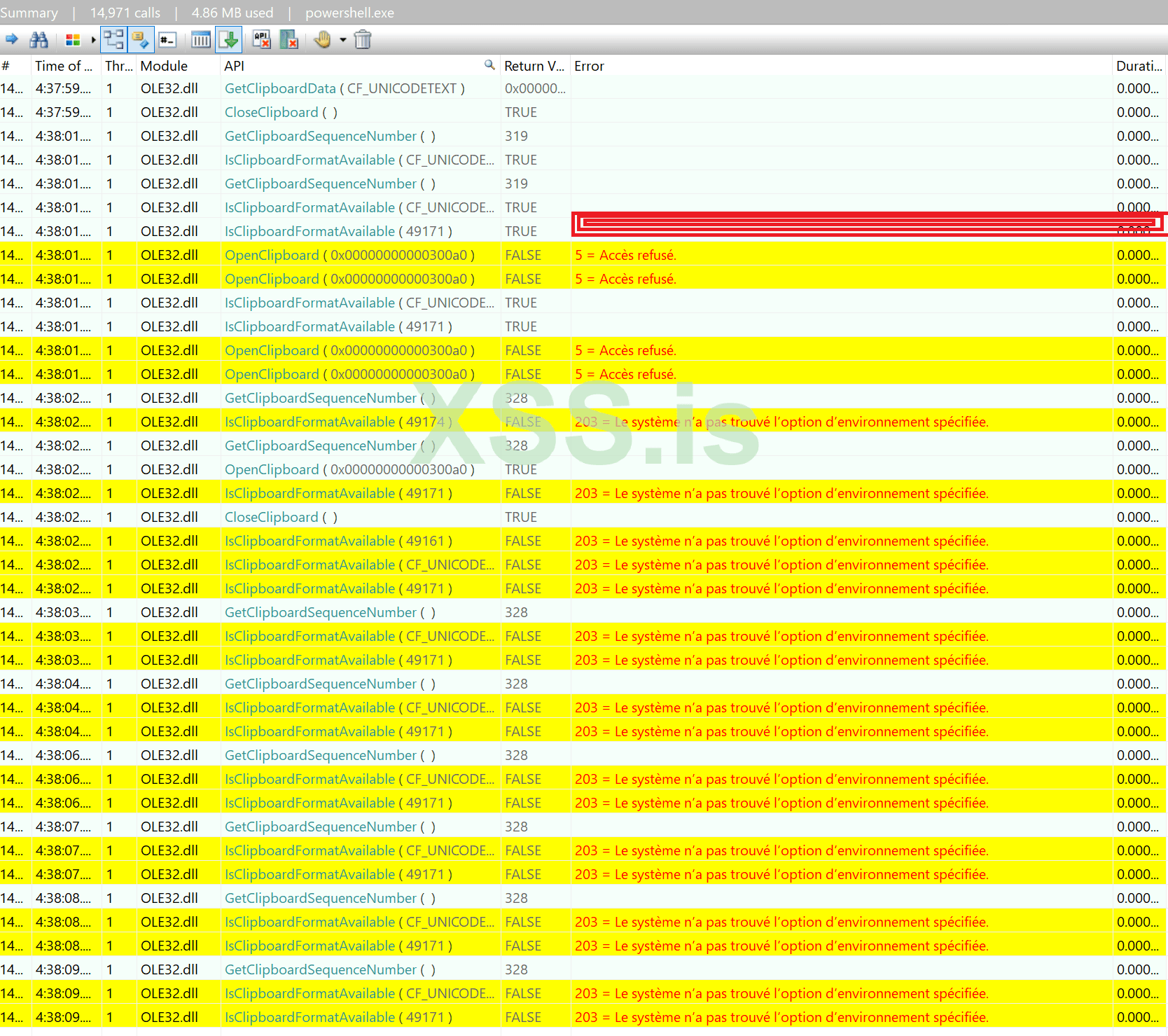
Hello, I am infected by a clipper who is connected to the internet with Powershell.exe on my Windows 10... So I think there is a RAT in there.
When I stop the internet I can copy BTC address normally but when the internet is here, the malware replaces the BTC adress with the same BTC address...
So I have identified the corrupt processes/tasks on my Windows and the name is Powershell.exe.
How can I remove it, please? I have tried with the Tron script and it doesn't work so now I am a little bit lost, I don't want to reinstall my windows and format everything...
Thanks for your advice! Have a great day!
If you need some screenshots or requirements to help you to see what I have on my computer just let me know in the comments!
When I stop the internet I can copy BTC address normally but when the internet is here, the malware replaces the BTC adress with the same BTC address...
So I have identified the corrupt processes/tasks on my Windows and the name is Powershell.exe.
How can I remove it, please? I have tried with the Tron script and it doesn't work so now I am a little bit lost, I don't want to reinstall my windows and format everything...
Thanks for your advice! Have a great day!
If you need some screenshots or requirements to help you to see what I have on my computer just let me know in the comments!