Пожалуйста, обратите внимание, что пользователь заблокирован
- Цена
- 1500$
- Контакты
- https://t.me/cyb3rph4nt0m
Hello! I'm introducing a botnet source that I have made over the past several months. This malware has its very own unique signature and is one of the best bots available for purchase at the moment. Completely advanced and carefully crafted it excels even the most known malware strains such as mirai variants, qbot, dosbot, mozi, and much more. This bot is capable of infecting pretty much virtually any device that runs on a Linux kernel. It has been tested all the way from Linux kernel 2.6 to 6.11 at the most recent.
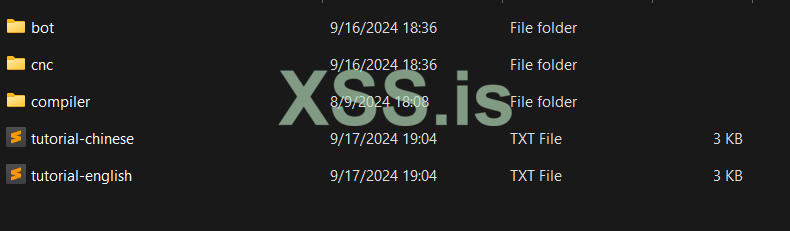
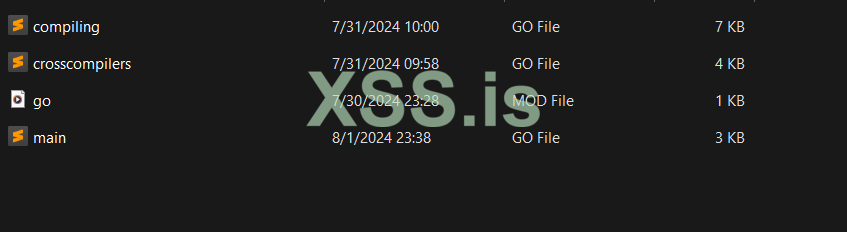
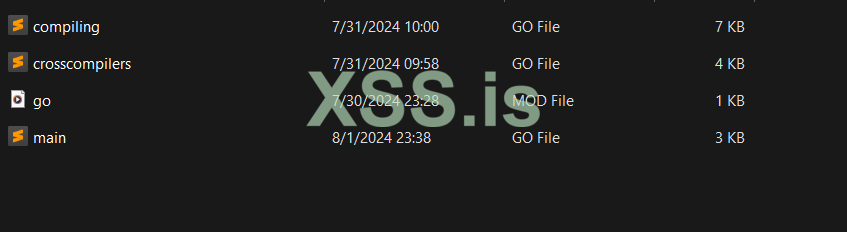
Compiling Binaries:
A compiler was built in GoLang to download, extract, and build binaries automatically within less than a minute eliminating the need to compile everything manually or with complicated shell scripting. This means that you can make code changes, fresh rebuilds, and much more to easily build all of the binaries in a quick amount of time. The user seamlessly and can easily add binaries to the code simply by inputting a URL and a few new lines of code with the name of the file.
List of supported binaries at base code:
ArmV4L
ArmV5L
ArmV6L
ArmV7L
Intel i586
Intel i686
M86k
Mips
Mips64
Mipsel
SH4
x86_64 (Same as i786 and the higher variations, works with both Intel and all AMD variations running 64 bit)
If the user wishes to add more binaries, they need a cross compiler built with uClibc.
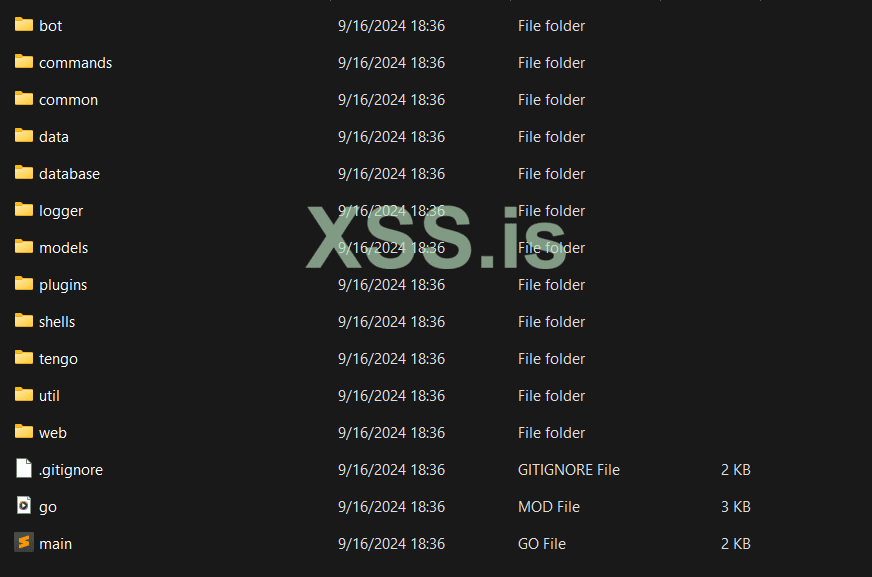
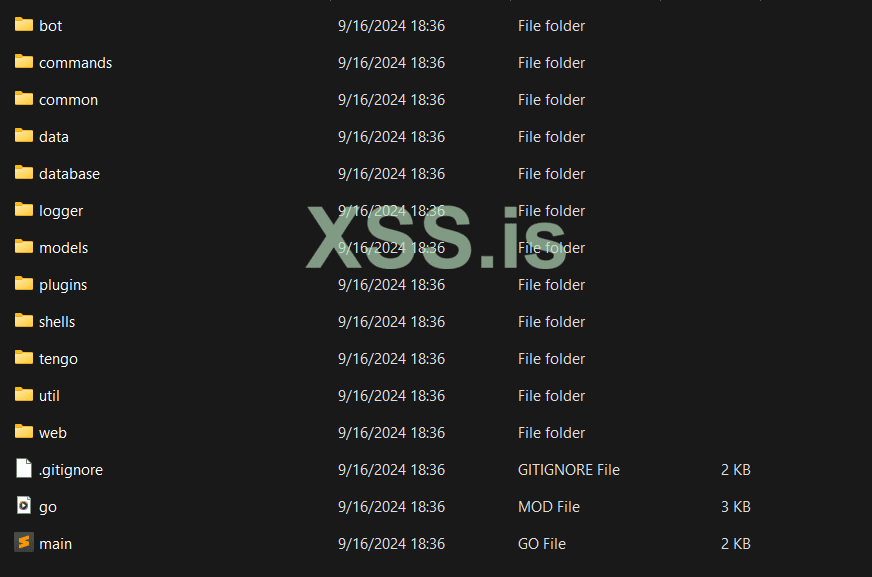
CNC:
The CNC was coded in GoLang using the Tengo library to eliminate the need of having to rebuild CNC's when you can just update a Tengo script with real time changes to avoid rebuilds. The CNC is feature dense with it's very own safe database used for creating users on the CNC.
The CNC runs off both HTTP and SSH. This is to ensure encrypted communications amongst ISP's, VPN's, and overall communication sniffing to avoid being questioned on what your activities consist of.
Customizable communication for the CNC is also available per user demands, you can change ports of SSH, bot communication, and HTTP.
The malware itself communicates to the CNC using XOR key exchanges in multiple iterations typically involving 3-5 key exchanges to also avoid communication sniffing.
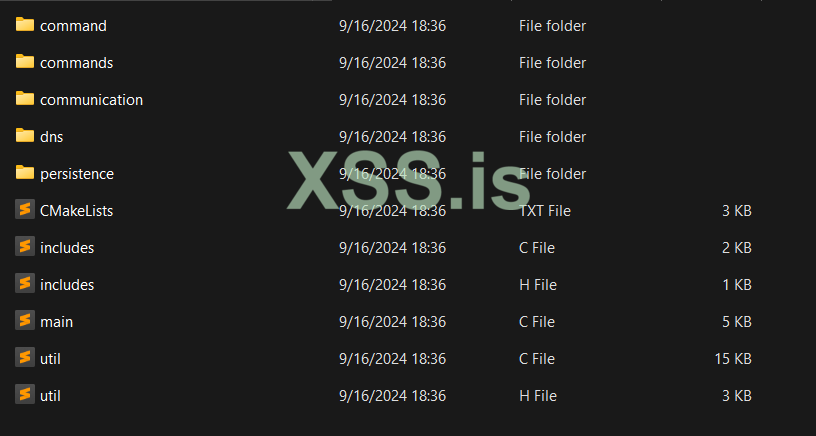
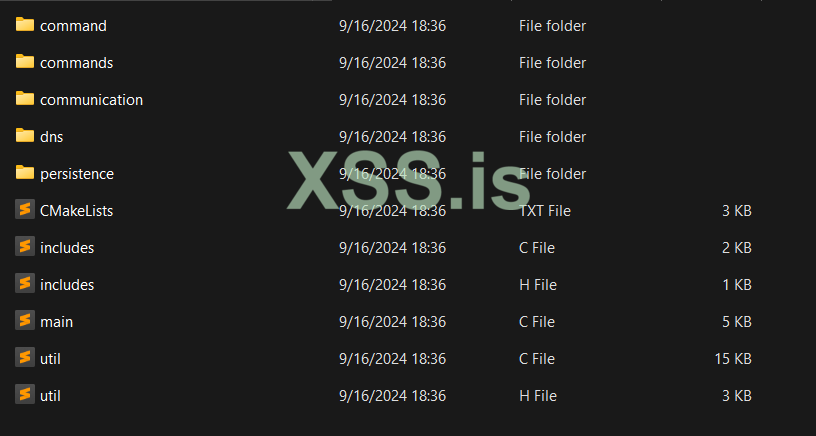
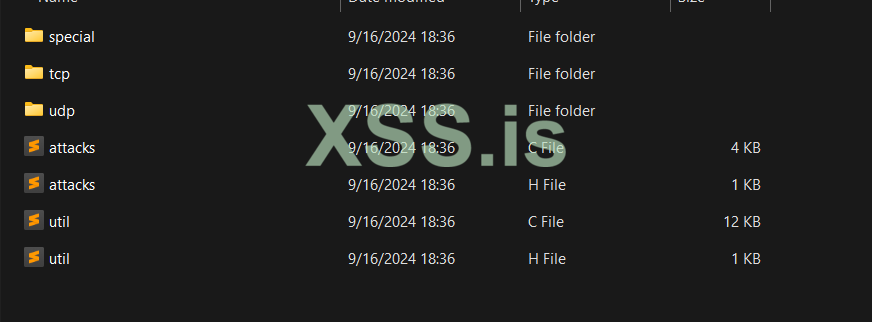
Bot Source/Malware:
The actual bot source code is made in C. It's very well organized which makes it easier to make modifications or to see where things are getting initialized. It's also very well coded so that there can never be a segmentation fault or any type of memory/resource issues.
Features:
Command execution and parsing.
Customized connection and packet sending.
Ability to stop sending attacks/packets initialized by a specific user. Every attack returns an ID. You can use this ID to stop an attack
Reverse Shell, allowing the users to execute commands on every device connected to the CNC. You can execute any command you want such as wget, pkill, curl, reboot, etc.
Shell, similar to the Reverse Shell except it executes in the context of the malware PID.
Shutting down devices, allowing the users to shutdown and kill all of the connected devices in the event of any compromise or law enforcement influence.
Updating bots automatically, allowing the users to automatically update every single connected device to receive an update after modifications were made to the malware. This eliminates the need to reload all of the devices manually.
Ability to set domain and IPv4 connections on the bot. This allows the users to use a domain which makes it possible to regain all of the connected devices simply by changing the IPv4 on the A Record. So if the actual CNC IPv4 gets ddos'd, banned, or seized you can easily get it back online. Domain is not required for the bot to function or connect to the CNC.
DNS Resolver, pretty self explanatory, resolved the DNS associated with the domain connections and so on.
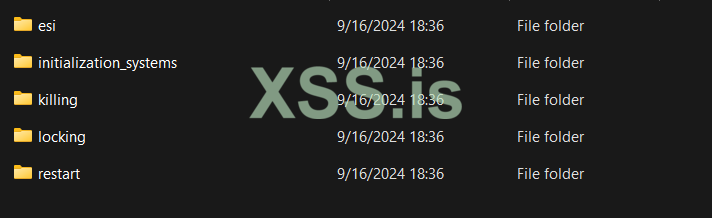
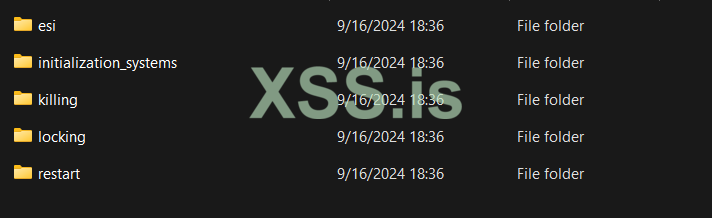
Persistence to maintain connections in the event of a device reboot or PID kill. Persistence includes cron, initd, rcd, and systemd.
Watchdog, similar to persistence it watches if the PID dies and restarts it in any event it goes down.
Malware Killing, the bot has a pretty extensive method for killing and removing other malware or unwanted programs from the devices. This includes specific details about scanning binaries for certain data matches.
File Locking, the bot has a file locker which prohibits the use of creating certain binaries and files on the device, excluding our very own bot.
ESI, the bot has Ensure Single Instance to make sure the user never encounters any duplicated connections on the same device.
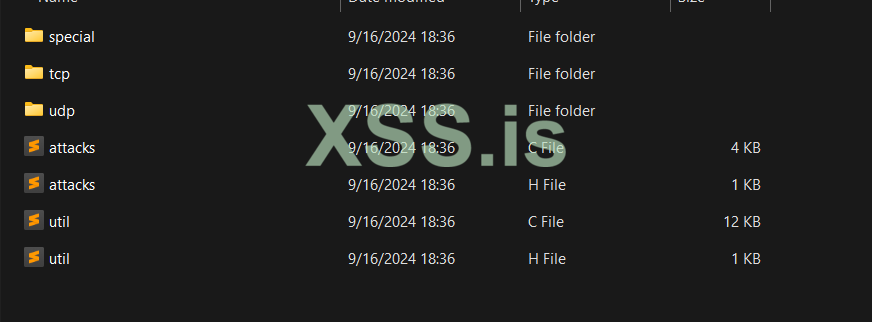
Attack Methods:
Using specialized Linux kernel coding we were able to achieve sending TCP packets without the need of root/admin privileges across a vast number of devices. This makes it so that even basic logins can send TCP packets.
Layer 3 Methods are customizable with specifying the time and size. There are no destination ports in Layer 3.
TCP Methods are customizable with specifying the destination port, time, and PPS.
UDP Methods are customizable with specifying the destination port, time, and size.
Layer 3 (ICMP, ICMP_Fragmentation, IPIP).
Layer 4 - TCP (Generic, Hold, Junk, OpenVPN, Socket).
Layer 4 - UDP (Generic, Bypass, Junk, OpenVPN).
Users can easily add more Attack Methods using the same structure in the code.
Contact Information:
Telegram: https://t.me/cyb3rph4nt0m
On-site DMS also available but may be slower for a response
Price: 1500$
ESCROW ACCEPTED AND ENCOURAGED FOR USE!
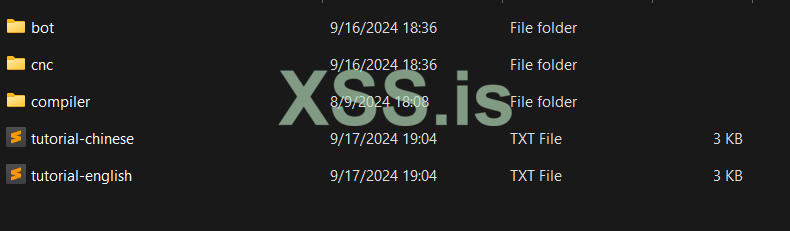
Compiling Binaries:
A compiler was built in GoLang to download, extract, and build binaries automatically within less than a minute eliminating the need to compile everything manually or with complicated shell scripting. This means that you can make code changes, fresh rebuilds, and much more to easily build all of the binaries in a quick amount of time. The user seamlessly and can easily add binaries to the code simply by inputting a URL and a few new lines of code with the name of the file.
List of supported binaries at base code:
ArmV4L
ArmV5L
ArmV6L
ArmV7L
Intel i586
Intel i686
M86k
Mips
Mips64
Mipsel
SH4
x86_64 (Same as i786 and the higher variations, works with both Intel and all AMD variations running 64 bit)
If the user wishes to add more binaries, they need a cross compiler built with uClibc.
CNC:
The CNC was coded in GoLang using the Tengo library to eliminate the need of having to rebuild CNC's when you can just update a Tengo script with real time changes to avoid rebuilds. The CNC is feature dense with it's very own safe database used for creating users on the CNC.
The CNC runs off both HTTP and SSH. This is to ensure encrypted communications amongst ISP's, VPN's, and overall communication sniffing to avoid being questioned on what your activities consist of.
Customizable communication for the CNC is also available per user demands, you can change ports of SSH, bot communication, and HTTP.
The malware itself communicates to the CNC using XOR key exchanges in multiple iterations typically involving 3-5 key exchanges to also avoid communication sniffing.
Bot Source/Malware:
The actual bot source code is made in C. It's very well organized which makes it easier to make modifications or to see where things are getting initialized. It's also very well coded so that there can never be a segmentation fault or any type of memory/resource issues.
Features:
Command execution and parsing.
Customized connection and packet sending.
Ability to stop sending attacks/packets initialized by a specific user. Every attack returns an ID. You can use this ID to stop an attack
Reverse Shell, allowing the users to execute commands on every device connected to the CNC. You can execute any command you want such as wget, pkill, curl, reboot, etc.
Shell, similar to the Reverse Shell except it executes in the context of the malware PID.
Shutting down devices, allowing the users to shutdown and kill all of the connected devices in the event of any compromise or law enforcement influence.
Updating bots automatically, allowing the users to automatically update every single connected device to receive an update after modifications were made to the malware. This eliminates the need to reload all of the devices manually.
Ability to set domain and IPv4 connections on the bot. This allows the users to use a domain which makes it possible to regain all of the connected devices simply by changing the IPv4 on the A Record. So if the actual CNC IPv4 gets ddos'd, banned, or seized you can easily get it back online. Domain is not required for the bot to function or connect to the CNC.
DNS Resolver, pretty self explanatory, resolved the DNS associated with the domain connections and so on.
Persistence to maintain connections in the event of a device reboot or PID kill. Persistence includes cron, initd, rcd, and systemd.
Watchdog, similar to persistence it watches if the PID dies and restarts it in any event it goes down.
Malware Killing, the bot has a pretty extensive method for killing and removing other malware or unwanted programs from the devices. This includes specific details about scanning binaries for certain data matches.
File Locking, the bot has a file locker which prohibits the use of creating certain binaries and files on the device, excluding our very own bot.
ESI, the bot has Ensure Single Instance to make sure the user never encounters any duplicated connections on the same device.
Attack Methods:
Using specialized Linux kernel coding we were able to achieve sending TCP packets without the need of root/admin privileges across a vast number of devices. This makes it so that even basic logins can send TCP packets.
Layer 3 Methods are customizable with specifying the time and size. There are no destination ports in Layer 3.
TCP Methods are customizable with specifying the destination port, time, and PPS.
UDP Methods are customizable with specifying the destination port, time, and size.
Layer 3 (ICMP, ICMP_Fragmentation, IPIP).
Layer 4 - TCP (Generic, Hold, Junk, OpenVPN, Socket).
Layer 4 - UDP (Generic, Bypass, Junk, OpenVPN).
Users can easily add more Attack Methods using the same structure in the code.
Contact Information:
Telegram: https://t.me/cyb3rph4nt0m
On-site DMS also available but may be slower for a response
Price: 1500$
ESCROW ACCEPTED AND ENCOURAGED FOR USE!