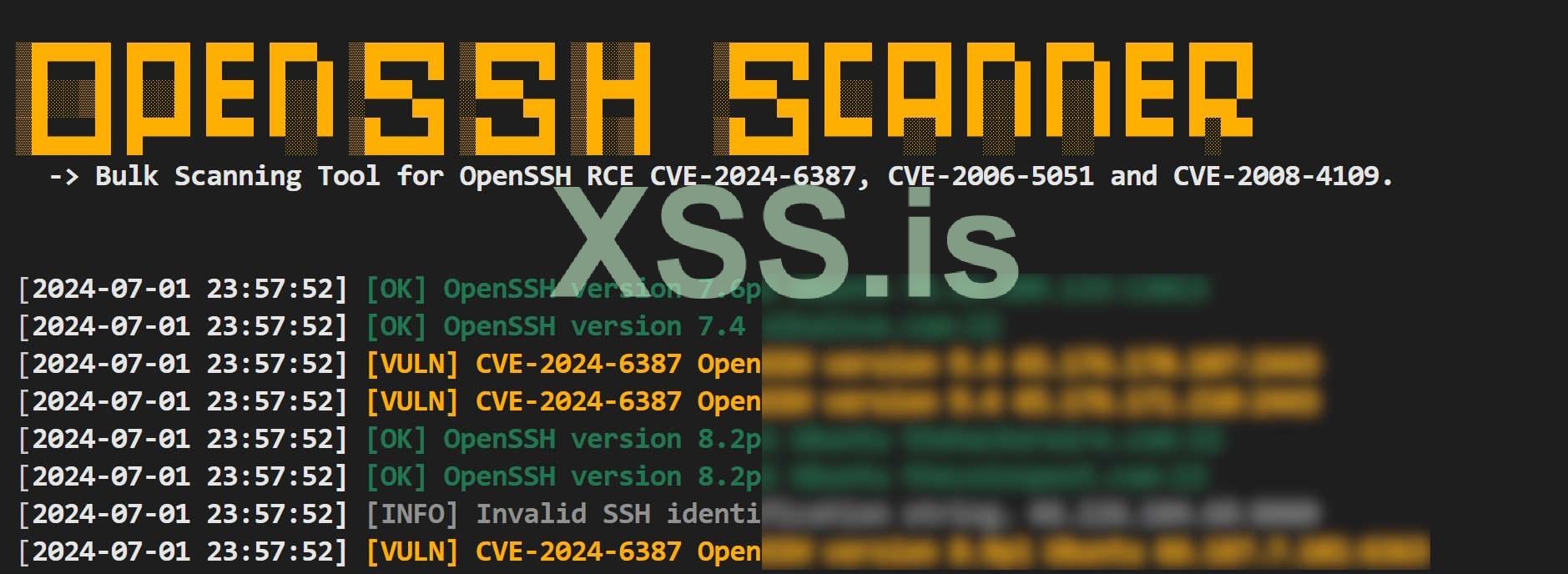
CVE-2024-6387: RCE in OpenSSH's server, on glibc-based Linux systems
source: https://blog.qualys.com/vulnerabili...ode-execution-vulnerability-in-openssh-server
PoC: https://xss.pro/threads/117932/#post-828747
тысячеглаз не заметит бэкдор, если ты замаскируешь его под "случайно оставленную" уязвимость
 github.com
github.com
source: https://blog.qualys.com/vulnerabili...ode-execution-vulnerability-in-openssh-server
PoC: https://xss.pro/threads/117932/#post-828747
- 8.5p1 <= OpenSSH < 9.8p1 is vulnerable again to this signal handler
race condition (because the "#ifdef DO_LOG_SAFE_IN_SIGHAND" was
accidentally removed from sigdie()).
...
In our experiments, it takes ~10,000 tries on average to win this race condition, so ~3-4 hours with 100 connections (MaxStartups) accepted per 120 seconds (LoginGraceTime). Ultimately, it takes ~6-8 hours on average to obtain a remote root shell
...
This regression was introduced in October 2020 (OpenSSH 8.5p1) by commit 752250c ("revised log infrastructure for OpenSSH"), which accidentally removed an "#ifdef DO_LOG_SAFE_IN_SIGHAND" from sigdie(), a function that is directly called by sshd's SIGALRM handler
тысячеглаз не заметит бэкдор, если ты замаскируешь его под "случайно оставленную" уязвимость
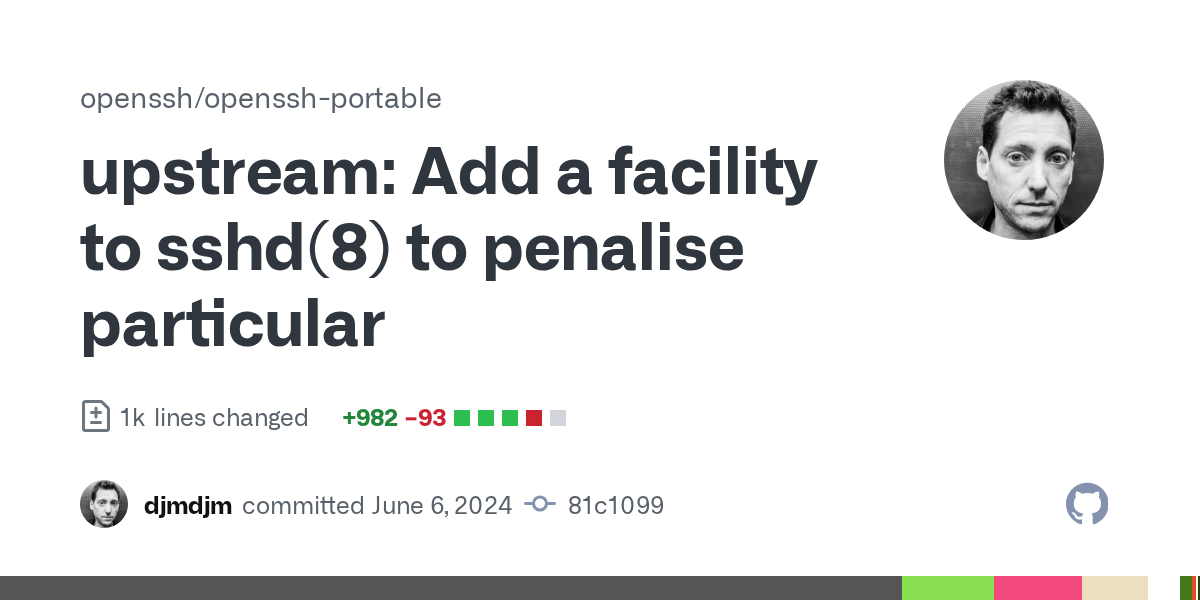
On June 6, 2024, this signal handler race condition was fixed by commit 81c1099 ("Add a facility to sshd(8) to penalise particular problematic client behaviours")
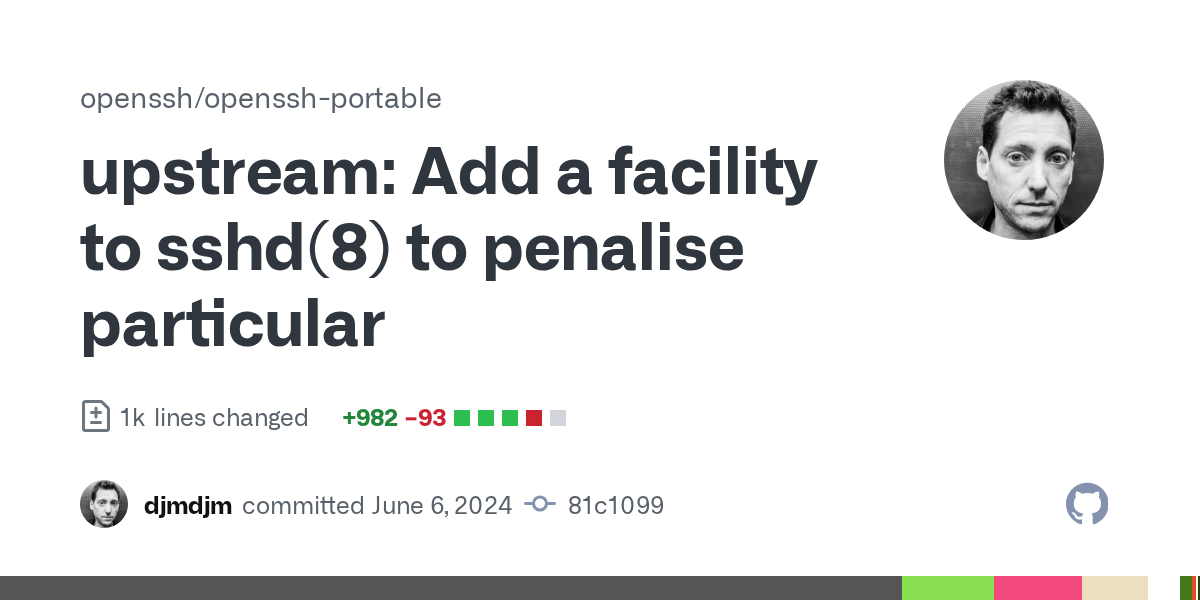
upstream: Add a facility to sshd(8) to penalise particular · openssh/openssh-portable@81c1099
problematic client behaviours, controlled by two new sshd_config(5) options: PerSourcePenalties and PerSourcePenaltyExemptList. When PerSourcePenalties are enabled, sshd(8) will monitor the exit s...
Последнее редактирование: