Пожалуйста, обратите внимание, что пользователь заблокирован
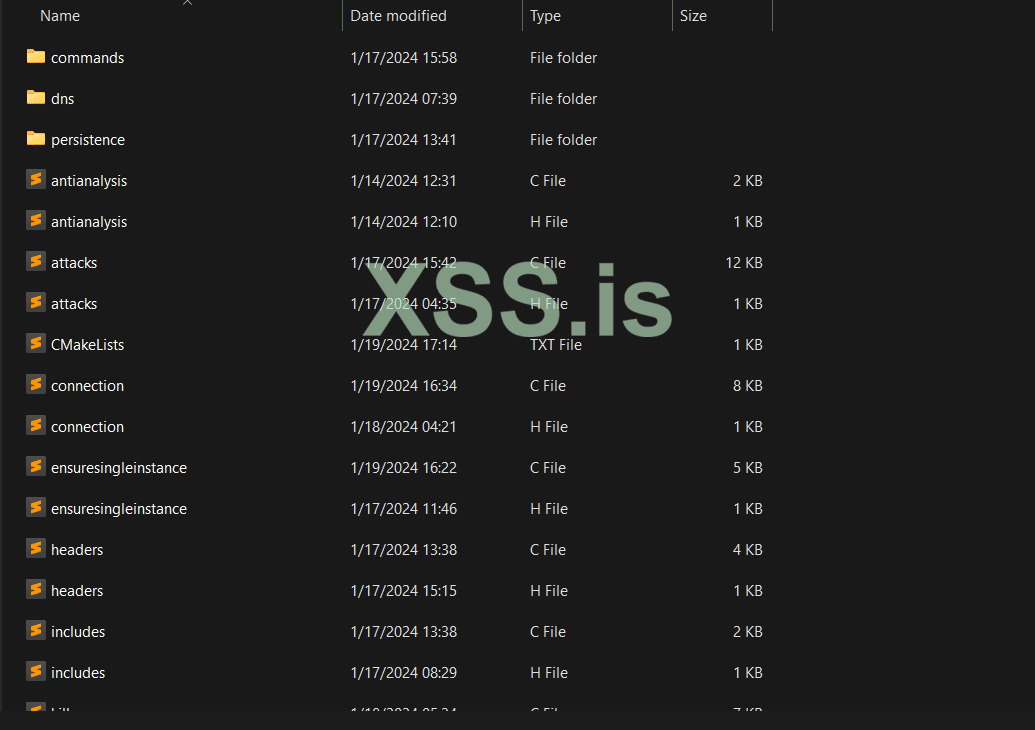
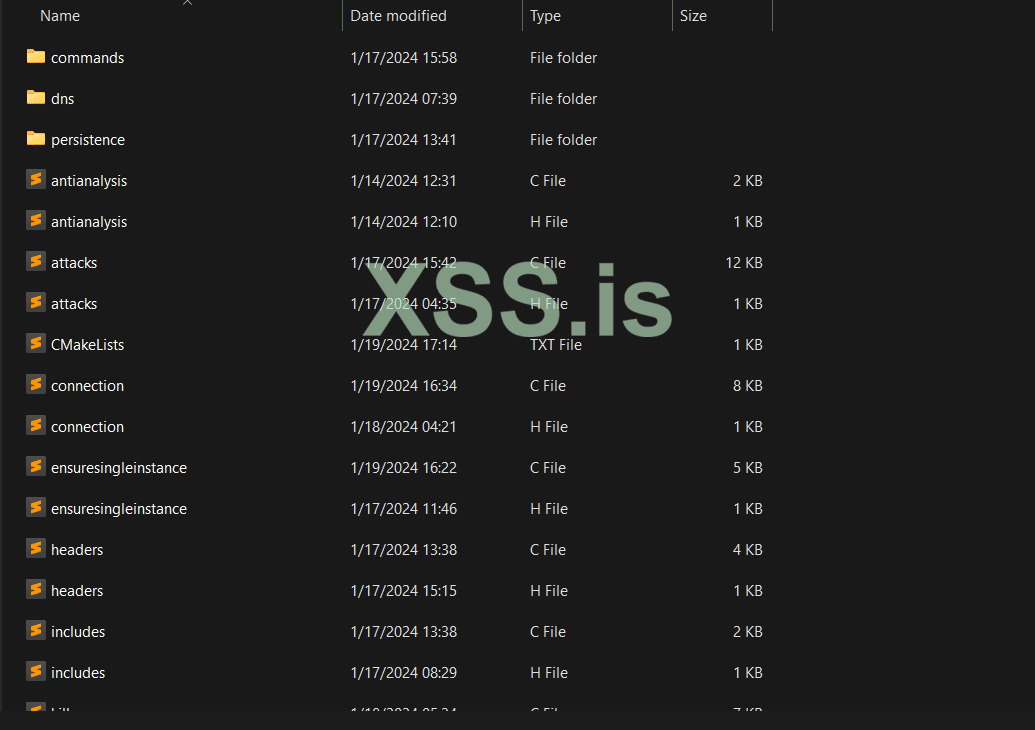
Introducing a very advanced Linux botnet with unique and stand-alone features. This botnet is referred to as Mushi Bot. This botnet is controlled through CNC a server and fallback domain method, offering additional capabilities beyond standard malicious uses. This is not a mirai fork, qbot, etc. This is completely its own bot.
Let's dive into the features of the bot.
Malware Killer: Mushi Bot includes a feature to eliminate competing malware present in any other infected systems. This ensures that the bot maintains exclusive control over the device, enhancing its stability and effectiveness. The specific way it works will not be disclosed. This malware killer will kill any non system process that operates in specific ways, thus efficiently eliminating other malwares. This has been tested with XorDDOS, mirai variants, mozi, gafgyt, qbots, and much more. None of them survived when I infected the devices.
Bot Updates: The network is capable of receiving and deploying updates to all its bots with one simple command that takes 5 seconds to type out. This allows the operator to continuously enhance the capabilities, fix bugs, add features, and adapt to countermeasures deployed by security teams, keeping the network resilient and operational over time.
Bot Shutdown: The network is capable of shutting down every single device connected to the CNC and or infected by the bot. It will also remove/delete every trace of the binary on the devices you infect. This allows for stealthy operations in case something goes wrong.
Stealth Operations: The bot is designed to operate under the radar, employing techniques to avoid detection by antivirus and other security software. This includes encryption, domain (dns resolving), mounting techniques, and much more.
Customizable Attack Vectors: The bot has a highly customizable attack vector options for customized attack on protected systems, such as using your own tcp flags, your own udp flags, payloads, pps, size, time, etc. You can always add in your own customized methods later in time after you scan bots as the ability to run bot updates is present. With the bot you can also end attacks based off each attack ID which is automatically assigned and printed in the CNC.
Persistence: The bot implements multiple persistence methods to ensure that your bot will run on devices if the process somehow dies or the device reboots. We operate persistence on IOT devices including telnet and openWRT. We also operate SSH persistence with the unique ability to kill SSHD indefinitely. Once you infect an SSH server nothing will be able to login to the server again, even after reboot.
Bot Messages: The bot has the ability to relay messages back to the CNC on what it's doing. For example what processes are getting killed, what attacks are running, and more.
Control and Command Flexibility: The bot is managed through a customizable live updating CNC without the need to rebuild the program. All actions are also logged in the CNC screen thus allowing your clients or yourself to easily command and monitor the network.
And more!
PRICE for full source code + lifetime updates for FREE! + FREE support: 3000$
PRICE for any custom feature you want added is 100-200$ per feature depending on complexity.
Please contact the following socials to negotiate deal. Proof provided in messages.
ELEMENT: @kiberphant0m:matrix.org
TOX: 99A108DFC3EE6F0B2FCC15F220BCF052FF05AAB4E8D95497FB49044501EBAF01AB70FA3C3E1E


Let's dive into the features of the bot.
Malware Killer: Mushi Bot includes a feature to eliminate competing malware present in any other infected systems. This ensures that the bot maintains exclusive control over the device, enhancing its stability and effectiveness. The specific way it works will not be disclosed. This malware killer will kill any non system process that operates in specific ways, thus efficiently eliminating other malwares. This has been tested with XorDDOS, mirai variants, mozi, gafgyt, qbots, and much more. None of them survived when I infected the devices.
Bot Updates: The network is capable of receiving and deploying updates to all its bots with one simple command that takes 5 seconds to type out. This allows the operator to continuously enhance the capabilities, fix bugs, add features, and adapt to countermeasures deployed by security teams, keeping the network resilient and operational over time.
Bot Shutdown: The network is capable of shutting down every single device connected to the CNC and or infected by the bot. It will also remove/delete every trace of the binary on the devices you infect. This allows for stealthy operations in case something goes wrong.
Stealth Operations: The bot is designed to operate under the radar, employing techniques to avoid detection by antivirus and other security software. This includes encryption, domain (dns resolving), mounting techniques, and much more.
Customizable Attack Vectors: The bot has a highly customizable attack vector options for customized attack on protected systems, such as using your own tcp flags, your own udp flags, payloads, pps, size, time, etc. You can always add in your own customized methods later in time after you scan bots as the ability to run bot updates is present. With the bot you can also end attacks based off each attack ID which is automatically assigned and printed in the CNC.
Persistence: The bot implements multiple persistence methods to ensure that your bot will run on devices if the process somehow dies or the device reboots. We operate persistence on IOT devices including telnet and openWRT. We also operate SSH persistence with the unique ability to kill SSHD indefinitely. Once you infect an SSH server nothing will be able to login to the server again, even after reboot.
Bot Messages: The bot has the ability to relay messages back to the CNC on what it's doing. For example what processes are getting killed, what attacks are running, and more.
Control and Command Flexibility: The bot is managed through a customizable live updating CNC without the need to rebuild the program. All actions are also logged in the CNC screen thus allowing your clients or yourself to easily command and monitor the network.
And more!
PRICE for full source code + lifetime updates for FREE! + FREE support: 3000$
PRICE for any custom feature you want added is 100-200$ per feature depending on complexity.
Please contact the following socials to negotiate deal. Proof provided in messages.
ELEMENT: @kiberphant0m:matrix.org
TOX: 99A108DFC3EE6F0B2FCC15F220BCF052FF05AAB4E8D95497FB49044501EBAF01AB70FA3C3E1E


Последнее редактирование: