Пожалуйста, обратите внимание, что пользователь заблокирован
Hi!
Need link to BlueKeep for windows(bksexe)
im very need.
Need link to BlueKeep for windows(bksexe)
im very need.
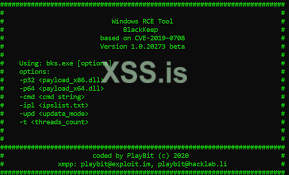
Need version by PlayBit(bks.exe)
GitHub - Ekultek/BlueKeep: Proof of concept for CVE-2019-0708
Proof of concept for CVE-2019-0708. Contribute to Ekultek/BlueKeep development by creating an account on GitHub.github.com
=[ metasploit v6.3.30-dev- ]
+ -- --=[ 2340 exploits - 1220 auxiliary - 413 post ]
+ -- --=[ 1387 payloads - 46 encoders - 11 nops ]
+ -- --=[ 9 evasion ]
Metasploit tip: You can pivot connections over sessions
started with the ssh_login modules
Metasploit Documentation: https://docs.metasploit.com/
msf6 > search bluekeep
Matching Modules
================
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 auxiliary/scanner/rdp/cve_2019_0708_bluekeep 2019-05-14 normal Yes CVE-2019-0708 BlueKeep Microsoft Remote Desktop RCE Check
1 exploit/windows/rdp/cve_2019_0708_bluekeep_rce 2019-05-14 manual Yes CVE-2019-0708 BlueKeep RDP Remote Windows Kernel Use After Free
Interact with a module by name or index. For example info 1, use 1 or use exploit/windows/rdp/cve_2019_0708_bluekeep_rceNeed version for windows. (BlackKeep by PlayBit)It's in metasploit...
Install msf: https://docs.metasploit.com/docs/using-metasploit/getting-started/nightly-installers.html
Код:=[ metasploit v6.3.30-dev- ] + -- --=[ 2340 exploits - 1220 auxiliary - 413 post ] + -- --=[ 1387 payloads - 46 encoders - 11 nops ] + -- --=[ 9 evasion ] Metasploit tip: You can pivot connections over sessions started with the ssh_login modules Metasploit Documentation: https://docs.metasploit.com/ msf6 > search bluekeep Matching Modules ================ # Name Disclosure Date Rank Check Description - ---- --------------- ---- ----- ----------- 0 auxiliary/scanner/rdp/cve_2019_0708_bluekeep 2019-05-14 normal Yes CVE-2019-0708 BlueKeep Microsoft Remote Desktop RCE Check 1 exploit/windows/rdp/cve_2019_0708_bluekeep_rce 2019-05-14 manual Yes CVE-2019-0708 BlueKeep RDP Remote Windows Kernel Use After Free Interact with a module by name or index. For example info 1, use 1 or use exploit/windows/rdp/cve_2019_0708_bluekeep_rce
https://github.com/nccgroup/BKScan.git This is a checker to scan if the system is vulnerable to bluekeepHi!
Need link to BlueKeep for windows(bksexe)
Need version for windows. (BlackKeep by PlayBit)https://github.com/nccgroup/BKScan.git This is a checker to scan if the system is vulnerable to bluekeep
This is how to build, but you have more instruction on the github
$ git clone https://github.com/nccgroup/BKScan.git
$ cd BKScan
$ sudo docker build -t bkscan .
[...]
Successfully built f7666aeb3259
Successfully tagged bkscan:latest
And how to run it, again the github have more detailed instruction
$ git clone https://github.com/nccgroup/BKScan.git
$ cd BKScan
$ sudo docker build -t bkscan .
[...]
Successfully built f7666aeb3259
Successfully tagged bkscan:latest
https://github.com/TinToSer/bluekeep-exploit.git here is an exploit, work with metasploit
https://www.rapid7.com/blog/post/20...it-exploit-module-for-bluekeep-cve-2019-0708/ more info for this exploit on rapid7
I hope this help you, have a nice day

 dropmefiles.com
dropmefiles.com
The file is deleted, I appreciate if you can re-share it sir ?pass1:123
DropMeFiles – free one-click file sharing service
Share your pictures, send large videos, exchange music or transfer big files. No registration required. Unlimited upload/download speed.dropmefiles.com
pass2:playbit

 dropmefiles.com
dropmefiles.com
that bluekeep exploit is old. has anyone developed any newer version of that?It's in metasploit...
Install msf: https://docs.metasploit.com/docs/using-metasploit/getting-started/nightly-installers.html
Код:=[ metasploit v6.3.30-dev- ] + -- --=[ 2340 exploits - 1220 auxiliary - 413 post ] + -- --=[ 1387 payloads - 46 encoders - 11 nops ] + -- --=[ 9 evasion ] Metasploit tip: You can pivot connections over sessions started with the ssh_login modules Metasploit Documentation: https://docs.metasploit.com/ msf6 > search bluekeep Matching Modules ================ # Name Disclosure Date Rank Check Description - ---- --------------- ---- ----- ----------- 0 auxiliary/scanner/rdp/cve_2019_0708_bluekeep 2019-05-14 normal Yes CVE-2019-0708 BlueKeep Microsoft Remote Desktop RCE Check 1 exploit/windows/rdp/cve_2019_0708_bluekeep_rce 2019-05-14 manual Yes CVE-2019-0708 BlueKeep RDP Remote Windows Kernel Use After Free Interact with a module by name or index. For example info 1, use 1 or use exploit/windows/rdp/cve_2019_0708_bluekeep_rce
did you find a newer way to access rdp?I just found a post mentioning:
A fresh BlueKeep exploit + loader, written by the exploit developer known as "PlayBit" and named by him "BlackKeep".
— Check Point Research (@_CPResearch_) February 23, 2021
The sample is available on Virus Total (6/68): https://t.co/CWvJkTxcKA pic.twitter.com/PCznQVHoU6
where can i find @playbit?

 dropmefiles.com
dropmefiles.com
thank you, and then tell me how to use cfg.txt. Can i modify the groomsize and groombase address (NPP address) in bks.exe ?Pass: xss.pro
DropMeFiles – free one-click file sharing service
Share your pictures, send large videos, exchange music or transfer big files. No registration required. Unlimited upload/download speed.dropmefiles.com
А кто то может, пожалуйста обновить ссылку на файл?

 dropmefiles.com
dropmefiles.com
Товарищ, можете перезалить?
DropMeFiles – free one-click file sharing service
Share your pictures, send large videos, exchange music or transfer big files. No registration required. Unlimited upload/download speed.dropmefiles.com