification: Establishing processes for verifying requests, such as confirming with the supposed sender through a separate communication channel.
Training: Providing training on recognizing social influence tactics can help individuals resist manipulation attempts.
<< ----------------- >>
Here is Advanced Basic Tools Needed!! and Service Web Tools Online:
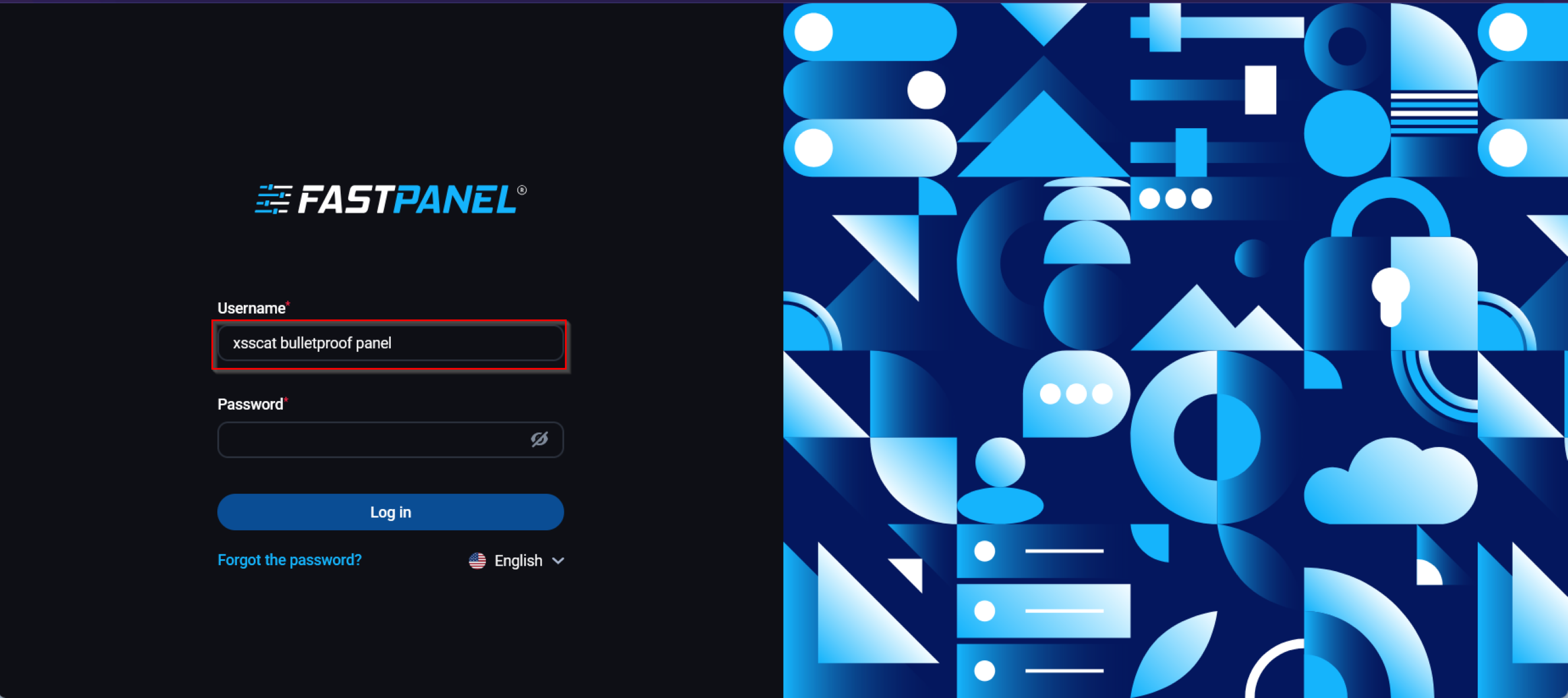
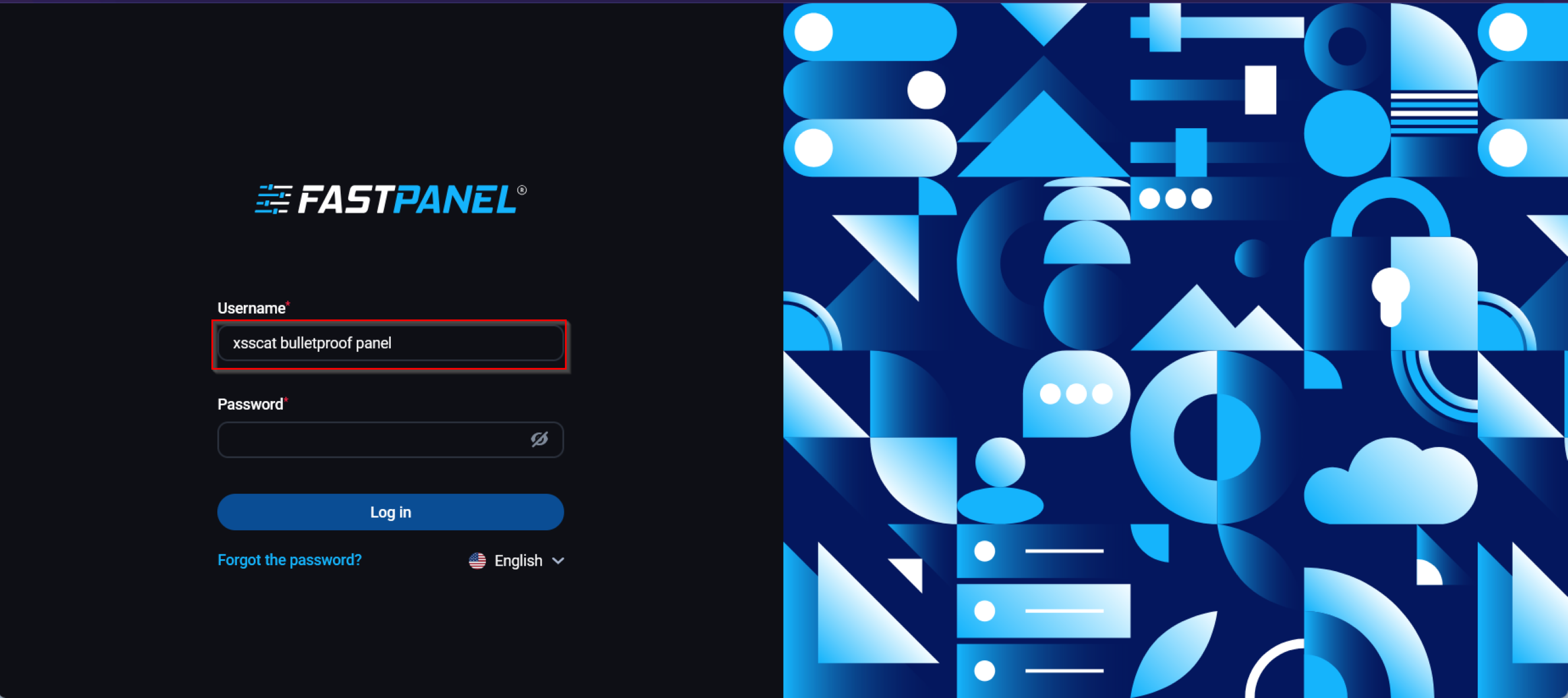
 1- Monthly bulletproof link + Script page & cookies stealer
1- Monthly bulletproof link + Script page & cookies stealer
2- Strong RDP 8gb 4cpu 2 needed
 3- Mass-Mailer script to make private single Email phishing or massive mailling but not recommended massive mailling, with randomly commond email spam
3- Mass-Mailer script to make private single Email phishing or massive mailling but not recommended massive mailling, with randomly commond email spam
 4- Bot-killer + Smart-Link apikey + host webpanel obfuscastor url redirect
4- Bot-killer + Smart-Link apikey + host webpanel obfuscastor url redirect
5- bulletproof domain
 6- Html letter words encryptor + subject + sender name
6- Html letter words encryptor + subject + sender name
7- Paid proton vpn
8- 3 domains needed
 9- How to create SI Social Engineering Letter plain Text or Html
9- How to create SI Social Engineering Letter plain Text or Html
 10- Pyhton script for corp website database scraping
10- Pyhton script for corp website database scraping
 11- Cloudflare free plan
11- Cloudflare free plan
 12- office365 email validator script
12- office365 email validator script
 13-Debounce leads mailbox checker validator + New API
13-Debounce leads mailbox checker validator + New API
14-Spam words checker tool free ( )
15- words encryptor script free
16- ChatGPT you can create yourself
 17- Office365 Log, Edu Corp 0.365 Box or Business Corp 0.365 Box needed for {Box To Box}
17- Office365 Log, Edu Corp 0.365 Box or Business Corp 0.365 Box needed for {Box To Box}
18- Yahoo financial account
19- Google cloud account needed you can create one self with live cc.
 20 Office365 attachment invoice.pdf.docs browser for cookies stealer payload is auto redirect download + Window avs Bypass
20 Office365 attachment invoice.pdf.docs browser for cookies stealer payload is auto redirect download + Window avs Bypass
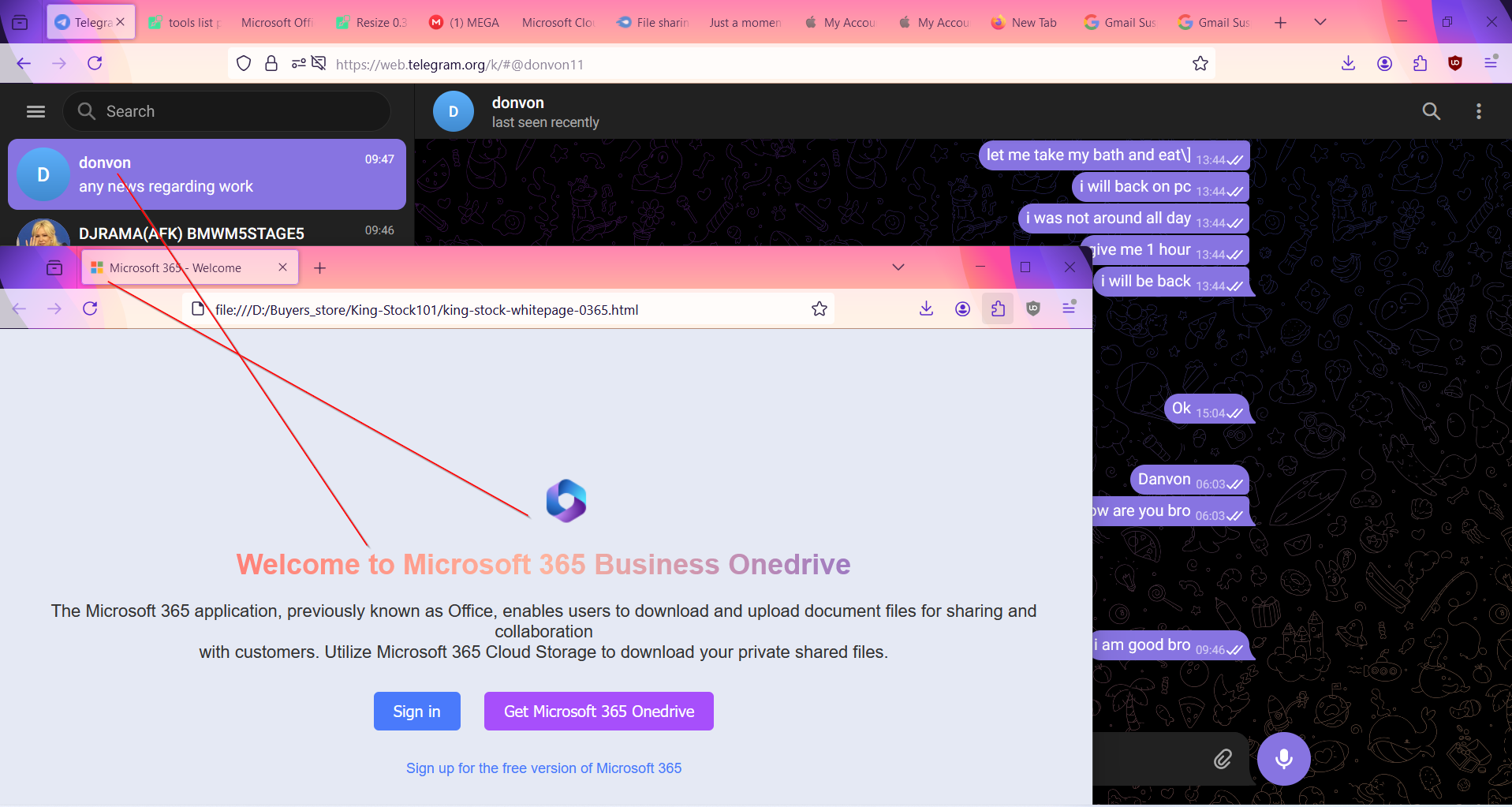
 21. Apollo Web tool you can create yourself with virtual card..!
21. Apollo Web tool you can create yourself with virtual card..!
 22. datanyze Chrome Extension
22. datanyze Chrome Extension
====================
Here is Short live Video of BEC SI Tutorial and spam setup: 10/16/2024 - 10/17/2024
1vd- https://gofile.io/d/0zSDke
2vd- https://gofile.io/d/T8t3T1
Private with key not for public DM for key.
<< ------------- >>
This is educational purpose To safeguard your organization
Conclusion
Understanding social influence in email manipulation can help individuals and organizations protect themselves from scams and deceptive practices. Awareness of these techniques can empower recipients to make more informed decisions and avoid falling victim to manipulative tactics.
<< ----------------- >>
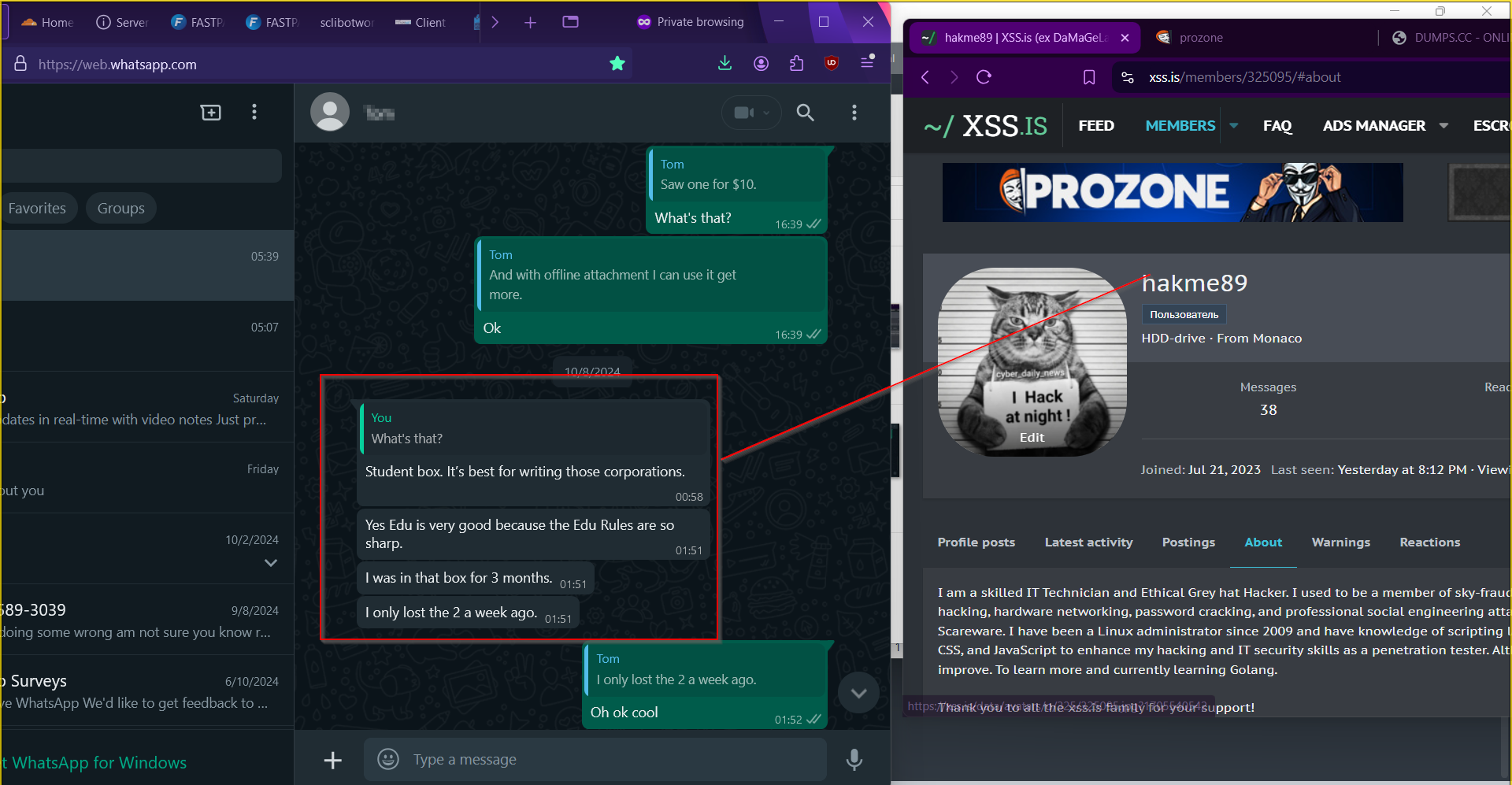
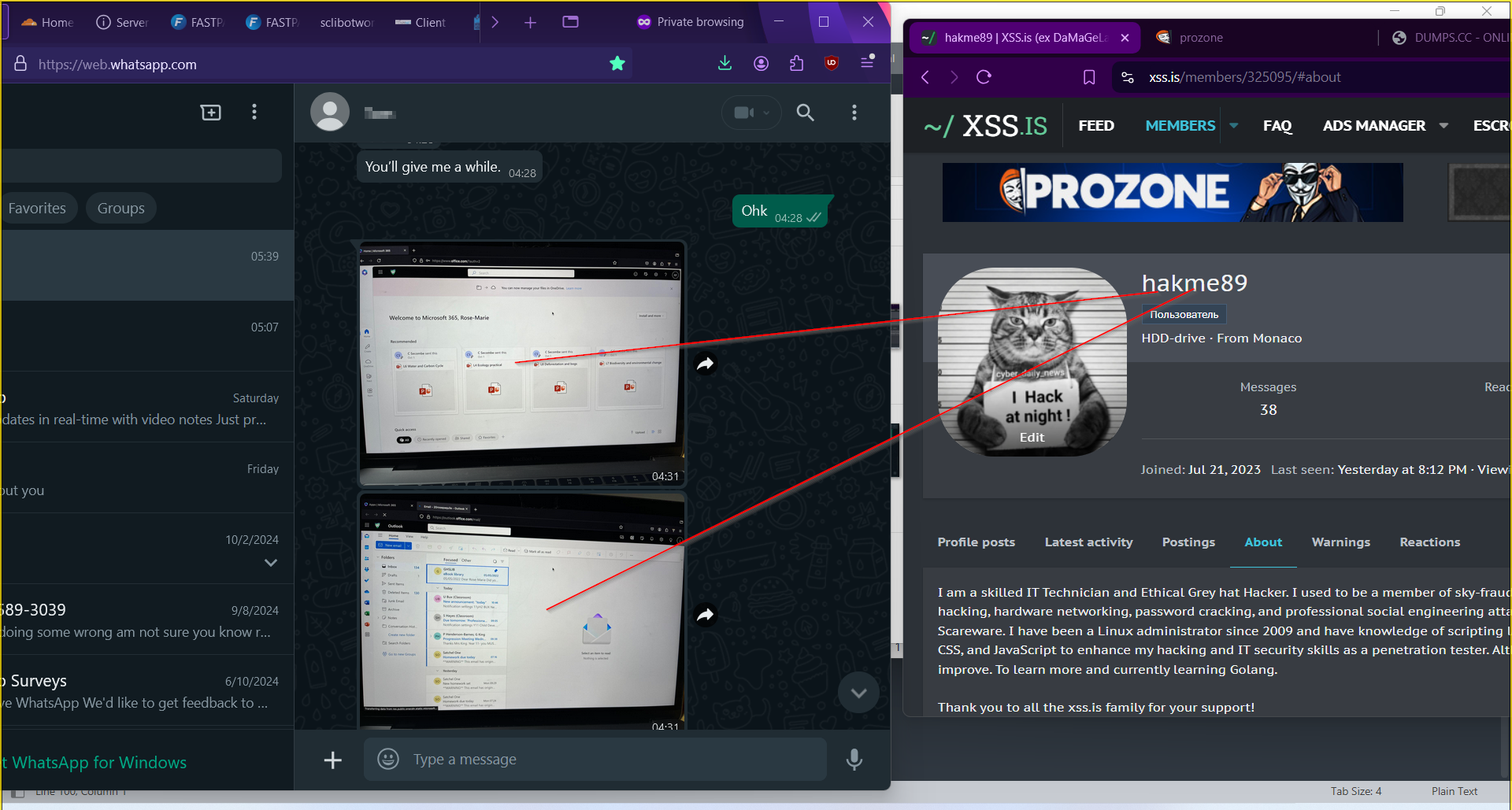
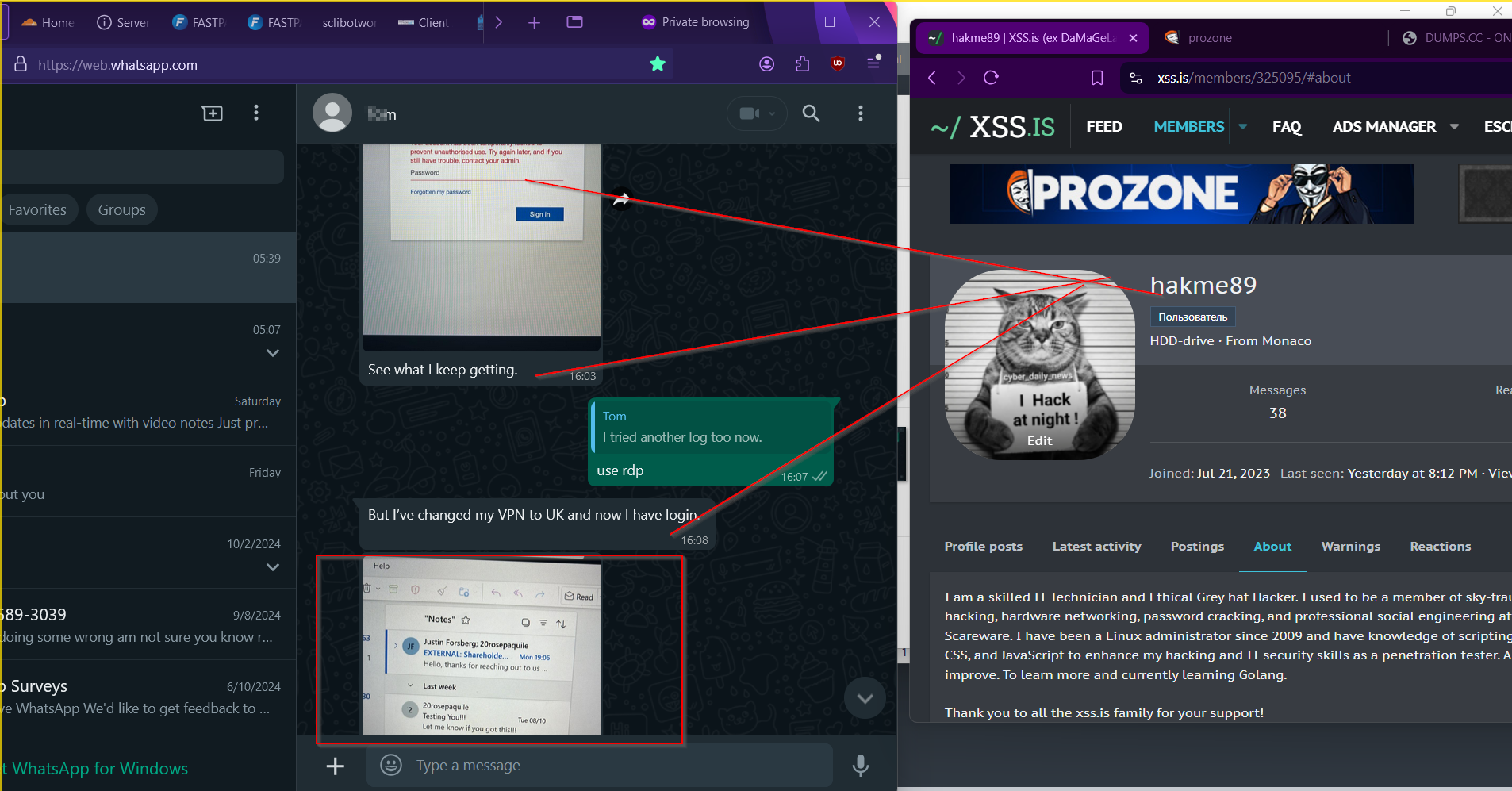
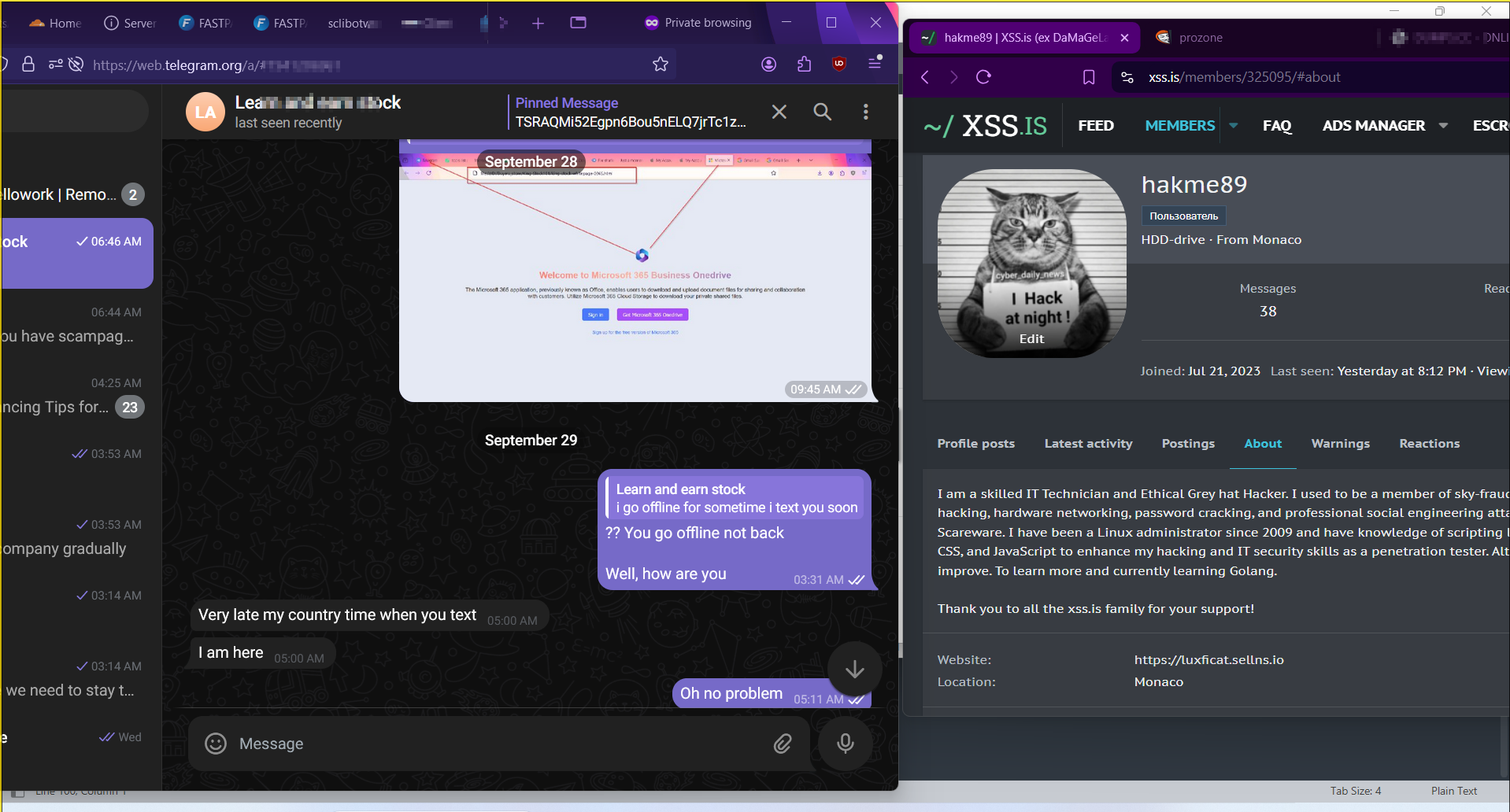
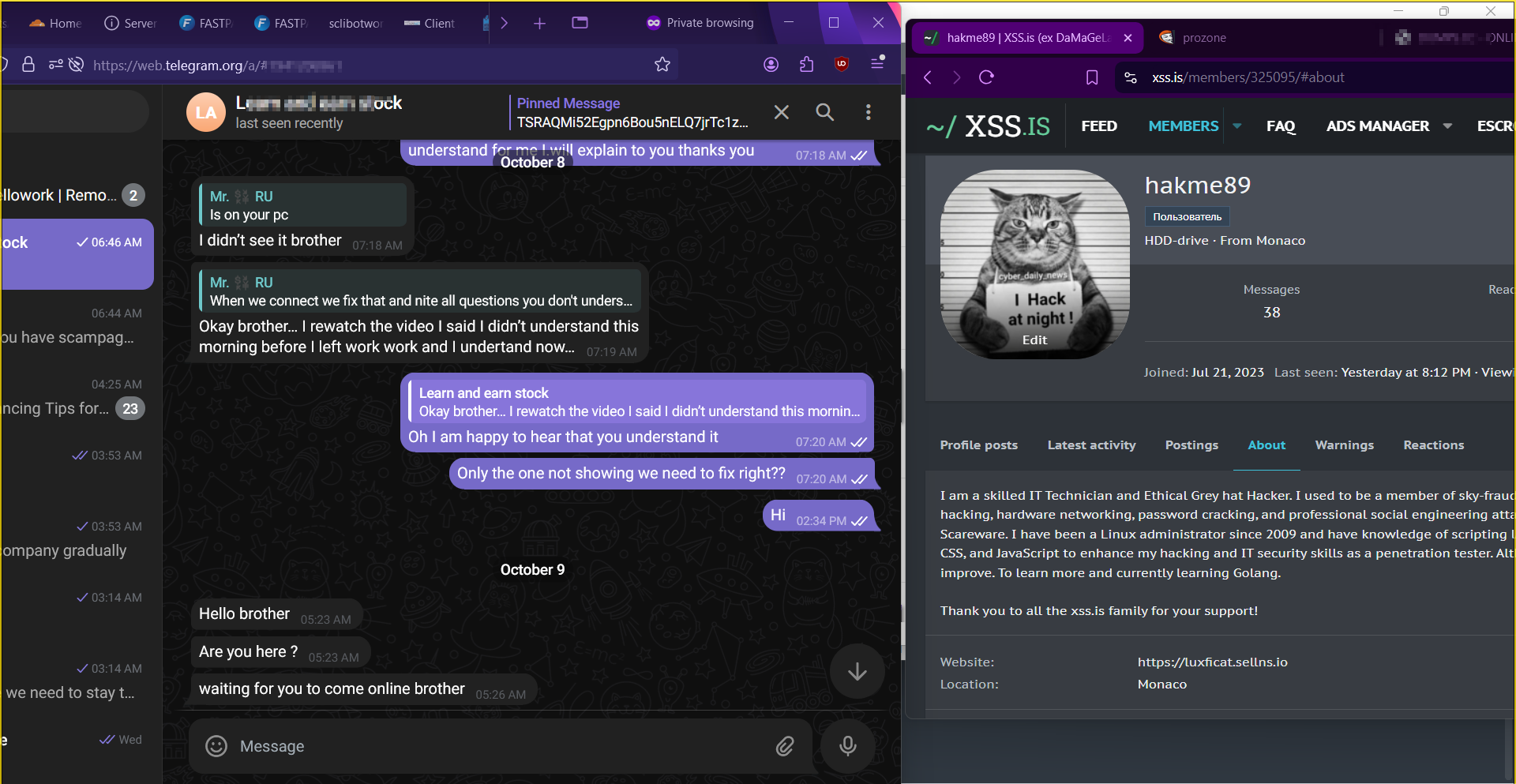
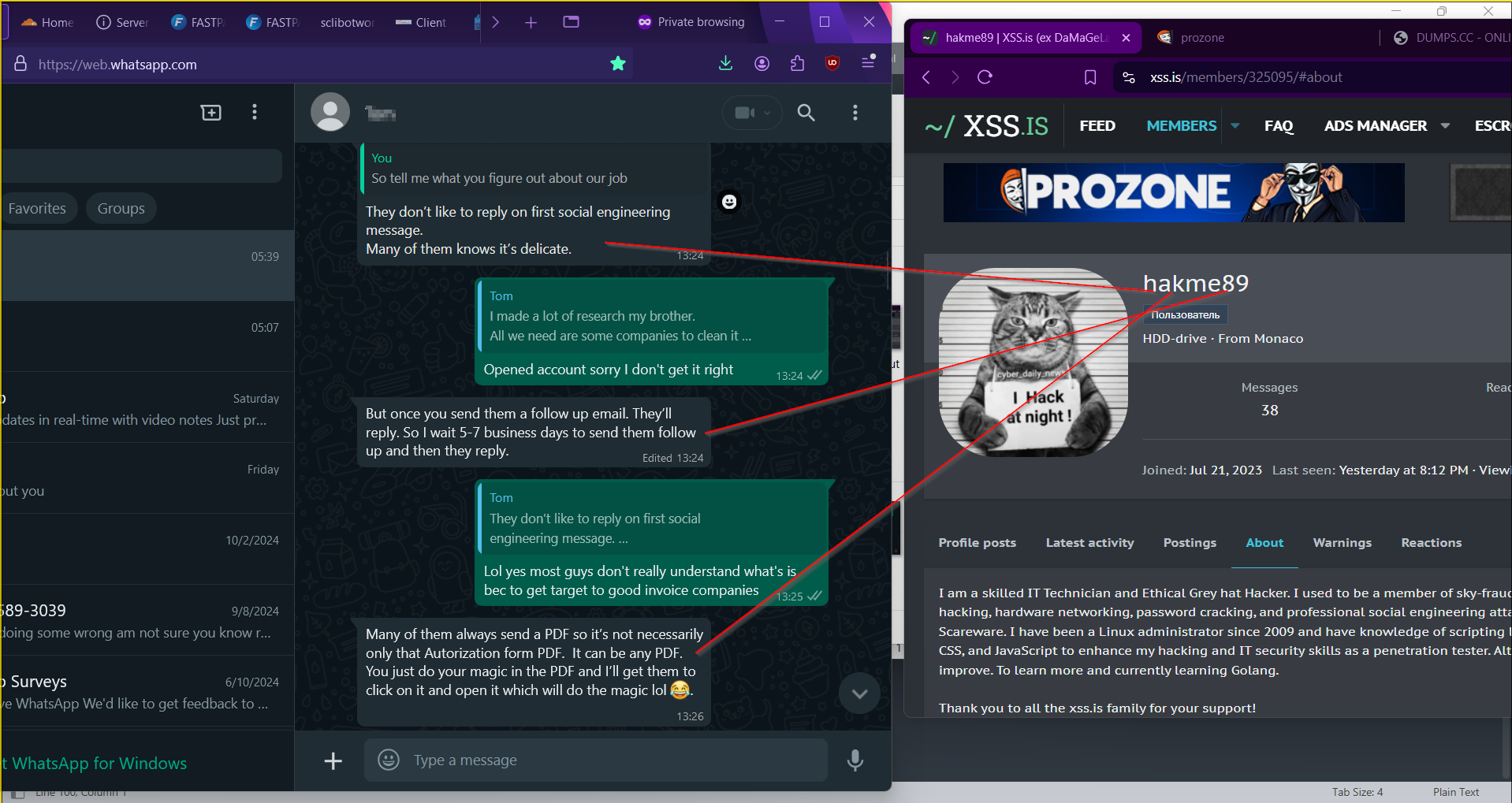
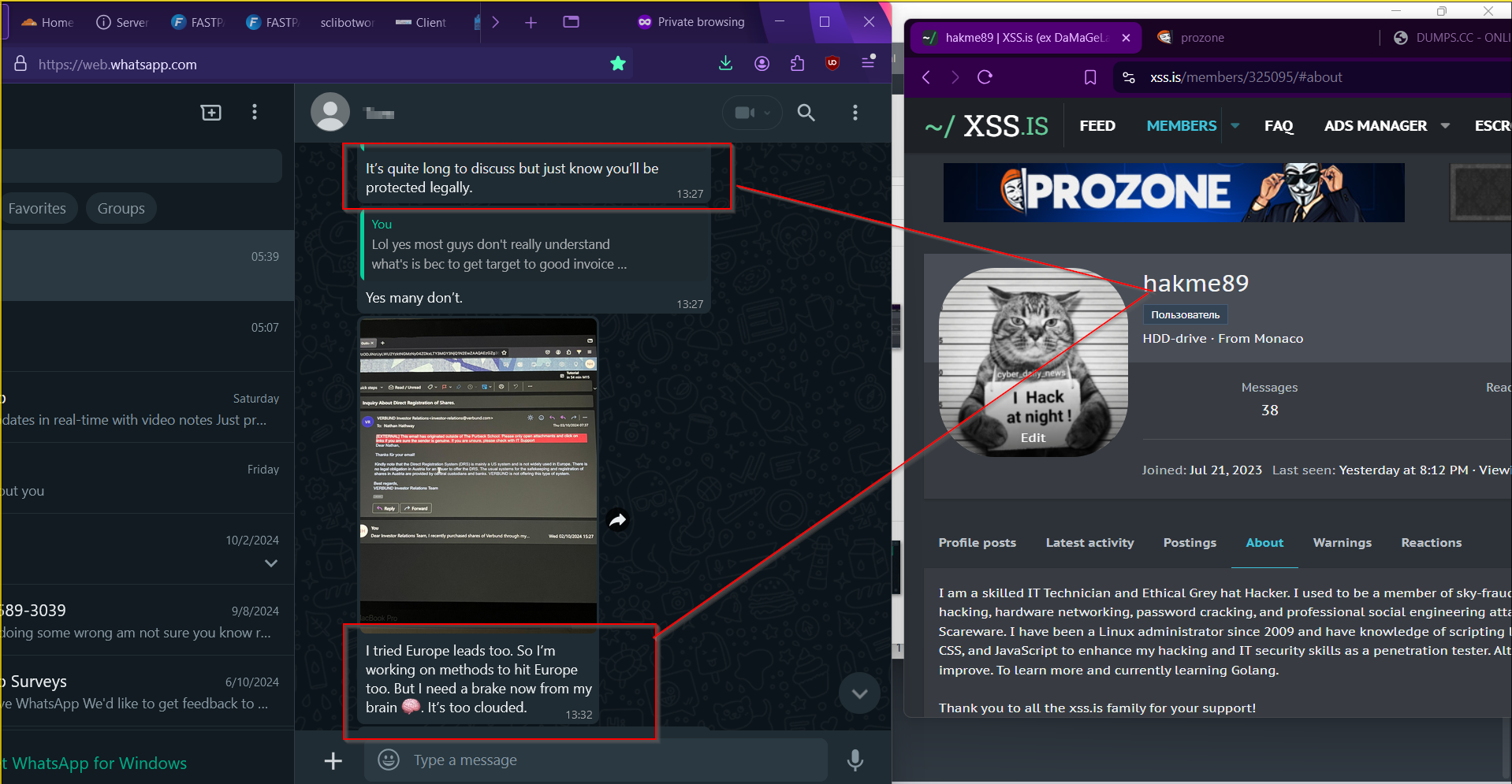
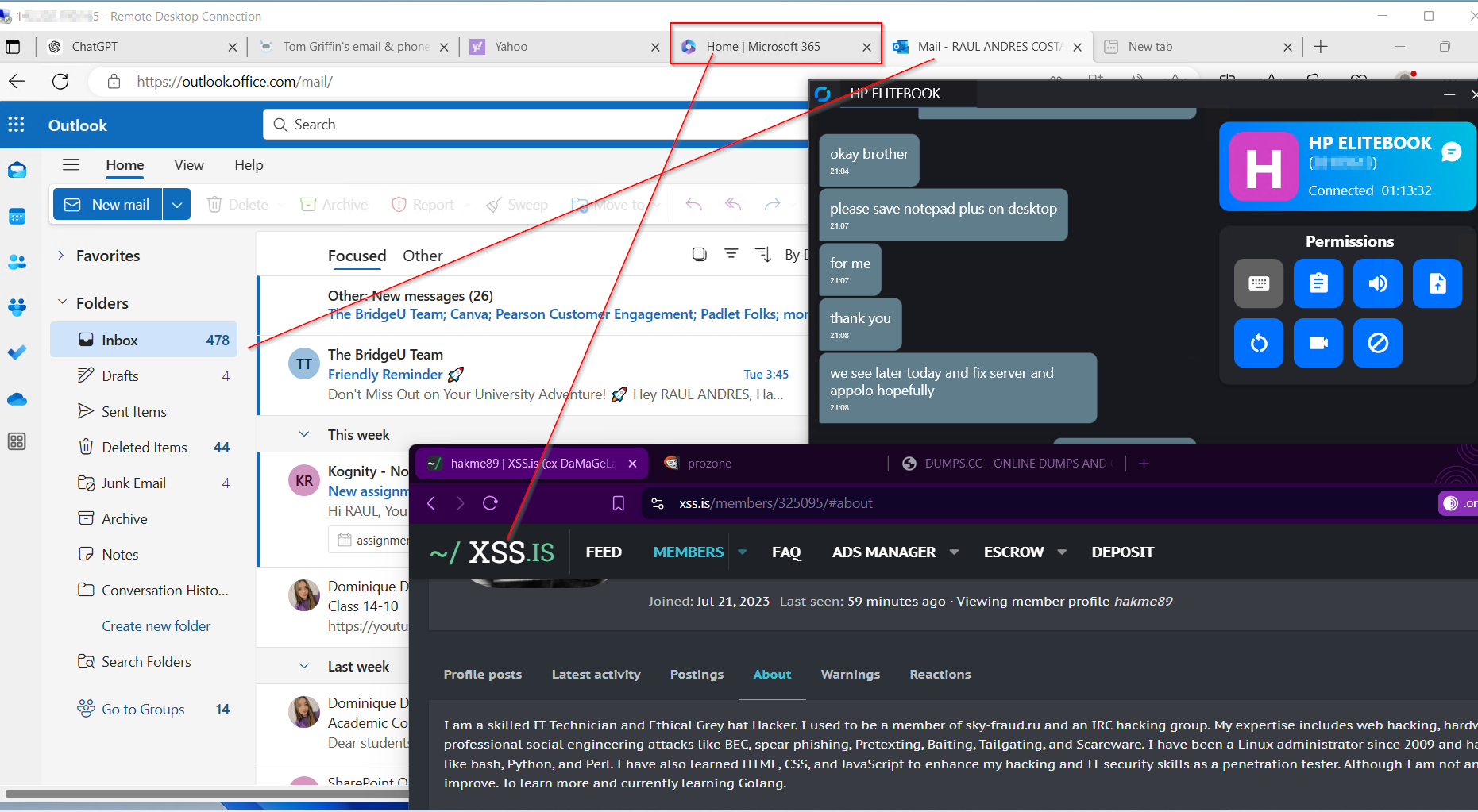
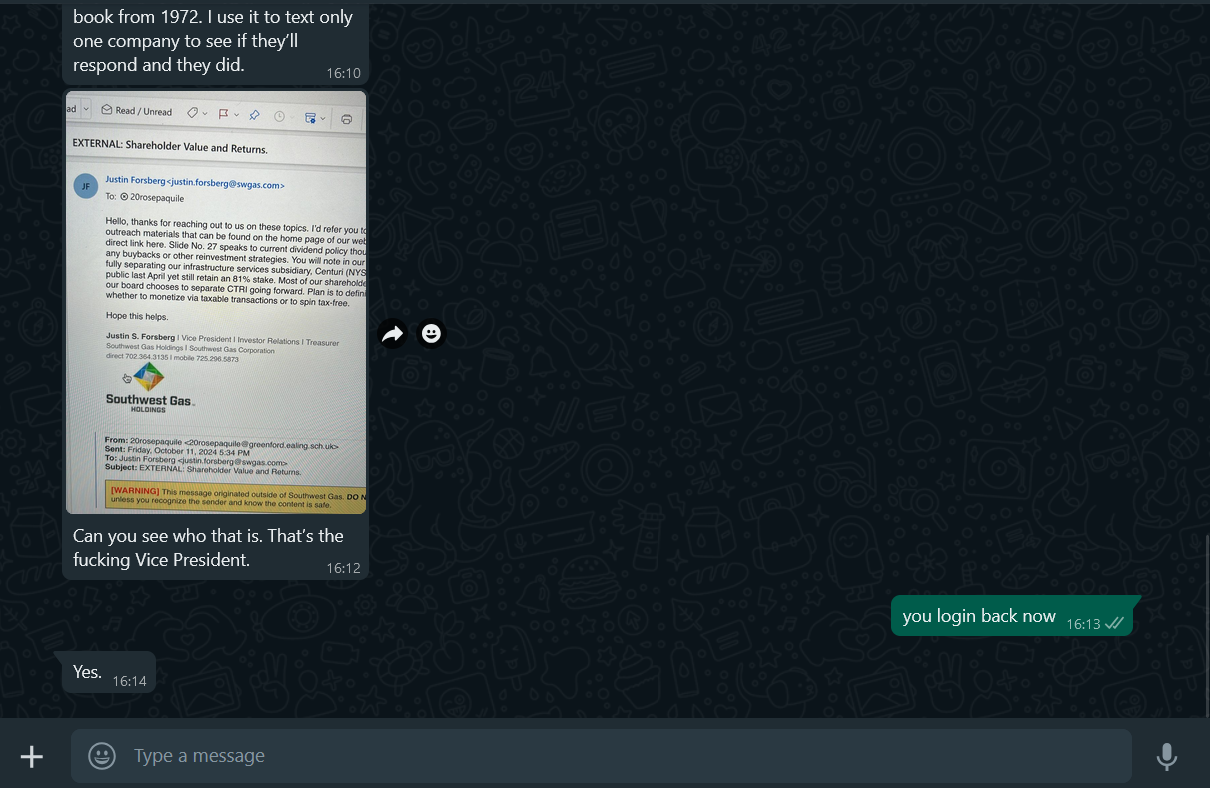
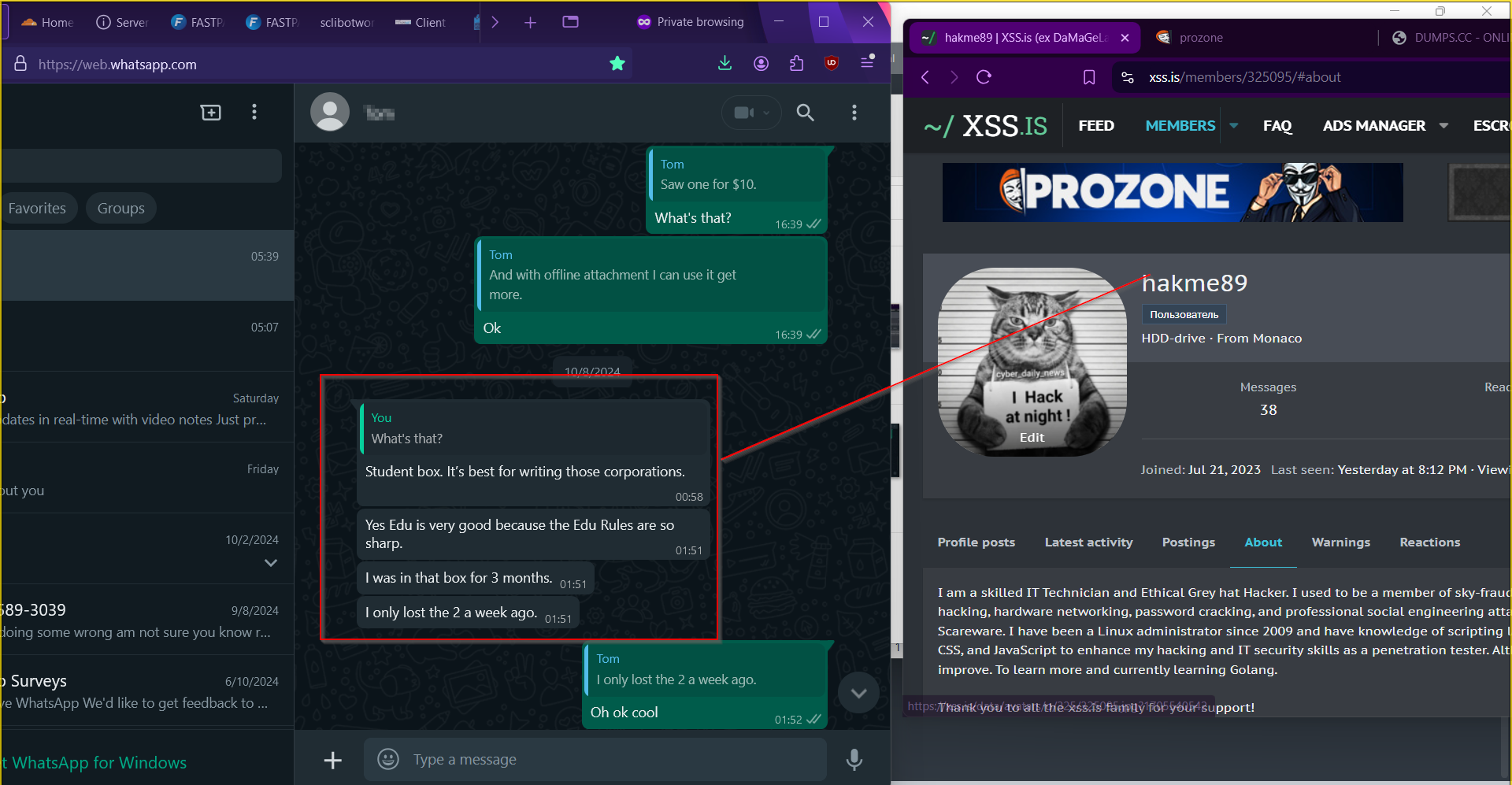
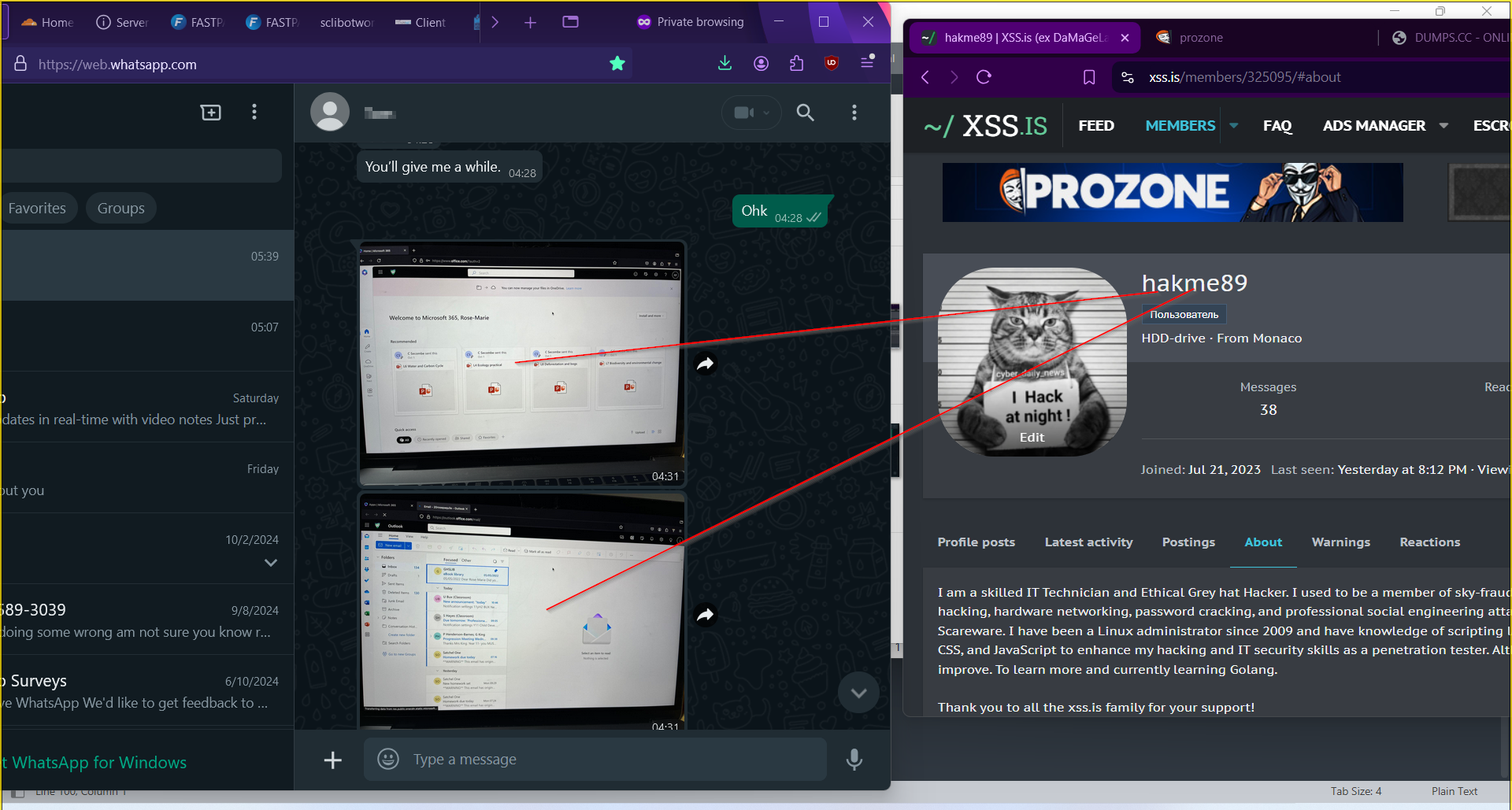
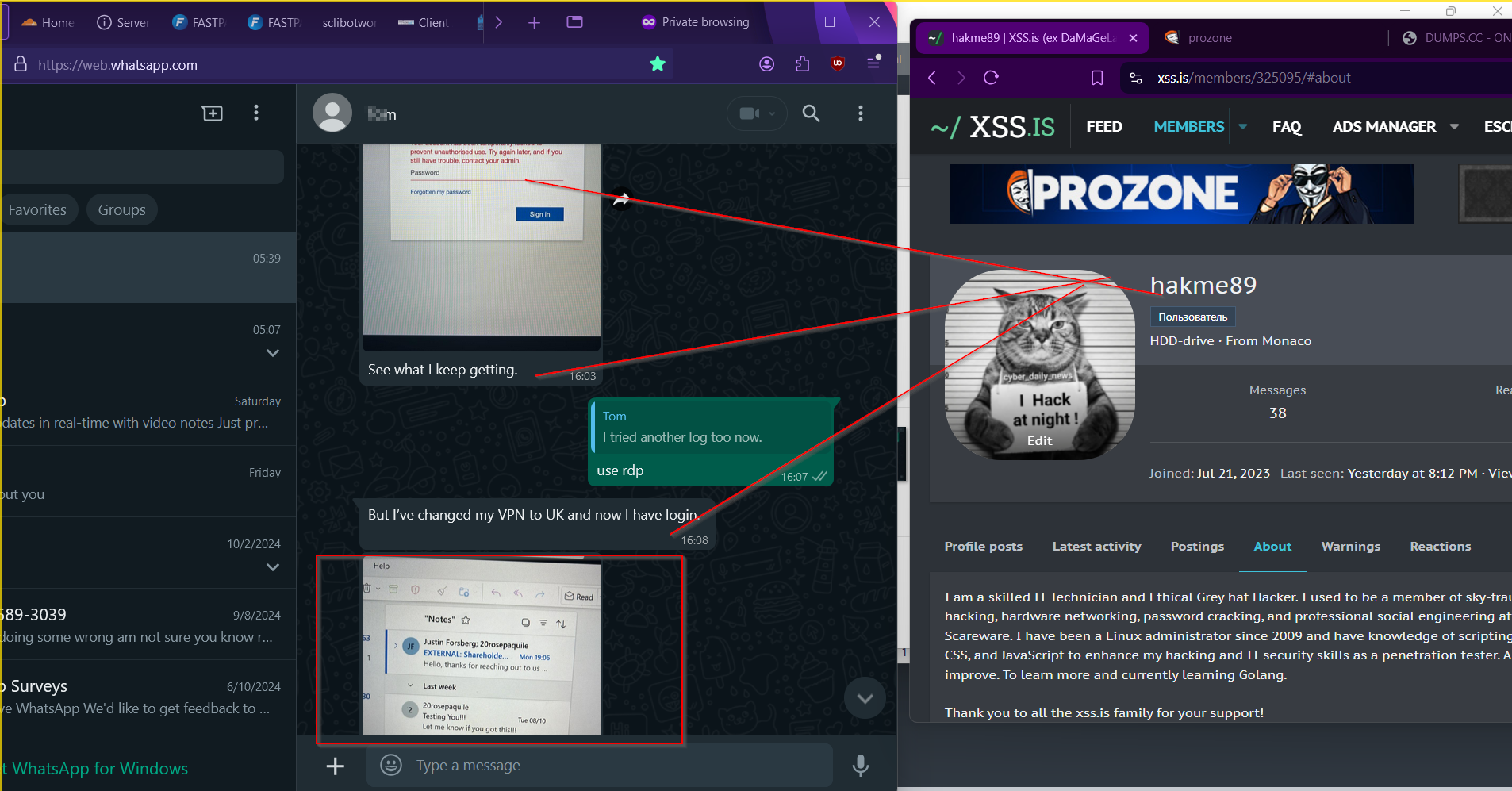
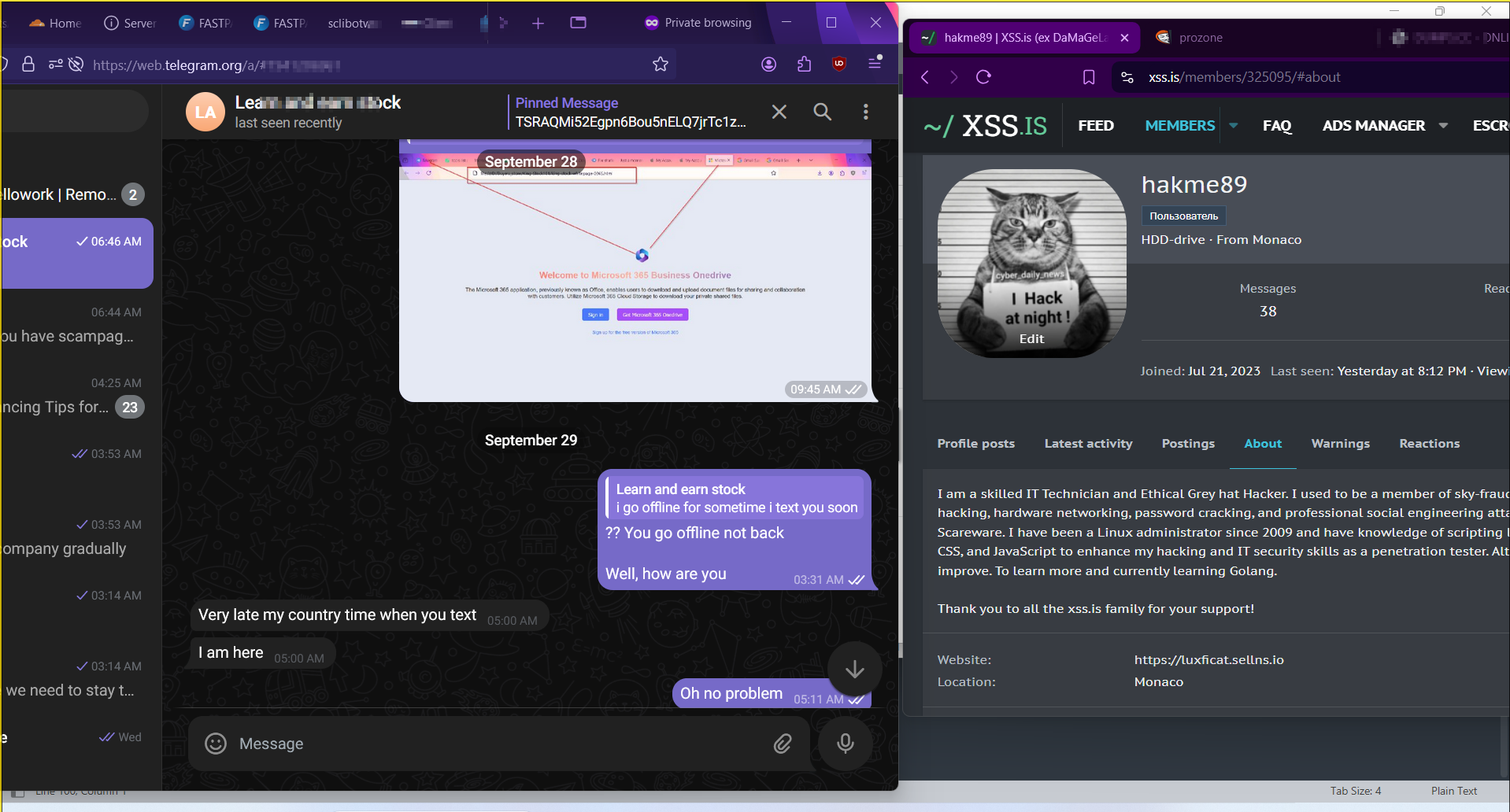
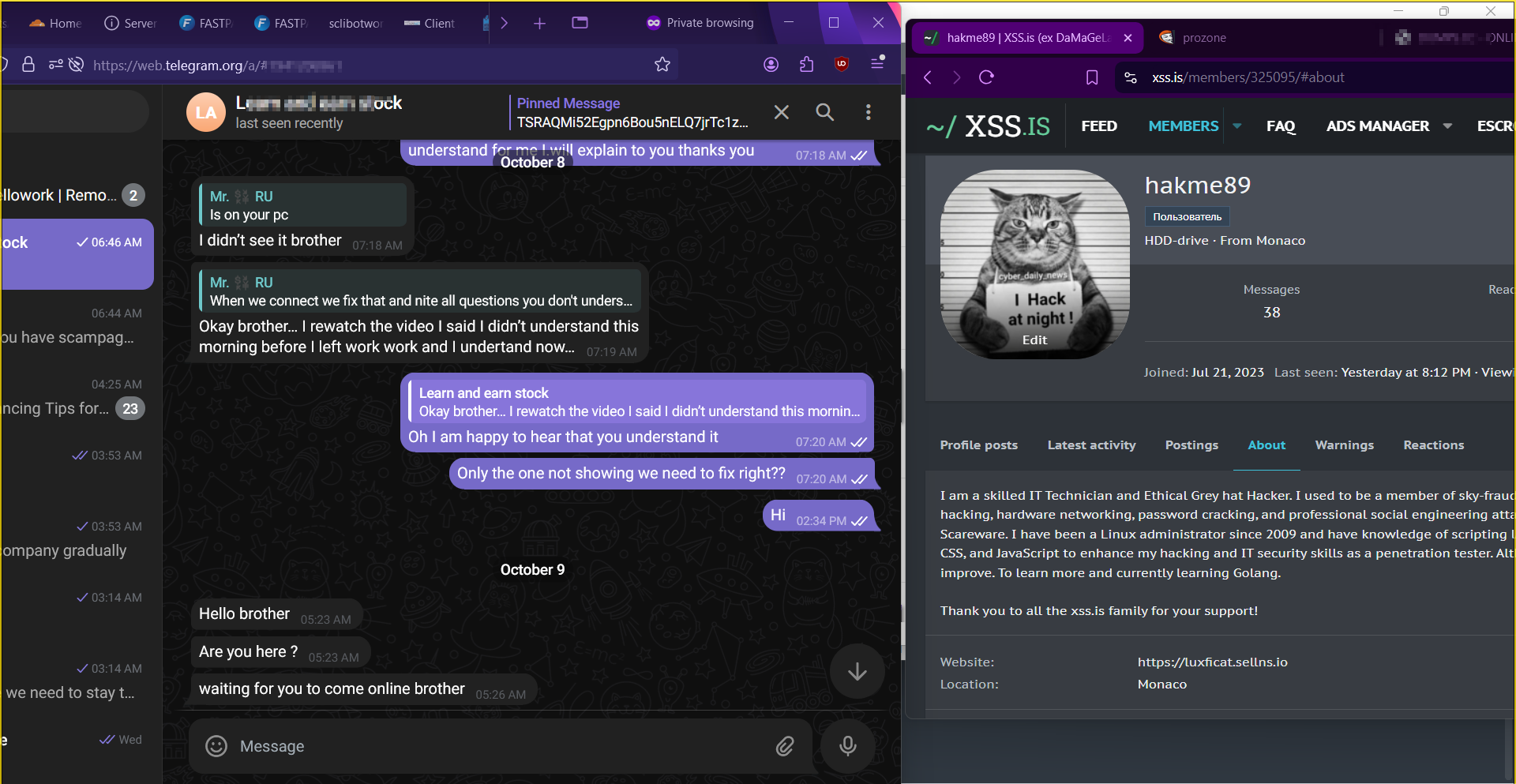
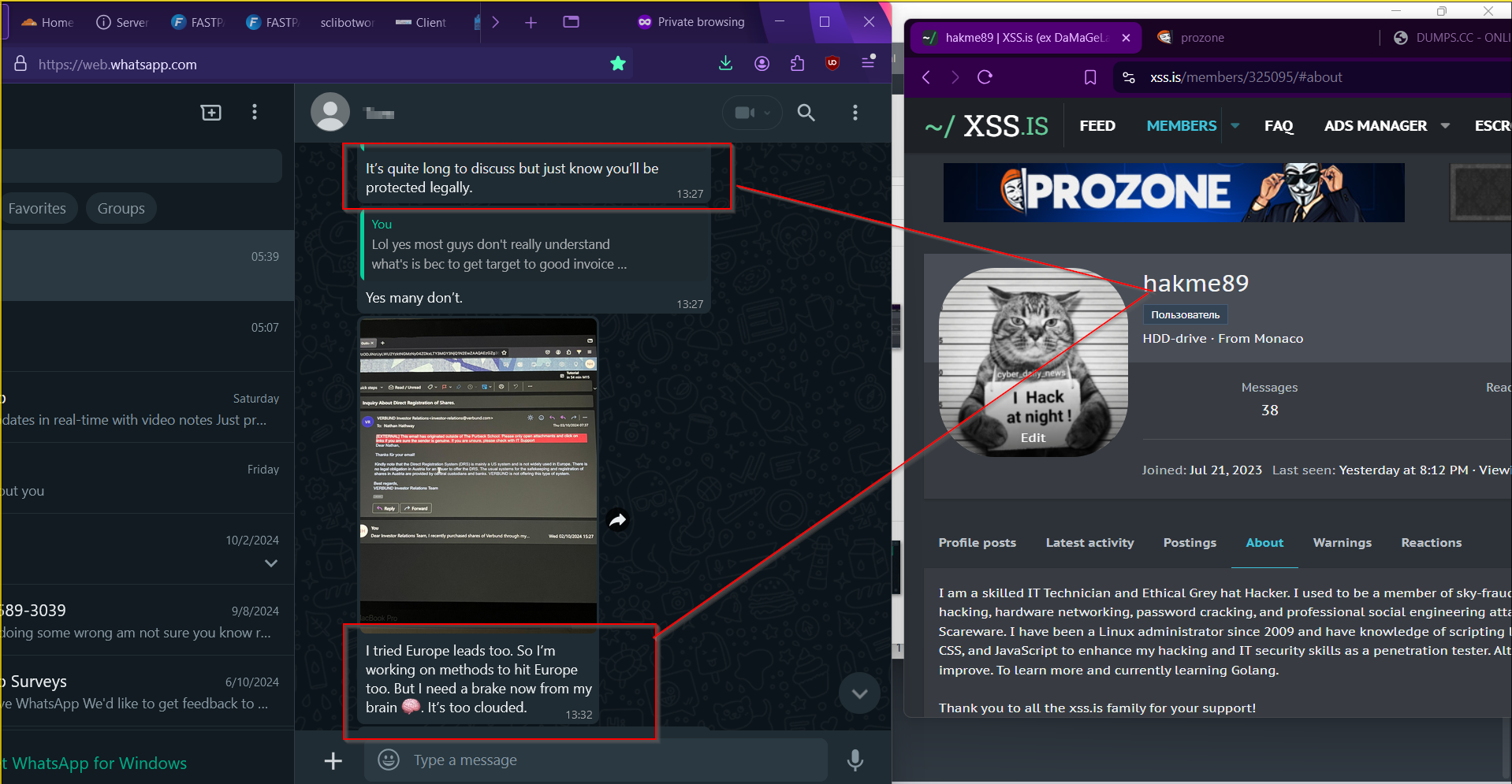
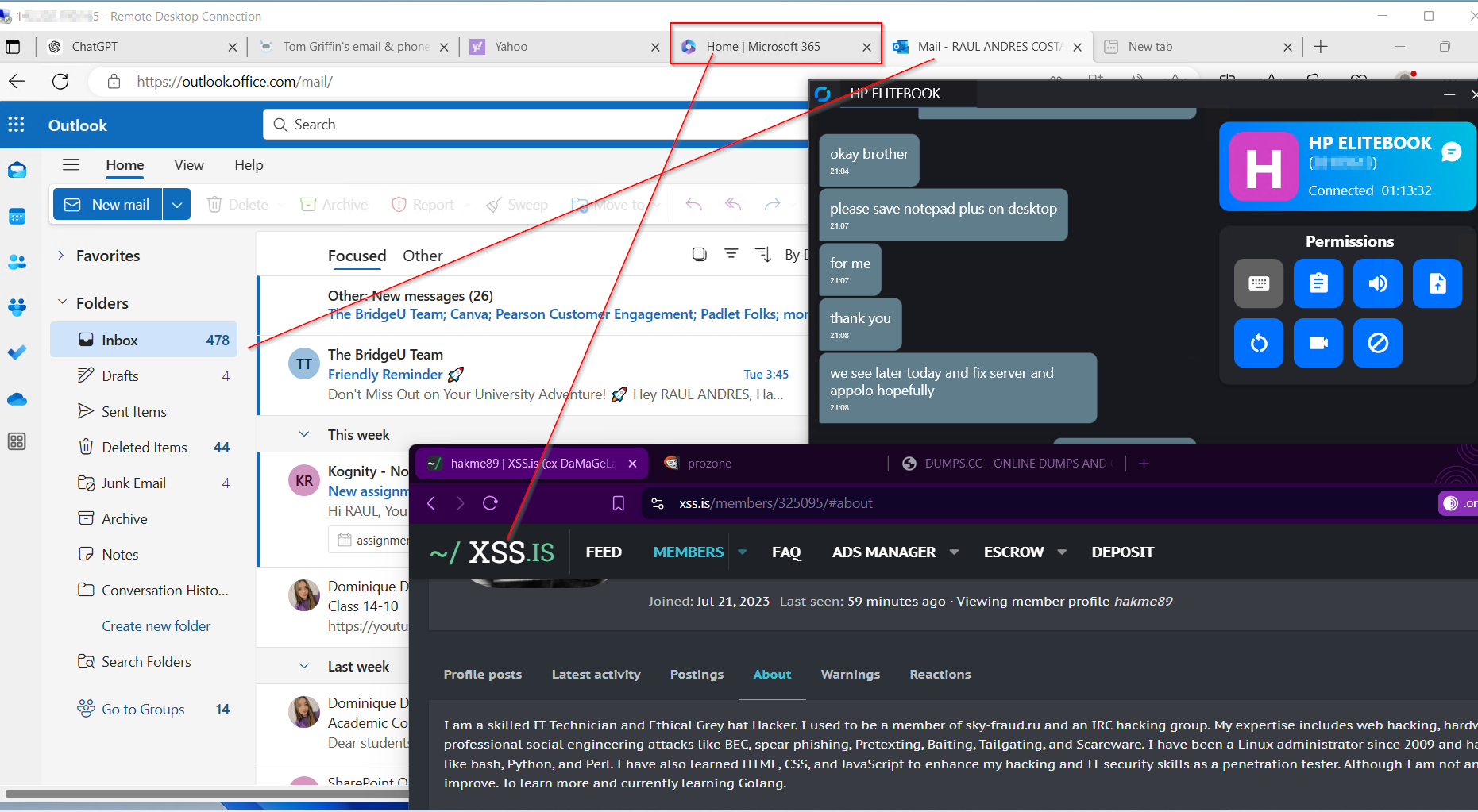
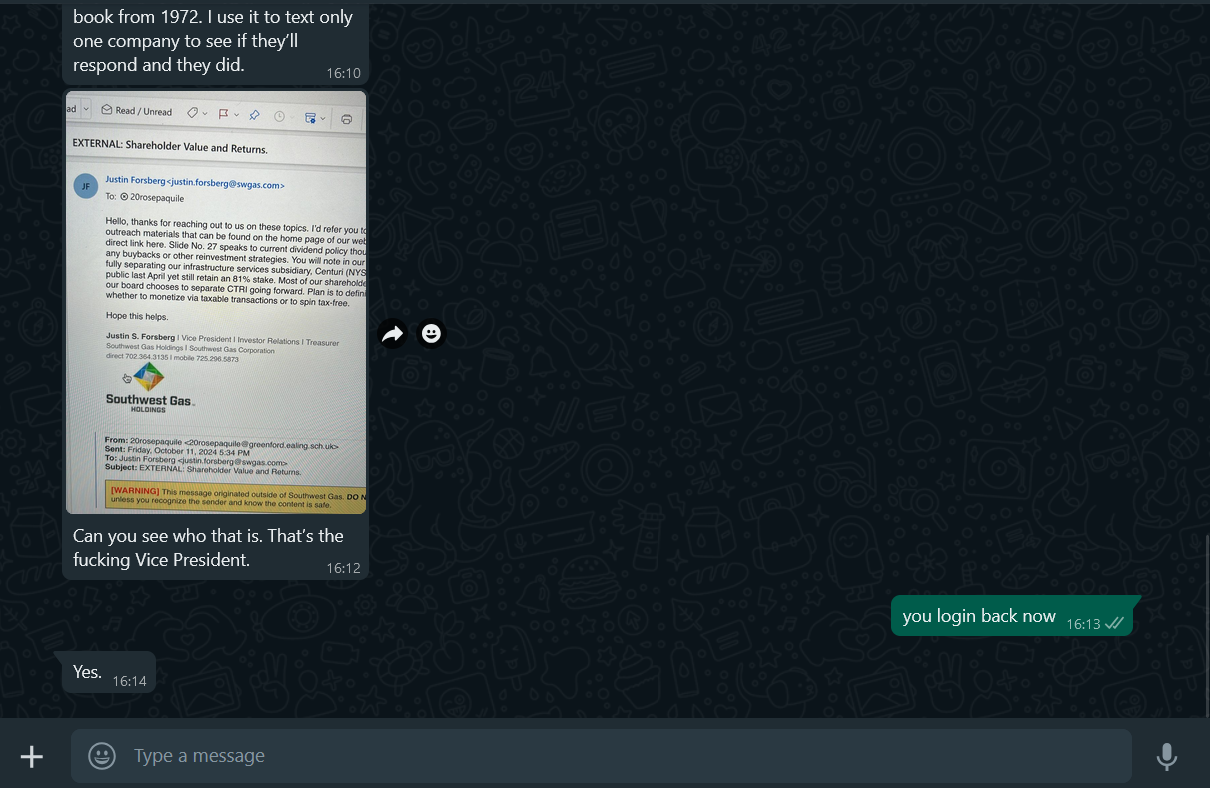
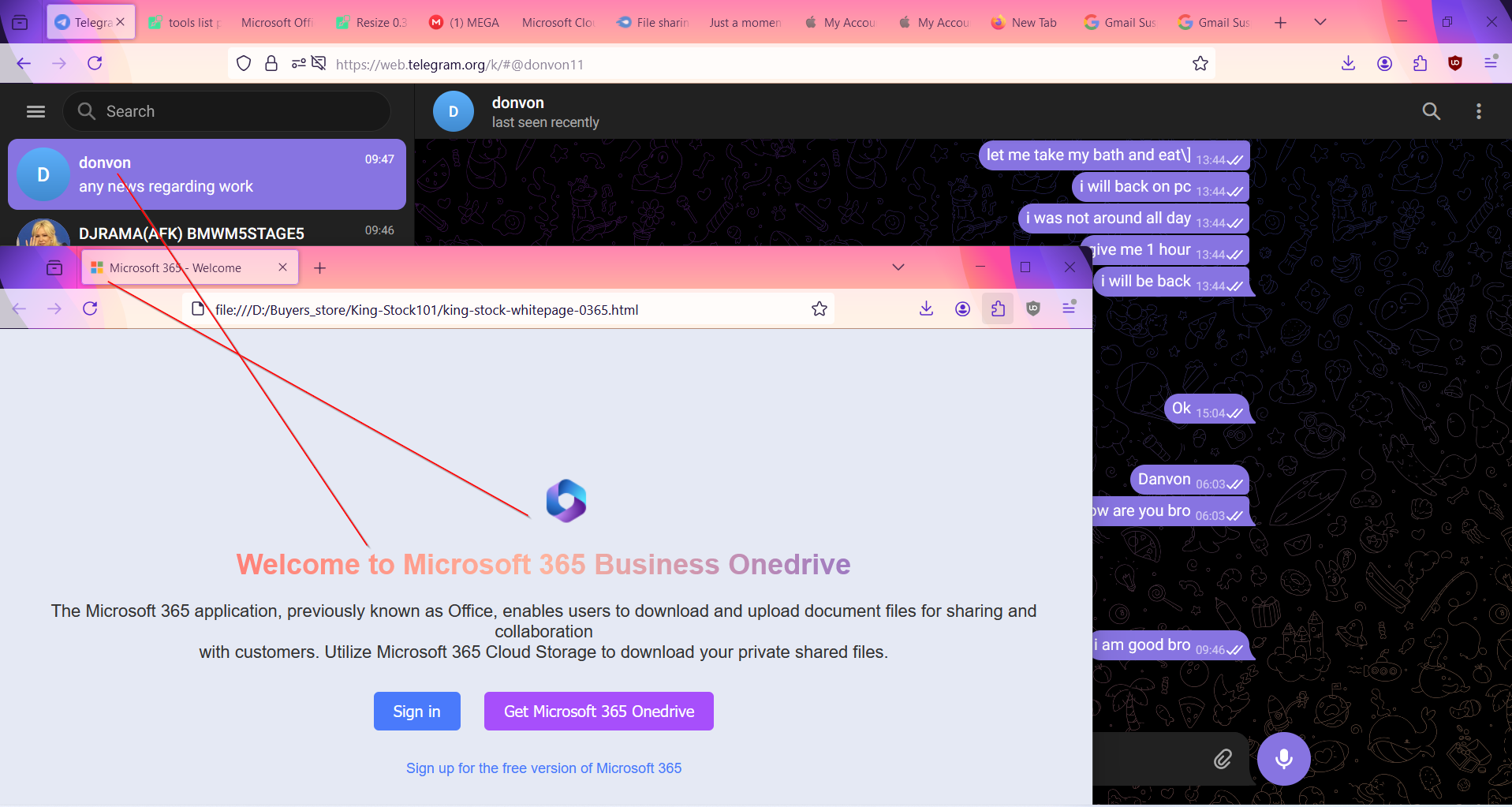
Some BEC setup buyer proof and testimony:
 Happy hacking and Phishing Techniques to all xss.pro Member's read thread's.. have a wonderful cashout weekend
Happy hacking and Phishing Techniques to all xss.pro Member's read thread's.. have a wonderful cashout weekend
I am offering a comprehensive Advanced Office 365 Tutorial focusing on BEC (Business Email Compromise) prevention for educational purposes. This package includes detailed methods, BEC tools, and a step-by-step setup guide to enhance your understanding of how BEC attacks work and how to Bypass the secuirty reuls, Bot filtering, isp mailling trafic bot scan, vpn-bot killer etc.
I provide support via RustDesk on RDP with lifetime assistance to ensure that you achieve practical results in improving Your BEC-0.365 Phishing Techniques.
Included is a full list of tools and resources tailored to achieve your goals. This package is aimed at improving your BEC Phishing Techniques and How to get diffrence BEC orgnizations target sector Office 365 Email and their details for SI social engineering. This method is not massive spamming with randomly messages with mailer. it's total different and advance techniques of SI BEC Phishing Method..! you can search my threads about bec i have post full detail how bec works for beginners and intermediate Phishers.
<< ------- ---->>
What is SI and how can we use it to manipulate in bec office365 and gain access to mailbox to achieve wire invoioce as mafia BEC BUYERS..!This method reduce stress and headache of anti spam and no click link, inbox smtp issue, link issue, outlook anti filtering protection.
Social Influence: in BEC Office635 Manipulation Corp Employee for gainning access to their mailbox with Evil cookies this emthod perfect for only Box To Box Setup with their script cookies stealer and Link depend on aspect to use thie link.
Definition:
Social Influence refers to the ways individuals change their thoughts, feelings, or behaviors in response to social interactions or cues. In email manipulation, this involves crafting messages that exploit social norms, emotions, and psychological triggers.
Common Techniques:
Authority: Emails that come from perceived authoritative figures (like a manager or a recognized institution) can compel individuals to comply with requests or share information.
Scarcity: Creating a sense of urgency or scarcity (e.g., "limited-time offer" or "only a few spots left") can push recipients to act quickly without thinking critically.
Reciprocity: Offering something of value (like a free resource or helpful information) can create a sense of obligation for the recipient to respond favorably.
Social Proof: Including testimonials, reviews, or examples of others taking action can persuade individuals to follow suit.
Examples of Manipulative Emails:
Phishing Scams: Emails that appear to come from trusted sources, asking for sensitive information by playing on fears (e.g., account suspensions) or urgency (e.g., “immediate action required”).
Impersonation: Emails that imitate a colleague or supervisor to extract confidential information, often citing a need for help or quick response.
Fake Surveys: Emails asking recipients to participate in surveys, with the intention of gathering personal data under the guise of research.
Prevention and Awareness:
Critical Thinking: Encourage individuals to critically assess emails, especially those that invoke strong emotions or urgent actions.
Verification: Establishing processes for verifying requests, such as confirming with the supposed sender through a separate communication channel.
Training: Providing training on recognizing social influence tactics can help individuals resist manipulation attempts.
<< ----------------- >>
Here is Advanced Basic Tools Needed!! and Service Web Tools Online:
 1- Monthly bulletproof link + Script page & cookies stealer
1- Monthly bulletproof link + Script page & cookies stealer 2- Strong RDP 8gb 4cpu 2 needed
 3- Mass-Mailer script to make private single Email phishing or massive mailling but not recommended massive mailling, with randomly commond email spam
3- Mass-Mailer script to make private single Email phishing or massive mailling but not recommended massive mailling, with randomly commond email spam 4- Bot-killer + Smart-Link apikey + host webpanel obfuscastor url redirect
4- Bot-killer + Smart-Link apikey + host webpanel obfuscastor url redirect 5- bulletproof domain
 6- Html letter words encryptor + subject + sender name
6- Html letter words encryptor + subject + sender name7- Paid proton vpn
8- 3 domains needed
 9- How to create SI Social Engineering Letter plain Text or Html
9- How to create SI Social Engineering Letter plain Text or Html  10- Pyhton script for corp website database scraping
10- Pyhton script for corp website database scraping 11- Cloudflare free plan
11- Cloudflare free plan 12- office365 email validator script
12- office365 email validator script 13-Debounce leads mailbox checker validator + New API
13-Debounce leads mailbox checker validator + New API 14-Spam words checker tool free ( )
15- words encryptor script free
16- ChatGPT you can create yourself
 17- Office365 Log, Edu Corp 0.365 Box or Business Corp 0.365 Box needed for {Box To Box}
17- Office365 Log, Edu Corp 0.365 Box or Business Corp 0.365 Box needed for {Box To Box}18- Yahoo financial account
19- Google cloud account needed you can create one self with live cc.
 20 Office365 attachment invoice.pdf.docs browser for cookies stealer payload is auto redirect download + Window avs Bypass
20 Office365 attachment invoice.pdf.docs browser for cookies stealer payload is auto redirect download + Window avs Bypass 21. Apollo Web tool you can create yourself with virtual card..!
21. Apollo Web tool you can create yourself with virtual card..! 22. datanyze Chrome Extension
22. datanyze Chrome Extension====================
Here is Short live Video of BEC SI Tutorial and spam setup: 10/16/2024 - 10/17/2024
1vd- https://gofile.io/d/0zSDke
2vd- https://gofile.io/d/T8t3T1
Private with key not for public DM for key.
<< ------------- >>
This is educational purpose To safeguard your organization
Conclusion
Understanding social influence in email manipulation can help individuals and organizations protect themselves from scams and deceptive practices. Awareness of these techniques can empower recipients to make more informed decisions and avoid falling victim to manipulative tactics.
<< ----------------- >>
Some BEC setup buyer proof and testimony:
 Happy hacking and Phishing Techniques to all xss.pro Member's read thread's.. have a wonderful cashout weekend
Happy hacking and Phishing Techniques to all xss.pro Member's read thread's.. have a wonderful cashout weekend