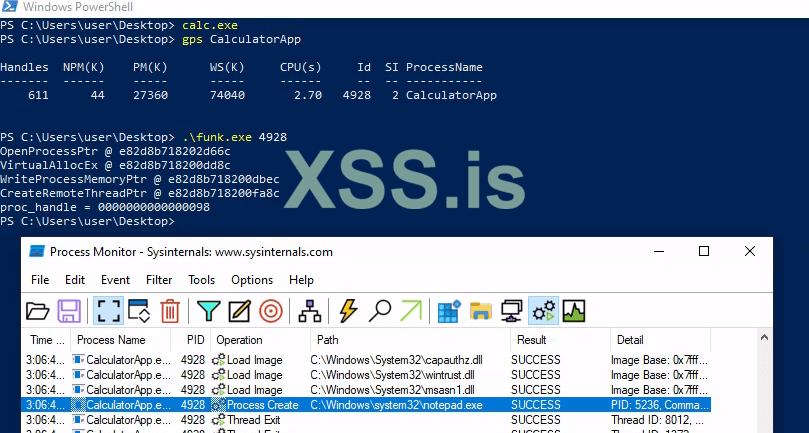
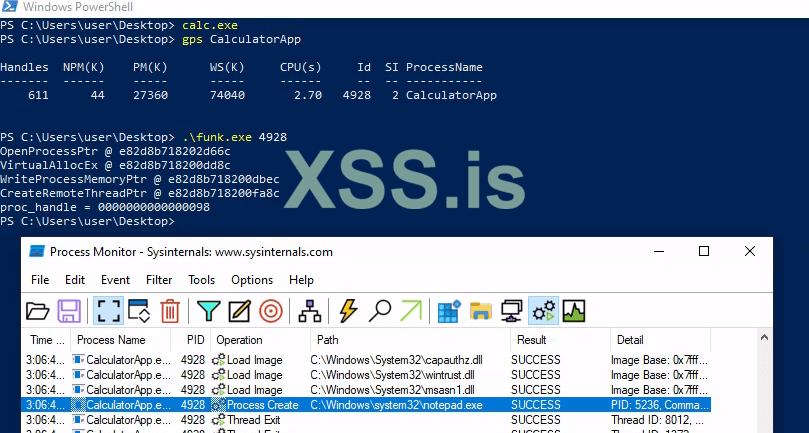
I released the code previously in the thread I was using to write about the injector and the changes I made until reaching this first version. The goal of the project was very basic, make a injector and change it until it can inject code without being detected(only defender was used on tests), also let the code easy to use for other people just include their payload and build.
Since its very simple I will list the "features" from the injector:
I described almost all steps of development on this Thread Evolving from basic
Download Link: https://xss.pro/attachments/77058/
Since its very simple I will list the "features" from the injector:
- Uses API hashing to locate needed WinAPI functions
- Encode WinAPI function pointers with a random 64bit value (XOR)
- FCALL macro to make WinAPI calls more easy
- Custom(very basic) encode/decode method
I described almost all steps of development on this Thread Evolving from basic
Download Link: https://xss.pro/attachments/77058/