Кто-нибудь может определить, что это за гашиш и соль?
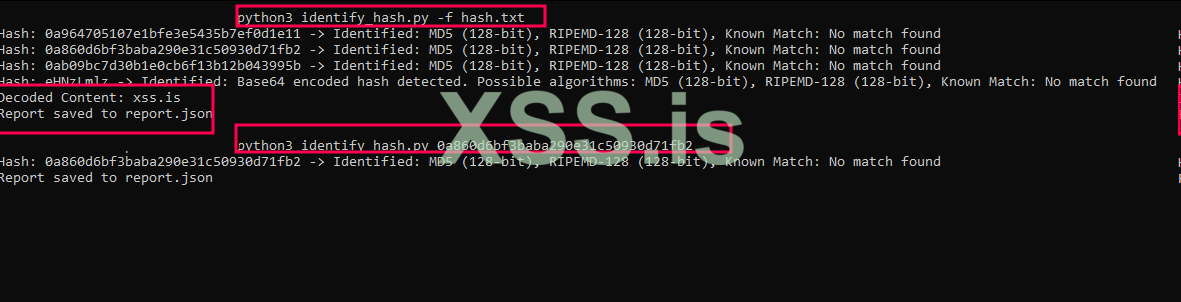
0a964705107e1bfe3e5435b7ef0d1e11
0a860d6bf3baba290e31c50930d71fb2
0ab09bc7d30b1e0cb6f13b12b043995b
0a964705107e1bfe3e5435b7ef0d1e11
0a860d6bf3baba290e31c50930d71fb2
0ab09bc7d30b1e0cb6f13b12b043995b