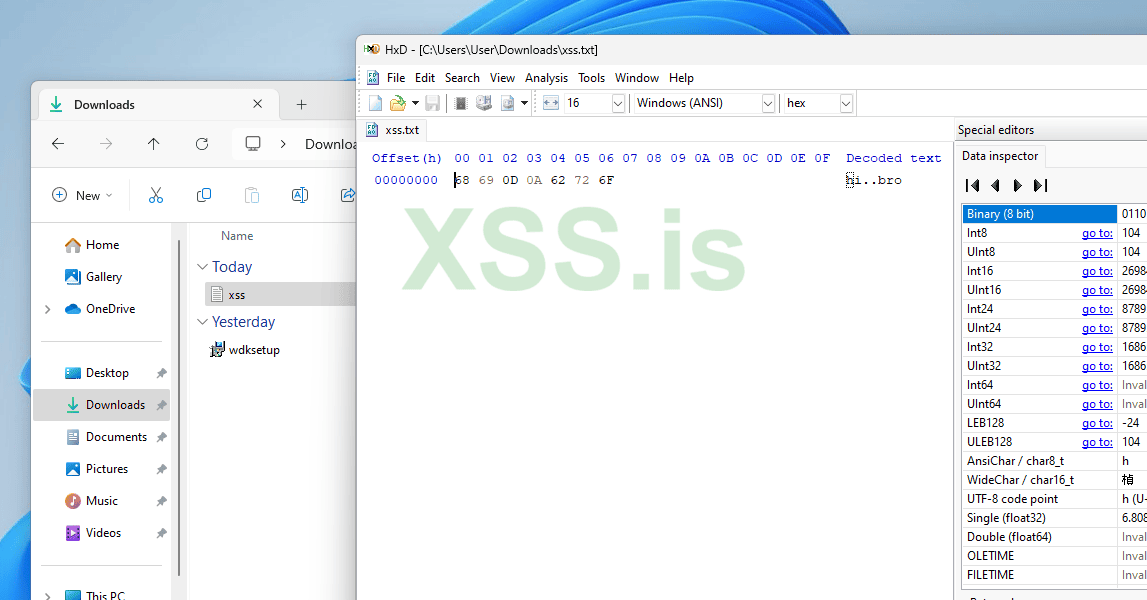
на сколько актуален эксплоит exe to txt, было бы не плохо его найти где нибудь бесплатно, просто на сколько мне известно такой эксплоит зародился примерно в 2017?
да и в целом было бы неплохо источники получить
да и в целом было бы неплохо источники получить