I have a proposal for collaboration for private groups, targeted spammers, or initial access brokers. Dont hesitate on talk to me if you have any questions or want to negotiate
Tox: 7227D4331E0B1CEA9918BF5C48AB955D1BC3251B864D0A018FF3D0EDC791980FF34576006816
Tg: @bathory630
Custom spam-payload:
I can code spamming payloads with excellent infection ratios. Spamming payloads coding is currently rough, but I'm experienced enough to build payloads that can perfectly bypass the most common defenses (MS Defender, Avast, AVG, Avira, Nod32, Panda, etc.). and keep having a lifetime of at least 1 week on targeted attacks, I will be checking the evasion ratio and remake the payloads every time needed to support the operations. If you are a spammer (or an initial access broker) that's having struggles with defense evasion on your mail payloads, I can be a high-value member of the team. I can build from the basic pdf->lnk->ps1->dll dropper to sophisticated embedded loaders that can lead to a fileless infection of the machine, so you can go directly from the mail attachment to "Cobaltstrike," leaving almost no trace on the machine (good for opsec).
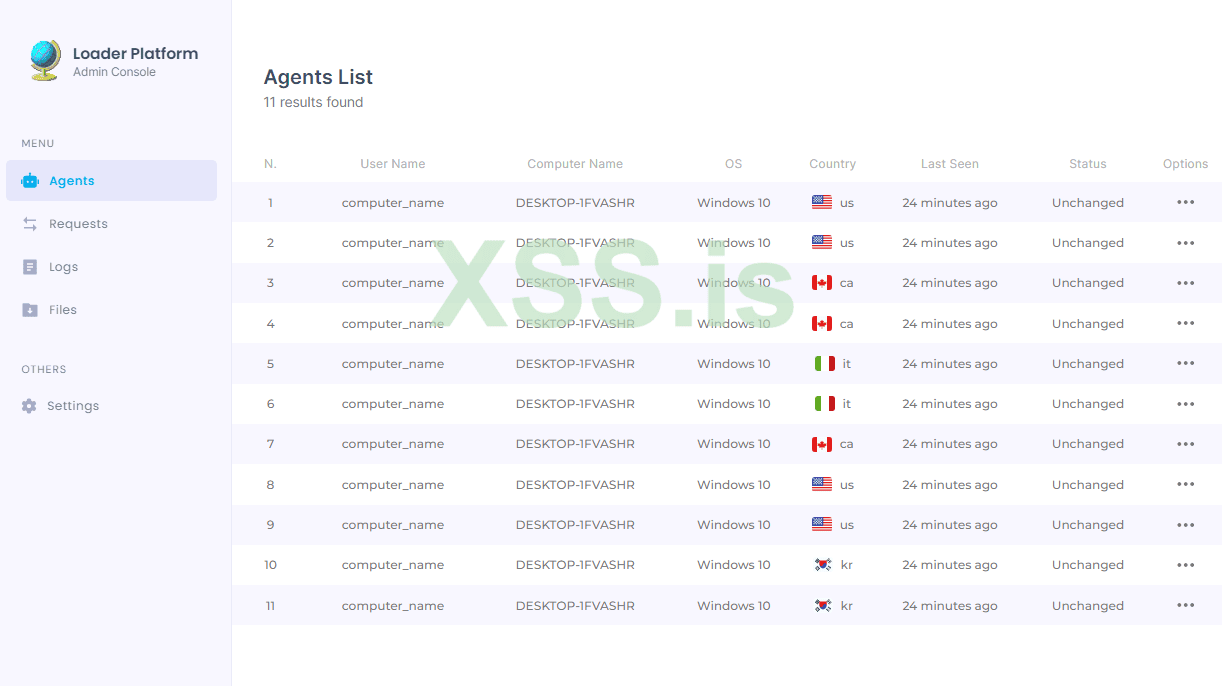
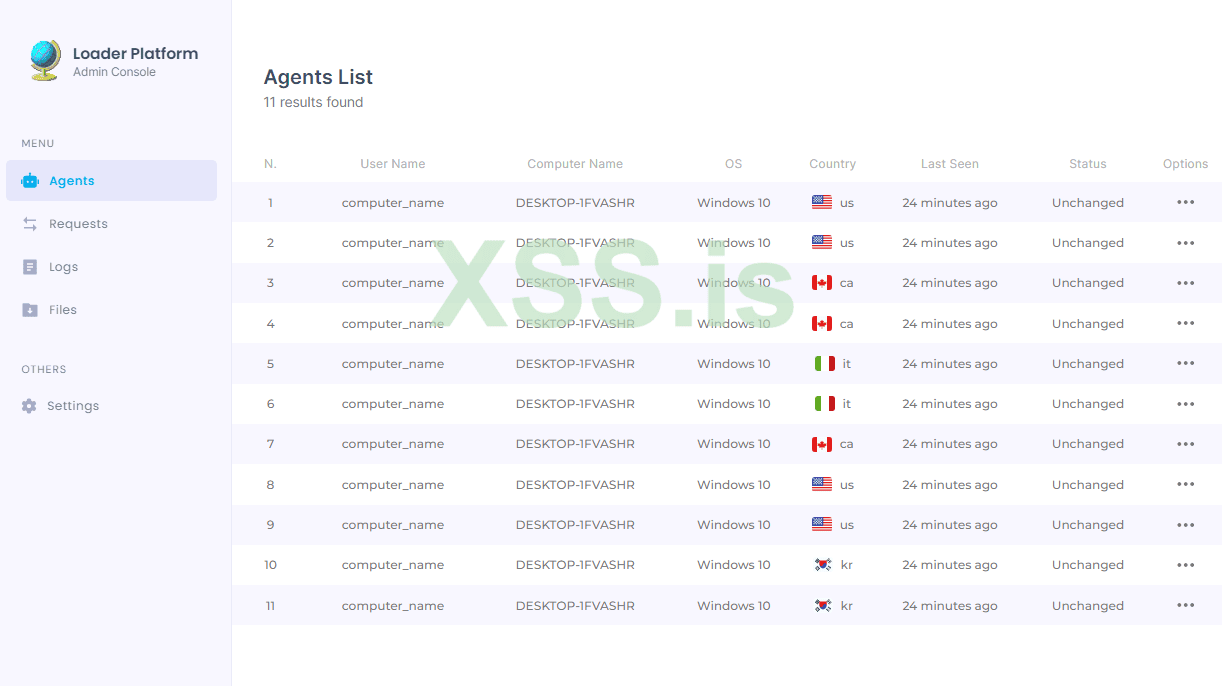
Private advanced loader:
My loader is written in Rust+C, my loader is entirely customized, is compatible with Windows 7 to Windows 11 and can flawlessly evade the majority of defenses (MS-Defender, Kaspersky, Bitdefender, Avast, Avg, Avira, Nod32, Panda, Malwarebytes, and so forth) using dll side loading. The following file types are also available for delivery: .DLL, and .EXE.
Loader capabilities:
- Process injection:
---> EXE payloads
---> Reflective DLLs payloads
- Download, Save, and run
---> EXE payloads
---> DLL payloads (rundll32)
- Execute commands and read output like:
---> net group "Domain Admins" /domain
---> net group "domain computers" /domain
---> nltest /domain_trusts /all_trusts
---> net localgroup "administrator"
---> net view /all /domain
---> net use
Tox: 7227D4331E0B1CEA9918BF5C48AB955D1BC3251B864D0A018FF3D0EDC791980FF34576006816
Tg: @bathory630
Tox: 7227D4331E0B1CEA9918BF5C48AB955D1BC3251B864D0A018FF3D0EDC791980FF34576006816
Tg: @bathory630
Custom spam-payload:
I can code spamming payloads with excellent infection ratios. Spamming payloads coding is currently rough, but I'm experienced enough to build payloads that can perfectly bypass the most common defenses (MS Defender, Avast, AVG, Avira, Nod32, Panda, etc.). and keep having a lifetime of at least 1 week on targeted attacks, I will be checking the evasion ratio and remake the payloads every time needed to support the operations. If you are a spammer (or an initial access broker) that's having struggles with defense evasion on your mail payloads, I can be a high-value member of the team. I can build from the basic pdf->lnk->ps1->dll dropper to sophisticated embedded loaders that can lead to a fileless infection of the machine, so you can go directly from the mail attachment to "Cobaltstrike," leaving almost no trace on the machine (good for opsec).
Private advanced loader:
My loader is written in Rust+C, my loader is entirely customized, is compatible with Windows 7 to Windows 11 and can flawlessly evade the majority of defenses (MS-Defender, Kaspersky, Bitdefender, Avast, Avg, Avira, Nod32, Panda, Malwarebytes, and so forth) using dll side loading. The following file types are also available for delivery: .DLL, and .EXE.
Loader capabilities:
- Process injection:
---> EXE payloads
---> Reflective DLLs payloads
- Download, Save, and run
---> EXE payloads
---> DLL payloads (rundll32)
- Execute commands and read output like:
---> net group "Domain Admins" /domain
---> net group "domain computers" /domain
---> nltest /domain_trusts /all_trusts
---> net localgroup "administrator"
---> net view /all /domain
---> net use
Tox: 7227D4331E0B1CEA9918BF5C48AB955D1BC3251B864D0A018FF3D0EDC791980FF34576006816
Tg: @bathory630