Пожалуйста, обратите внимание, что пользователь заблокирован
Валидные SSH доступы с нестандартными портами  2222, :2223, :8022 итд)
2222, :2223, :8022 итд)
[CLIKE]71.80.158.179:2223;admin;password;United States;Washington;Richland, 99352
71.94.177.57:2223;admin;password;United States;Washington;Yakima, 98902
207.41.179.35:8022;guest;guest;United States;New York;The Bronx, 10465
173.220.230.60:22;monitor;monitor;United States;New York;The Bronx, 10456
165.228.116.13:8022;user;user;Australia;VIC;Windsor, 3181
60.242.19.96:8022;user;user;Australia;NSW;Bondi Junction, 2022
120.151.215.172:8022;user;user;Australia;QLD;New Farm, 4005
144.139.149.2:2222;admin;password;Australia;VIC;Brunswick West, 3055
120.146.130.18:2222;admin;admin;Australia;NSW;Greystanes, 2145
203.45.56.161:8022;user;user;Australia;VIC;Ardeer, 3022[/CLIKE]
[CLIKE]71.80.158.179:2223;admin;password;United States;Washington;Richland, 99352
71.94.177.57:2223;admin;password;United States;Washington;Yakima, 98902
207.41.179.35:8022;guest;guest;United States;New York;The Bronx, 10465
173.220.230.60:22;monitor;monitor;United States;New York;The Bronx, 10456
165.228.116.13:8022;user;user;Australia;VIC;Windsor, 3181
60.242.19.96:8022;user;user;Australia;NSW;Bondi Junction, 2022
120.151.215.172:8022;user;user;Australia;QLD;New Farm, 4005
144.139.149.2:2222;admin;password;Australia;VIC;Brunswick West, 3055
120.146.130.18:2222;admin;admin;Australia;NSW;Greystanes, 2145
203.45.56.161:8022;user;user;Australia;VIC;Ardeer, 3022[/CLIKE]
еще валидные?
Пожалуйста, обратите внимание, что пользователь заблокирован
попробуй провалиться под другими пассами на эти IP . если пускает значит нарвался на ханипот ) тож частенько такое вижу
Кккпопробуй провалиться под другими пассами на эти IP . если пускает значит нарвался на ханипот ) тож частенько такое вижу
Последнее редактирование:
дава ещеВалидные SSH доступы с нестандартными портами2222, :2223, :8022 итд)
Скрытое содержимое
Пожалуйста, обратите внимание, что пользователь заблокирован
1.6.10.131 | admin | admin
1.6.4.209 | admin | admin
1.6.4.208 | admin | admin
1.6.11.97 | admin | admin
1.6.11.70 | admin | admin
1.23.165.158 | ubnt | ubnt
1.6.10.81 | admin | admin
1.6.132.51 | admin | admin
1.6.138.119 | admin | admin
1.6.138.121 | admin | admin
1.6.141.219 | admin | admin
1.6.141.226 | admin | admin
1.6.144.82 | admin | admin
27.106.6.34 | ubnt | ubnt
27.106.14.10 | ubnt | ubnt
27.106.15.174 | ubnt | ubnt
give a thumbs up if you like it ..
1.6.4.209 | admin | admin
1.6.4.208 | admin | admin
1.6.11.97 | admin | admin
1.6.11.70 | admin | admin
1.23.165.158 | ubnt | ubnt
1.6.10.81 | admin | admin
1.6.132.51 | admin | admin
1.6.138.119 | admin | admin
1.6.138.121 | admin | admin
1.6.141.219 | admin | admin
1.6.141.226 | admin | admin
1.6.144.82 | admin | admin
27.106.6.34 | ubnt | ubnt
27.106.14.10 | ubnt | ubnt
27.106.15.174 | ubnt | ubnt
give a thumbs up if you like it ..
will try them soon1.6.10.131 | admin | admin
1.6.4.209 | admin | admin
1.6.4.208 | admin | admin
1.6.11.97 | admin | admin
1.6.11.70 | admin | admin
1.23.165.158 | ubnt | ubnt
1.6.10.81 | admin | admin
1.6.132.51 | admin | admin
1.6.138.119 | admin | admin
1.6.138.121 | admin | admin
1.6.141.219 | admin | admin
1.6.141.226 | admin | admin
1.6.144.82 | admin | admin
27.106.6.34 | ubnt | ubnt
27.106.14.10 | ubnt | ubnt
27.106.15.174 | ubnt | ubnt
give a thumbs up if you like it ..
thanks
fun ask 
for what are this god .. the ssh?
for what are this god .. the ssh?
Взгляните на эту пасту, я запечатлел ее благодаря одному из моих ботов. Я вошел в машину и, похоже, это виртуальная машина, может кто-нибудь подскажет мне, что я могу сделать?
--
Take a look at this paste, I captured it thanks to one of my bots. I access into the machine with those creds and seems to be a virtual machine, can someone tell me what can I do?
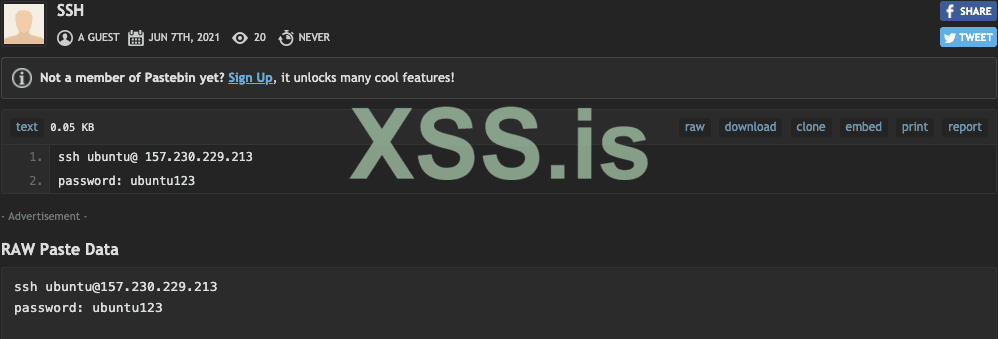
https://pastebin.com/5yc6LWZD
--
Take a look at this paste, I captured it thanks to one of my bots. I access into the machine with those creds and seems to be a virtual machine, can someone tell me what can I do?
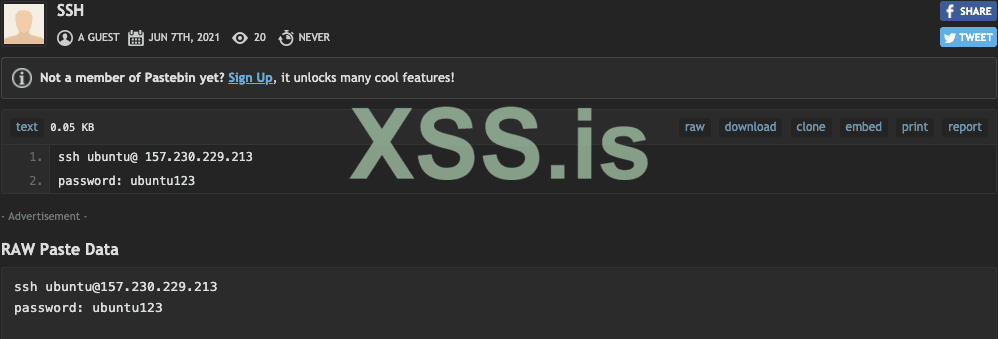
https://pastebin.com/5yc6LWZD
Here are a few web servers that have been configured badly, they all have SSH private keys in the SSH directory but if you do a bit of directory traversal then you can get access to the entire machine. Let me know if you want more as I can scrape thousands of these. Enjoy! 
https://www.nsrc.org/workshops/configs/2010/apricot/etc/ssh/https://www.nsrc.org/workshops/configs/2010/apricot/etc/ssh/
---------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
Вот несколько веб-серверов, которые были плохо настроены, все они имеют закрытые ключи SSH в каталоге SSH, но если вы немного пройдете по каталогу, то сможете получить доступ ко всей машине. Дайте мне знать, если вам нужно больше, так как я могу наскрести тысячи таких. Наслаждайтесь!
https://www.nsrc.org/workshops/configs/2010/apricot/etc/ssh/https://www.nsrc.org/workshops/configs/2010/apricot/etc/ssh/
https://www.nsrc.org/workshops/configs/2010/apricot/etc/ssh/https://www.nsrc.org/workshops/configs/2010/apricot/etc/ssh/
---------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
Вот несколько веб-серверов, которые были плохо настроены, все они имеют закрытые ключи SSH в каталоге SSH, но если вы немного пройдете по каталогу, то сможете получить доступ ко всей машине. Дайте мне знать, если вам нужно больше, так как я могу наскрести тысячи таких. Наслаждайтесь!
https://www.nsrc.org/workshops/configs/2010/apricot/etc/ssh/https://www.nsrc.org/workshops/configs/2010/apricot/etc/ssh/
Спасибо, что поделились!
Here I have a list of host names or IP address (depending on the box), they come with guaranteed usernames. This should be easy to brute force as you have the usernames and anyone with any sense will block root from being allowed to login via SSH (apart from one guy down in the list lol). Keep an eye in the dumps section as I will be posting up private keys for SSH boxes soon as well as API keys for various places. Enjoy! 
Host faqademy.dev
HostName vs05.faqademy.com
User faqademy
Host faqademy.prod
HostName vs04.faqademy.com
User faqademy
Host progress.staging
HostName staging1.wwdi.ru
User ap
IdentityFile "/Users/deppkind/.ssh/apavlyutprogressengine"
Host gitlab.berezka
HostName gitlab.brzka.ru
User ap
IdentityFile "/Users/deppkind/.ssh/apavlyutprogressengine"
Host bazalt
HostName 188.226.184.73
User ap
IdentityFile "/Users/deppkind/.ssh/apavlyutprogressengine"
Host ansible
HostName 82.196.9.105
User root
IdentityFile "/Users/deppkind/.ssh/apavlyutprogressengine"
Host depp
HostName 192.168.33.10
User deppkind
Host fightcamp
HostName 178.62.178.230
User deploy
----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
Здесь у меня есть список имен хостов или IP-адресов (в зависимости от поля), они поставляются с гарантированными именами пользователей. Это должно быть легко сделать грубой силой, так как у вас есть имена пользователей, и любой, у кого есть хоть какой-то смысл, заблокирует root, чтобы ему разрешили войти через SSH (кроме одного парня в списке lol). Следите за разделом "дампы", так как я скоро опубликую закрытые ключи для ящиков SSH, а также ключи API для различных мест. Наслаждайтесь!
Host faqademy.dev
HostName vs05.faqademy.com
User faqademy
Host faqademy.prod
HostName vs04.faqademy.com
User faqademy
Host progress.staging
HostName staging1.wwdi.ru
User ap
IdentityFile "/Users/deppkind/.ssh/apavlyutprogressengine"
Host gitlab.berezka
HostName gitlab.brzka.ru
User ap
IdentityFile "/Users/deppkind/.ssh/apavlyutprogressengine"
Host bazalt
HostName 188.226.184.73
User ap
IdentityFile "/Users/deppkind/.ssh/apavlyutprogressengine"
Host ansible
HostName 82.196.9.105
User root
IdentityFile "/Users/deppkind/.ssh/apavlyutprogressengine"
Host depp
HostName 192.168.33.10
User deppkind
Host fightcamp
HostName 178.62.178.230
User deploy
Host faqademy.dev
HostName vs05.faqademy.com
User faqademy
Host faqademy.prod
HostName vs04.faqademy.com
User faqademy
Host progress.staging
HostName staging1.wwdi.ru
User ap
IdentityFile "/Users/deppkind/.ssh/apavlyutprogressengine"
Host gitlab.berezka
HostName gitlab.brzka.ru
User ap
IdentityFile "/Users/deppkind/.ssh/apavlyutprogressengine"
Host bazalt
HostName 188.226.184.73
User ap
IdentityFile "/Users/deppkind/.ssh/apavlyutprogressengine"
Host ansible
HostName 82.196.9.105
User root
IdentityFile "/Users/deppkind/.ssh/apavlyutprogressengine"
Host depp
HostName 192.168.33.10
User deppkind
Host fightcamp
HostName 178.62.178.230
User deploy
----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
Здесь у меня есть список имен хостов или IP-адресов (в зависимости от поля), они поставляются с гарантированными именами пользователей. Это должно быть легко сделать грубой силой, так как у вас есть имена пользователей, и любой, у кого есть хоть какой-то смысл, заблокирует root, чтобы ему разрешили войти через SSH (кроме одного парня в списке lol). Следите за разделом "дампы", так как я скоро опубликую закрытые ключи для ящиков SSH, а также ключи API для различных мест. Наслаждайтесь!
Host faqademy.dev
HostName vs05.faqademy.com
User faqademy
Host faqademy.prod
HostName vs04.faqademy.com
User faqademy
Host progress.staging
HostName staging1.wwdi.ru
User ap
IdentityFile "/Users/deppkind/.ssh/apavlyutprogressengine"
Host gitlab.berezka
HostName gitlab.brzka.ru
User ap
IdentityFile "/Users/deppkind/.ssh/apavlyutprogressengine"
Host bazalt
HostName 188.226.184.73
User ap
IdentityFile "/Users/deppkind/.ssh/apavlyutprogressengine"
Host ansible
HostName 82.196.9.105
User root
IdentityFile "/Users/deppkind/.ssh/apavlyutprogressengine"
Host depp
HostName 192.168.33.10
User deppkind
Host fightcamp
HostName 178.62.178.230
User deploy
SSH host names, known hosts, configs and public/private keys. Enjoy! 
----------------------------------------------------------------------------------------------------------------------------------
Имена хостов SSH, известные хосты, конфигурации и открытые/закрытые ключи. Наслаждайтесь!
----------------------------------------------------------------------------------------------------------------------------------
Имена хостов SSH, известные хосты, конфигурации и открытые/закрытые ключи. Наслаждайтесь!
Look what I've seen on another forum:
I've accessed using those credentials and yes those credentials are working. Enjoy it
Another forum's thread:
#1
username1 commented
1 day ago
I was developing a simple API integration with Pastebin and I found a paste with some credentials. I tested them and it looks like some kind of HMI at 88.26.254.22:5900 (gonsalpe-operador:OUSTicHolDes). I’d never messed around with OT stuff but it was interesting
#2
username2 commented
23 hours ago
Yeah, username1. Creds totally work. I’ve dug a bit into the hostname and other keywords I could find on the net and it looks something related to the Spanish electrical company “Red Electrica Espanola”. Get away from there, governments involved...
#3
username1 commented
23 hours ago
LOL, thanks username2 ! I’d never think that a simple Pastebin script could find such a big rabithole hehe
I've accessed using those credentials and yes those credentials are working. Enjoy it
where is this?
Look what I've seen on another forum:
I've accessed using those credentials and yes those credentials are working. Enjoy it
You mean the forum?
That's not gonna happen, I don't want to get banned if I post you a link from another forum.
That's not gonna happen, I don't want to get banned if I post you a link from another forum.
where is this?
Последнее редактирование:
Учетки SSH
user/sudo/root
Просто ставьте +
user/sudo/root
Просто ставьте +
+ root
+ root
Скрытый контент для пользователей: sanytol.