Пожалуйста, обратите внимание, что пользователь заблокирован
im selling New loader for cobalt strike, this is another post on an earlier one i have created, but here im talking in details;
1. First ACHLYS detects the environment of the machine its being in, by checking sandboxes and debuggers presents.
2.second when the check succeeded achlys will download a pdf file (u created by a python script that comes with it)
the pdf file is the payload, the reason why its a pdf file is that avs won't even upload to there servers for analysis,
thats bcz it assume its personal information - review kaspersky av for example -
3.then it will start to inject the pdf file into the memory 5 bytes at a time, and not all the shellcodes at once, it will sleep for 1 sec
after each 5 bytes are injected.
4. After the injection succeeds it will sleep again for 10 secs before executing the shellcode.
5.here comes the interesting part:
- when the shellcode is executed it will be mapped as rwx [normal situations], thus some avs can scan it, and some blue teamers tools will too.
- but i made a new way of evading this kind of act, the shellcode will be in rwx for milliseconds only, and that's when cobalt strike
sends the heartbeat [network traffic] ... if it carried a command it will run it, so it won't affect anything.
- achlys will in the time of the dead connection between the server and the client be mapping the shellcode memory part to 'no access', thus it will
prevent any scanning tech for the memory signatures, because there is no such thing as "payload" in memory.
- it will map the shellcode part to rwx when the connection of the server is alive again [by default each 1 min on cobalt]
- so during this 1 min, [by default] the shellcode will be in 'no access' permissions.
- if ur not getting it, we will allow the avs to detect the shellcode only for milliseconds, and since there is many processes, and many other things to scan during
our processes [that's if the av choose us at first] other than our nice shellcode, it's impossible for the av to catch it. [it will have to choose our process and the memory part in which we have the
shellcode located to scan it and get the results in milliseconds - during our heartbeat communication!]
6.in addition to that achlys uses sysalls obtained by hashes during [runtime], thats to bypass edrs / avs so in the code u will not see something as
ntallocatevirtualmemory but instead u will see its hash, plus it will check if these syscalls are hooked and will unhook them.
achlys is sold with a profile, that changes the network traffic signatures.
and with a python file to make ur shellcode a pdf.
and a usage.txt file to know how to build it.
its a [c / cpp / assembly] project and cost 150 $ as [eth or btc] coins.
for any other details, feel free to ask!
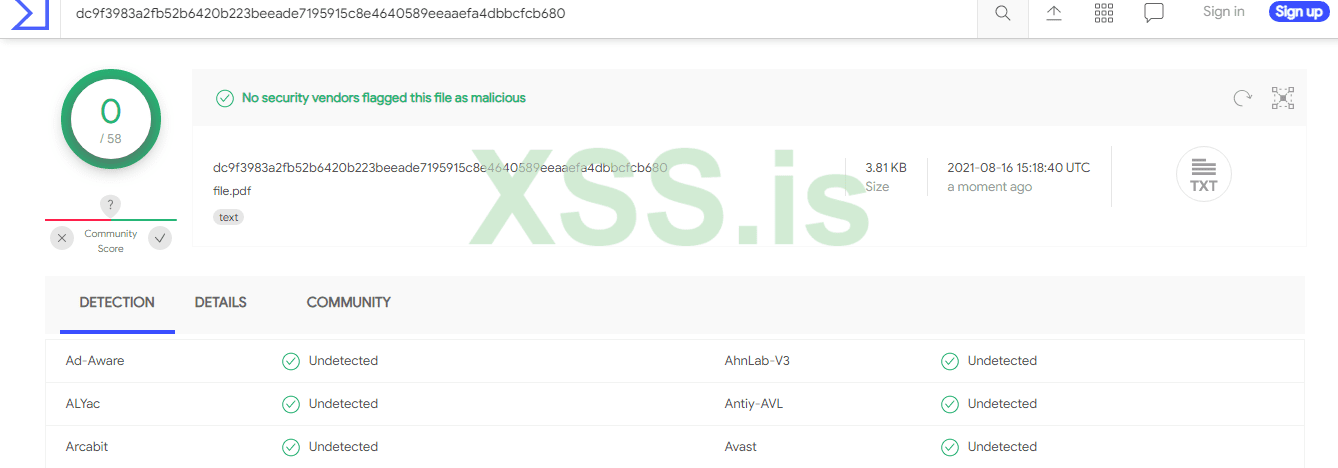
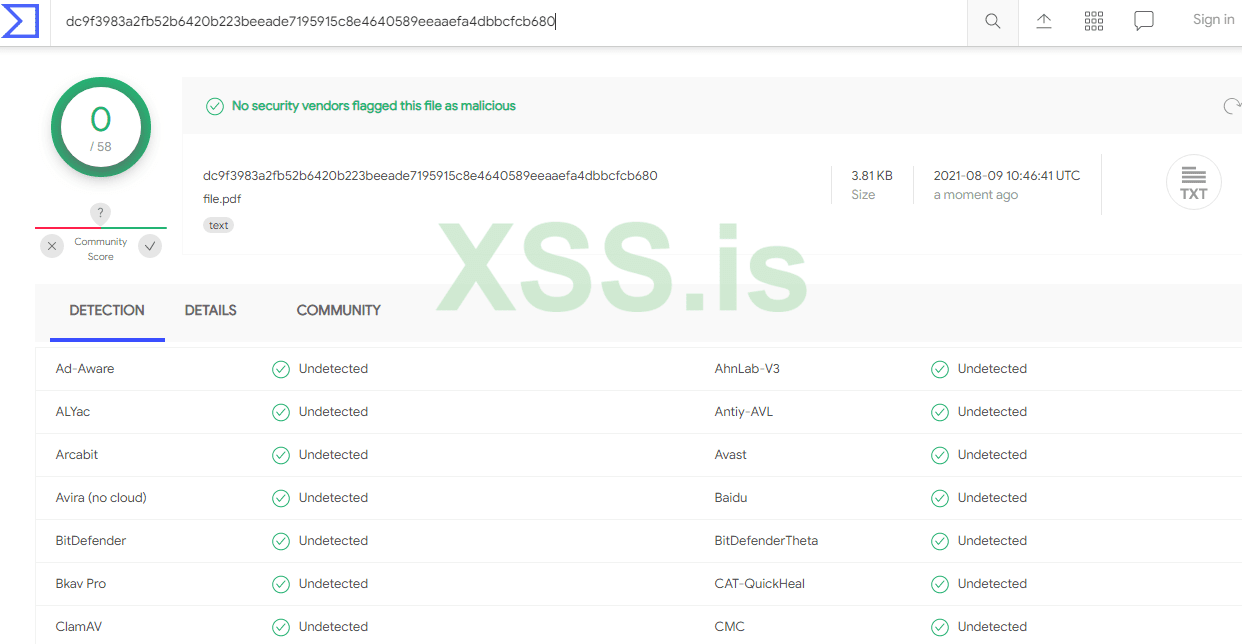
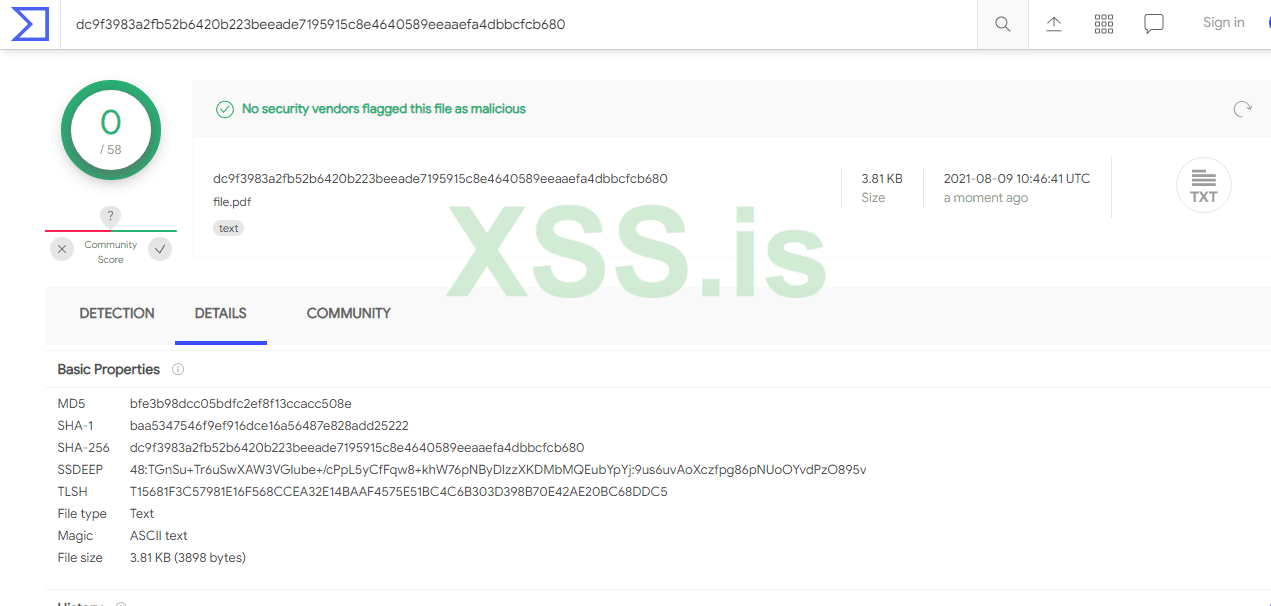
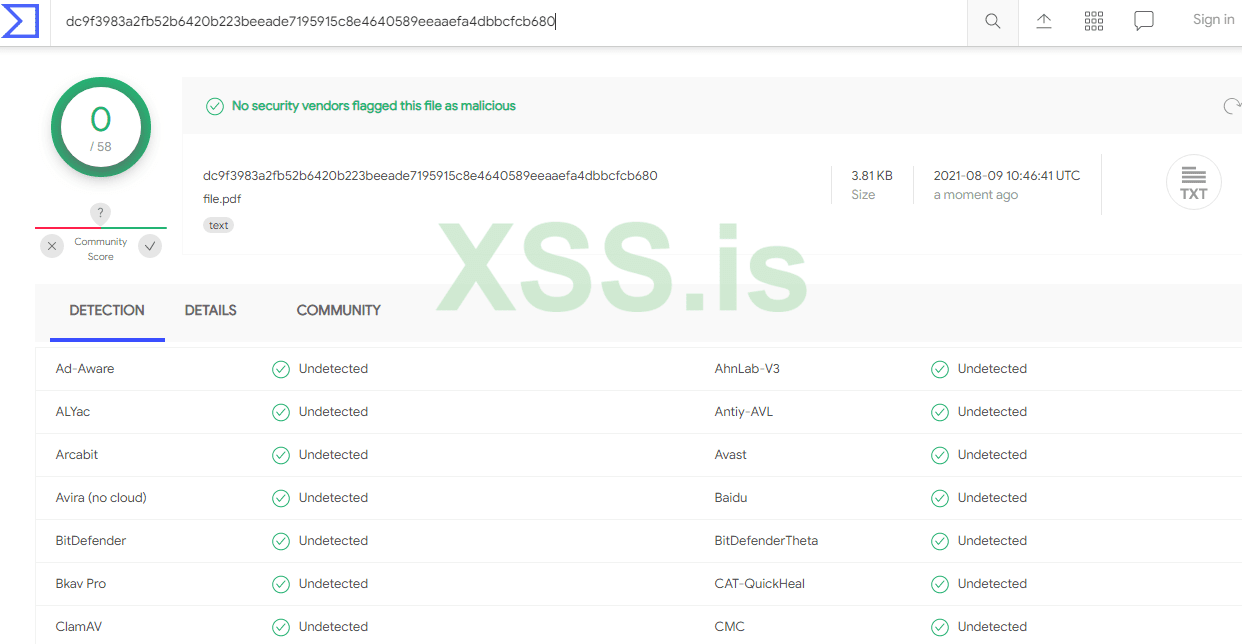
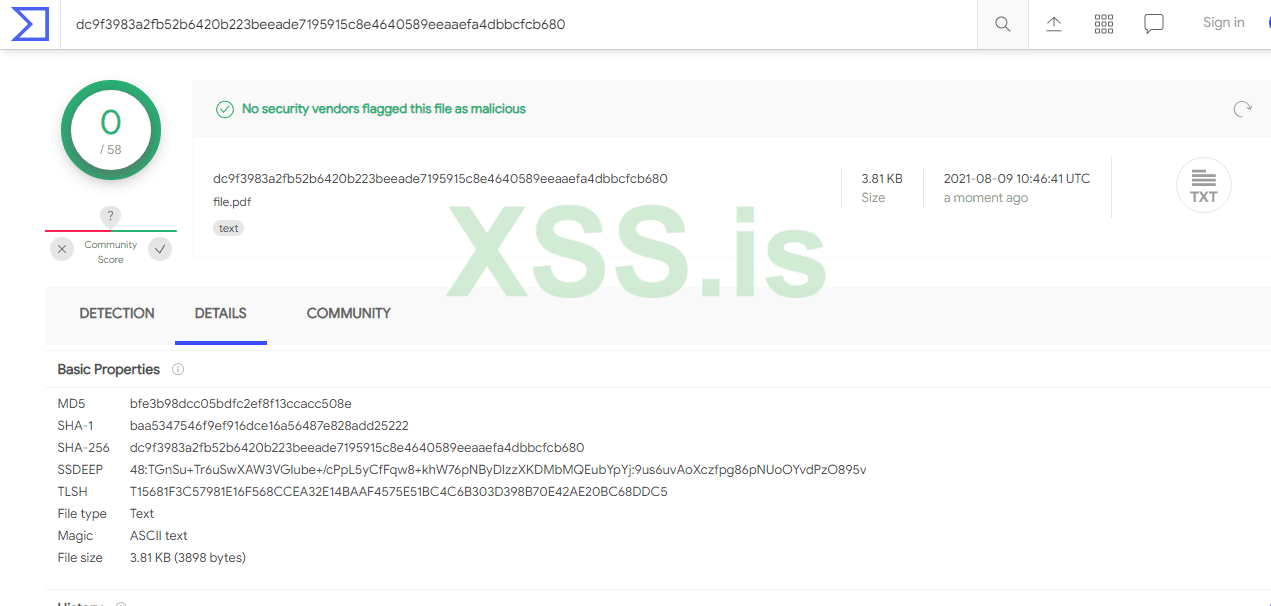
the pdf file [which is the payload file; cobalt strike shellcode]:
If u are interested in a vd clip or u wanna purchase the code, contact me at Mr-ORCA666@protonmail.com
[i will only be selling for 5 other guys now only, and thats to make it last]
1. First ACHLYS detects the environment of the machine its being in, by checking sandboxes and debuggers presents.
2.second when the check succeeded achlys will download a pdf file (u created by a python script that comes with it)
the pdf file is the payload, the reason why its a pdf file is that avs won't even upload to there servers for analysis,
thats bcz it assume its personal information - review kaspersky av for example -
3.then it will start to inject the pdf file into the memory 5 bytes at a time, and not all the shellcodes at once, it will sleep for 1 sec
after each 5 bytes are injected.
4. After the injection succeeds it will sleep again for 10 secs before executing the shellcode.
5.here comes the interesting part:
- when the shellcode is executed it will be mapped as rwx [normal situations], thus some avs can scan it, and some blue teamers tools will too.
- but i made a new way of evading this kind of act, the shellcode will be in rwx for milliseconds only, and that's when cobalt strike
sends the heartbeat [network traffic] ... if it carried a command it will run it, so it won't affect anything.
- achlys will in the time of the dead connection between the server and the client be mapping the shellcode memory part to 'no access', thus it will
prevent any scanning tech for the memory signatures, because there is no such thing as "payload" in memory.
- it will map the shellcode part to rwx when the connection of the server is alive again [by default each 1 min on cobalt]
- so during this 1 min, [by default] the shellcode will be in 'no access' permissions.
- if ur not getting it, we will allow the avs to detect the shellcode only for milliseconds, and since there is many processes, and many other things to scan during
our processes [that's if the av choose us at first] other than our nice shellcode, it's impossible for the av to catch it. [it will have to choose our process and the memory part in which we have the
shellcode located to scan it and get the results in milliseconds - during our heartbeat communication!]
6.in addition to that achlys uses sysalls obtained by hashes during [runtime], thats to bypass edrs / avs so in the code u will not see something as
ntallocatevirtualmemory but instead u will see its hash, plus it will check if these syscalls are hooked and will unhook them.
achlys is sold with a profile, that changes the network traffic signatures.
and with a python file to make ur shellcode a pdf.
and a usage.txt file to know how to build it.
its a [c / cpp / assembly] project and cost 150 $ as [eth or btc] coins.
for any other details, feel free to ask!
the pdf file [which is the payload file; cobalt strike shellcode]:
If u are interested in a vd clip or u wanna purchase the code, contact me at Mr-ORCA666@protonmail.com
[i will only be selling for 5 other guys now only, and thats to make it last]
Последнее редактирование: