Hello everybody! There is a problem with which I want to ask you for help. Perhaps it will be useful to someone else.
All this is necessary in order to get a relatively clean IP and DNS of VPN in the last section of network to use any virtual machine through this network.
The host machine is connected to VPN_1, and 3 VirtualBox machines operate on it:
m1. pfSense TOR-gateway configured by manual
m2. pfSense VPN_2-gateway
m3. Windows /or/ Android_x86
From the m2 SSH console DNS will be resolved through OPT1 and from WAN, but from the m3 there is no longer opportunity to use DNS. IP connections work, but DNS - no.
Any idea?
All this is necessary in order to get a relatively clean IP and DNS of VPN in the last section of network to use any virtual machine through this network.
The host machine is connected to VPN_1, and 3 VirtualBox machines operate on it:
m1. pfSense TOR-gateway configured by manual
eth0(WAN): NAT
eth1(LAN): internal_network_1 (192.168.168.0/24) DHCP server
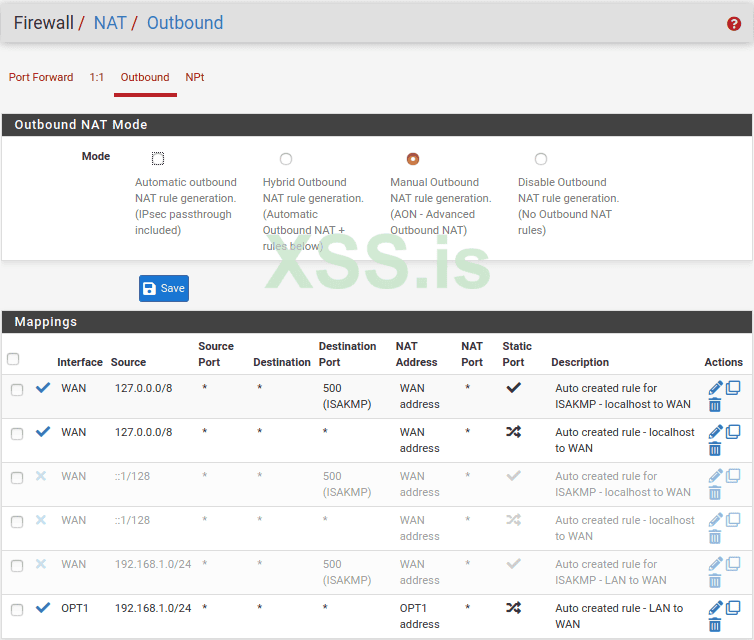
m2. pfSense VPN_2-gateway
eth0(WAN): internal_network_1 (192.168.168.0/24) DHCP client
eth1(LAN): internal_network_2 (192.168.1.0/24) DHCP server
OPT1: ovpn_client (default gateway)
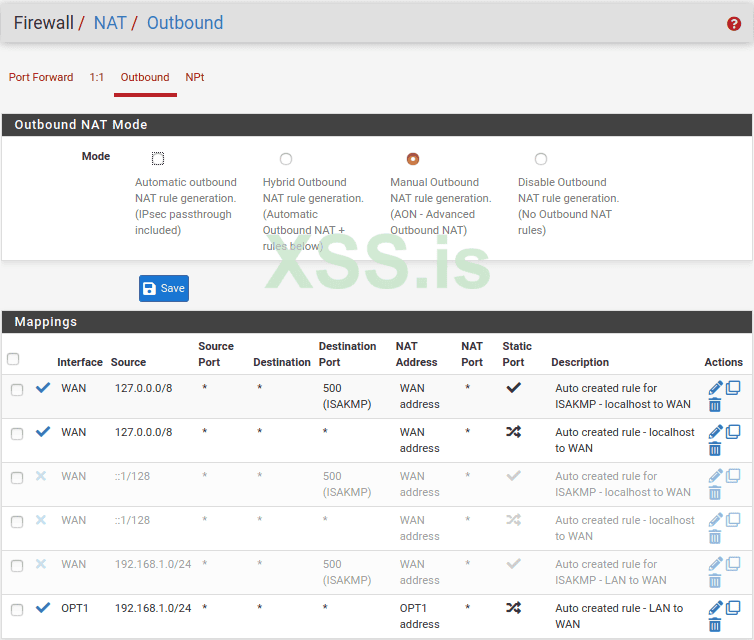
and has 2 DNS server:
10.0.254.1 with OPT1_ovpn as gateway
1.1.1.1 with eth0(WAN) as gateway
DNS Server Override is OFF.
m3. Windows /or/ Android_x86
eth0: internal_network_2 (192.168.1.0/24) DHCP client
From the m2 SSH console DNS will be resolved through OPT1 and from WAN, but from the m3 there is no longer opportunity to use DNS. IP connections work, but DNS - no.
Any idea?