Пожалуйста, обратите внимание, что пользователь заблокирован
drpalpatine $900
forum profile - https://xss.pro/members/235794/
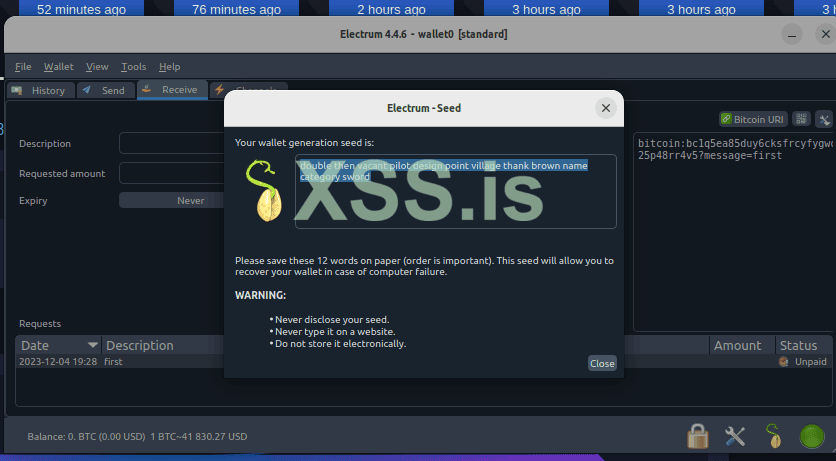
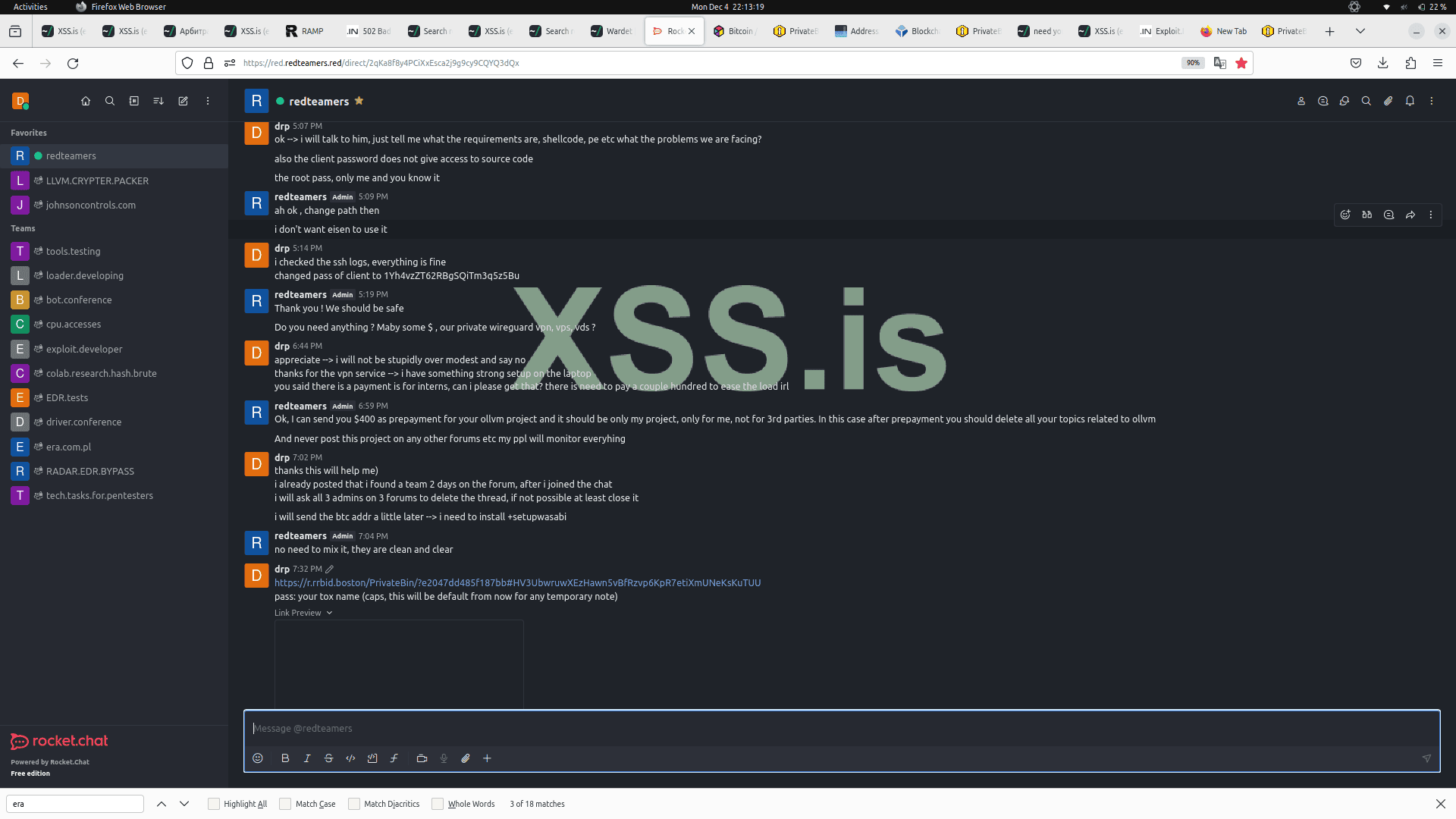
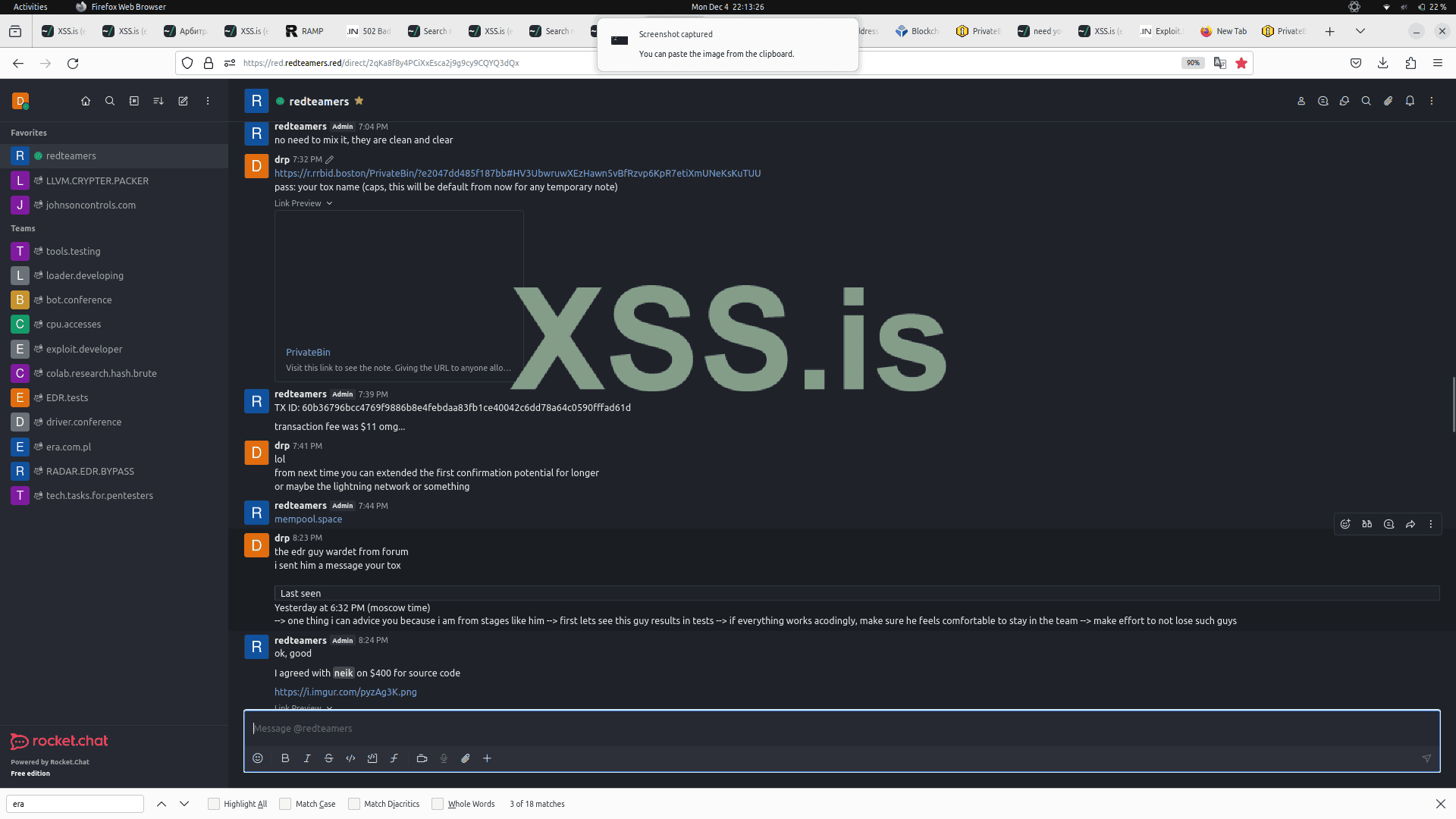
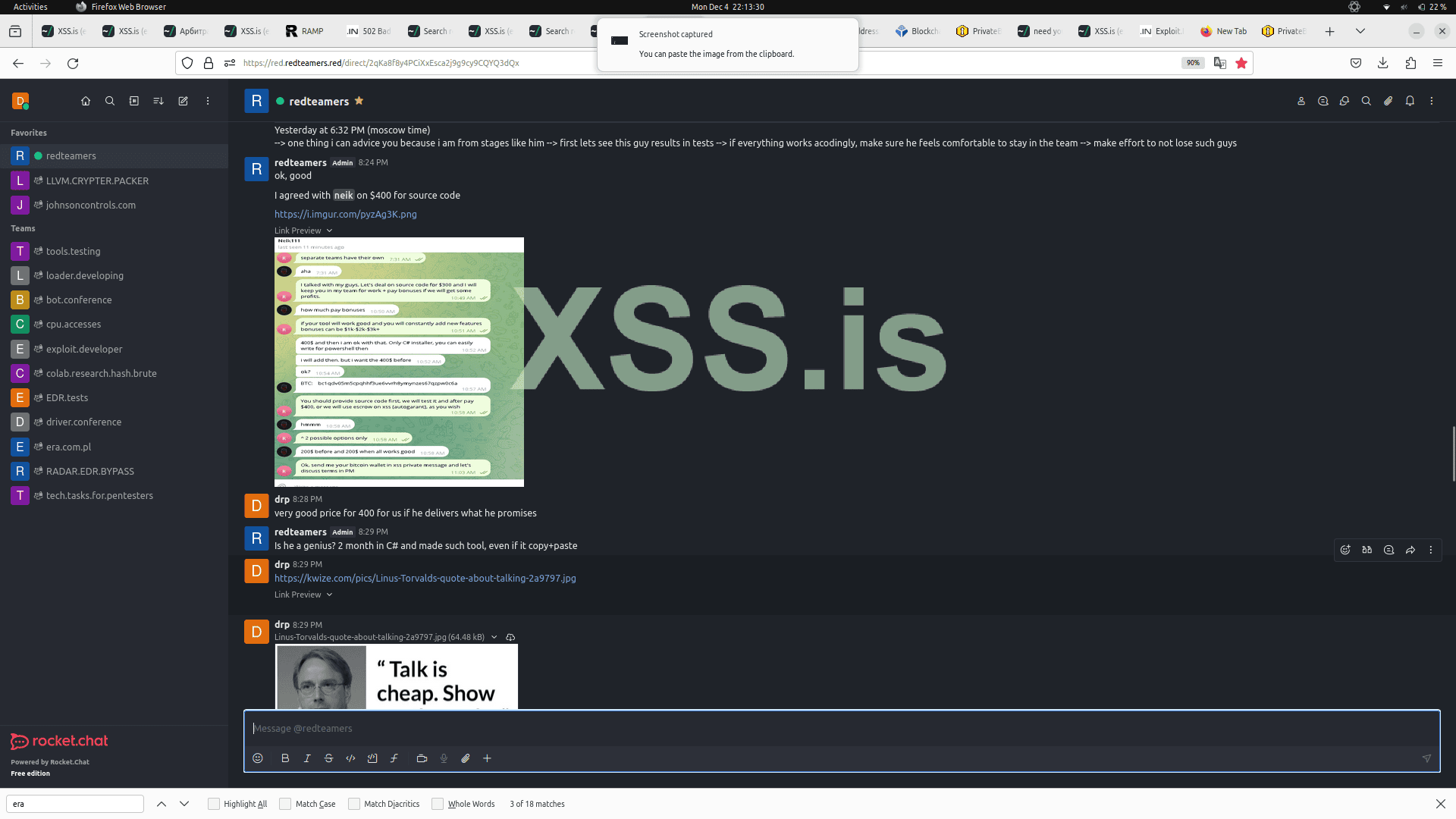
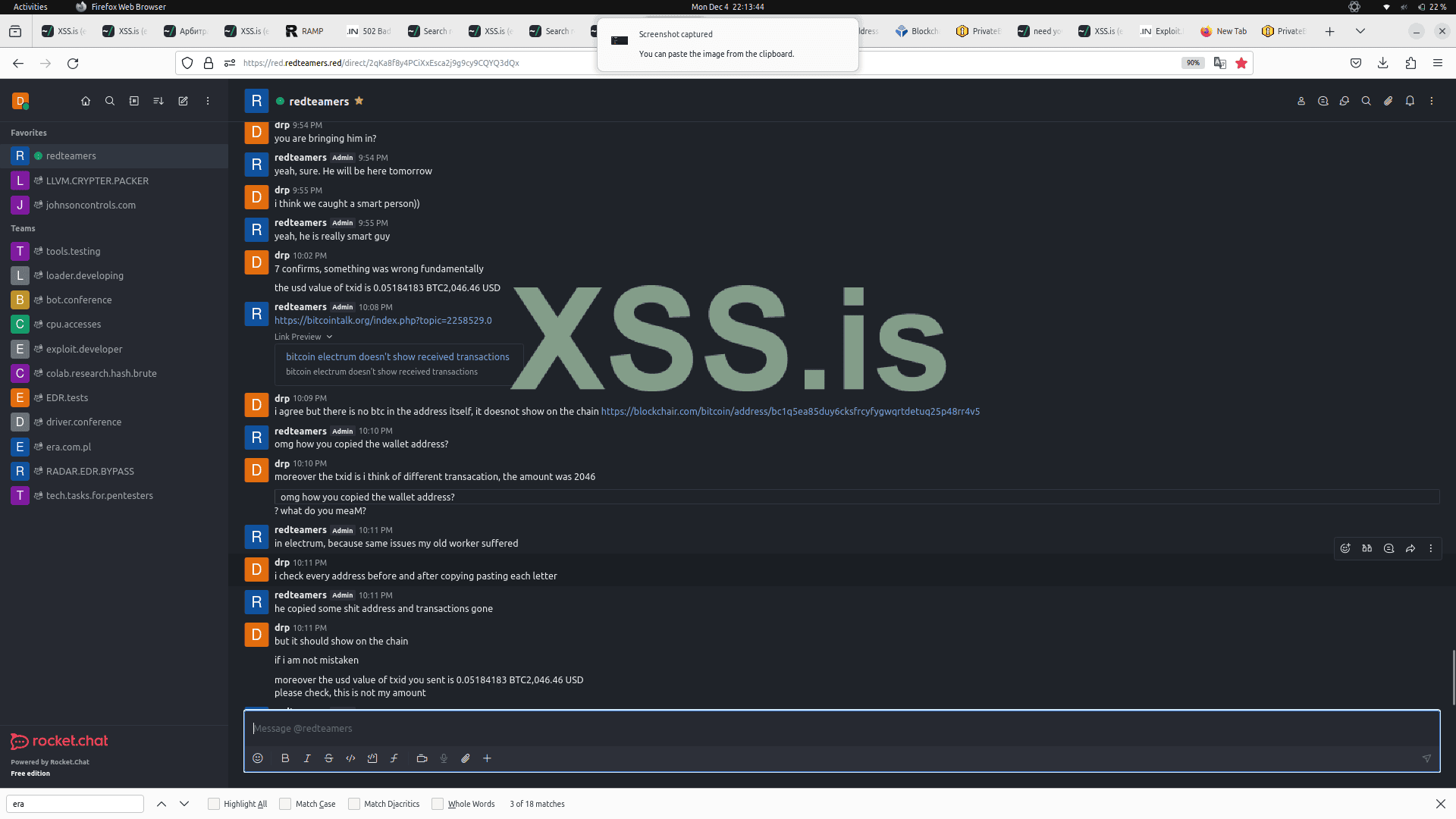
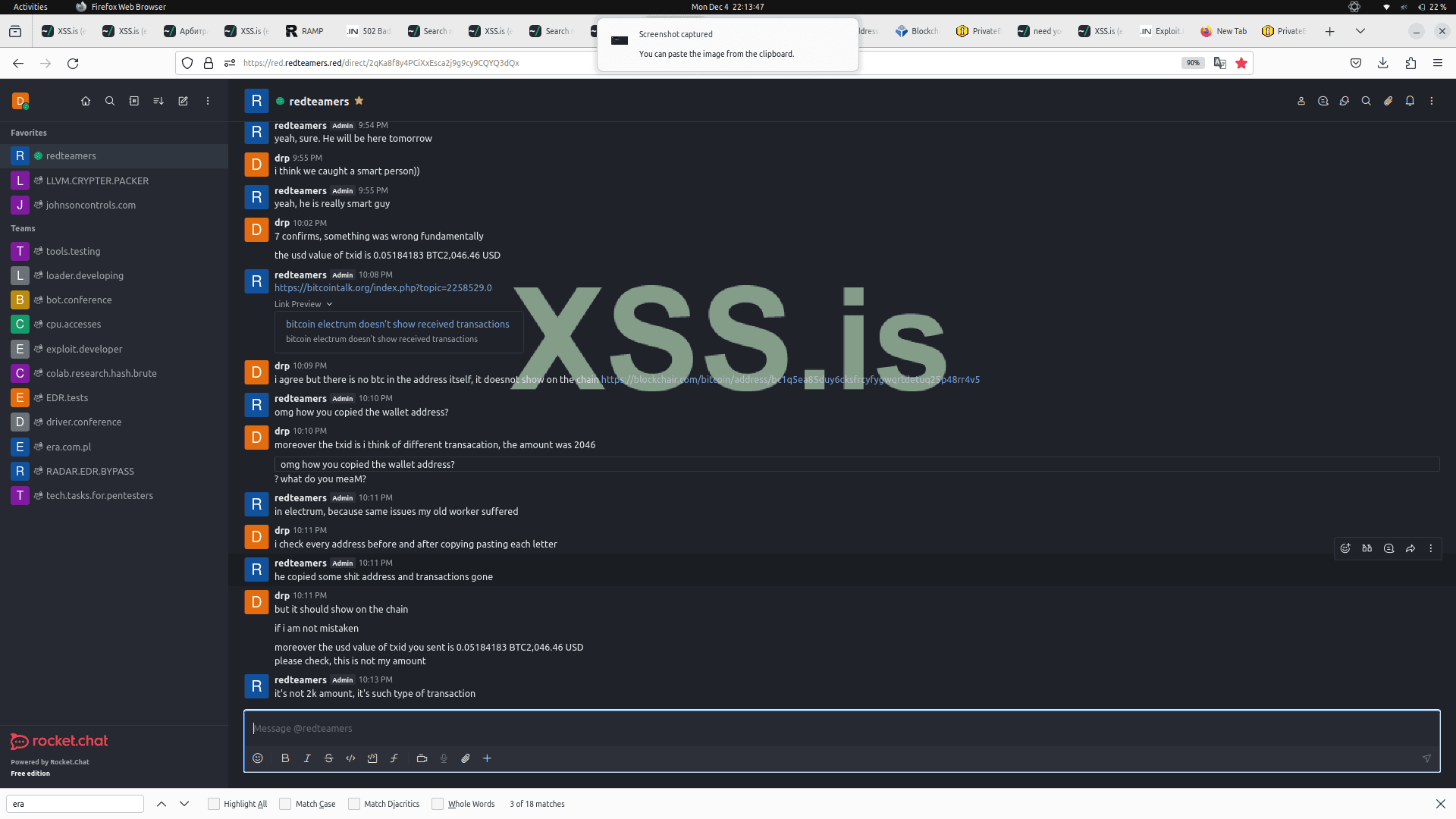
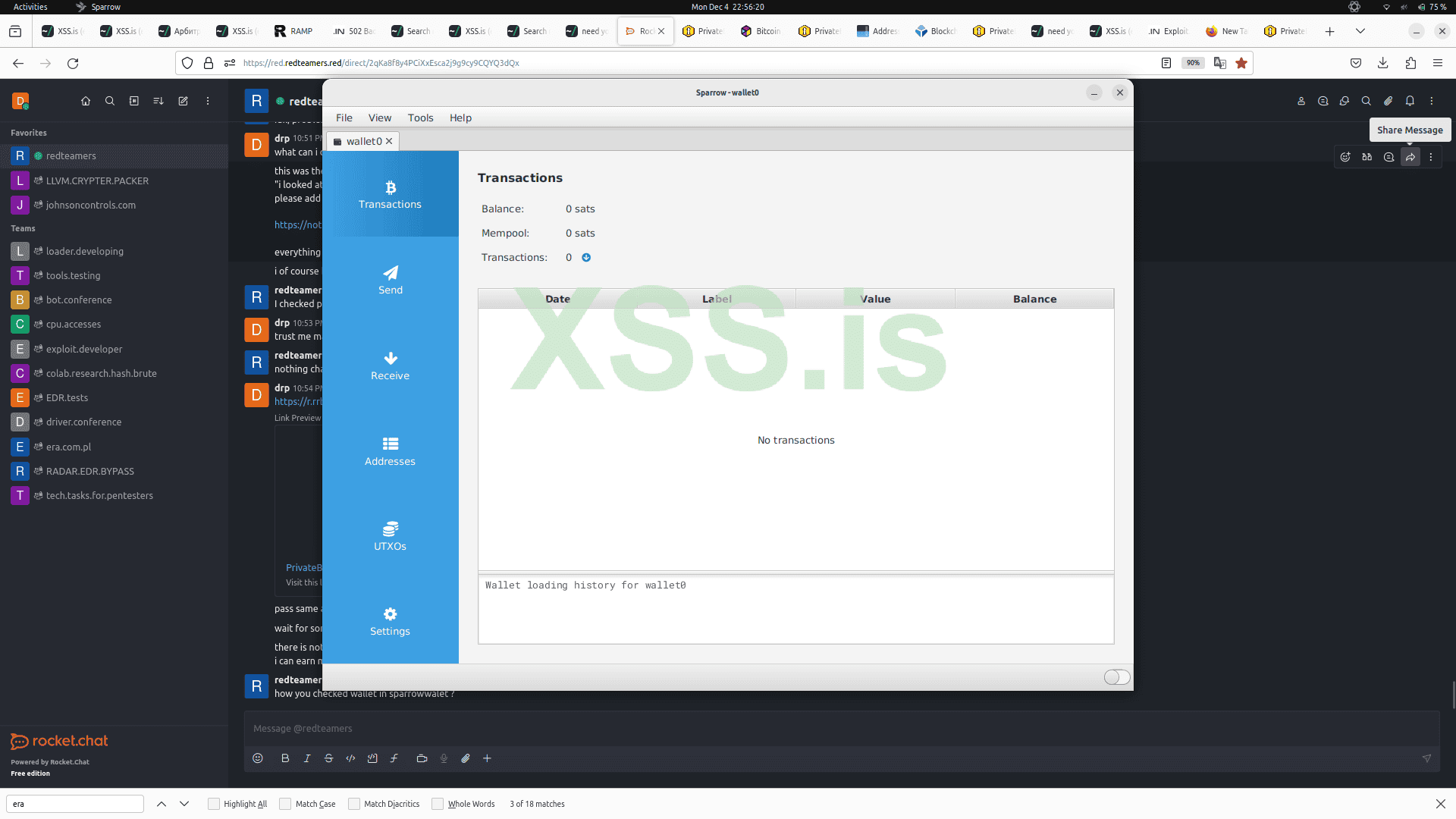
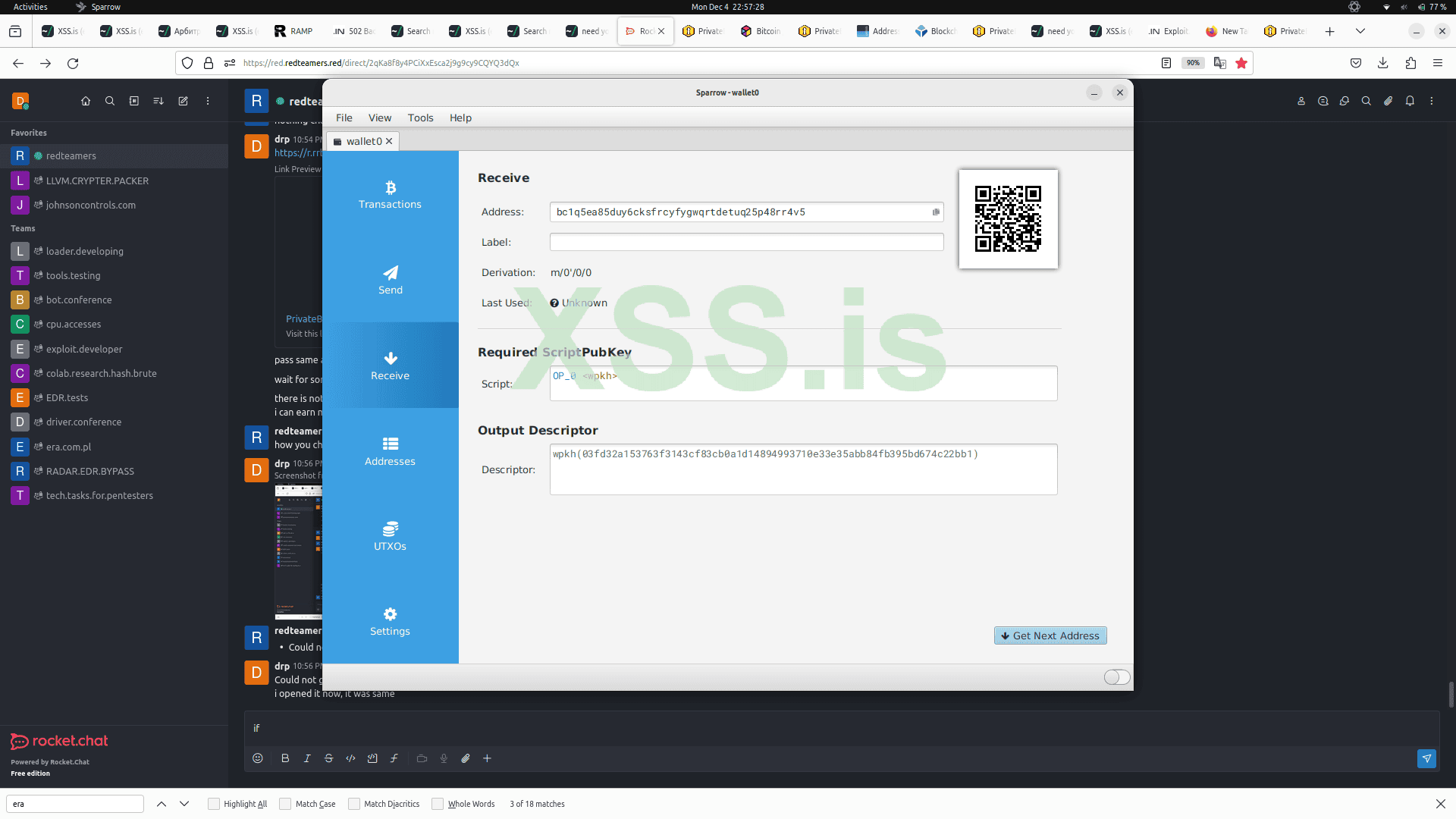
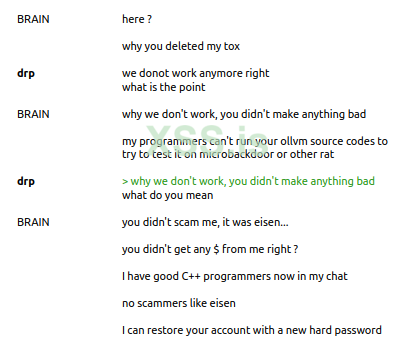
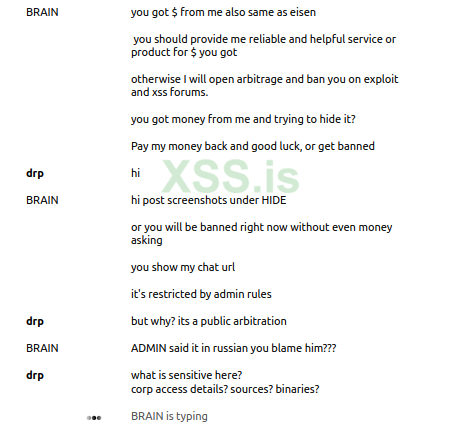
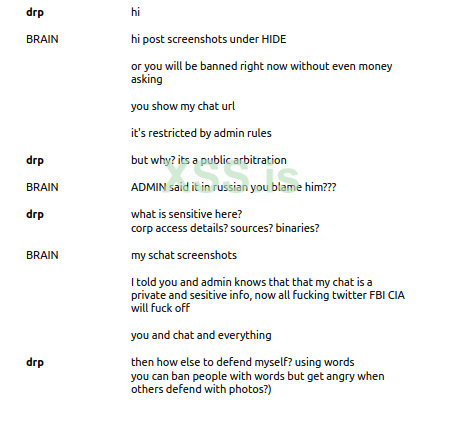
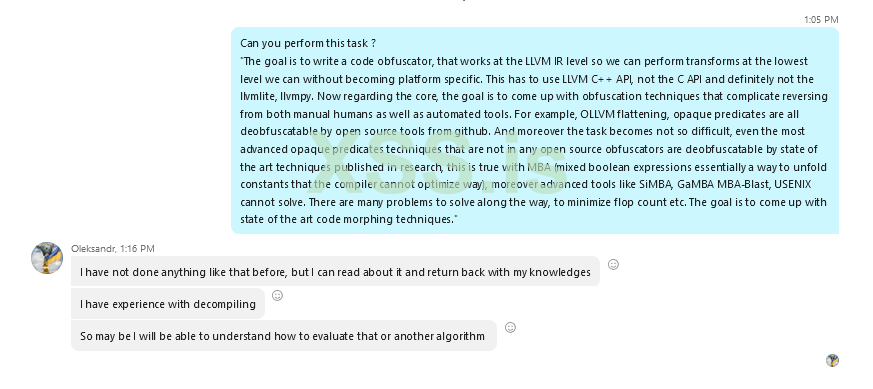
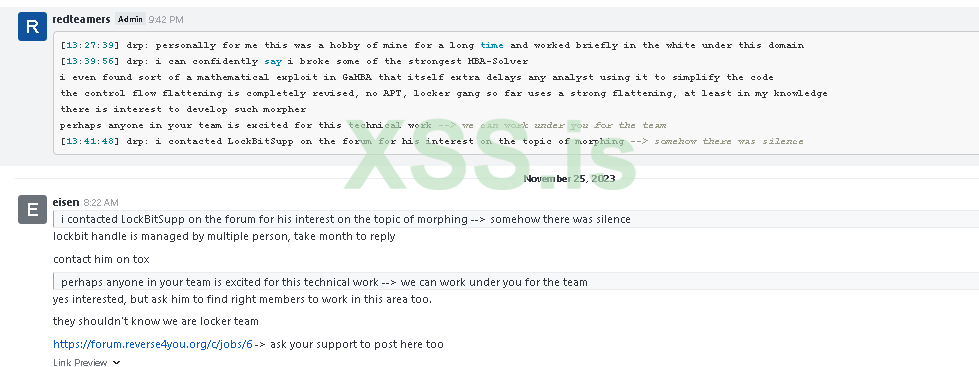
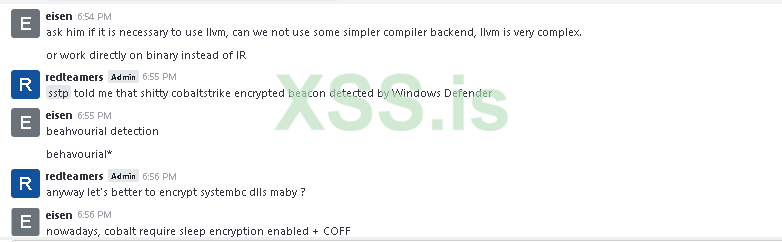
вливался в доверие долгое время в токсе втирая мне что он гуру кодер и пентестер и его приват проект OLLVM++ обходит все ТОП EDR включая CrowdStrike, Sentinel, Cortex, Trellix итп
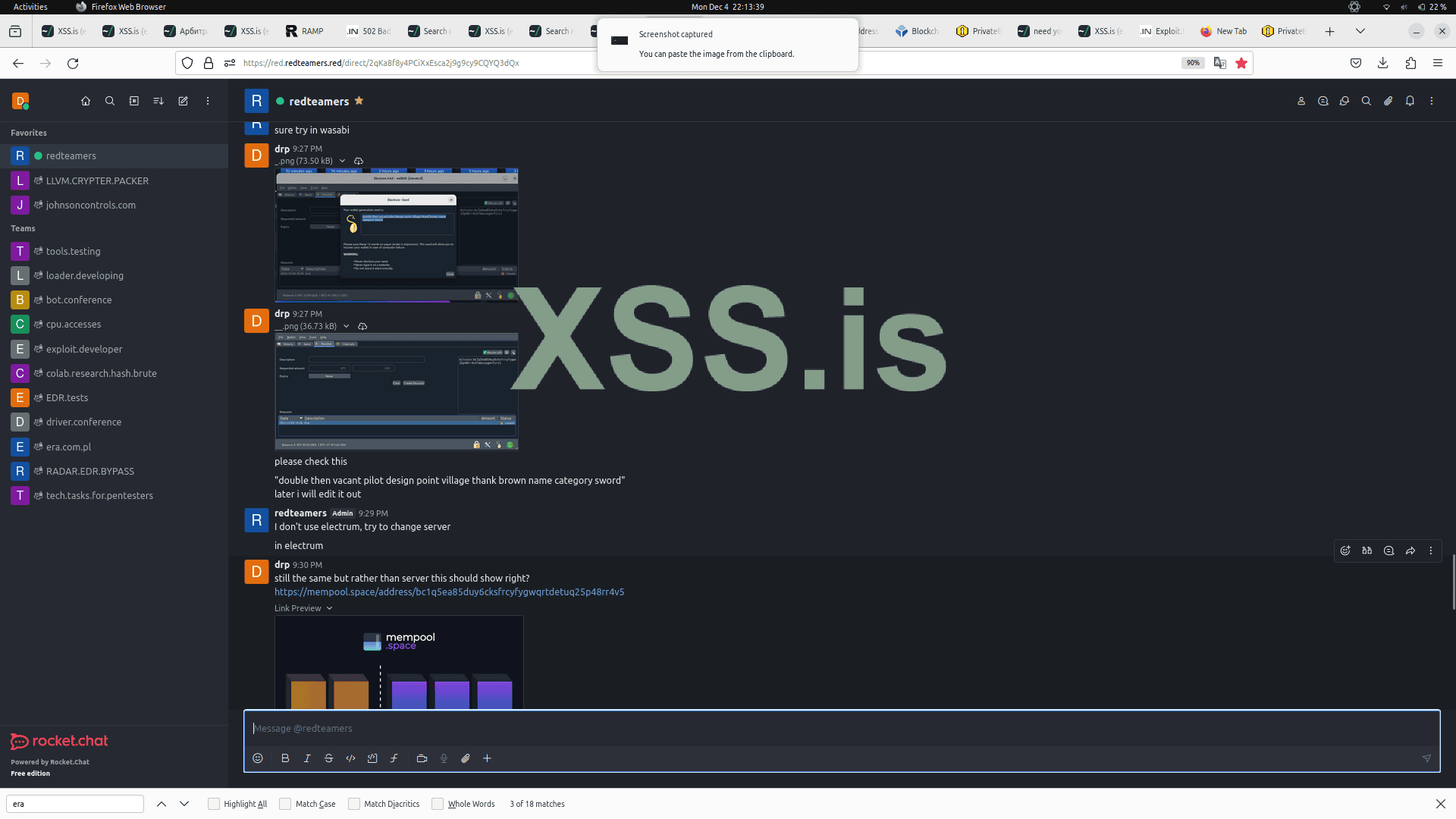
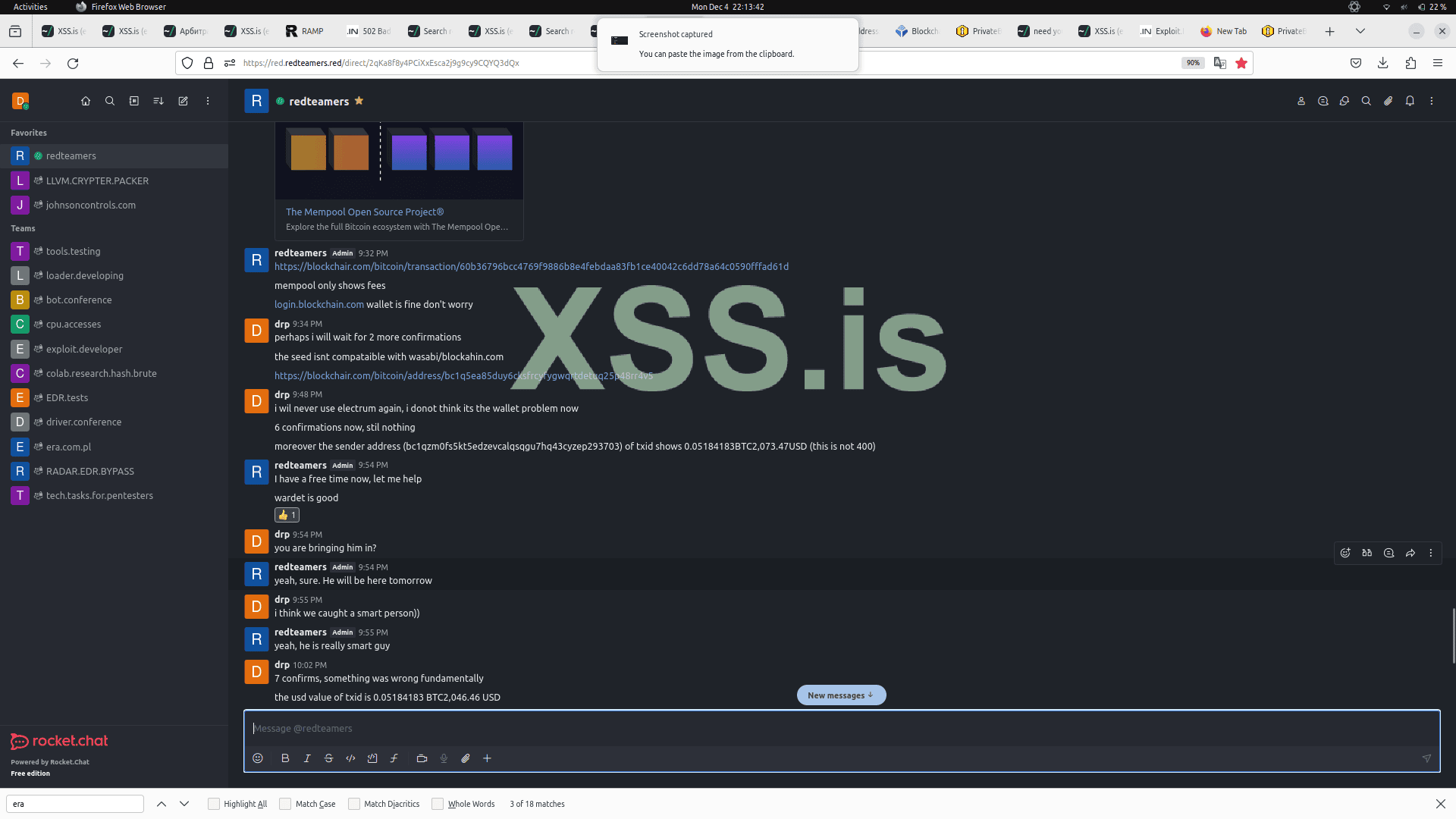
в итоге стянул с меня $900 и ушел в офф как крыса последняя, а сейчас приплетает каких-то третих лиц, мотивируя что все это я и во всем виноват я =)
admin bratva лог переписки скину в лс по запросу
forum profile - https://xss.pro/members/235794/
вливался в доверие долгое время в токсе втирая мне что он гуру кодер и пентестер и его приват проект OLLVM++ обходит все ТОП EDR включая CrowdStrike, Sentinel, Cortex, Trellix итп
в итоге стянул с меня $900 и ушел в офф как крыса последняя, а сейчас приплетает каких-то третих лиц, мотивируя что все это я и во всем виноват я =)
admin bratva лог переписки скину в лс по запросу