Пожалуйста, обратите внимание, что пользователь заблокирован
- Цена
- 500
- Контакты
- evild34d
Hi,
Did you ever think about protect your Payload/Malware along with bind it with a legit windows programs (example bind or hide your malware with Office software or an Installer..etc) but you haven't found a strong and real Runtime FUD solution! now you are in the right place.
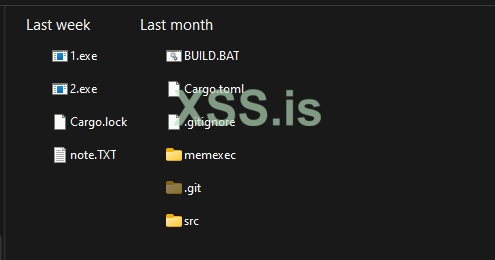
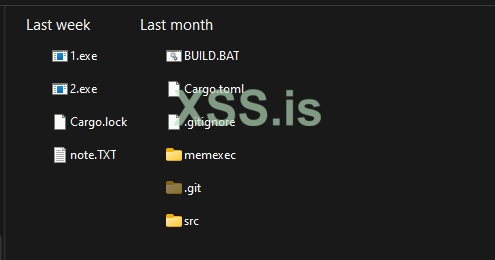
* Coded in Rust, CLI and Stub
* Unlimited EXE size bind (doesn't matter the legit software is 100Mb or 1GB)
* FUD Scantime & Runtime Stub
*Very small size stub
* Bind up to 4 EXE files at once in 4 clicks
* Support execution in memory for Native EXE [C/C++/ASM/Delphi]
* compatible support for non-Native Malwares
* Very long FUD time for the stub due to the nature Rust language and the Implementation.
Selling only 3 copies to keep it private and clean for long time.
Price 500$ per copy. (in case of future detection cleaning is free)
Note1: Your Payload/Malware must be FUD (or Semi FUD) to get best result
Note2 : If your Payload is not clean, I provide cleaning for extra charge
Note2: I work through XSS guarantor!!
Contact via PM or TG: evild34d, Test in live available to show you this amazing tool in action
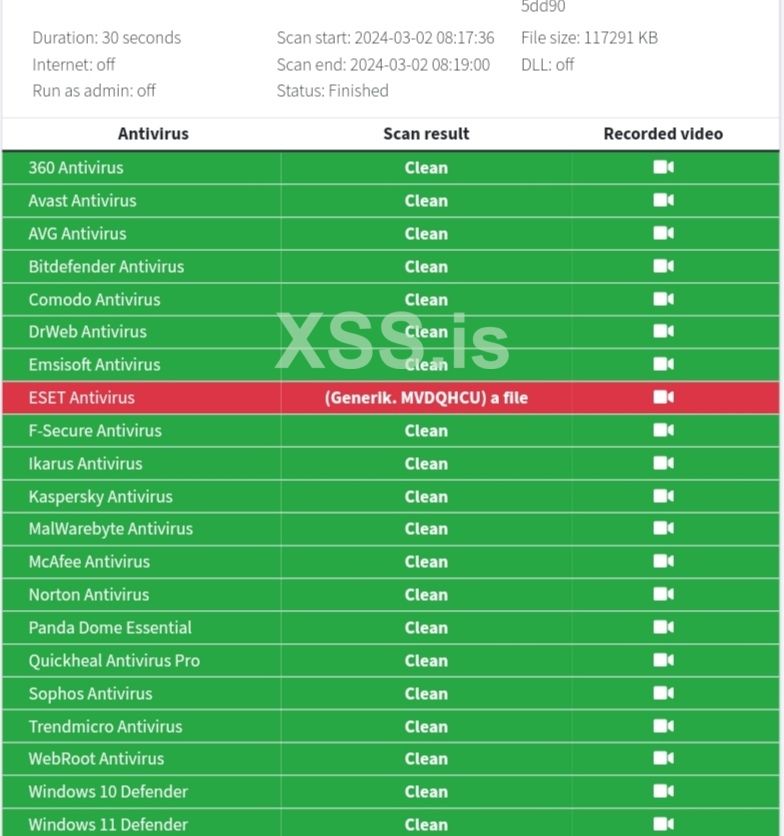
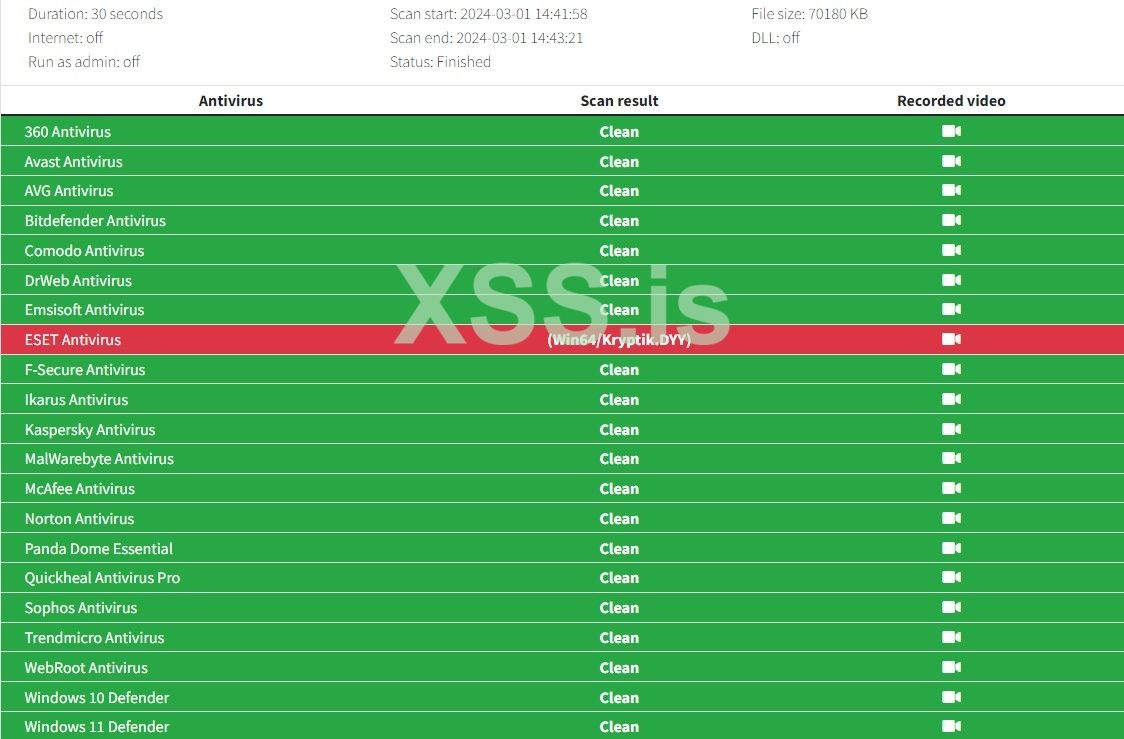
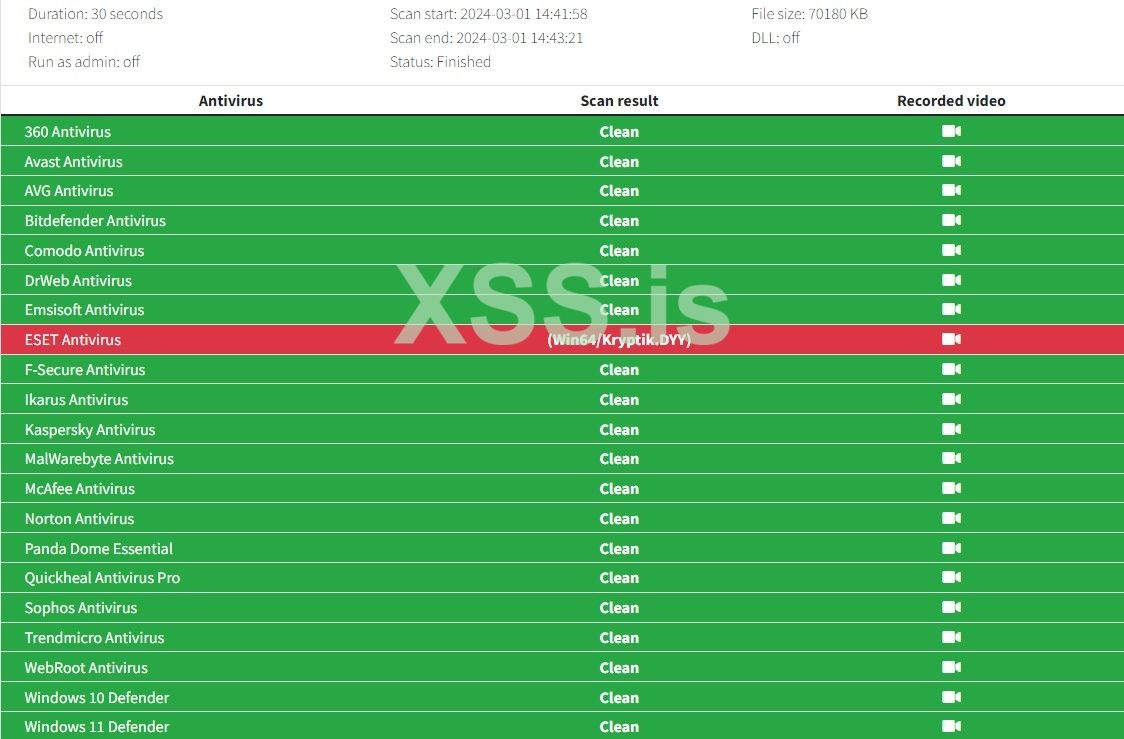
Scan result of two merged EXE's (Malware Payload bind with an Installer): https://scanner.to/result/yKASyMzPdQcQ
Did you ever think about protect your Payload/Malware along with bind it with a legit windows programs (example bind or hide your malware with Office software or an Installer..etc) but you haven't found a strong and real Runtime FUD solution! now you are in the right place.
* Coded in Rust, CLI and Stub
* Unlimited EXE size bind (doesn't matter the legit software is 100Mb or 1GB)
* FUD Scantime & Runtime Stub
*Very small size stub
* Bind up to 4 EXE files at once in 4 clicks
* Support execution in memory for Native EXE [C/C++/ASM/Delphi]
* compatible support for non-Native Malwares
* Very long FUD time for the stub due to the nature Rust language and the Implementation.
Selling only 3 copies to keep it private and clean for long time.
Price 500$ per copy. (in case of future detection cleaning is free)
Note1: Your Payload/Malware must be FUD (or Semi FUD) to get best result
Note2 : If your Payload is not clean, I provide cleaning for extra charge
Note2: I work through XSS guarantor!!
Contact via PM or TG: evild34d, Test in live available to show you this amazing tool in action
Scan result of two merged EXE's (Malware Payload bind with an Installer): https://scanner.to/result/yKASyMzPdQcQ
Последнее редактирование: