News about a leak of Cobalt Strike v4.9 broke out on 2023-10-09 and there seems to be two versions, one appears to be leaked by an actor that goes by alias "pwn3rzs" and the other one is allegedly available on a Chinese website.
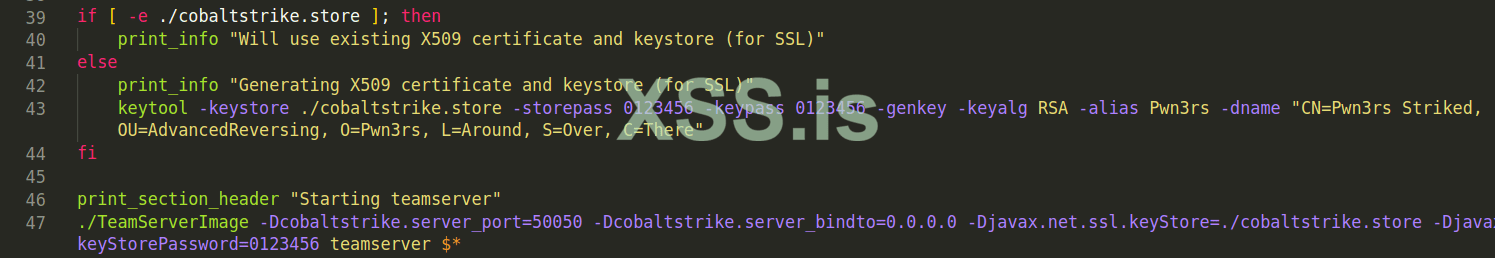
teamserver script
Taking a close look at the parameters passed to the keytool command, we noticed multiple indicators that we can utilize to build detection rules to identify the infra being used by a threat actor who decided to utilize this leaked version of CS without introducing any changes on the configuration (specifically the SSL/TLS certificate parameters)
The indicators we extracted are as follows:
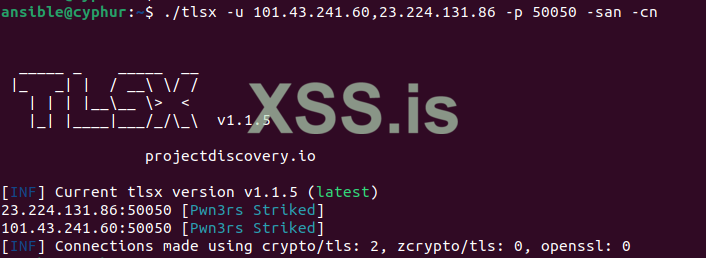
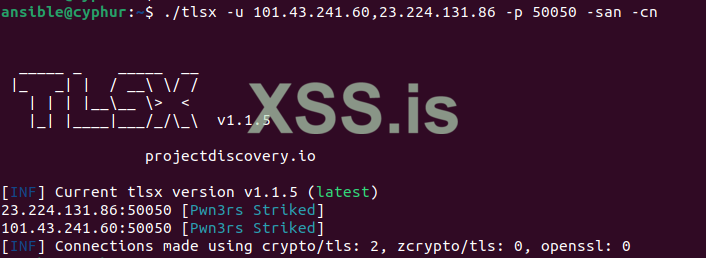
We attempted to test our detection rules in the wild and we already got multiple hits:
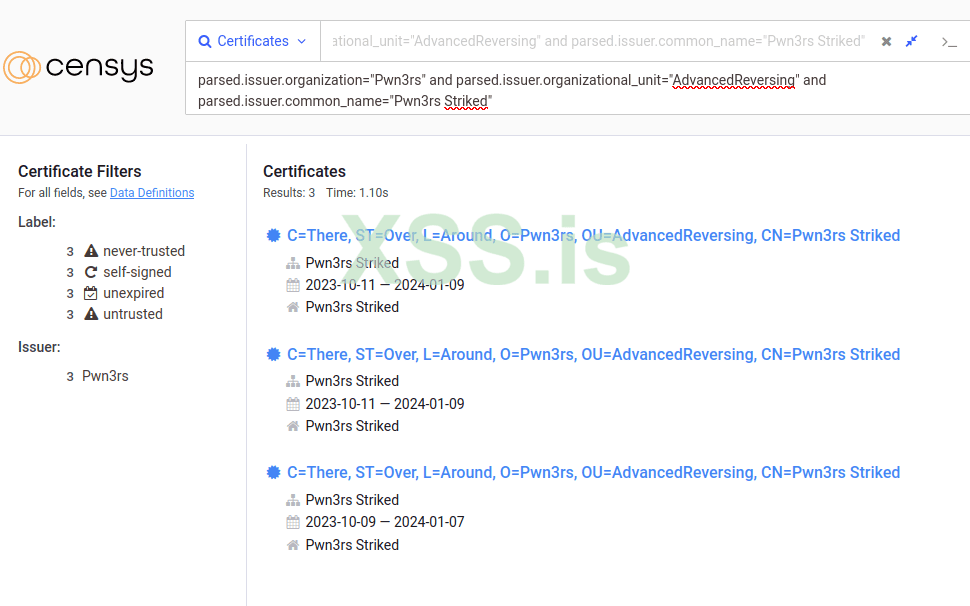
Searching for the indicators
We decided to pivot from identified certificate(s) to corresponding host(s) and found two servers:
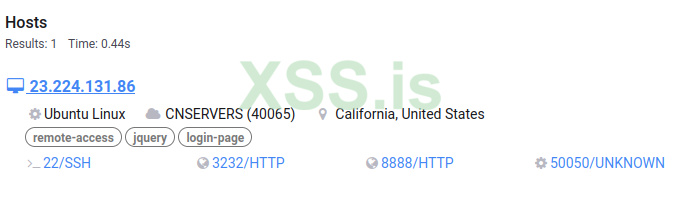
Host 1
Host 2
We verified the served SSL/TLS certificate manually and we can confirm it matches the indicators collected from the leak.
We got our hands on the "pwn3rzs" leak and started playing around and searching for indicators. We noticed that it contains a script which does minor checks and applies some configurations. Then, it proceeds to run the CS Team Server. The configuration introduced contains several changes but what caught our eyes is generating an SSL/TLS certificate. This certificate is used later by the "Team Server".Seems to be spreading around Telegram fast, along with the arsenal kit pic.twitter.com/XVczRlgfa3
— Dominic Chell(@domchell) October 9, 2023
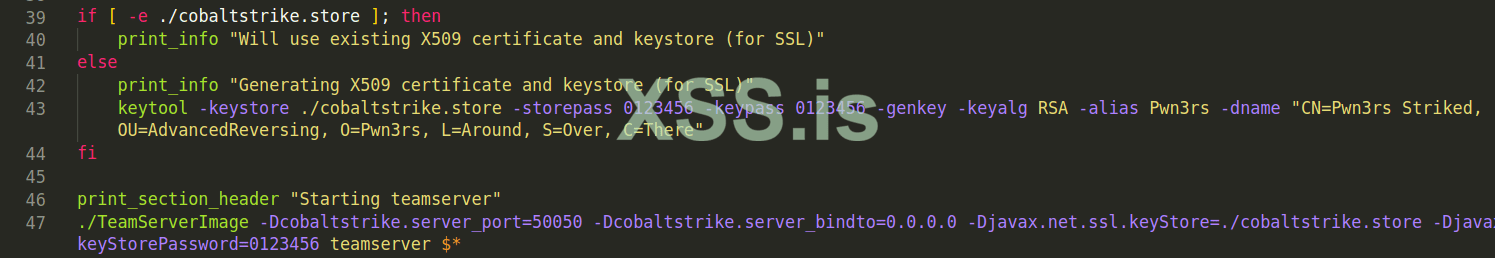
teamserver script
Taking a close look at the parameters passed to the keytool command, we noticed multiple indicators that we can utilize to build detection rules to identify the infra being used by a threat actor who decided to utilize this leaked version of CS without introducing any changes on the configuration (specifically the SSL/TLS certificate parameters)
The indicators we extracted are as follows:
- The "Team Server" will be running at port 50050
- The service on that port will be utilizing the generated SSL/TLS certificate with the following values:
| Field | Value |
|---|---|
| Common Name | Pwn3rs Striked |
| Organization | Pwn3rs |
| Organizational Unit | AdvancedReversing |
| Locality or City | Around |
| State or Province | Over |
| Country Name | There |
We attempted to test our detection rules in the wild and we already got multiple hits:
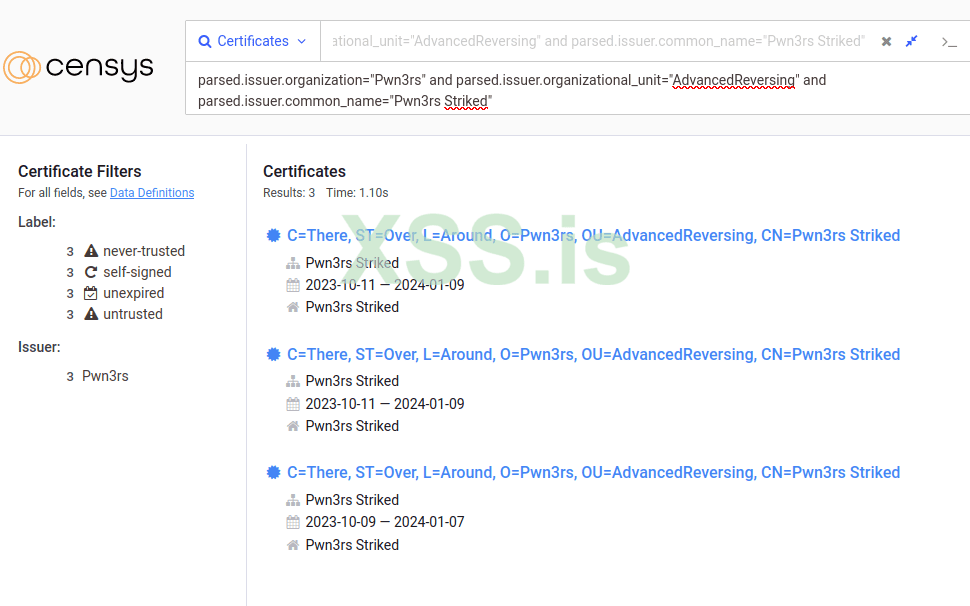
Searching for the indicators
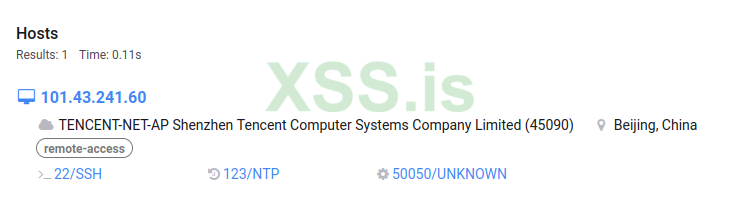
We decided to pivot from identified certificate(s) to corresponding host(s) and found two servers:
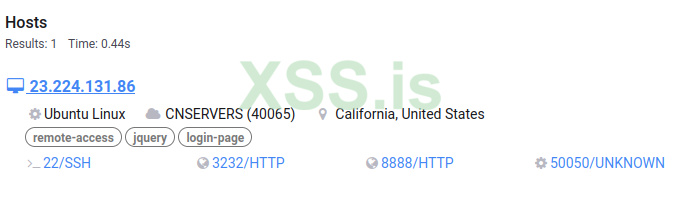
Host 1
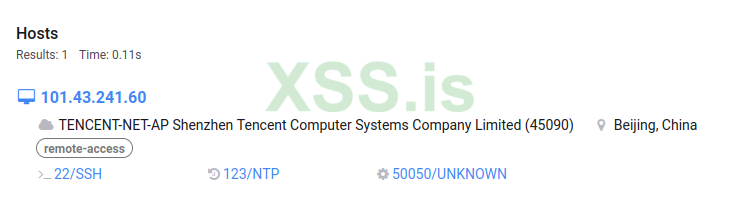
Host 2
We verified the served SSL/TLS certificate manually and we can confirm it matches the indicators collected from the leak.