Пожалуйста, обратите внимание, что пользователь заблокирован
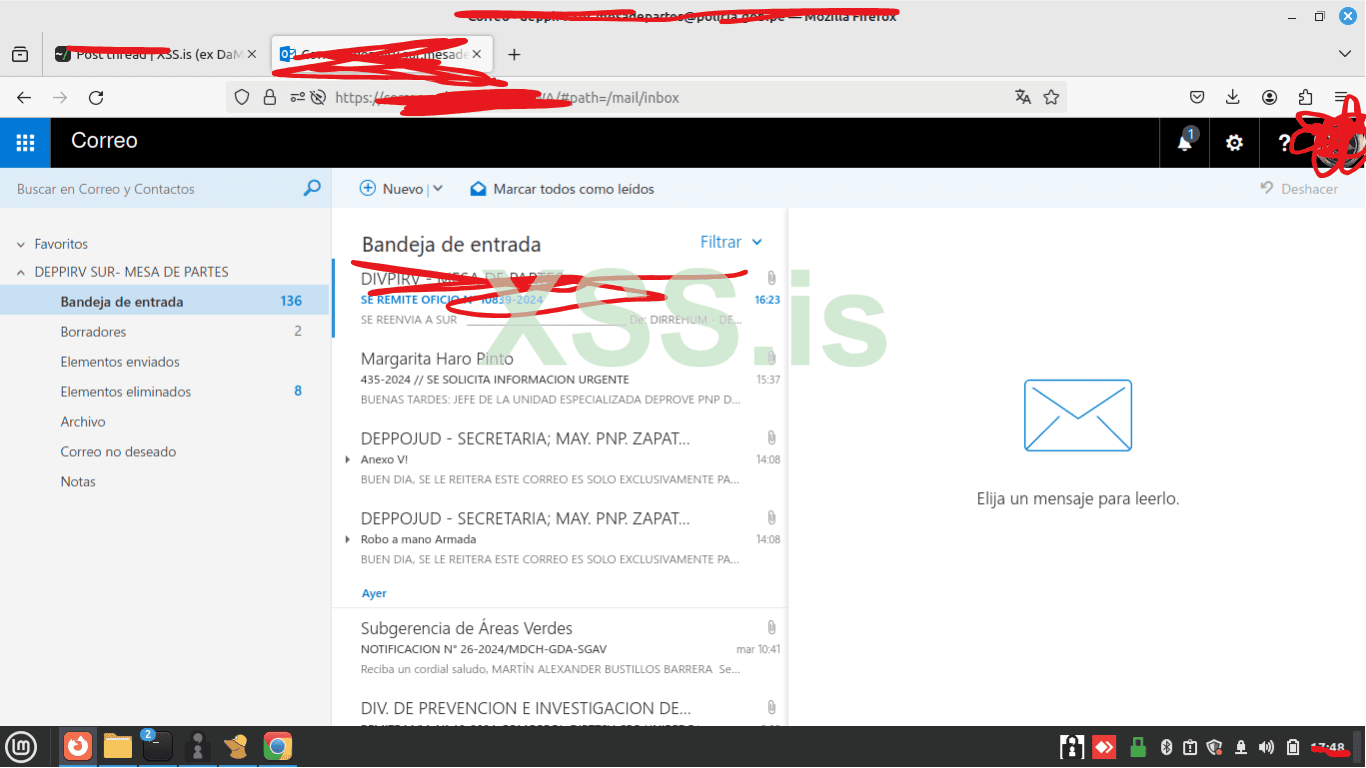
Hello everyone, I want to share with you a screenshot of an email I accessed after my first, successful malware attack,
to start with all this, I got user and password of the mail of the police of a country that I can not name at least for now, after that I prepared my stealer and an office document that downloaded and executed the stealer, including other malware but apparently the backdoor was detected, although even so the stealer was executed successfully, and I managed to get mail credentials of the same company to which I had access, but in this case another user and password, plus access to another web platform that is not the mail.
to start with all this, I got user and password of the mail of the police of a country that I can not name at least for now, after that I prepared my stealer and an office document that downloaded and executed the stealer, including other malware but apparently the backdoor was detected, although even so the stealer was executed successfully, and I managed to get mail credentials of the same company to which I had access, but in this case another user and password, plus access to another web platform that is not the mail.