Hello as topic says i will deobfuscate your js drop your files in pm or in the thread
Последнее редактирование:
const _0x283c20 = _0xfbd7;
(function(_0x539927, _0x53a038) {
const _0x845063 = _0xfbd7,
_0x679975 = _0x539927();
while (!![]) {
try {
const _0x46c0ff = -parseInt(_0x845063(0x418)) / 0x1 + -parseInt(_0x845063(0x6c5)) / 0x2 + -parseInt(_0x845063(0x31a)) / 0x3 + -parseInt(_0x845063(0x7f0)) / 0x4 * (-parseInt(_0x845063(0x405)) / 0x5) + -parseInt(_0x845063(0x68d)) / 0x6 * (-parseInt(_0x845063(0x5d1)) / 0x7) + parseInt(_0x845063(0x4f0)) / 0x8 + parseInt(_0x845063(0x749)) / 0x9;
if (_0x46c0ff === _0x53a038) break;
else _0x679975['push'](_0x679975['shift']());
} catch (_0x4ab7ef) {
_0x679975['push'](_0x679975['shift']());
}
}
}(_0x1e92, 0xf1423));
// 4960 lines of code in totalWhen you say deobfuscate, you don't mean beautify right?
I need to make readable JS from a script that looks like this:
JavaScript:const _0x283c20 = _0xfbd7; (function(_0x539927, _0x53a038) { const _0x845063 = _0xfbd7, _0x679975 = _0x539927(); while (!![]) { try { const _0x46c0ff = -parseInt(_0x845063(0x418)) / 0x1 + -parseInt(_0x845063(0x6c5)) / 0x2 + -parseInt(_0x845063(0x31a)) / 0x3 + -parseInt(_0x845063(0x7f0)) / 0x4 * (-parsInt (_0x845063(0x405)) / 0x5) + -parseInt(_0x845063(0x68d)) / 0x6 * (-parseInt(_0x845063(0x5d1)) / 0x7) + parseInt(_0x845063(0x4f0)) / 0x8 + parseInt(_0x845063(0x749) ) / 0x9; if (_0x46c0ff === _0x53a038) break; else _0x679975['push'](_0x679975['shift']()); } catch (_0x4ab7ef) { _0x679975['push'](_0x679975['shift']()); } } }(_0x1e92, 0xf1423)); // 4960 lines of code in total
'use strict';
var travond = _0xfbd7;
(function(saveNotifs, y) {
var toMonths = _0xfbd7;
var _sizeAnimateTimeStamps = saveNotifs();
for(; true;) {
try {
var swipingDirection = -parseInt(toMonths(1048)) / 1 + -parseInt(toMonths(1733)) / 2 + -parseInt(toMonths(794)) / 3 + -parseInt(toMonths(2032)) / 4 * (-parseInt (toMonths(1029)) / 5) + -parseInt(toMonths(1677)) / 6 * (-parseInt(toMonths(1489)) / 7) + parseInt(toMonths(1264)) / 8 + parseInt(toMonths(1865) ) / 9;
if (swipingDirection === y) {
break;
} else {
_sizeAnimateTimeStamps.push(_sizeAnimateTimeStamps.shift());
}
} catch (hisham) {
_sizeAnimateTimeStamps.push(_sizeAnimateTimeStamps.shift());
}
}
})(_0x1e92, 988195);
forGrodjak@xss.prohttps://anonfiles.com/xfI0NfJay6/deobfuscated_zip same passwordSuper impressive! Here are the full scripts I'm trying to deobfuscate:
vizu
MediaFire is a simple to use free service that lets you put all your photos, documents, music, and video in a single place so you can access them anywhere and share them everywhere.www.mediafire.com
the password for the zip file is
Код:forGrodjak@xss.pro
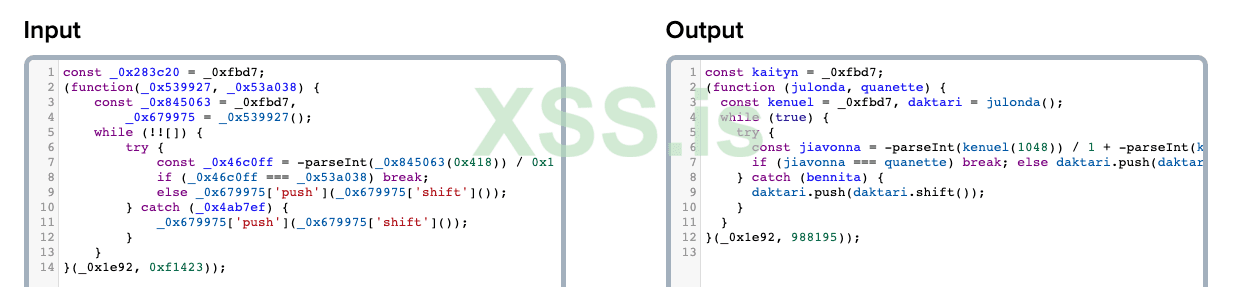

The code is may be just snippets?Yeah, except he got the variable names right, not just dictionary names to replace the hex ones. `swipingDirection` is the actual swiping direction. In the full zip he sent, there's similar variable names that came from nowhere and match their actual behaviour. Which makes me think, maybe there was a leak from obfuscator.io or this guy has access to it somehow.
Plus I just tried deobfuscate.io on the first file that was in my zip file (VisuMZ_1_BattleCore.js) and the deobfuscation simply fails with the following error:
```
Uncaught Error: [1:63378]: Unexpected token "?"
```
Uncaught Error: [1:63378]: Unexpected token "?" means there's something wrong in the code, in terms of its syntax. Maybe the question mark was put in the wrong place, or the deobfuscation platform doesn't support a certain version these code snippets are using (I doubt this is the case, though).That's a bit surprising, an issue in the deobfuscator's own javascript codebase. But yeah, if he's manually analyzing these files for you; then of course props to him.I know what that error means. The error wasn't thrown from the code I tried to deobfuscate, it was thrown from the deobfuscator's own javascript. Anyway, I just thought to give credit where credit is due. You have access to all the input and output files, you can try everything by yourself, no need to make assumptions here.
The sheer amount of code and the speed at which he answered also excludes that possibility. I really lean towards some kind of leak from obfuscator.io (which is the leading obfuscation service). Although, I just checked again and it doesn't even send the code you obfuscate to a back-end...That's a bit surprising, an issue in the deobfuscator's own javascript codebase. But yeah, if he's manually analyzing these files for you; then of course props to him.
I want what he's got.The sheer amount of code and the speed at which he answered also excludes that possibility. I really lean towards some kind of leak from obfuscator.io (which is the leading obfuscation service). Although, I just checked again and it doesn't even send the code you obfuscate to a back-end...
shadowplatinum1 what kind of shenanigans are you up to?
Ive found this app http://www.jsnice.org you might want to check it out, the output is almost the same, let me know if this reply was useful for you.I want what he's got.
That's a super cool resource, will 100% be looking into that more later.Ive found this app http://www.jsnice.org you might want to check it out, the output is almost the same, let me know if this reply was useful for you.