EN:
-----------------------------------------------
Everytime I get a shell from screenconnect exploit and I try a command I get this returned, instead of the command.
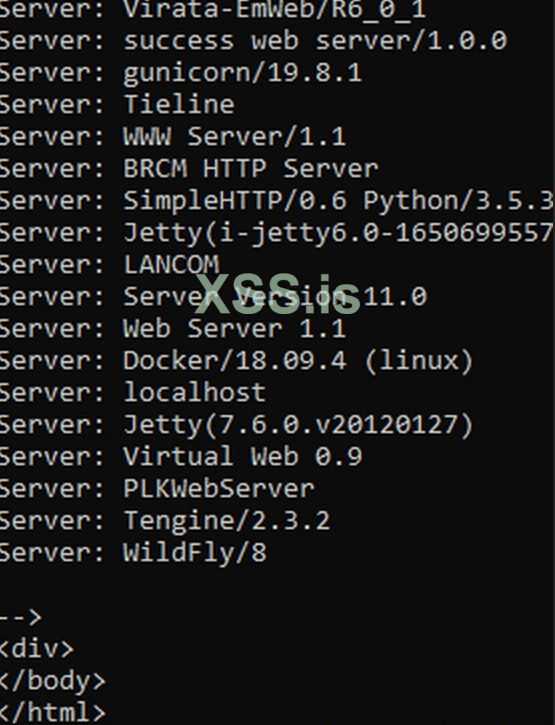
Also tried ping a machine to see if it could communicate with it and no response... What is the issue here? Bad exploit?
RU
--------------------------------------------------------------------------
Каждый раз, когда я получаю оболочку от эксплойта screenconnect и пробую команду, я получаю это вместо команды.
Также попробовал пропинговать машину, чтобы узнать, может ли она с ней связаться, но ответа нет... В чем здесь проблема? Плохой эксплойт?
-----------------------------------------------
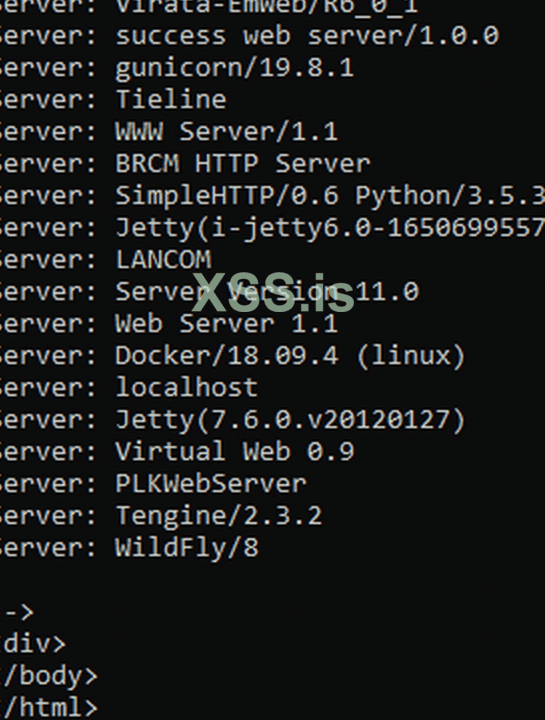
Everytime I get a shell from screenconnect exploit and I try a command I get this returned, instead of the command.
Also tried ping a machine to see if it could communicate with it and no response... What is the issue here? Bad exploit?
RU
--------------------------------------------------------------------------
Каждый раз, когда я получаю оболочку от эксплойта screenconnect и пробую команду, я получаю это вместо команды.
Также попробовал пропинговать машину, чтобы узнать, может ли она с ней связаться, но ответа нет... В чем здесь проблема? Плохой эксплойт?