проблемы с распаковкой bin.tar.xz
после монтирования .vmdk и распаковки rootfs нашел бинарь xz в директории /sbin . не понимаю, почему дает ошибку при запуске его.
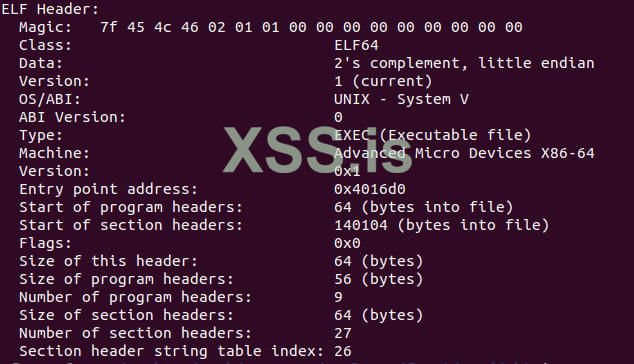
readelf:
uname -a:
Linux 5.19.0-41-generic #42~22.04.1-Ubuntu SMP PREEMPT_DYNAMIC Tue Apr 18 17:40:00 UTC 2 x86_64 x86_64 x86_64 GNU/Linux
хэлпаните плс.
после монтирования .vmdk и распаковки rootfs нашел бинарь xz в директории /sbin . не понимаю, почему дает ошибку при запуске его.
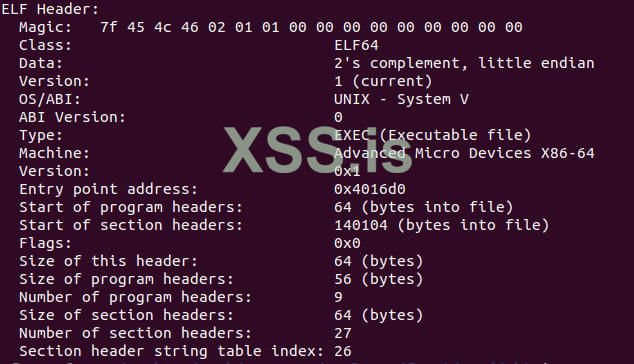
readelf:
uname -a:
Linux 5.19.0-41-generic #42~22.04.1-Ubuntu SMP PREEMPT_DYNAMIC Tue Apr 18 17:40:00 UTC 2 x86_64 x86_64 x86_64 GNU/Linux
хэлпаните плс.