CVE-2024-6704
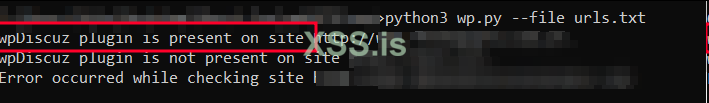
CVE-2024-6704 - [Wordpress wpDiscuz_Plugin] < Unauthenticated HTML Injection ExploiterThe Comments – wpDiscuz plugin for WordPress is vulnerable to HTML Injection in all versions up to, and including, 7.6.21. This is due to a lack of filtering of HTML tags in comments. This makes it possible for unauthenticated attackers to add HTML such as hyperlinks to comments when rich editing is disabled.
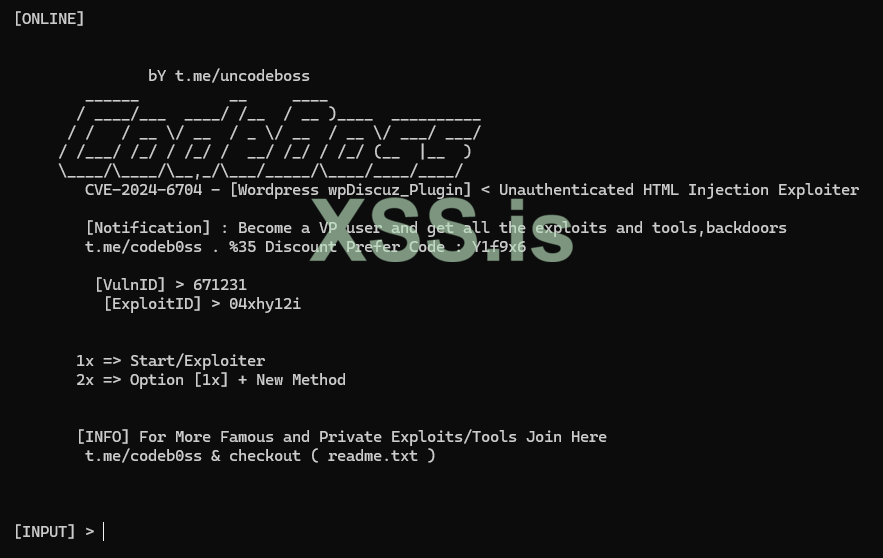
Source Github : https://github.com/codeb0ss/CVE-2024-6704
Последнее редактирование: