there are increasing mitigations, nx, aslr etc, programs are being written with memory safe languages
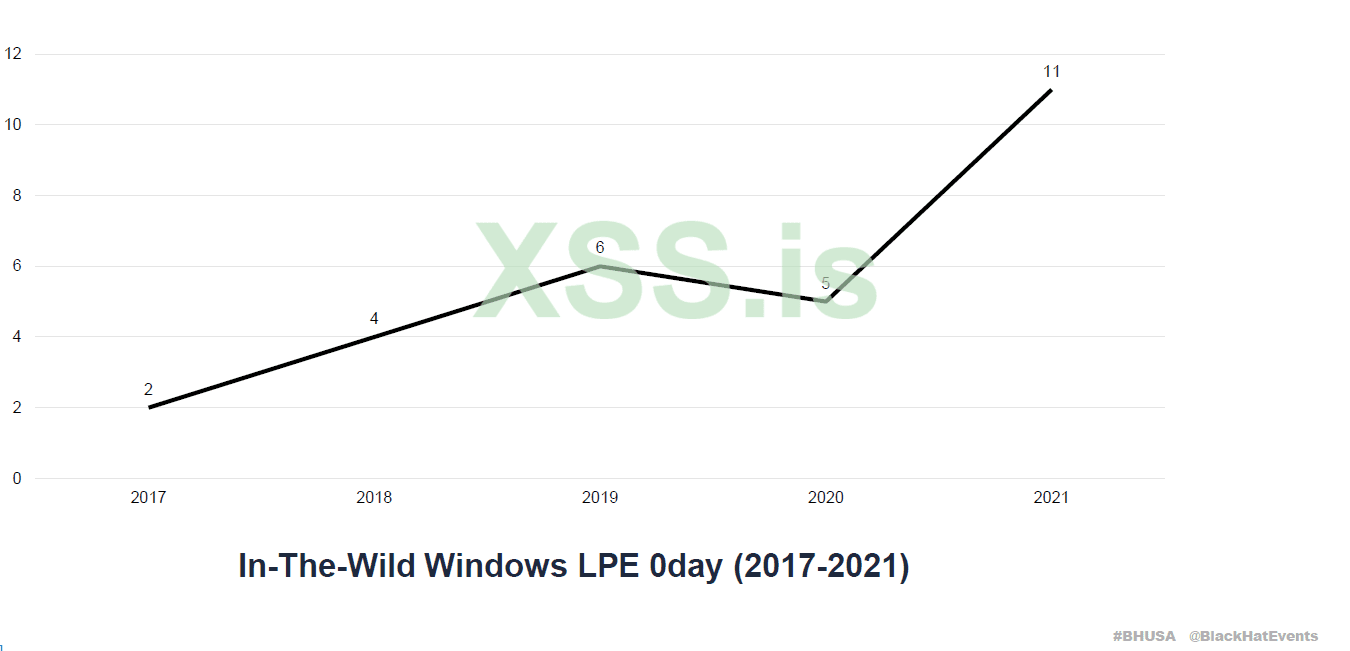
of course exploits still appear out every year but not like it was 20 years before with simple fuzzing
maybe more frequently exploits are found in iot but very difficult in windows, linux, macos
there is basic knowledge with memory level exploitation with me
is it recommend for a such beginners like myself to go deep into this field so as to one day work with advanced area like os kernels, cpu level?
some man say that already those who are with good knowledge and skill will remain in this field and all the lower skilled will go away in future years
you can discuss future of this field, is it worth to start now so one day a guy like me can work with os kernels, cpu etc before the field become very difficult, also write your learning experience and advise for such beginners like myself
of course exploits still appear out every year but not like it was 20 years before with simple fuzzing
maybe more frequently exploits are found in iot but very difficult in windows, linux, macos
there is basic knowledge with memory level exploitation with me
is it recommend for a such beginners like myself to go deep into this field so as to one day work with advanced area like os kernels, cpu level?
some man say that already those who are with good knowledge and skill will remain in this field and all the lower skilled will go away in future years
you can discuss future of this field, is it worth to start now so one day a guy like me can work with os kernels, cpu etc before the field become very difficult, also write your learning experience and advise for such beginners like myself
Последнее редактирование: