- Цена
- PM
- Контакты
- Forum
Sophos Endpoint Detection (EDR/XDR/MDR) Havoc bypass
Bitdefender Endpoint Detection and Response (EDR) Cobalt Strike bypass
Bitdefender Endpoint Detection and Response (EDR) Havoc bypass
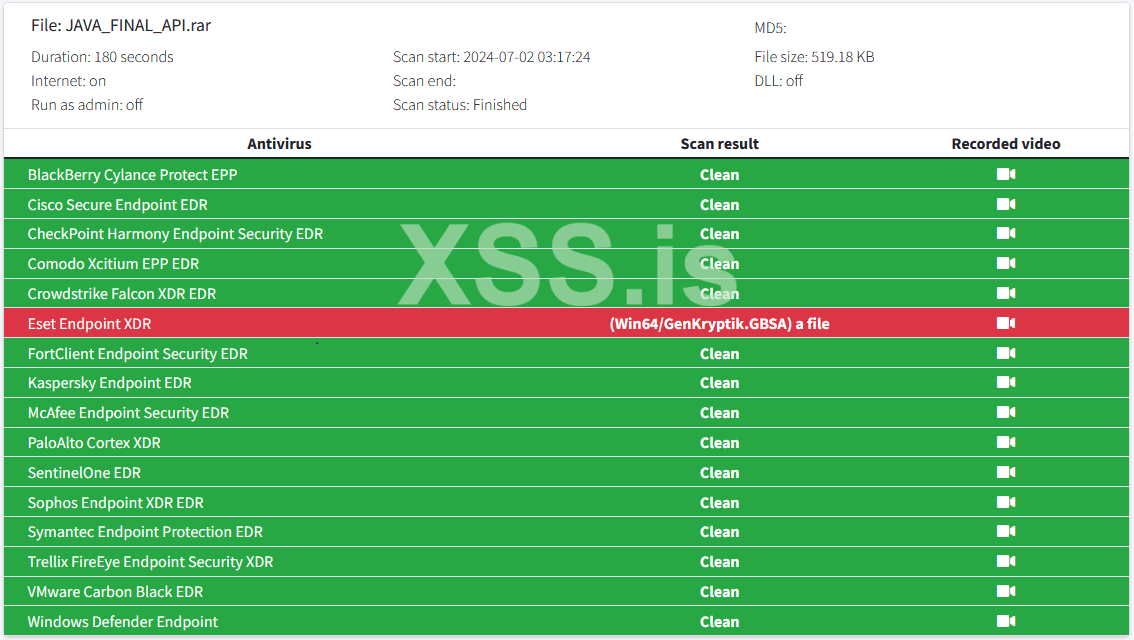
ESET Endpoint Antivirus Cobalt Strike bypass
ESET Endpoint Antivirus Havoc bypass
Microsoft excel (.xll) Cobalt Strike
Microsoft excel (.xll) Havoc
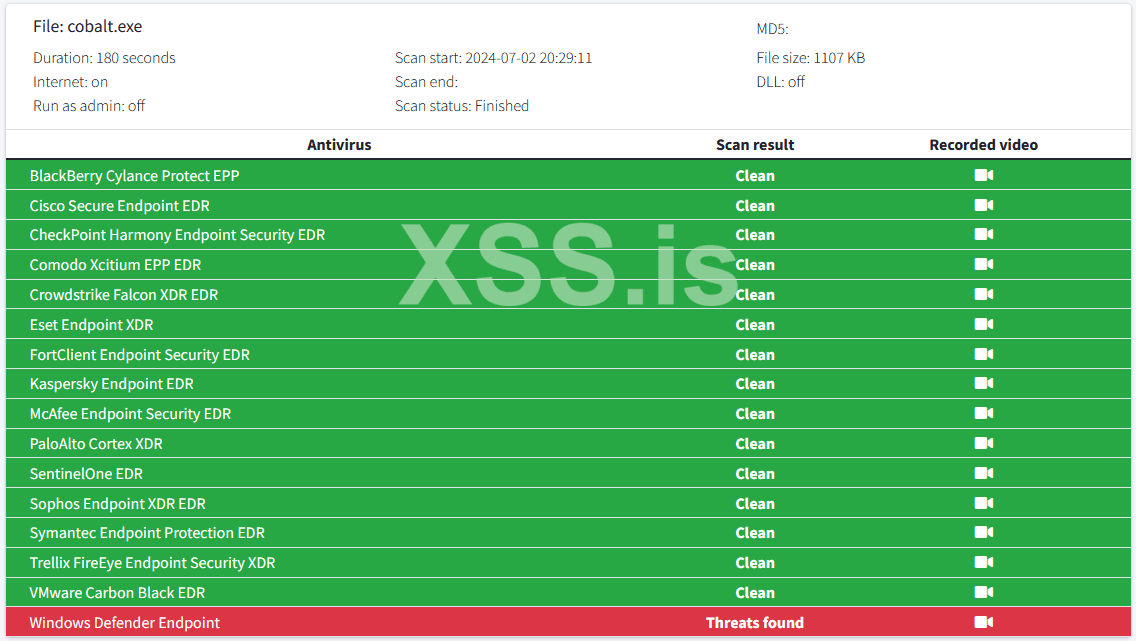
Windows Defender + Smartscreen (Windows 11-23H2) Cobalt Strike (DLL sideloading, chrome binary)
Windows Defender + Smartscreen (Windows 11-23H2) Havoc (DLL sideloading, chrome binary)
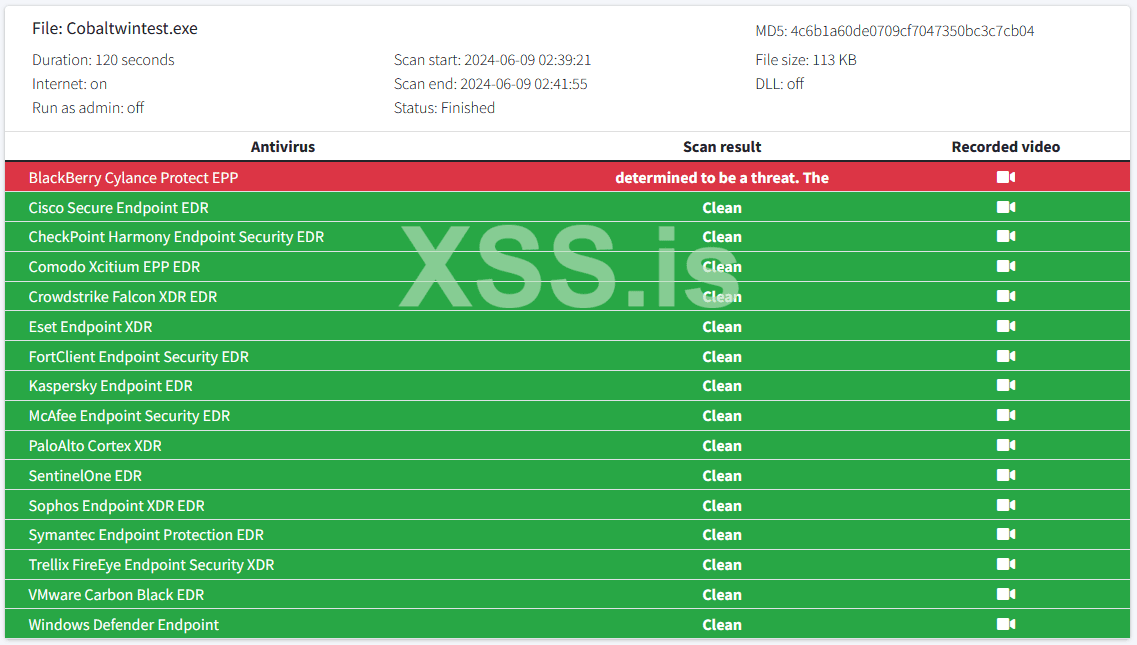
https://scanner.to/result_EDR/qzpMBWRv6B9e
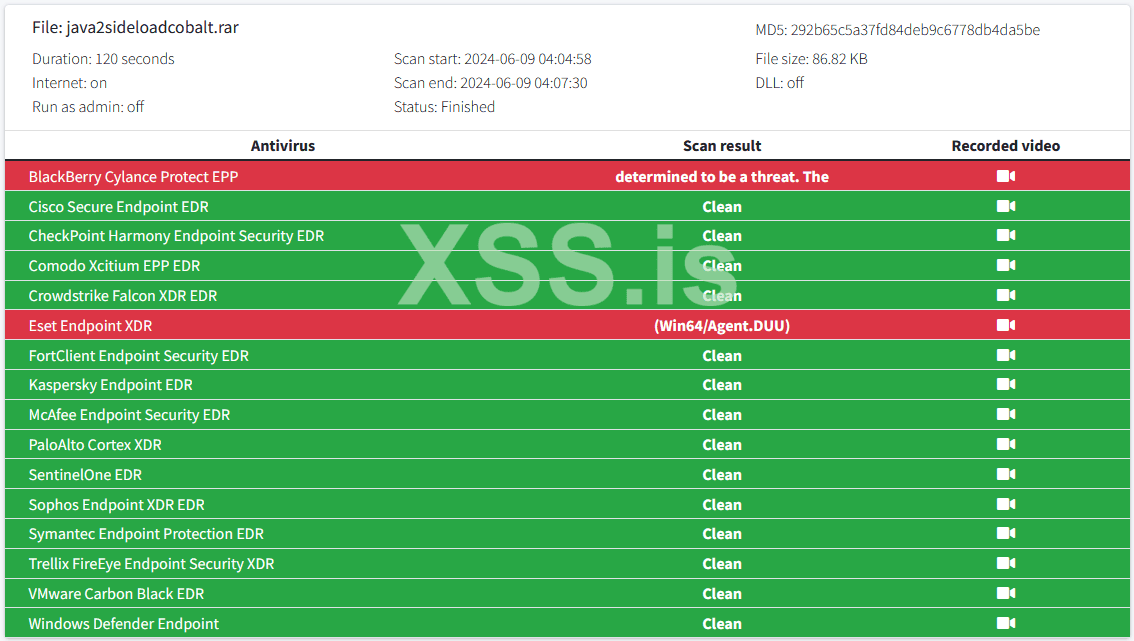
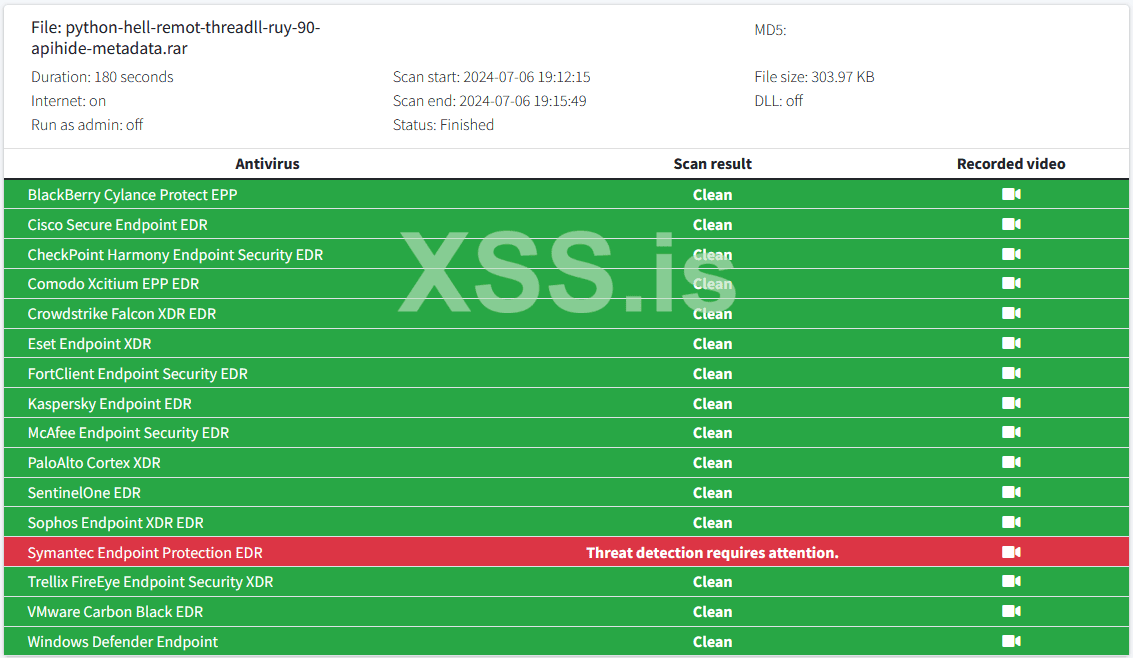
https://scanner.to/result_EDR/CCj3JHAxXG4G
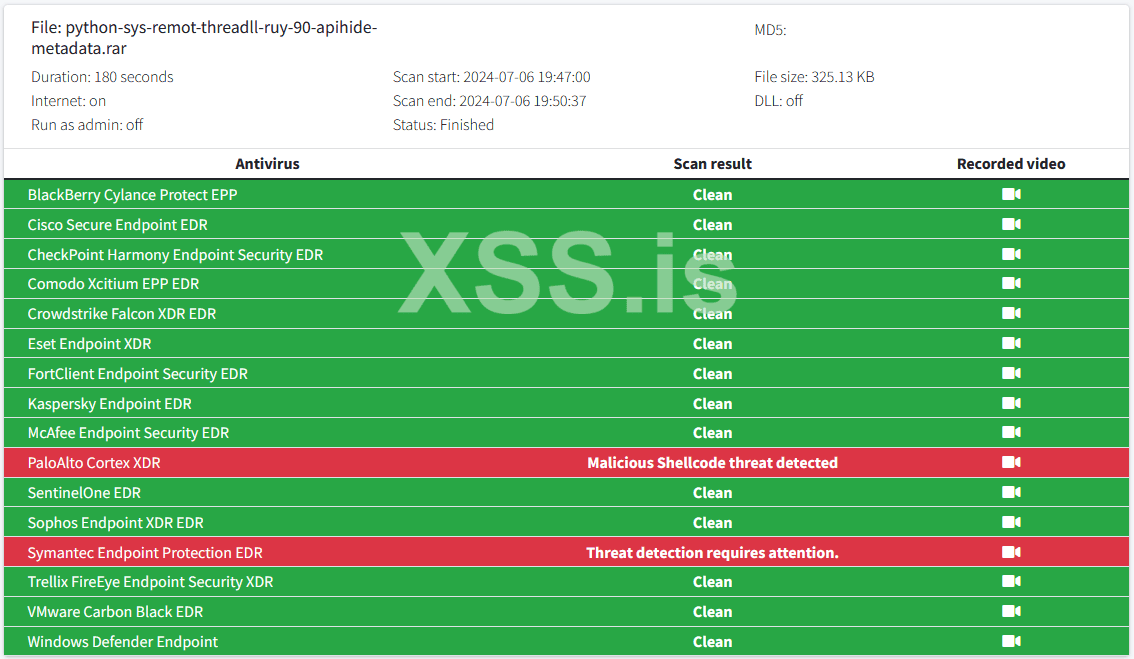
https://scanner.to/result_EDR/4FVc8d3qRVaL
https://scanner.to/result_EDR/dNv7z8AkzMZQ#
https://scanner.to/result_EDR/Tq8AhX3E8Cb8
https://scanner.to/result_EDR/LX9VuYjd8YHk
All tests on scanner.to are performed with an active internet connection and using small-sized files. Recently, there have been instances of individuals attempting to circumvent others' efforts by disabling their internet connection and using significantly large payloads, exceeding 100 MB. Please exercise caution.
Welcome to our shop! Please, make yourself comfortable and feel free to ask anything you need. I'm here to share my experience and knowledge with those who seek it. Rest assured, all our work has been conducted under real AV/EDR environments, utilizing the top tools available in the market. If you have any questions or need guidance, don't hesitate to reach out. For your peace of mind, we only take orders through a secure escrow or guarantor system. Looking forward to assisting you on your journey!
Technical information
- Encrypt PE Files: Securely encrypt Portable Executable (PE) files for runtime decryption and execution, either as shellcode via Donut or directly through a syscall-enhanced Run-PE method.
- Architecture Support: Compatible with x64 architecture.
- Memory Execution: By default, all payloads execute in an RX memory region, with the option to switch to RWX.
- C# Assembly Loading: Load C# assemblies with hardcoded arguments into the encrypted file (.exe/.dll).
- More than 15 legitimate binaries for DLL Sideloading (Apple, Chrome, CiscoWebEx, GithubDesktop, Java, Microsoft, Obsidian, OperaBrowser, Oracle, Teams, Visual Studio, Windows R_Server, WinSDK...)
Features
- Anti-sandbox and debugging resistance.
- Auto-deletion post execution.
- Use of pump values to confuse static analysis.
- Injection into newly created processes, with customizable options.
- Custom process spawning for remote injection.
- Spoofing of process arguments for injection targets.
- PPID spoofing to mimic the parent process.
- Threadless injection for shellcode execution.
- Module Stomping without memory allocation.
- Customization of resource file information such as icons and descriptions.
- Compiling the binary in debug mode for detailed output.
- Creation of service binaries or DLLs for use in lateral movement or persistence strategies.
- Steganographic embedding of encrypted payloads in image files.
Formarts supported
- Standalone EXE (.exe)
- MSI installers (.msi)
- Microsoft Excel XLL (.xll)
- Windows Control Panel CPL (.cpl)
- DLL and DLL sideloading under legit signed certificates (Microsoft, Java, Google, Apple, Python...)
- Powershell Output format, reflectively loading the packed binary. (.ps1)
- Shellcode Output format.
Other services
- Customizable Malleable C2 Profiles.
- Rootkits, AV/EDR killer...
- APT simulation chains.
- UAC Bypass/LPE.
- Technical support.
- Custom Cobalt Strike and Havoc scripts. (Auto-persistance, auto execution of commands, etc...).
- We have support for any c2 tool (Havoc, Cobalt Strike, Merlin, Sliver, Brute Ratel...).
- The buyer holds full responsibility for their actions. We do not take any responsibility for your actions.
- By purchasing this service, you acknowledge that there is a no-refund policy.
- The product is intended exclusively for educational purposes.
- We guarantee a money-back refund if we are unable to successfully complete a deployment or if the specified conditions are not met.
- We reserve the right to refuse service to specific users at our discretion.
- All orders are processed through an escrow service.
- The testing phase includes a verbose mode and displays a CMD console to ensure transparency and prevent fraudulent activities by scammers and rippers.
BazarJackson
Последнее редактирование:



