Why is the PE header important?
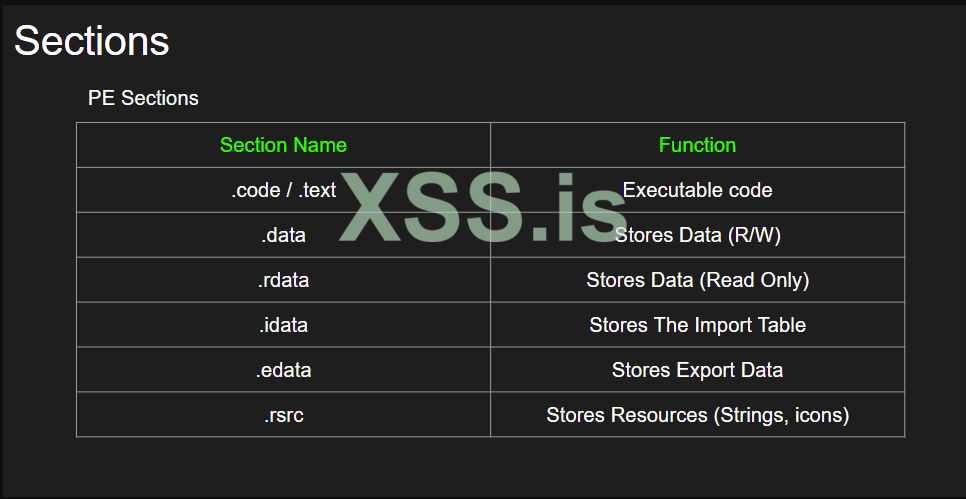
For UPX, when we are dealing with a packed malware sample, if we see the section names, the names will not be coded rdata insetad it will be changed to upx, upx1. That’s another indicator to know the malware sample is packed.
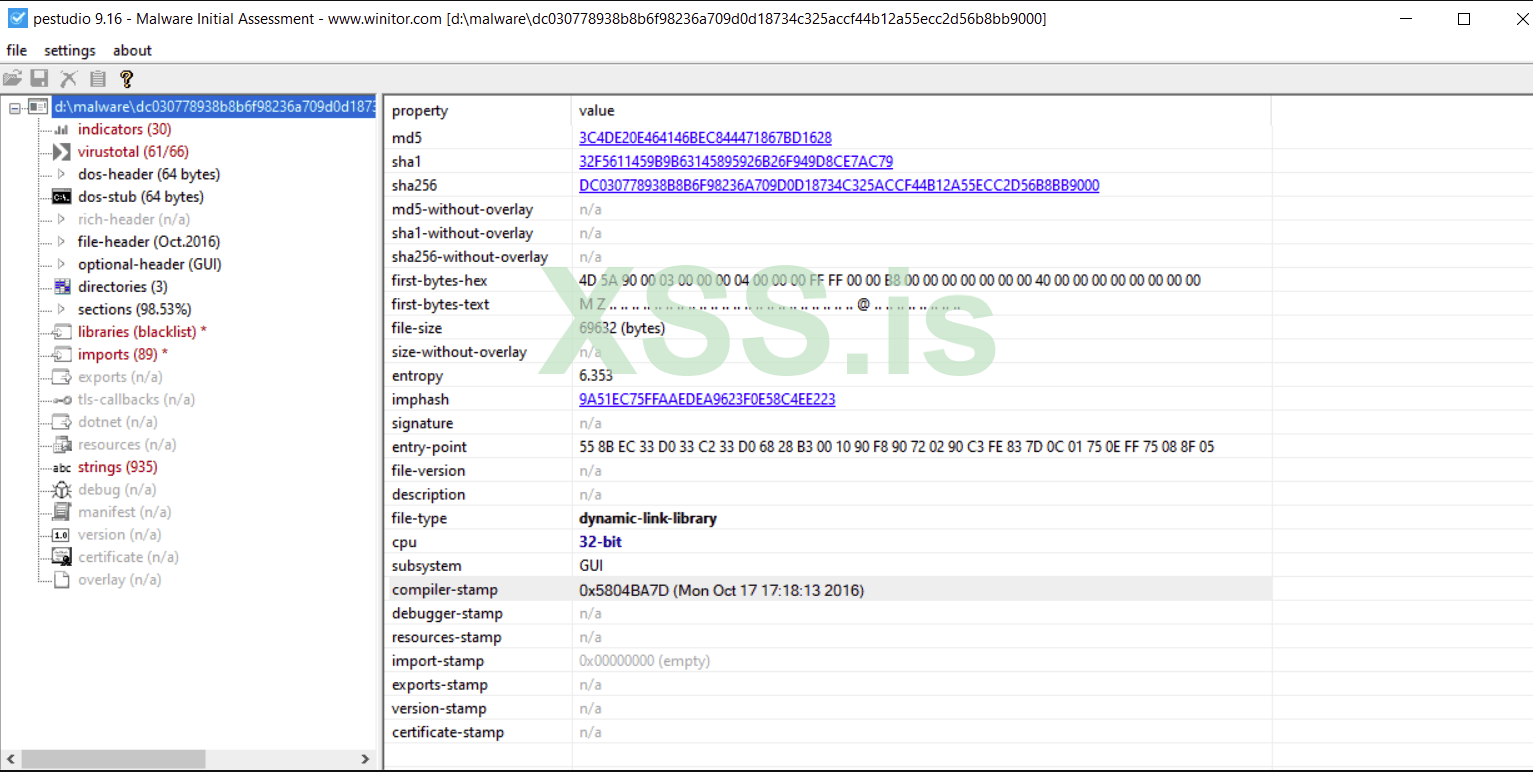
The compiler-stamp indicated when the sample file was compiled
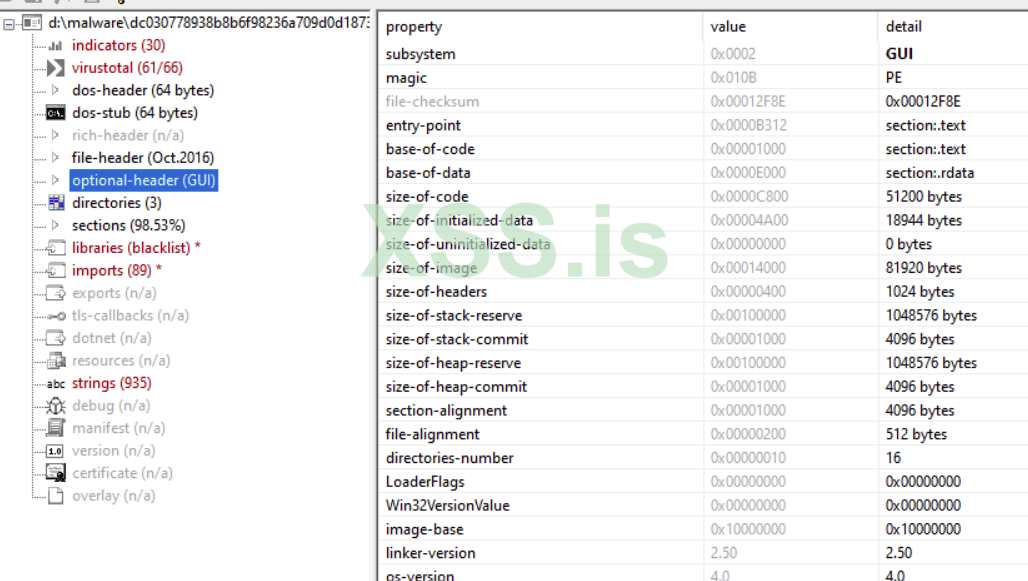
Optional header gives information on which subsystem is used, inclusing size of code, entry point etc.
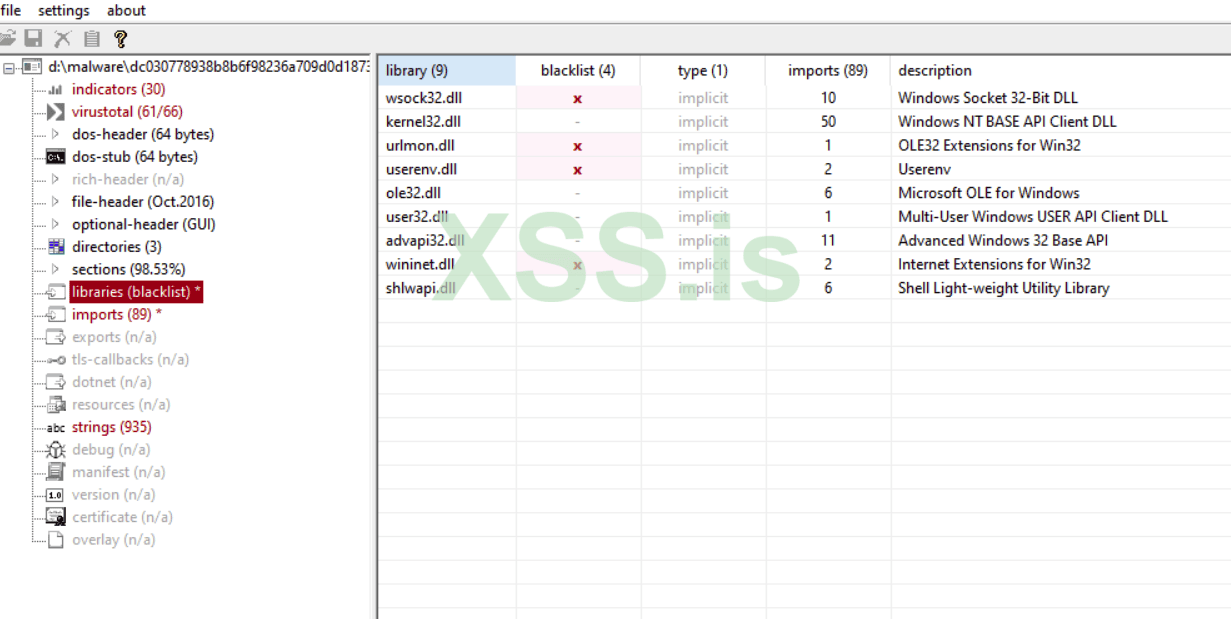
Libraries denote all the dll files that are used
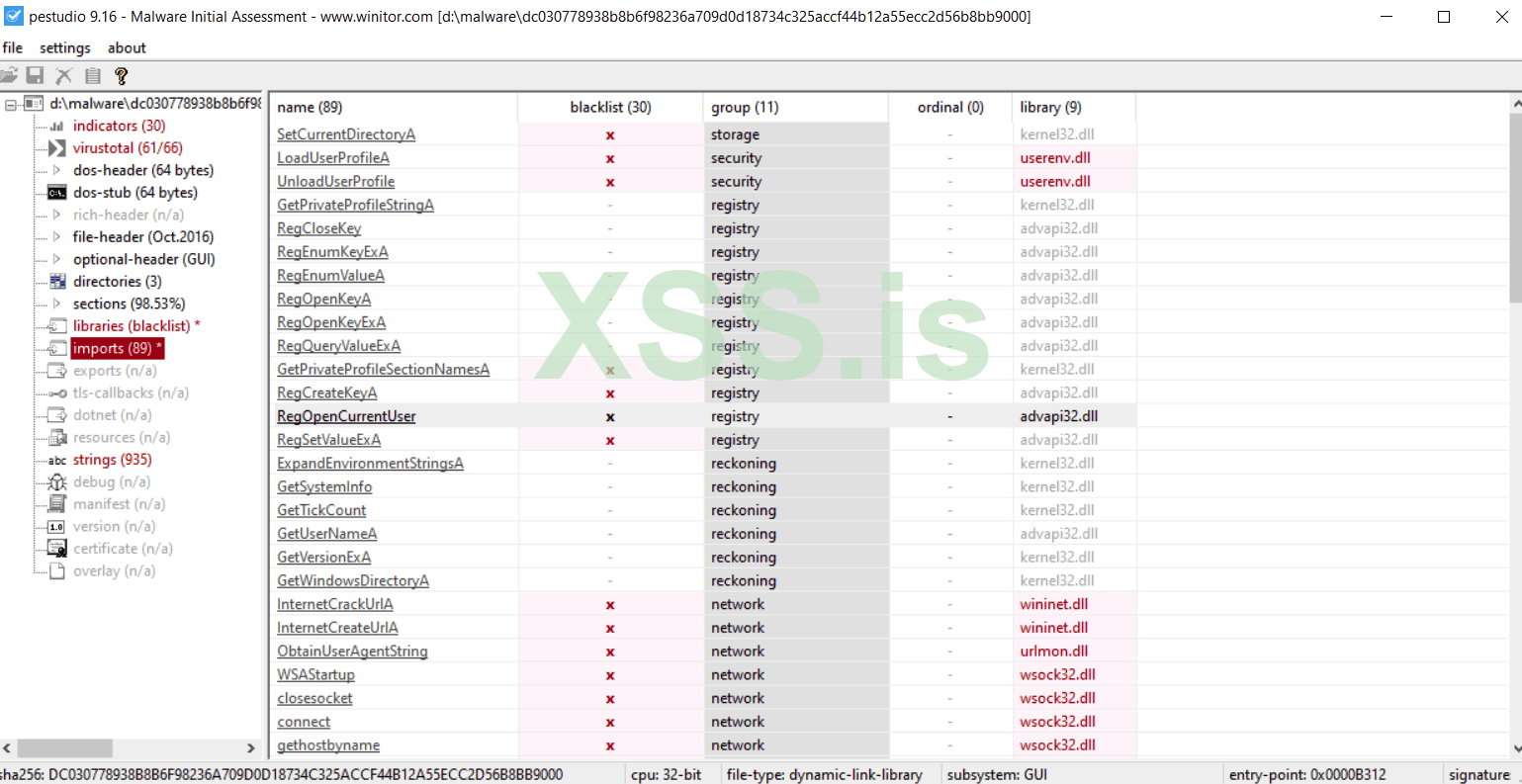
All dlls and its corresponding functions.
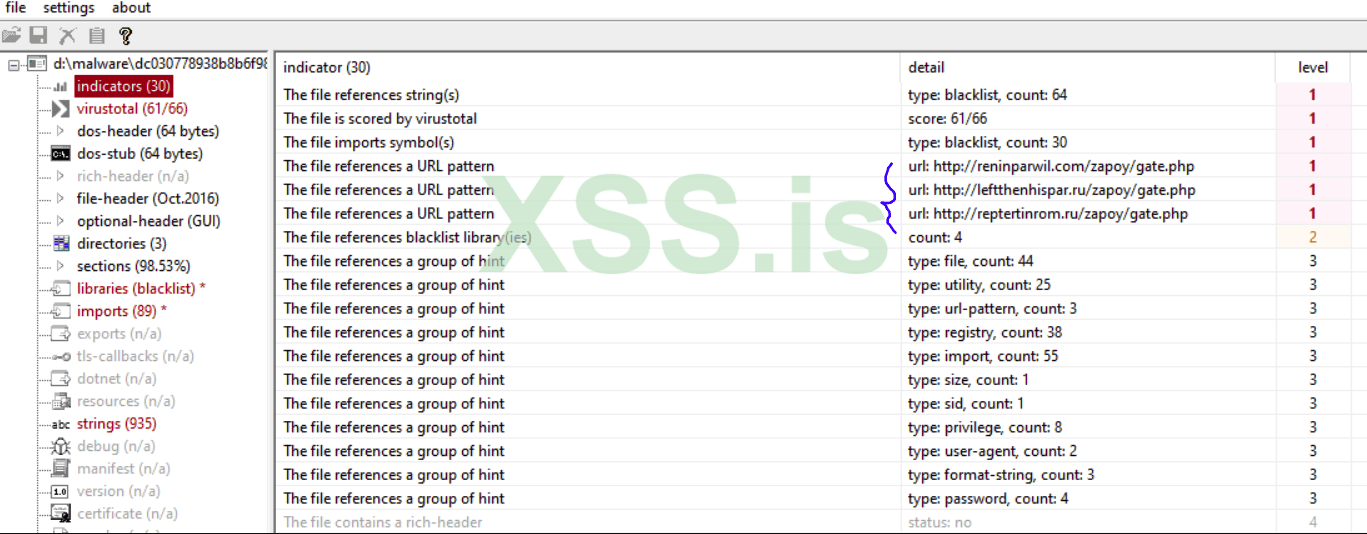
In indicators, we can find three russian domains (c&c), where we get a basic idea of the malware’s origin.
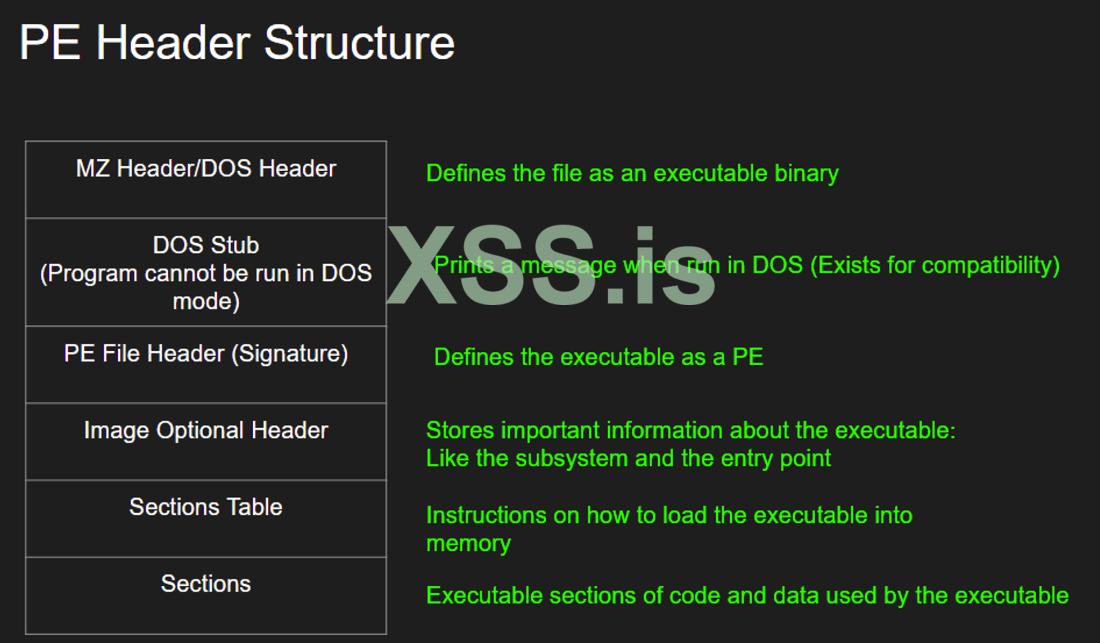
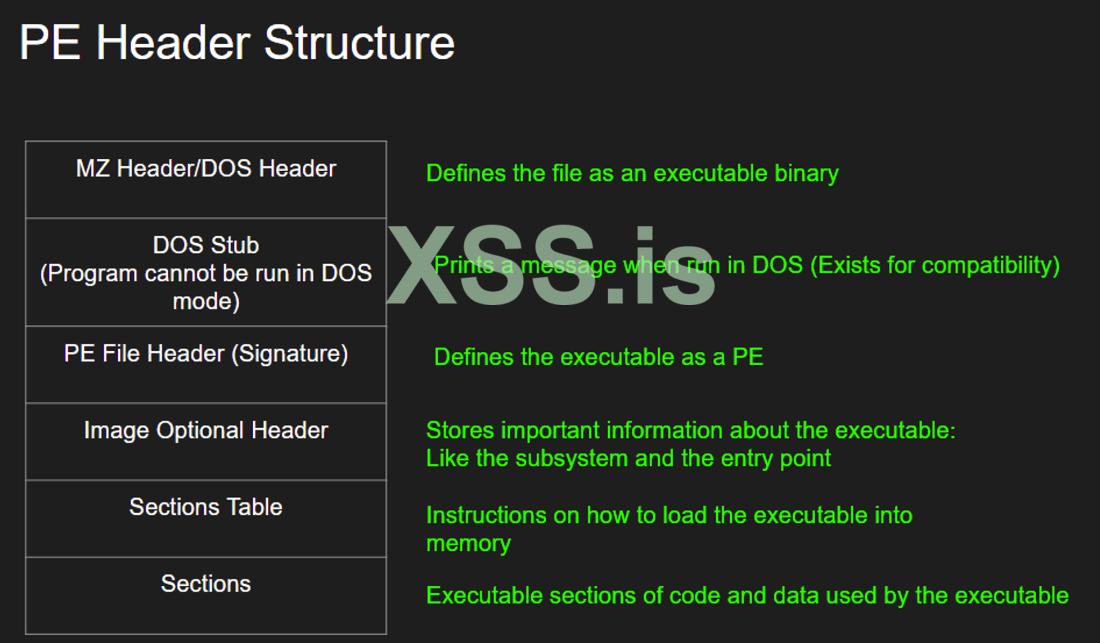
- It contains all of the important and necessary information required by the OS to execute the executable, and functionality of the malware and how the malware interacts with the OS.
- It contains information that specifies where the executable needs to be loaded in to memory.
- It contains the libraries that the executable requires to be loaded (dll).
- It contains information that specifies where the execution begins.
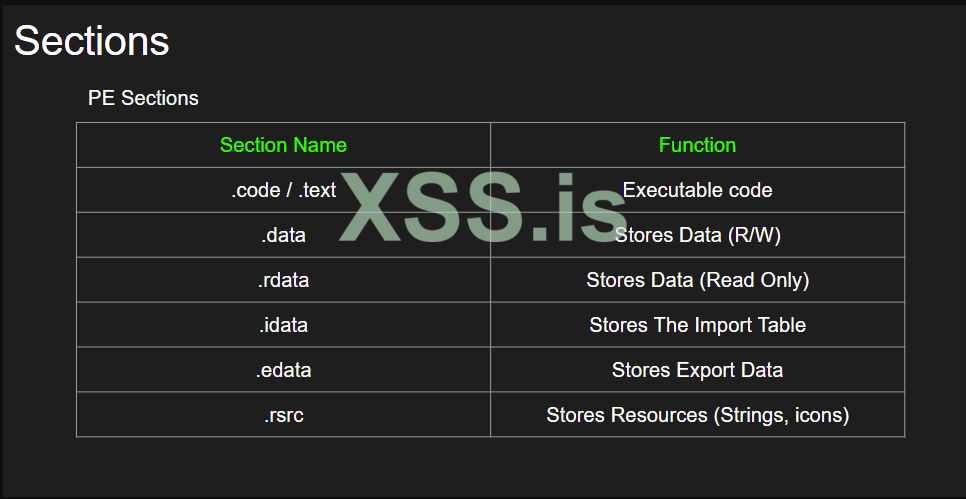
For UPX, when we are dealing with a packed malware sample, if we see the section names, the names will not be coded rdata insetad it will be changed to upx, upx1. That’s another indicator to know the malware sample is packed.
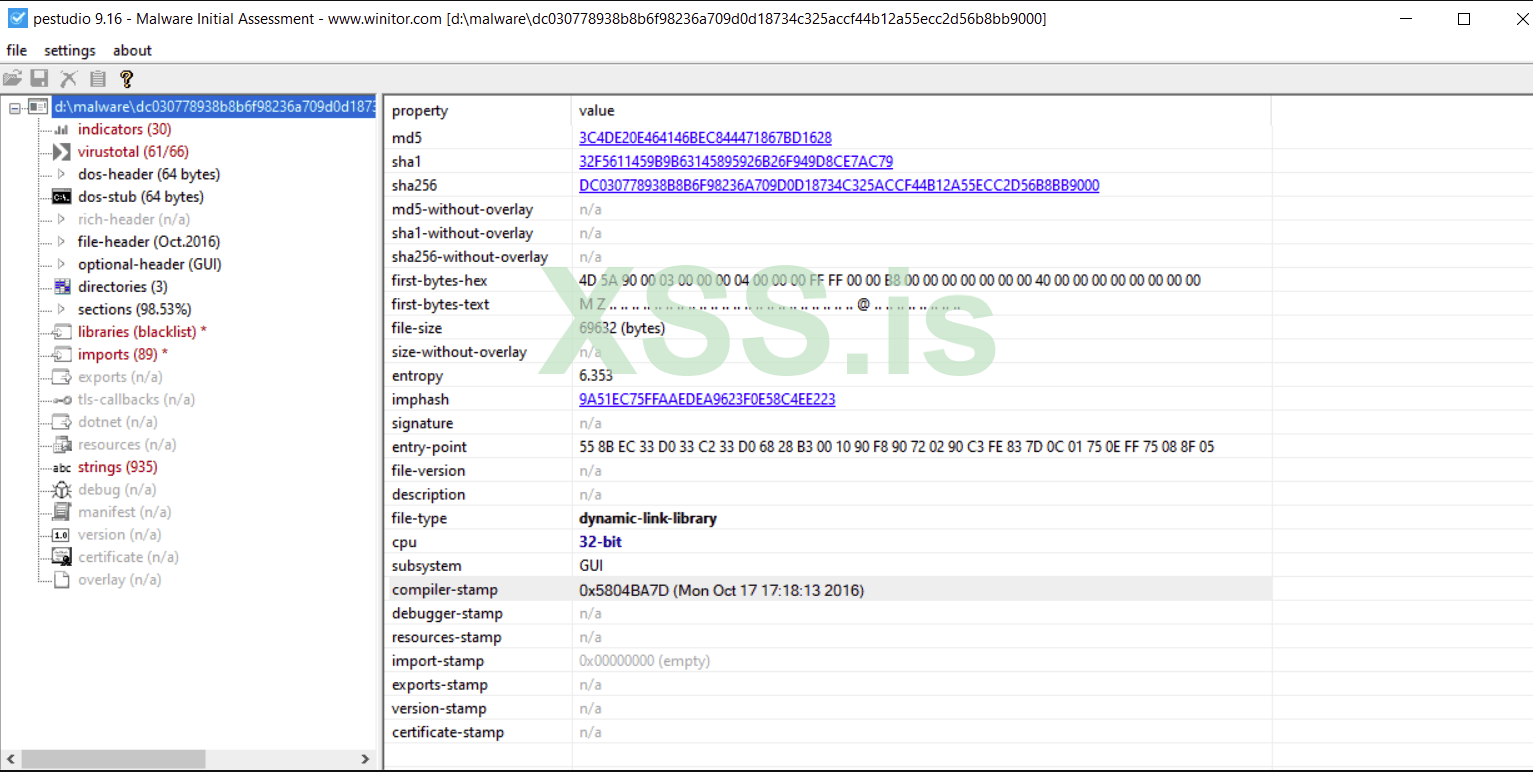
The compiler-stamp indicated when the sample file was compiled
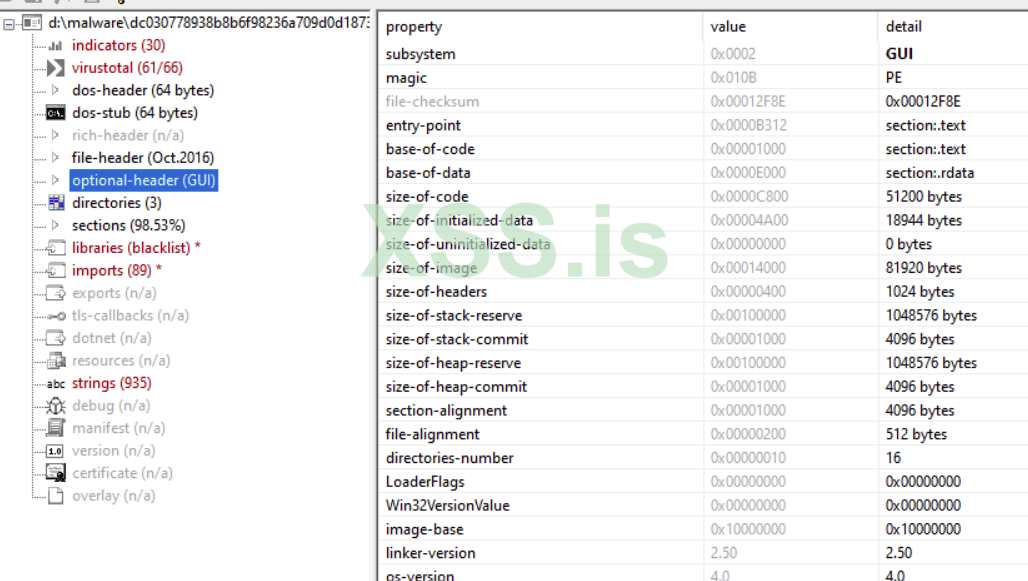
Optional header gives information on which subsystem is used, inclusing size of code, entry point etc.
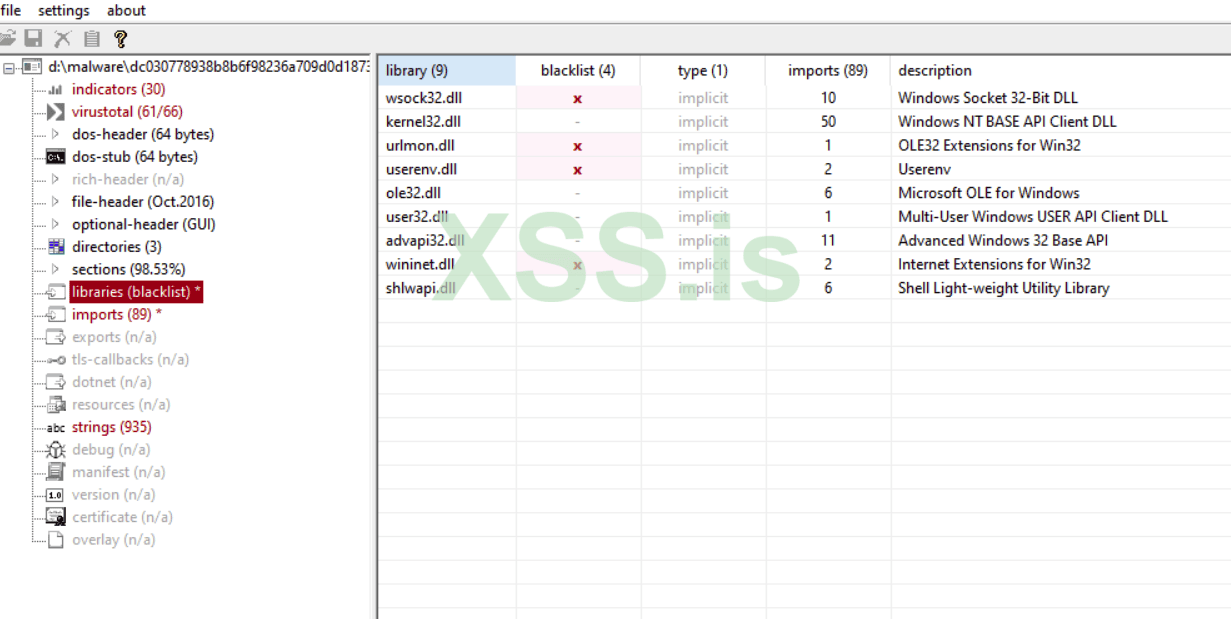
Libraries denote all the dll files that are used
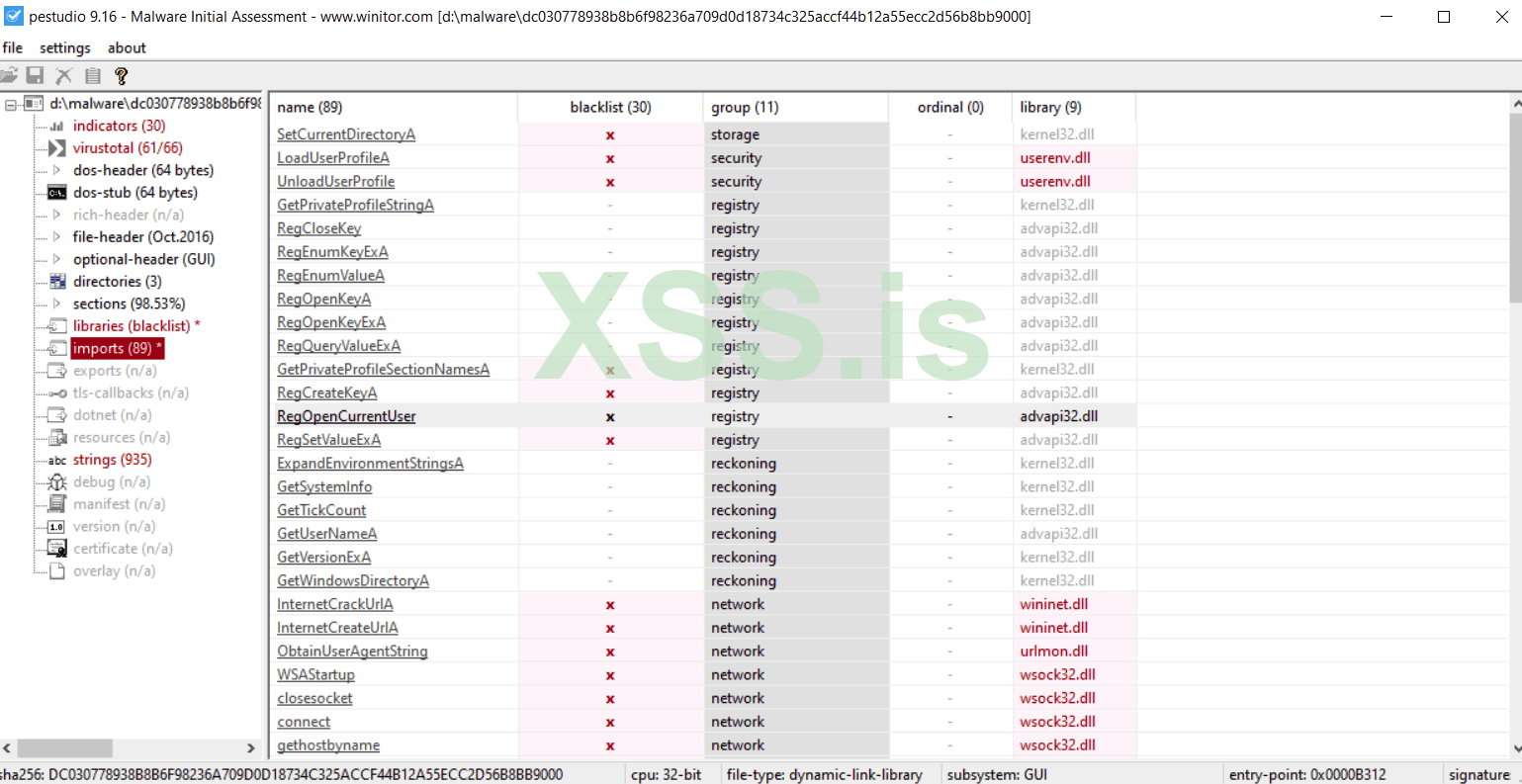
All dlls and its corresponding functions.
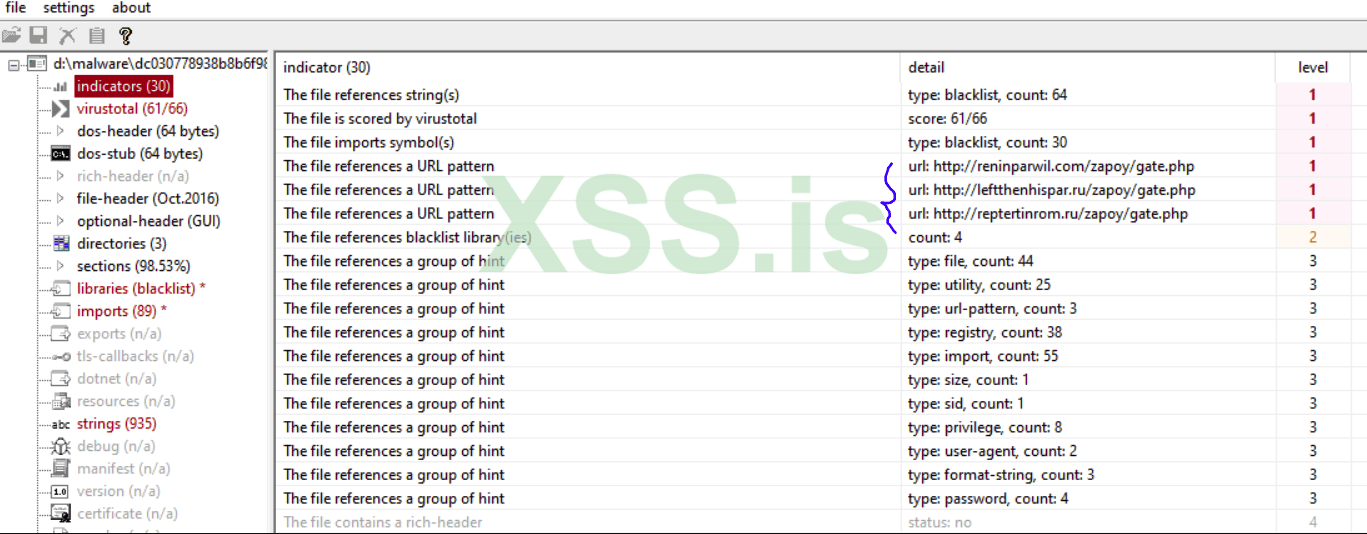
In indicators, we can find three russian domains (c&c), where we get a basic idea of the malware’s origin.