I've been experimenting with a lot Cobalt Strike, but I've found that it's not always as effective as I'd like. I'm more accustomed to using terminal-based pentesting tools, and I'm exploring ways to integrate them for better results.
I came across some posts suggesting the setup of a SOCKS proxy on a target within Cobalt Strike. The idea is to configure my pentesting machine to connect through this proxy using the 'socks4 <CS_IP> <Socks_Number>' command. However, despite following these steps, I haven't been able to make it work. I'm curious if there are any approaches or ideas that could achieve this outcome effectively.
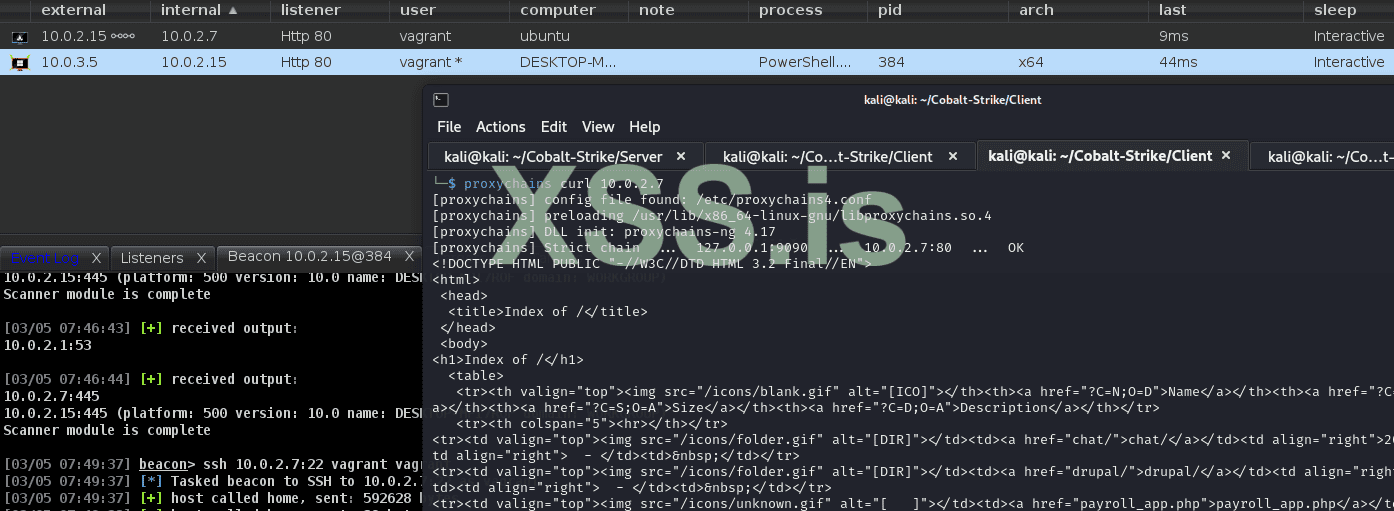
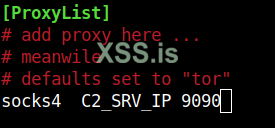
Example:
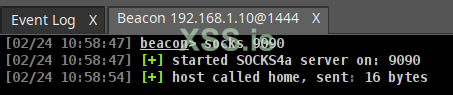
Setting up the Socks on my targets host.
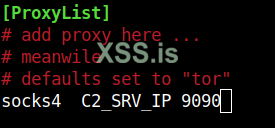
Adding the Proxychains with:
Protocol: Socks4
C2_SRV_IP: My C2 Server IP
Port: Socks Port
After I want to scan the network with nbstscan for example or do any other commands, I get no results back.
Command:
proxychains nbtscan 192.168.1.0/24, no results are returned
I came across some posts suggesting the setup of a SOCKS proxy on a target within Cobalt Strike. The idea is to configure my pentesting machine to connect through this proxy using the 'socks4 <CS_IP> <Socks_Number>' command. However, despite following these steps, I haven't been able to make it work. I'm curious if there are any approaches or ideas that could achieve this outcome effectively.
Example:
Setting up the Socks on my targets host.
Adding the Proxychains with:
Protocol: Socks4
C2_SRV_IP: My C2 Server IP
Port: Socks Port
After I want to scan the network with nbstscan for example or do any other commands, I get no results back.
Command:
proxychains nbtscan 192.168.1.0/24, no results are returned