Пожалуйста, обратите внимание, что пользователь заблокирован
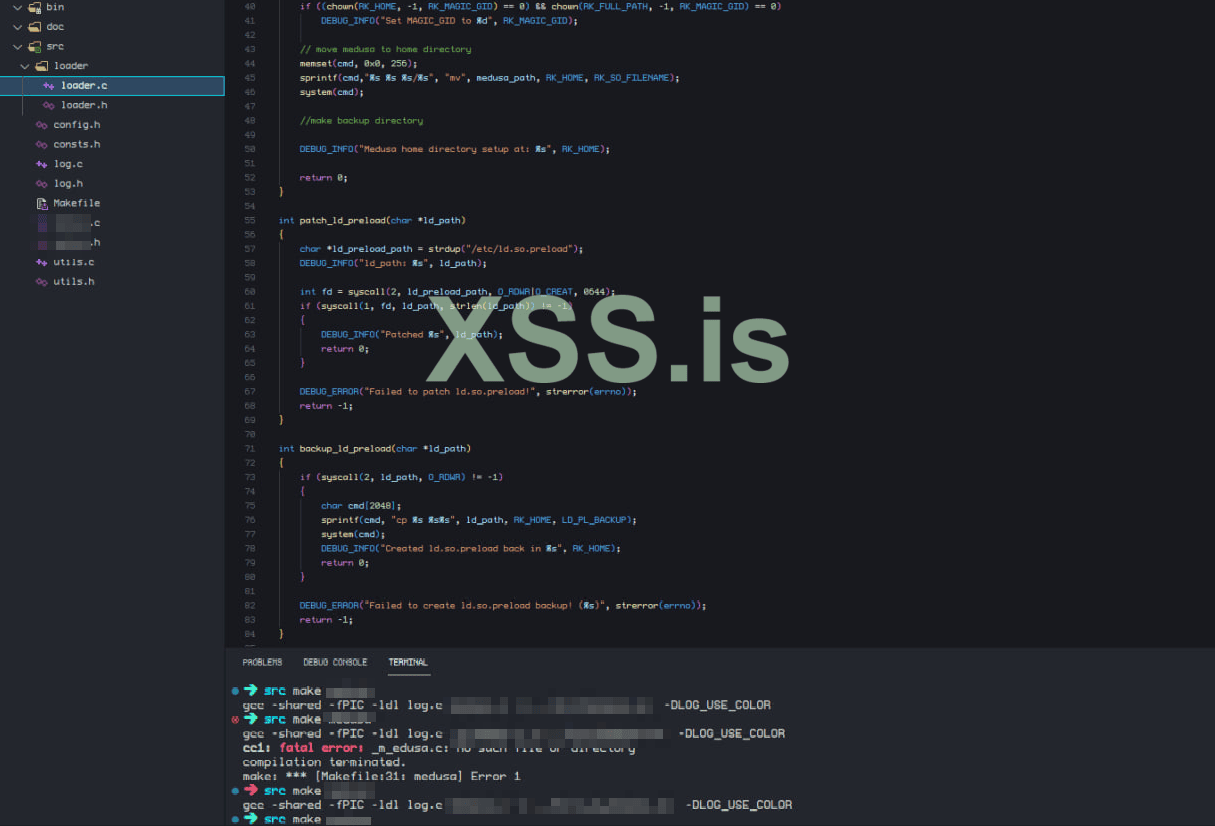
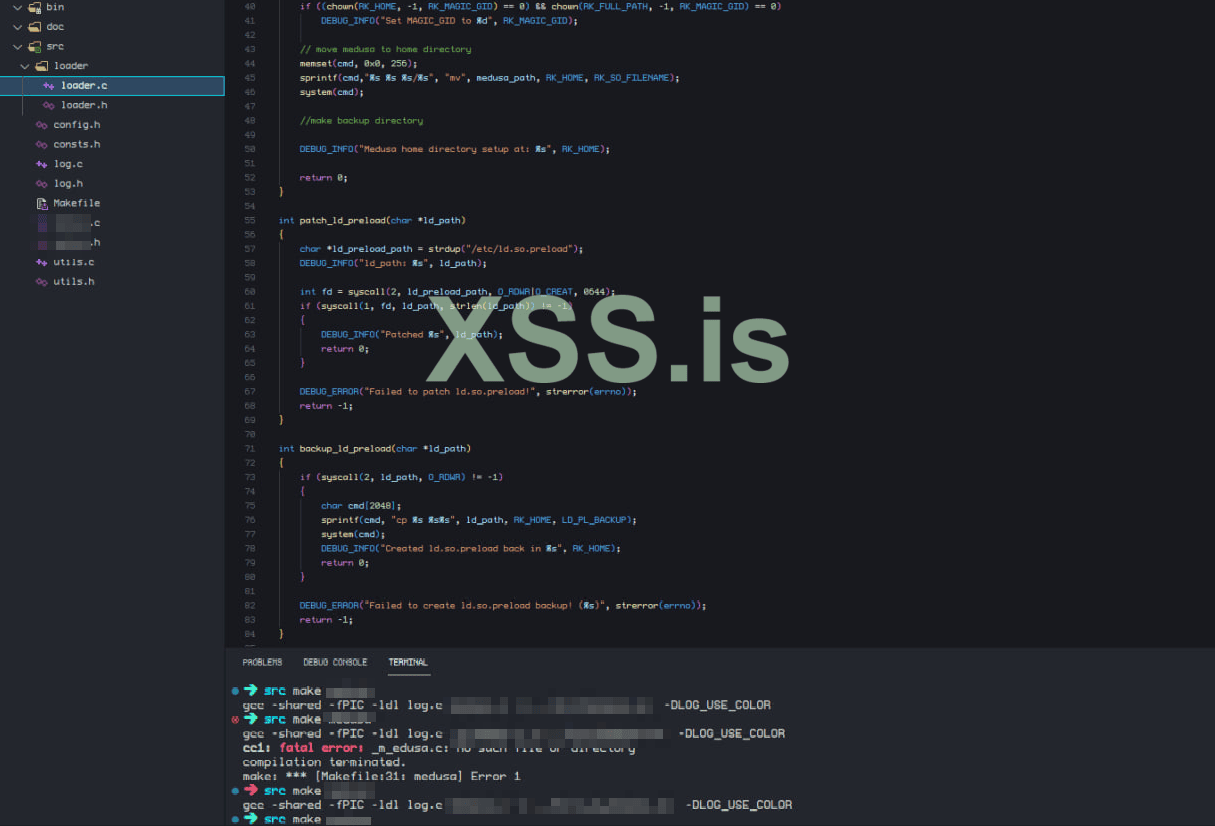
NOTE: There were previously claims of my rootkit source code being leaked... It HAS NEVER been leaked. The person that leaked said code is lying, and just wants to detour sales of my product. Check below for screenshots on my code with actual proof, that this code is in fact... NOT public!
THIS CODE HAS NOTHING TO DO WITH NzT rootkit, NzT is a Windows based project!
SyM Linux Rootkit
SyM is a universal user-mode Linux rootkit that will sustainability hold root persistence across all Linux kernel versions, and will successfully bypass any EDR or rootkit detection software. SyM will also come with a plethora of features capable of stealing important files such as SQL database backups, .git, and other configuration files; And much more. Along with being the first of it's kind SyM implements some API system call hooking that has never been seen before which makes it such a unique, and undetectable rootkit experience.
eBPF:
Internal System Logging:
Hiding self / rootkit
EDR Bypass / Evasion
File stealer
Pricing
Screenshots
Contact
THIS CODE HAS NOTHING TO DO WITH NzT rootkit, NzT is a Windows based project!
SyM Linux Rootkit
SyM is a universal user-mode Linux rootkit that will sustainability hold root persistence across all Linux kernel versions, and will successfully bypass any EDR or rootkit detection software. SyM will also come with a plethora of features capable of stealing important files such as SQL database backups, .git, and other configuration files; And much more. Along with being the first of it's kind SyM implements some API system call hooking that has never been seen before which makes it such a unique, and undetectable rootkit experience.
eBPF:
- Utilizes eBPF to detour and hide network activity of your configuration, by utilizing a magic packet.
- ICMP backdoor
Use a unique magic identifier to open a reverse shell - accept () backdoor
Use a unique magic identify to open a listening TCP server - PAM backdoor
Direct interactive SSH backdoor with custom hidden port, username, and password
Internal System Logging:
- SSH Log
Log all incoming and outgoing SSH authorizations in plaintext by hooking pam_vprompt, read, and write API calls - Execution log
Log all normal (including root) user command execution flow
Hiding self / rootkit
- Hide all files, processes, open ports, and all connections based on unique magic identifier
- Hide process map files, to prevent direct mapping of process and being able to identify rootkit
- Hide any file, or directory of choice
- All rootkit master created directories and files will be kept track of, so no need to manually add or edit anything to keep it hidden!
- Note: It is possible to forge or fake as any other installed software, service, or similar
EDR Bypass / Evasion
- Looking API calls to hide it's self from / proc * / * maps as well as many other system locations
- Bypassing SELinux and GRSec
- Bypasses and hides from SentinelOne and other similar software
File stealer
- By scanning and keeping tracking of a user made list of interesting files and directories the rootkit is capable of stealing anything on the fly and uploading it directly to an external server
- Stuff like SQL databases are stolen automatically by default!
Pricing
- Source Code: $ 5000
Screenshots
Contact
- Telegram: https://t.me/succumb
